Shiro(三) - SSM 整合实例 - 附数据库和完整 Demo
文章目录
- 简述
- 数据库设计
- maven
- 配置文件
- 编写 applicationContext-shiro.xml
- web.xml
- springMVC.xml
- 具体代码实现
- 搭建 SSM 基本项目结构
- DatabaseRealm 类
- DefaultExceptionHandler 类
- URLPathMatchingFilter 类
- 登录验证
- User 用户管理的实现
- 完整 Demo,内附数据库
- 参考教程
简述
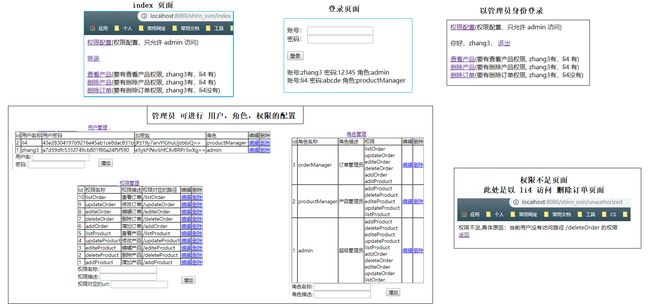
此处用一个实例模拟以下场景,以此来实现 shiro 和 ssm 的整合。
用户:zhang3,密码:12345,角色:admin(管理员)
用户:li4,密码:abcde,角色:productManager(产品经理)
权限:管理员什么都能做,产品经理只能做产品管理(产品的增删改查),订单经理只能做订单管理(订单的增删改查)
数据库设计
3 张基础表:用户,角色,权限。
2 张中间表:建立「用户与角色的多对多关系」,「角色与权限的多对多关系」。 用户与权限之间也是多对多关系,但是是通过角色间接建立的。
maven
<dependency>
<groupId>org.apache.shirogroupId>
<artifactId>shiro-allartifactId>
<version>1.2.5version>
dependency>
配置文件
在常规 SSM 配置文件的基础上增加了如下配置:
编写 applicationContext-shiro.xml
<beans xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns="http://www.springframework.org/schema/beans" xmlns:util="http://www.springframework.org/schema/util"
xsi:schemaLocation="http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans-4.0.xsd
http://www.springframework.org/schema/util
http://www.springframework.org/schema/util/spring-util.xsd">
<bean id="urlPathMatchingFilter" class="top.qingrang.filter.URLPathMatchingFilter"/>
<bean id="shiroFilter" class="org.apache.shiro.spring.web.ShiroFilterFactoryBean">
<property name="securityManager" ref="securityManager"/>
<property name="loginUrl" value="/login"/>
<property name="unauthorizedUrl" value="/unauthorized"/>
<property name="filters">
<util:map>
<entry key="logout" value-ref="logoutFilter"/>
<entry key="url" value-ref="urlPathMatchingFilter"/>
util:map>
property>
<property name="filterChainDefinitions">
<value>
/login=anon
/index=anon
/static/**=anon
/admin/**=roles[admin]
/doLogout=logout
/** = url
value>
property>
bean>
<bean id="logoutFilter" class="org.apache.shiro.web.filter.authc.LogoutFilter">
<property name="redirectUrl" value="/index"/>
bean>
<bean id="sessionIdGenerator" class="org.apache.shiro.session.mgt.eis.JavaUuidSessionIdGenerator"/>
<bean id="sessionIdCookie" class="org.apache.shiro.web.servlet.SimpleCookie">
<constructor-arg value="sid"/>
<property name="httpOnly" value="true"/>
<property name="maxAge" value="-1"/>
bean>
<bean id="sessionDAO" class="org.apache.shiro.session.mgt.eis.EnterpriseCacheSessionDAO">
<property name="sessionIdGenerator" ref="sessionIdGenerator"/>
bean>
<bean name="sessionValidationScheduler" class="org.apache.shiro.session.mgt.ExecutorServiceSessionValidationScheduler">
<property name="interval" value="1800000"/>
<property name="sessionManager" ref="sessionManager"/>
bean>
<bean id="sessionManager"
class="org.apache.shiro.web.session.mgt.DefaultWebSessionManager">
<property name="globalSessionTimeout" value="1800000"/>
<property name="deleteInvalidSessions" value="true"/>
<property name="sessionValidationSchedulerEnabled" value="true"/>
<property name="sessionValidationScheduler" ref="sessionValidationScheduler"/>
<property name="sessionDAO" ref="sessionDAO"/>
<property name="sessionIdCookieEnabled" value="true"/>
<property name="sessionIdCookie" ref="sessionIdCookie"/>
bean>
<bean class="org.springframework.beans.factory.config.MethodInvokingFactoryBean">
<property name="staticMethod" value="org.apache.shiro.SecurityUtils.setSecurityManager"/>
<property name="arguments" ref="securityManager"/>
bean>
<bean id="credentialsMatcher" class="org.apache.shiro.authc.credential.HashedCredentialsMatcher">
<property name="hashAlgorithmName" value="md5"/>
<property name="hashIterations" value="2"/>
<property name="storedCredentialsHexEncoded" value="true"/>
bean>
<bean id="databaseRealm" class="top.qingrang.realm.DatabaseRealm">
<property name="credentialsMatcher" ref="credentialsMatcher"/>
bean>
<bean id="securityManager" class="org.apache.shiro.web.mgt.DefaultWebSecurityManager">
<property name="realm" ref="databaseRealm"/>
<property name="sessionManager" ref="sessionManager"/>
bean>
<bean id="lifecycleBeanPostProcessor" class="org.apache.shiro.spring.LifecycleBeanPostProcessor"/>
beans>
web.xml
- 添加 Shiro 配置,使用 shiro 过滤器
<filter>
<filter-name>shiroFilterfilter-name>
<filter-class>org.springframework.web.filter.DelegatingFilterProxyfilter-class>
<init-param>
<param-name>targetFilterLifecycleparam-name>
<param-value>trueparam-value>
init-param>
filter>
<filter-mapping>
<filter-name>shiroFilterfilter-name>
<url-pattern>/*url-pattern>
filter-mapping>
- 指明 applicationContext-shiro.xml 配置文件的位置
classpath:applicationContext-shiro.xml
springMVC.xml
- 启用 shiro 注解
<bean class="org.springframework.aop.framework.autoproxy.DefaultAdvisorAutoProxyCreator"
depends-on="lifecycleBeanPostProcessor">
<property name="proxyTargetClass" value="true"/>
bean>
<bean class="org.apache.shiro.spring.security.interceptor.AuthorizationAttributeSourceAdvisor">
<property name="securityManager" ref="securityManager"/>
bean>
- 控制器异常处理
<bean id="exceptionHandlerExceptionResolver"
class="org.springframework.web.servlet.mvc.method.annotation.ExceptionHandlerExceptionResolver">
bean>
<bean class="top.qingrang.exception.DefaultExceptionHandler"/>
具体代码实现
搭建 SSM 基本项目结构
编写 controller,pojo,service 等,还有相关的 jsp 页面。
DatabaseRealm 类
通过数据库,验证用户,和相关授权的类,继承自 AuthorizingRealm,需重写 doGetAuthenticationInfo 和doGetAuthorizationInfo 两个方法。
DatabaseRealm 类,由 Shiro 调用,在 applicationContext-shiro.xml 中配置。
public class DatabaseRealm extends AuthorizingRealm {
@Autowired
IUserService userService;
@Autowired
IPermissionService permissionService;
@Autowired
IRoleService roleService;
/**
* 验证
*/
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken authenticationToken) throws AuthenticationException {
// 获取输入用户的账号和密码
UsernamePasswordToken upToken = (UsernamePasswordToken) authenticationToken;
String name = upToken.getPrincipal().toString();
// 获取指定用户数据库中的密码,盐
User user = userService.getUserByName(name);
String pwdInDB = user.getPassword();
String salt = user.getSalt();
// 认证信息,存放账号,密码,盐,getName() 是当前 Realm 的继承方法,通常返回当前类名 :databaseRealm
// 通过 applicationContext-shiro.xml 里配置的 HashedCredentialsMatcher 进行自动校验
SimpleAuthenticationInfo authenticationInfo = new SimpleAuthenticationInfo(
name,pwdInDB, ByteSource.Util.bytes(salt),getName());
return authenticationInfo;
}
/**
* 授权
*/
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
// 能进入到这里,表示账号已经通过验证了
String name = (String) principalCollection.getPrimaryPrincipal();
// 获取账号的角色和权限信息
Set<String> roles = roleService.listRoleName(name);
Set<String> permissions = permissionService.listPermissionName(name);
// 授权对象信息
SimpleAuthorizationInfo authorizationInfo = new SimpleAuthorizationInfo();
authorizationInfo.setStringPermissions(permissions);
authorizationInfo.setRoles(roles);
return authorizationInfo;
}
}
DefaultExceptionHandler 类
异常处理,在 springMVC.xml 中声明使用。
/**
* 异常处理
* 当发生 UnauthorizedException 异常的时候,就表示访问了无授权的资源,那么就会跳转到 unauthorized.jsp,
* DefaultExceptionHandler 的使用,在 springMVC.xml 中声明
*/
@ControllerAdvice
public class DefaultExceptionHandler {
@ExceptionHandler({UnauthorizedException.class})
@ResponseStatus(HttpStatus.UNAUTHORIZED)
public ModelAndView processUnauthenticatedException(NativeWebRequest request, UnauthorizedException e) {
ModelAndView mv = new ModelAndView();
mv.addObject("ex", e); // 在 unauthorized.jsp 中就会把错误信息通过变量 ex 取出来。
mv.setViewName("unauthorized");
return mv;
}
}
springMVC.xml
<bean id="exceptionHandlerExceptionResolver" class="org.springframework.web.servlet.mvc.method.annotation.ExceptionHandlerExceptionResolver">
bean>
<bean class="top.qingrang.exception.DefaultExceptionHandler"/>
URLPathMatchingFilter 类
PathMatchingFilter 是 shiro 内置过滤器。
基本思路如下:
- 如果没登录就跳转到登录页面
- 如果当前访问路径没有在权限系统里维护,则允许访问
- 当前用户所拥有的权限如何不包含当前的访问地址,则跳转到 / unauthorized,否则就允许访问
public class URLPathMatchingFilter extends PathMatchingFilter {
@Autowired
IPermissionService permissionService;
@Override
protected boolean onPreHandle(ServletRequest request, ServletResponse response, Object mappedValue) throws Exception {
// 当前请求的 URL
String requestURI = getPathWithinApplication(request);
// 获取 subject 对象
Subject subject = SecurityUtils.getSubject();
// 如果没有登录,就跳转到登录页面
if (!subject.isAuthenticated()) {
WebUtils.issueRedirect(request, response, "/login");
return false;
}
// 看看这个路径权限里有没有维护,如果没有维护,一律放行(也可以改为一律不放行)
boolean needInterceptor = permissionService.needInterceptor(requestURI);
if (needInterceptor) { // 需要拦截
boolean hasPermission = false;
String userName = subject.getPrincipal().toString();
Set<String> permissionUrls = permissionService.listPermissionURLs(userName);
for (String url : permissionUrls) {
// 这就表示当前用户有这个权限
if (url.equals(requestURI)) {
hasPermission = true;
break;
}
}
if (hasPermission){
return true;
}else {
UnauthorizedException ex = new UnauthorizedException("当前用户没有访问路径 " + requestURI + " 的权限");
subject.getSession().setAttribute("ex", ex);
WebUtils.issueRedirect(request, response, "/unauthorized");
return false;
}
} else {
return true; // 不需要拦截
}
}
}
登录验证
public class LoginController {
/**
* 登录,获取账号密码进行验证
*/
@RequestMapping(value = "/login", method = RequestMethod.POST)
public String login(Model model, String name, String password) {
Subject subject = SecurityUtils.getSubject();
UsernamePasswordToken token = new UsernamePasswordToken(name, password);
try {
subject.login(token);
Session session = subject.getSession();
session.setAttribute("subject", subject);
return "redirect:index";
} catch (AuthenticationException e) {
model.addAttribute("error", "验证失败");
return "login";
}
}
}
User 用户管理的实现
用户,权限,角色这三者的实现方式都差不多,这里只针对用户管理进行说明。
实现了 User 基本的增删改查功能。
IUserService.java
public interface IUserService {
User getUserByName(String name);
List<User> listUser();
void addUser(User user);
void deleteUser(long id);
User getUserByID(long id);
void updateUser(User user);
}
UserServiceImpl.java
@Service
public class UserServiceImpl implements IUserService {
@Autowired
IUserDao userDao;
@Override
public User getUserByName(String name) {
return userDao.getUserByName(name);
}
@Override
public List<User> listUser() {
return userDao.selectUserList();
}
@Override
public void addUser(User user) {
userDao.insertUser(user);
}
@Override
public void deleteUser(long id) {
userDao.deleteUser(id);
}
@Override
public User getUserByID(long id) {
return userDao.getUserByID(id);
}
@Override
public void updateUser(User user) {
userDao.updateUser(user);
}
}
IUSerDao.java
public interface IUserDao {
User getUserByName(String name);
List<User> selectUserList();
void insertUser(User user);
void deleteUser(long id);
User getUserByID(long id);
void updateUser(User user);
}
IUSerDao.xml
<mapper namespace="top.qingrang.dao.IUserDao">
<select id="getUserByName" resultType="User">
SELECT * FROM user WHERE name = #{name}
select>
<select id="getUserByID" resultType="User">
SELECT * FROM user WHERE id = #{id}
select>
<select id="selectUserList" resultType="User">
select * from USER order by id desc;
select>
<insert id="insertUser">
INSERT into user(name,password,salt) VALUES (#{name},#{password},#{salt})
insert>
<delete id="deleteUser">
DELETE FROM user WHERE id = #{id}
delete>
<update id="updateUser">
UPDATE user set name=#{name},password=#{password},salt=#{salt} WHERE id = #{id}
update>
mapper>
UserController.java
@Controller
@RequestMapping("admin")
public class UserController {
@Autowired
IUserRoleService userRoleService;
@Autowired
IUserService userService;
@Autowired
IRoleService roleService;
/**
* 用户列表
*/
@RequestMapping("listUser")
public String list(Model model) {
List<User> listUser = userService.listUser();
model.addAttribute("listUser", listUser);
// 一个用户对应一堆角色
Map<User, List<Role>> user_roles = new HashMap<>();
for (User user : listUser) {
List<Role> roles = roleService.listRoleByUser(user);
user_roles.put(user, roles);
}
model.addAttribute("user_roles", user_roles);
return "listUser";
}
/**
* 添加用户
*/
@RequestMapping("addUser")
public String add(Model model, String name, String password) {
String salt = new SecureRandomNumberGenerator().nextBytes().toString(); // 盐
int times = 2; // 加盐次数
String algorithmName = "md5"; // MD5 加密
// 加密 密码
String encodedPassword = new SimpleHash(algorithmName, password, salt, times).toString();
// 添加用户
User user = new User();
user.setName(name);
user.setPassword(encodedPassword);
user.setSalt(salt);
userService.addUser(user);
return "redirect:listUser";
}
/**
* 更改用户,页面
*/
@RequestMapping("editUser")
public String edit(Model model, long id) {
List<Role> listRole = roleService.listRole();
model.addAttribute("listRole", listRole);
User user = userService.getUserByID(id);
model.addAttribute("user", user);
List<Role> roles = roleService.listRoleByUser(user);
model.addAttribute("currentRoles", roles);
return "editUser";
}
/**
* 更改用户,实现
*/
@RequestMapping("updateUser")
public String update(User user, long[] roleIds) {
// 修改 用户角色 表
userRoleService.editUserRole(user, roleIds);
// 修改密码
String password = user.getPassword();
// 如果在修改的时候没有设置密码,就表示不改动密码
if (user.getPassword().length() != 0) {
String salt = new SecureRandomNumberGenerator().nextBytes().toString();
int times = 2;
String algorithmName = "md5";
String encodedPassword = new SimpleHash(algorithmName, password, salt, times).toString();
user.setSalt(salt);
user.setPassword(encodedPassword);
} else{
User u = userService.getUserByID(user.getId());
user.setPassword(u.getPassword());
user.setSalt(u.getSalt());
}
// 修改用户信息
userService.updateUser(user);
return "redirect:listUser";
}
/**
* 删除用户
*/
@RequestMapping("deleteUser")
public String delete(long id) {
userService.deleteUser(id);
return "redirect:listUser";
}
}
完整 Demo,内附数据库
https://github.com/SSGamble/shiro_ssm.git
参考教程
http://how2j.cn?p=10400