- 毫秒级断电+AI预警:广州曼顿智能空开如何重新定义电气安全?
mdkk678
人工智能安全
在智慧城市、工业4.0与“双碳”目标的推动下,电力系统正经历从传统被动响应向主动智能防控的深刻变革。广州曼顿科技推出的智能空气开关,凭借毫秒级断电技术与AI预警系统的深度融合,不仅填补了传统断路器在响应速度、故障预判和能效管理上的技术空白,更以“零时差守护”理念重塑了电气安全的新范式。一、技术突破:毫秒级断电的“物理屏障”传统断路器依赖机械结构实现过载保护,其响应时间通常在数十毫秒以上,难以应对瞬
- Python爬虫小白入门指南,成为大牛必须经历的三个阶段
学习任何一门技术,都应该带着目标去学习,目标就像一座灯塔,指引你前进,很多人学着学着就学放弃了,很大部分原因是没有明确目标,所以,一定要明确学习目的,在你准备学爬虫前,先问问自己为什么要学习爬虫。有些人是为了一份工作,有些人是为了好玩,也有些人是为了实现某个黑科技功能。不过可以肯定的是,学会了爬虫能给你的工作提供很多便利。小白入门必读作为零基础小白,大体上可分为三个阶段去实现。第一阶段是入门,掌握
- 如何设计可扩展的后端系统架构?
破碎的天堂鸟
学习教程系统架构
设计可扩展的后端系统架构需综合考虑核心原则、架构模式、扩展策略、数据存储、容错机制及监控体系。以下是基于行业实践的详细指南:一、可扩展架构的核心原则无状态性(Statelessness)服务不保存客户端状态,请求可被任意实例处理,便于水平扩展。实现:通过负载均衡器(如Nginx、HAProxy)分发请求至多个无状态实例。松散耦合(LooseCoupling)模块间通过API或消息队列通信,减少依赖
- 一文详解:使用HTTPS有哪些优势?
JoySSL303
https网络协议httpssl网络
互联网发展到今天,HTTP协议的明文传输会让用户存在非常大的安全隐患。试想一下,假如你在一个HTTP协议的网站上面购物,你需要在页面上输入你的银行卡号和密码,然后你把数据提交到服务器实现购买。假如这个环节稍有不慎,你的传输数据被第三者给截获了,由于HTTP明文数据传输的原因,你的银行卡号和密码,将会被这个截获人所得到。现在你还敢在一个HTTP的网站上面购物吗?你还会在一个HTTP的网站上面留下你的
- 语言模型 RLHF 实践指南(一):策略网络、价值网络与 PPO 损失函数
在使用ProximalPolicyOptimization(PPO)对语言模型进行强化学习微调(如RLHF)时,大家经常会问:策略网络的动作概率是怎么来的?价值网络的得分是如何计算的?奖励从哪里来?损失函数怎么构建?微调后的旧轨迹还能用吗?这篇文章将以语言模型强化学习微调为例,结合实际实现和数学公式,深入解析PPO的关键计算流程。1️⃣策略网络:如何计算动作概率?策略网络πθ(a∣s)\pi_\t
- AI+区块链:代购系统如何破解碳足迹追踪“数据黑箱”?
绿色电商趋势:代购系统如何实现碳足迹追踪与可持续物流?在全球气候危机与可持续发展目标的双重驱动下,绿色电商正从概念走向实践。作为跨境电商的核心环节,代购系统如何通过技术创新实现碳足迹追踪与可持续物流,成为行业突破增长瓶颈、构建差异化竞争力的关键。本文结合技术架构、行业实践与未来趋势,解析代购系统在绿色转型中的路径选择。一、碳足迹追踪:从数据孤岛到全链路透明1.技术架构:区块链+IoT构建可信数据链
- Three.js 实现导出模型文件(.glb,.gltf)功能 GLTFExporter
Three.js提供了导出(.glb,.gltf)文件的APIGLTFExporter用于实现场景内容导出模型文件的功能导出模型文件主要使用parse方法,该方法接收三个参数:1.scene:要导出的场景对象。2.onComplete:解析完成后的回调函数,接收一个参数result,表示解析后的glTF数据。3.options:可选参数,用于配置导出的选项。下面是options的一些常用参数选项:
- python 包管理工具uv
uv--versionuvpythonfinduvpythonlistexportUV_DEFAULT_INDEX="https://mirrors.tuna.tsinghua.edu.cn/pypi/web/simple"#换成私有的repoexportUV_HTTP_TIMEOUT=120uvpythoninstall3.12uvvenvmyenv--python3.12--seeduvhtt
- [晕事]今天做了件晕事83: pen test
mzhan017
英语学习笔记晕事英语学习
这个缩写,就不能顾名思义了,而且pen是一个独立的单词,从读音上来说还容易和pain混淆,所以导致初接触者有些困扰。所以这个pentest的缩写,有些失败。全写是penetrationtest:渗透测试。https://en.wikipedia.org/wiki/Penetration_test修改建议是改成penetest,至少可以和pen在书写上区分,在读音是也可以区分,就读“排你test”。
- Android四大组件:Broadcast
giaoho
安卓开发学习android
Android四大组件:Broadcast-1.标准广播(Normalbroadcasts)执行特性:完全异步,广播发出后,所有接收器几乎同时接收,无先后顺序。效率与拦截:效率高,但无法被截断。流程:发出广播后,多个接收器同时接收,中“发出广播”向“广播接收器1、2、3”同时传递。有序广播(Orderedbroadcasts)执行特性:同步执行,同一时刻仅一个接收器接收,执行完逻辑后广播才继续传递
- Tamd Status Pages统一样式状态页模板库
https://github.com/alonehill/tamd-status-pageshttps://gitee.com/alonehill/tamd-status-pageshttps://github.com/alonehill/tamd-status-pages
- Python协程从入门到精通:9个案例解析yield、gevent与asyncio实战
python_chai
Pythonpython开发语言协程并发yield生成器gerrnletgevent
引言痛点分析:传统多线程在高并发场景下的性能瓶颈。协程优势:轻量级、高并发、低资源消耗。本文目标:通过9个代码案例,系统讲解协程的核心技术和应用场景。目录引言1.协程基础:理解yield生成器1.1yield的暂停与恢复机制1.2生产者-消费者模型实战1.3双向通信:send()方法详解2.手动协程控制:greenlet进阶2.1greenlet的显式切换原理2.2多任务协作案例3.自动化协程:g
- 数据结构:位图
顾小玙
数据结构算法
目录问题引入位图定义相关整型位操作疑点位运算C++库里的bitset实现应用优缺点问题引入有一道经典的面试题:有40亿个无序无符号整数,要求你高效判断一个数是否在这堆数中。想法一:暴力查找似乎能够解决问题,但显然找一次就要消耗O(N)的时间,这是不能接受的;想法二:问题的本质是查找,因此想到使用高效的二分查找:先进行一次O(NlogN)的排序,之后的每次查找都只要O(logN)。想法二的改进很不错
- IDEA Maven报错 无法解析 com.taobao:parent:pom:1.0.1【100%解决 此类型问题】
Dolphin_Home
私有_案例分析生产环境_场景抽象Debugintellij-ideamavenjava
IDEAMaven报错无法解析com.taobao:parent:pom:1.0.1【100%解决此类型问题】报错日志PSD:\Learn_Materials\IDEA_WorkSpace\Demo\spring_test_demo>mvncleaninstall-U[INFO]Scanningforprojects...[WARNING][WARNING]Someproblemswereenco
- 大模型中标斩获3项第一!
百度智能云
今年1-4月,百度智能云在主流大模型厂商中一举拿下三项第一!数量最多!中标项目数量7个!行业最全!覆盖最多行业6个!金额最高!中标金额总数最高5600万+南方电网、泰康保险、北京车网、中华总工会、上海城投污水处理有限公司等行业头部客户,纷纷与百度智能云达成合作,体现出大模型技术在政策、市场的双轮驱动下的强劲增长态势。百度智能云将继续深化与行业客户合作,共同探索大模型技术在各行业的应用场景,推动行业
- c语言逻辑运算符编程,C语言之逻辑运算符详解
湛蓝色的迷惘
c语言逻辑运算符编程
一逻辑运算符:&&:逻辑与,读作并且表达式左右两边都为真,那么结果才为真口诀:一假则假||:逻辑或,读作或者表达式左右两边,有一个为真,那么结果就为真口诀:一真则真!:逻辑非,读作取反表达式的结果如果为假,就变成真,如果为真,就变成假口诀:真变假,假变真二逻辑运算符的短路问题tips:非0为真,0为假短路的情况:&&:左边如果为假,则右边短路(右边不会被执行)||:左边如果为真,则右边短路(右边不
- PHP安全编程实践系列(三):安全会话管理与防护策略
软考和人工智能学堂
php#php程序设计经验php安全开发语言
前言会话管理是Web应用安全的核心环节,不安全的会话实现可能导致用户账户被劫持、敏感数据泄露等严重后果。本文将深入探讨PHP中的会话安全机制,分析常见会话攻击手段,并提供全面的防护策略和实践方案。一、会话安全基础1.1PHP会话机制工作原理理论:PHP会话是通过会话ID(SessionID)在服务器和客户端之间维持状态的一种机制。关键流程包括:会话初始化:session_start()调用会话ID
- Python异步编程终极指南:用协程与事件循环重构你的高并发系统
title:Python异步编程终极指南:用协程与事件循环重构你的高并发系统date:2025/2/24updated:2025/2/24author:cmdragonexcerpt:深入剖析Python异步编程的核心机制。你将掌握:\n事件循环的底层实现原理与调度算法\nasync/await协程的6种高级用法模式\n异步HTTP请求的性能优化技巧(速度提升15倍+)\n常见异步陷阱的26种解决
- python 异步编程:协程与 asyncio
花_城
Python开发语言后端异步协程
文章目录一、协程(coroutine)1.1协程的概念1.2实现协程的方式二、asyncio异步编程2.1事件循环2.2快速上手2.3运行协程2.4await关键字2.5可等待对象2.5.1协程2.5.2任务(Task)2.5.3asyncio.Future三、concurrent.futures.Future(补充)3.1爬虫案例(asyncio+不支持异步的模块)四、asyncio异步迭代器五
- Three.js实现海洋与天空
Three.js实现海洋与天空https://threehub.cn/#/codeMirror?navigation=ThreeJS&classify=shader&id=waterSkyimport*asTHREEfrom"three";import{OrbitControls}from'three/examples/jsm/controls/OrbitControls.js'constDOM=
- Three.js引擎开发:Three.js动画系统实现_(9).Three.js中的骨骼动画实现
chenlz2007
游戏开发javascriptnginx开发语言vr性能优化ecmascript前端
Three.js中的骨骼动画实现在上一节中,我们介绍了如何在Three.js中加载和显示3D模型。接下来,我们将深入探讨如何在Three.js中实现骨骼动画。骨骼动画是一种高级的动画技术,它通过控制模型的骨骼来驱动模型的动画,广泛应用于虚拟角色的动画制作。在本节中,我们将学习如何在Three.js中实现骨骼动画,包括骨骼动画的基本原理、如何加载带有骨骼的模型、如何创建和控制动画混合器(Animat
- 突破性能瓶颈,几个高性能Python网络框架,高效实现网络应用
引言随着互联网和大数据时代的到来,高性能网络应用的需求日益增加。Python作为一种流行的编程语言,在高性能网络编程领域也具有广泛的应用。本文将深入探讨基于Python的几种高性能网络框架,分析它们各自的优势和适用场景,帮助开发者选择最适合自己需求的网络框架这里插播一条粉丝福利,如果你正在学习Python或者有计划学习Python,想要突破自我,对未来十分迷茫的,可以点击这里获取最新的Python
- Python面试题:Python中的异步编程:详细讲解asyncio库的使用
超哥同学
Python系列python开发语言面试编程
Python的异步编程是实现高效并发处理的一种方法,它使得程序能够在等待I/O操作时继续执行其他任务。在Python中,asyncio库是实现异步编程的主要工具。asyncio提供了一种机制来编写可以在单线程内并发执行的代码,适用于I/O密集型任务。以下是对asyncio库的详细讲解,包括基本概念、用法、示例以及注意事项。1.基本概念1.1协程(Coroutines)协程是一个特殊的函数,它可以被
- 新手向:实现验证码程序
nightunderblackcat
Java新手开发语言javamavenspringintellij-ideaspringbootspringcloud
本文将从零开始,通过一个简单的验证码程序。即使你没有任何编程基础,也能跟着这篇文章一步步学习。第一章:Java开发环境搭建1.1安装JDK要开始Java编程,首先需要安装Java开发工具包(JDK)。JDK是Java开发的核心,包含了运行Java程序所需的工具和库。访问Oracle官网下载适合你操作系统的JDK运行安装程序,按照提示完成安装配置环境变量(这一步很重要,确保你可以在任何目录下运行Ja
- Linux守护进程
不脱发的程序猿
嵌入式Linux“望闻问切“linux嵌入式
目录1、编写守护进程的步骤2、守护进程的使用和案例设计2.1、案例功能分析2.2、守护进程代码结构2.3、代码实现2.4、代码详解3、编译和运行守护进程4、检查守护进程5、停止守护进程守护进程(Daemon)是一种在后台运行的特殊进程,通常用于执行系统服务、管理任务或处理请求。它们具有几个显著的特征,使其在系统中扮演重要角色。主要特征:长期运行:守护进程通常在系统启动时启动,并会持续运行,直至系统
- Python 爬虫实战:如何搭建高效的分布式爬虫架构,突破数据抓取极限
程序员威哥
python爬虫分布式
随着互联网数据量的飞速增长,单一爬虫在抓取大量数据时的效率和稳定性往往无法满足需求。在这种情况下,分布式爬虫架构应运而生。分布式爬虫通过多节点并行工作,可以大大提高数据抓取的速度,同时减少单点故障的风险。本文将深入探讨如何使用Python构建一个高效的分布式爬虫架构,从架构设计到技术实现,帮助你突破数据抓取的极限。一、什么是分布式爬虫?分布式爬虫系统将爬虫任务拆分为多个子任务,分布到不同的服务器或
- 一文搞懂 Cursor 内部工作原理~
zz_jesse
介绍了Cursor,一个结合了AI技术的代码编辑器,它通过深度学习和语义索引的方式,提升了开发者的工作效率。Cursor通过与VSCode相似的界面和功能,以及自己的AI特性,实现了代码的智能化编辑和错误检查。译文从这开始~~你可能已经看到新闻:OpenAI正以高达30亿美元的价格收购Windsurf!与此同时,Cursor的母公司Anysphere也正在以90亿美元估值融资9亿美元!这对于代码生
- 量子传感探针:金刚石NV色心实现细胞级磁弹性成像(分辨率10nm)技术解析
百态老人
人工智能
一、技术原理与核心突破金刚石氮-空位色心(NV色心)作为原子级量子传感器,其磁弹性成像能力源于电子自旋态与环境磁场的量子相干相互作用,结合纳米探针技术实现细胞级分辨率。核心技术原理包括:1.NV色心量子传感机制磁弹性耦合模型:NV色心的自旋哈密顿量可表示为:H=DSz2+γeB⋅S+λϵ⋅SH=DS_z^2+\gamma_e\mathbf{B}\cdot\mathbf{S}+\lambda\mat
- Hanbit便携式GIS局部放电检测仪中PRPD图的绘制方法研究
Hanbit便携式GIS局部放电检测仪中PRPD图的绘制方法研究摘要本报告详细阐述了韩国HanbitPoDAS便携式GIS局部放电检测仪软件中相分辨局部放电(PRPD)图的生成方法。报告旨在阐明其技术原理、数据采集、信号处理以及分析功能,这些功能共同实现了对气体绝缘开关设备(GIS)绝缘状态的精确评估。HanbitPoDAS系统利用超高频(UHF)传感器和智能软件算法来捕获、处理并显示PRPD模式
- 如何让AI真正理解你的意图(自适应Prompt实战指南)
nine是个工程师
大语言模型人工智能prompt
目前的LLM模型,在理解用户意图方面,正在使用自适应Prompt技术,来提升模型的理解能力。目前使用deepseek推理模型能明显看到自适应的一个过程。前言:为什么你的AI总是"答非所问"?相信很多人都遇到过这样的情况:你问:“帮我写一个Python爬虫”AI答:给你一堆理论知识和完整教程(你只想要简单代码)你问:“推荐一部电影”AI答:推荐了《教父》(你想看轻松喜剧)你问:“解释一下机器学习”A
- 强大的销售团队背后 竟然是大数据分析的身影
蓝儿唯美
数据分析
Mark Roberge是HubSpot的首席财务官,在招聘销售职位时使用了大量数据分析。但是科技并没有挤走直觉。
大家都知道数理学家实际上已经渗透到了各行各业。这些热衷数据的人们通过处理数据理解商业流程的各个方面,以重组弱点,增强优势。
Mark Roberge是美国HubSpot公司的首席财务官,HubSpot公司在构架集客营销现象方面出过一份力——因此他也是一位数理学家。他使用数据分析
- Haproxy+Keepalived高可用双机单活
bylijinnan
负载均衡keepalivedhaproxy高可用
我们的应用MyApp不支持集群,但要求双机单活(两台机器:master和slave):
1.正常情况下,只有master启动MyApp并提供服务
2.当master发生故障时,slave自动启动本机的MyApp,同时虚拟IP漂移至slave,保持对外提供服务的IP和端口不变
F5据说也能满足上面的需求,但F5的通常用法都是双机双活,单活的话还没研究过
服务器资源
10.7
- eclipse编辑器中文乱码问题解决
0624chenhong
eclipse乱码
使用Eclipse编辑文件经常出现中文乱码或者文件中有中文不能保存的问题,Eclipse提供了灵活的设置文件编码格式的选项,我们可以通过设置编码 格式解决乱码问题。在Eclipse可以从几个层面设置编码格式:Workspace、Project、Content Type、File
本文以Eclipse 3.3(英文)为例加以说明:
1. 设置Workspace的编码格式:
Windows-&g
- 基础篇--resources资源
不懂事的小屁孩
android
最近一直在做java开发,偶尔敲点android代码,突然发现有些基础给忘记了,今天用半天时间温顾一下resources的资源。
String.xml 字符串资源 涉及国际化问题
http://www.2cto.com/kf/201302/190394.html
string-array
- 接上篇补上window平台自动上传证书文件的批处理问卷
酷的飞上天空
window
@echo off
: host=服务器证书域名或ip,需要和部署时服务器的域名或ip一致 ou=公司名称, o=公司名称
set host=localhost
set ou=localhost
set o=localhost
set password=123456
set validity=3650
set salias=s
- 企业物联网大潮涌动:如何做好准备?
蓝儿唯美
企业
物联网的可能性也许是无限的。要找出架构师可以做好准备的领域然后利用日益连接的世界。
尽管物联网(IoT)还很新,企业架构师现在也应该为一个连接更加紧密的未来做好计划,而不是跟上闸门被打开后的集成挑战。“问题不在于物联网正在进入哪些领域,而是哪些地方物联网没有在企业推进,” Gartner研究总监Mike Walker说。
Gartner预测到2020年物联网设备安装量将达260亿,这些设备在全
- spring学习——数据库(mybatis持久化框架配置)
a-john
mybatis
Spring提供了一组数据访问框架,集成了多种数据访问技术。无论是JDBC,iBATIS(mybatis)还是Hibernate,Spring都能够帮助消除持久化代码中单调枯燥的数据访问逻辑。可以依赖Spring来处理底层的数据访问。
mybatis是一种Spring持久化框架,要使用mybatis,就要做好相应的配置:
1,配置数据源。有很多数据源可以选择,如:DBCP,JDBC,aliba
- Java静态代理、动态代理实例
aijuans
Java静态代理
采用Java代理模式,代理类通过调用委托类对象的方法,来提供特定的服务。委托类需要实现一个业务接口,代理类返回委托类的实例接口对象。
按照代理类的创建时期,可以分为:静态代理和动态代理。
所谓静态代理: 指程序员创建好代理类,编译时直接生成代理类的字节码文件。
所谓动态代理: 在程序运行时,通过反射机制动态生成代理类。
一、静态代理类实例:
1、Serivce.ja
- Struts1与Struts2的12点区别
asia007
Struts1与Struts2
1) 在Action实现类方面的对比:Struts 1要求Action类继承一个抽象基类;Struts 1的一个具体问题是使用抽象类编程而不是接口。Struts 2 Action类可以实现一个Action接口,也可以实现其他接口,使可选和定制的服务成为可能。Struts 2提供一个ActionSupport基类去实现常用的接口。即使Action接口不是必须实现的,只有一个包含execute方法的P
- 初学者要多看看帮助文档 不要用js来写Jquery的代码
百合不是茶
jqueryjs
解析json数据的时候需要将解析的数据写到文本框中, 出现了用js来写Jquery代码的问题;
1, JQuery的赋值 有问题
代码如下: data.username 表示的是: 网易
$("#use
- 经理怎么和员工搞好关系和信任
bijian1013
团队项目管理管理
产品经理应该有坚实的专业基础,这里的基础包括产品方向和产品策略的把握,包括设计,也包括对技术的理解和见识,对运营和市场的敏感,以及良好的沟通和协作能力。换言之,既然是产品经理,整个产品的方方面面都应该能摸得出门道。这也不懂那也不懂,如何让人信服?如何让自己懂?就是不断学习,不仅仅从书本中,更从平时和各种角色的沟通
- 如何为rich:tree不同类型节点设置右键菜单
sunjing
contextMenutreeRichfaces
组合使用target和targetSelector就可以啦,如下: <rich:tree id="ruleTree" value="#{treeAction.ruleTree}" var="node" nodeType="#{node.type}"
selectionChangeListener=&qu
- 【Redis二】Redis2.8.17搭建主从复制环境
bit1129
redis
开始使用Redis2.8.17
Redis第一篇在Redis2.4.5上搭建主从复制环境,对它的主从复制的工作机制,真正的惊呆了。不知道Redis2.8.17的主从复制机制是怎样的,Redis到了2.4.5这个版本,主从复制还做成那样,Impossible is nothing! 本篇把主从复制环境再搭一遍看看效果,这次在Unbuntu上用官方支持的版本。 Ubuntu上安装Red
- JSONObject转换JSON--将Date转换为指定格式
白糖_
JSONObject
项目中,经常会用JSONObject插件将JavaBean或List<JavaBean>转换为JSON格式的字符串,而JavaBean的属性有时候会有java.util.Date这个类型的时间对象,这时JSONObject默认会将Date属性转换成这样的格式:
{"nanos":0,"time":-27076233600000,
- JavaScript语言精粹读书笔记
braveCS
JavaScript
【经典用法】:
//①定义新方法
Function .prototype.method=function(name, func){
this.prototype[name]=func;
return this;
}
//②给Object增加一个create方法,这个方法创建一个使用原对
- 编程之美-找符合条件的整数 用字符串来表示大整数避免溢出
bylijinnan
编程之美
import java.util.LinkedList;
public class FindInteger {
/**
* 编程之美 找符合条件的整数 用字符串来表示大整数避免溢出
* 题目:任意给定一个正整数N,求一个最小的正整数M(M>1),使得N*M的十进制表示形式里只含有1和0
*
* 假设当前正在搜索由0,1组成的K位十进制数
- 读书笔记
chengxuyuancsdn
读书笔记
1、Struts访问资源
2、把静态参数传递给一个动作
3、<result>type属性
4、s:iterator、s:if c:forEach
5、StringBuilder和StringBuffer
6、spring配置拦截器
1、访问资源
(1)通过ServletActionContext对象和实现ServletContextAware,ServletReque
- [通讯与电力]光网城市建设的一些问题
comsci
问题
信号防护的问题,前面已经说过了,这里要说光网交换机与市电保障的关系
我们过去用的ADSL线路,因为是电话线,在小区和街道电力中断的情况下,只要在家里用笔记本电脑+蓄电池,连接ADSL,同样可以上网........
- oracle 空间RESUMABLE
daizj
oracle空间不足RESUMABLE错误挂起
空间RESUMABLE操作 转
Oracle从9i开始引入这个功能,当出现空间不足等相关的错误时,Oracle可以不是马上返回错误信息,并回滚当前的操作,而是将操作挂起,直到挂起时间超过RESUMABLE TIMEOUT,或者空间不足的错误被解决。
这一篇简单介绍空间RESUMABLE的例子。
第一次碰到这个特性是在一次安装9i数据库的过程中,在利用D
- 重构第一次写的线程池
dieslrae
线程池 python
最近没有什么学习欲望,修改之前的线程池的计划一直搁置,这几天比较闲,还是做了一次重构,由之前的2个类拆分为现在的4个类.
1、首先是工作线程类:TaskThread,此类为一个工作线程,用于完成一个工作任务,提供等待(wait),继续(proceed),绑定任务(bindTask)等方法
#!/usr/bin/env python
# -*- coding:utf8 -*-
- C语言学习六指针
dcj3sjt126com
c
初识指针,简单示例程序:
/*
指针就是地址,地址就是指针
地址就是内存单元的编号
指针变量是存放地址的变量
指针和指针变量是两个不同的概念
但是要注意: 通常我们叙述时会把指针变量简称为指针,实际它们含义并不一样
*/
# include <stdio.h>
int main(void)
{
int * p; // p是变量的名字, int *
- yii2 beforeSave afterSave beforeDelete
dcj3sjt126com
delete
public function afterSave($insert, $changedAttributes)
{
parent::afterSave($insert, $changedAttributes);
if($insert) {
//这里是新增数据
} else {
//这里是更新数据
}
}
- timertask
shuizhaosi888
timertask
java.util.Timer timer = new java.util.Timer(true);
// true 说明这个timer以daemon方式运行(优先级低,
// 程序结束timer也自动结束),注意,javax.swing
// 包中也有一个Timer类,如果import中用到swing包,
// 要注意名字的冲突。
TimerTask task = new
- Spring Security(13)——session管理
234390216
sessionSpring Security攻击保护超时
session管理
目录
1.1 检测session超时
1.2 concurrency-control
1.3 session 固定攻击保护
- 公司项目NODEJS实践0.3[ mongo / session ...]
逐行分析JS源代码
mongodbsessionnodejs
http://www.upopen.cn
一、前言
书接上回,我们搭建了WEB服务端路由、模板等功能,完成了register 通过ajax与后端的通信,今天主要完成数据与mongodb的存取,实现注册 / 登录 /
- pojo.vo.po.domain区别
LiaoJuncai
javaVOPOJOjavabeandomain
POJO = "Plain Old Java Object",是MartinFowler等发明的一个术语,用来表示普通的Java对象,不是JavaBean, EntityBean 或者 SessionBean。POJO不但当任何特殊的角色,也不实现任何特殊的Java框架的接口如,EJB, JDBC等等。
即POJO是一个简单的普通的Java对象,它包含业务逻辑
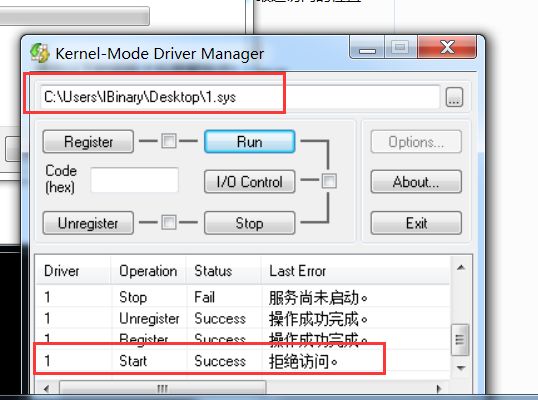
- Windows Error Code
OhMyCC
windows
0 操作成功完成.
1 功能错误.
2 系统找不到指定的文件.
3 系统找不到指定的路径.
4 系统无法打开文件.
5 拒绝访问.
6 句柄无效.
7 存储控制块被损坏.
8 存储空间不足, 无法处理此命令.
9 存储控制块地址无效.
10 环境错误.
11 试图加载格式错误的程序.
12 访问码无效.
13 数据无效.
14 存储器不足, 无法完成此操作.
15 系
- 在storm集群环境下发布Topology
roadrunners
集群stormtopologyspoutbolt
storm的topology设计和开发就略过了。本章主要来说说如何在storm的集群环境中,通过storm的管理命令来发布和管理集群中的topology。
1、打包
打包插件是使用maven提供的maven-shade-plugin,详细见maven-shade-plugin。
<plugin>
<groupId>org.apache.maven.
- 为什么不允许代码里出现“魔数”
tomcat_oracle
java
在一个新项目中,我最先做的事情之一,就是建立使用诸如Checkstyle和Findbugs之类工具的准则。目的是制定一些代码规范,以及避免通过静态代码分析就能够检测到的bug。 迟早会有人给出案例说这样太离谱了。其中的一个案例是Checkstyle的魔数检查。它会对任何没有定义常量就使用的数字字面量给出警告,除了-1、0、1和2。 很多开发者在这个检查方面都有问题,这可以从结果
- zoj 3511 Cake Robbery(线段树)
阿尔萨斯
线段树
题目链接:zoj 3511 Cake Robbery
题目大意:就是有一个N边形的蛋糕,切M刀,从中挑选一块边数最多的,保证没有两条边重叠。
解题思路:有多少个顶点即为有多少条边,所以直接按照切刀切掉点的个数排序,然后用线段树维护剩下的还有哪些点。
#include <cstdio>
#include <cstring>
#include <vector&