上次给大家说过IPSca ×××的配置方法 这次我将Cisco SSL ×××的配置。如下所示:
Cisco SSL ××× 配置实例
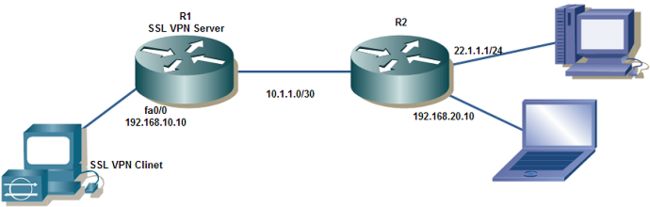
一、 网络拓扑图
二、SSL ××× Server 配置
软件版本: Cisco IOS Software, 7200 Software (C7200-ADVSECURITYK9-M), Version 12.4(9)T1, RELEASE SOFTWARE (fc2)
××× 客户端软件:sslclient-win- 1.1.2 .169.pkg
1、格式化 disk0
R1#format disk0:
Format operation may take a while. Continue? [confirm]
Format operation will destroy all data in "disk0:". Continue? [confirm]
Format: Drive communication & 1st Sector Write OK...
Writing Monlib sectors.
........................................................................................
Monlib write complete
Format: All system sectors written. OK...
Format: Total sectors in formatted partition: 8009
Format: Total bytes in formatted partition: 4100608
Format: Operation completed successfully.
Format of disk0 complete
2、上传软件
R1#copy tftp disk0:
Address or name of remote host []? 192.168.10.100
Source filename []? sslclient-win- 1.1.2 .169.pkg
Destination filename [sslclient-win-1.1.2.169.pkg]?
Accessing tftp://192.168.10.100/sslclient-win-1.1.2.169.pkg...
Loading sslclient-win-1.1.2.169.pkg from 192.168.10.100 (via FastEthernet0/0): !!
[OK - 415090 bytes]
415090 bytes copied in 12.892 secs (32197 bytes/sec)
3、安装 client 软件
R1(config)#web*** install svc disk0:/sslclient-win- 1.1.2 .169.pkg
SSL××× Package SSL-×××-Client : installed successfully
4、配置 SSL ×××
R1(config)# aaa new-model
R1(config)# aaa authentication login default local //为防止控制台超时而造成无法进入Exec
R1(config))# aaa authentication login web*** local
R1(config)# ip local pool ssl-add 11.1.1 .10 11.1.1.20
R1(config)# username user1 password 123 //定义Web×××本地认证用户名,密码
R1(config))# web*** gateway ***gateway //定义Web×××在哪个接口上进行监听,此时IOS会自动产生自签名证书。
R1 (config-web***-gateway)# ip address 192.168.10.10 port 443
R1 (config-web***-gateway)# inservice //启用web*** gateway配置
R1 (config)# web*** context webcontext //定义web***的相关配置,相当于ASA的tunnel-group,在这里可以定义
R1 (config-web***-context)# gateway ***gateway //将context和gateway相关联
R1 (config-web***-context)# aaa authentication list web***
R1 (config-web***-context)# inservice //启用web*** context配置
R1(config-web***-context)# policy group ssl***-policy //进入ssl***策略组
R1(config-web***-group)# functions svc-enabled
R1(config-web***-group)# svc address-pool ssl-add //分配svc使用的地址池
R1(config-web***-group)# svc split include 192.168.20.0 255.255.255.0 //定义隧道分离的目标地址,如果不配置,则默认为0.0.0.0
R1(config-web***-group)#exit
R1(config-web***-context)# default-group-policy ssl***-policy //当配置了多个policy group后,默认使用的策略组
注意:
在IOS中,如果地址池不和内网在一个段,则需创建一个和地址池在同一网段的loopback接口作为***客户端的网关。
还可以在context中指定virtual-host,类似于iis中的文件头,允许多个主机映射到同一个IP地址
同时context中还可以设置web登陆框的样式,比如logo,title等
5、完整配置
R1#show running-config
Building configuration...
Current configuration : 3223 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R1
!
boot-start-marker
boot-end-marker
!
aaa new-model
!
!
aaa authentication login default local
aaa authentication login web*** local
!
aaa session-id common
!
resource policy
!
ip cef
!
crypto pki trustpoint TP-self-signed-4294967295
enrollment selfsigned
subject-name cn=IOS-Self-Signed-Certificate-4294967295
revocation-check none
rsakeypair TP-self-signed-4294967295
!
!
crypto pki certificate chain TP-self-signed-4294967295
certificate self-signed 01
3082023A 308201A 3 A 0030201 02020101 300D0609 2A 864886 F 70D0101 04050030
31312F 30 2D060355 04031326 494F 532D 53656C 66 2D536967 6E65642D 43657274
69666963 6174652D 34323934 39363732 3935301E 170D3038 31323135 31393039
30335A 17 0D323030 31303130 30303030 305A 3031 312F 302D 06035504 03132649
4F 532D53 656C 662D 5369676E 65642D43 65727469 66696361 74652D34 32393439
36373239 3530819F 300D0609 2A 864886 F 70D0101 01050003 818D0030 81890281
8100C 6F 2 B499879D 1CEB3638 BA59B 459 A 72167BB FDD2CD73 3E3E6FB6
D1347E43
8CC 21C 65 BAC01E28 50013497 71CF 8062 C 54F 254C A6DB2D 5A CDDB864D
CFF 71A 50
F 3C 20566 1405E49B 18CE2DAB 469C 58E8 5B 4A 1FD6 59DCBCA5 12A 34543
4F 6842B6
24B 9A 7BD CE36E 98A A5463EB3 2D 2C 5BC0 FAA 247C 1 E44DB455 4537465F
18895A 14
66D10203 010001A 3 62306030 0F 060355 1D130101 FF040530 030101FF 300D0603
551D1104 06300482 02523130 1F 060355 1D230418 30168014 9F 7F 1B 46 F 6903BC5
803F 4AD7 2433EBD0 5813E29D 301D0603 551D0E04 1604149F 7F 1B 46F 6
903BC580
3F 4AD724 33EBD058 13E29D30 0D 06092A 864886F 7 0D010104 05000381
81002516
3F 75E2AA 33544113 9A 9179DB DFED2529 DF 5A 972F C2BFDE0E 0279D 1F 5
8D30CAC7
59BE 79C 6 85825281 AB2D0B08 2CA84D01 85A 4DB19 8977BC82 9E 59F 764
ADE75E22
9A 7FF 37A 9D 83819A 2287BE75 773FAA32 D38DD 3C 2 2C 0DF 23F 7D45D 7A 3
E 8006C 1A
6B9E0540 12483241 6EEAA0FF B 31240F 3 94044BCB 75210037 FEF5AD 15 F 49B
quit
username user1 password 0 123
!
interface Loopback0
ip address 11.1.1 .1 255.255.255.0
!
interface FastEthernet0/0
ip address 192.168.10.10 255.255.255.0
duplex half
!
interface Serial1/0
ip address 10.1.1.1 255.255.255.0
serial restart-delay 0
!
interface Serial1/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial1/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial1/3
no ip address
shutdown
serial restart-delay 0
!
router rip
version 2
network 10.0.0.0
network 11.0.0.0
network 192.168.10.0
no auto-summary
!
ip local pool ssl-add 11.1.1.10 11.1.1.20
no ip http server
no ip http secure-server
!
logging alarm informational
!
control-plane
!
line con 0
exec-timeout 0 0
stopbits 1
line aux 0
stopbits 1
line vty 0 4
!
web*** gateway ***gateway
ip address 192.168.10.10 port 443
ssl trustpoint TP-self-signed-4294967295
inservice
!
web*** install svc disk0:/web***/svc.pkg
!
web*** context webcontext
ssl authenticate verify all
!
policy group ssl***-policy
functions svc-enabled
svc address-pool "ssl-add"
svc split include 192.168.20.0 255.255.255.0
default-group-policy ssl***-policy
aaa authentication list web***
gateway ***gateway domain ssh***
inservice
!
end
R2#show running-config
Building configuration...
Current configuration : 973 bytes
!
version 12.4
service timestamps debug datetime msec
service timestamps log datetime msec
no service password-encryption
!
hostname R2
!
boot-start-marker
boot-end-marker
!
no aaa new-model
!
resource policy
!
ip cef
!
interface Loopback1
ip address 22.1.1 .1 255.255.255.0
!
interface FastEthernet0/0
ip address 192.168.20.10 255.255.255.0
duplex half
!
interface Serial1/0
ip address 10.1.1.2 255.255.255.252
serial restart-delay 0
!
interface Serial1/1
no ip address
shutdown
serial restart-delay 0
!
interface Serial1/2
no ip address
shutdown
serial restart-delay 0
!
interface Serial1/3
no ip address
shutdown
serial restart-delay 0
!
router rip
version 2
network 10.0.0.0
network 22.0.0.0
network 192.168.20.0
no auto-summary
!
no ip http server
no ip http secure-server
!
logging alarm informational
!
control-plane
!
line con 0
exec-timeout 0 0
stopbits 1
line aux 0
stopbits 1
line vty 0 4
!
end
三、客户端配置
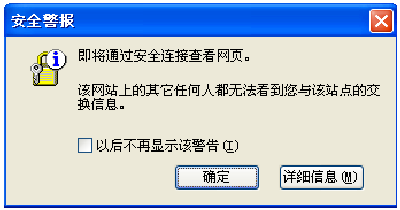
在浏览器中输入https://192.168.10.10/ 访问Web×××,这时会弹出提示信息,点击“确定”
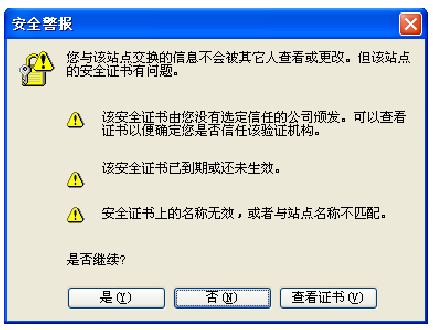
需要安装证书,点击“是”,这里第一个感叹号是因为这个证书只路由器自签发的,没有经过验证,而第二个感叹号是因为配置Web×××时应该注意证书颁发后的证书的有效期,往往颁发证书时的有有效期限时间会比当前时间晚一二天
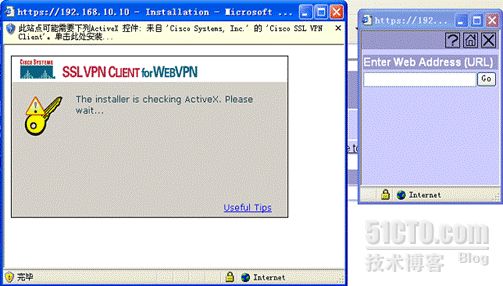
这时会弹出网页,输入用户和密码,点击 login
这时会自动安装 SSL ××× Client 软件
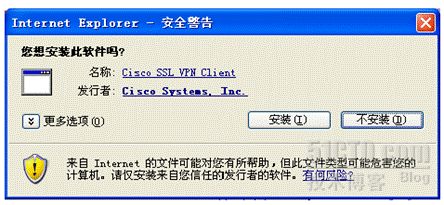
需要点击允许安装 ACTIVE 控件,会弹出安装界面,点击安装
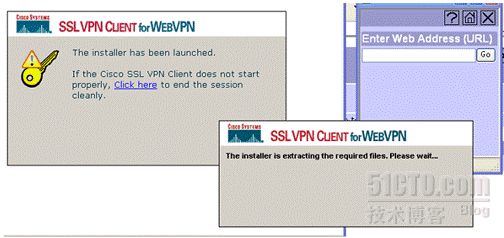
正在进行 SSL ××× Client
点击安装证书
安装证书之后,这样 ×××连接就建立起来,在屏幕的右下部会显示出×××的小钥匙的标志
四、验证配置
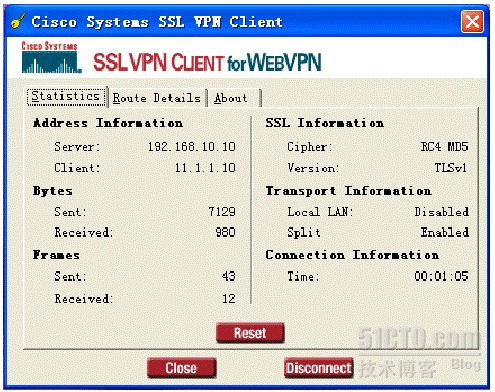
在客户端上可以查看 ×××的状态。
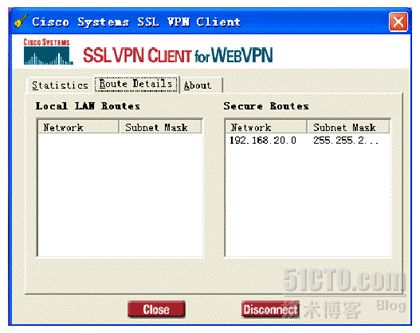
可以查看 ×××隧道的分离子网。
使用ipconfig命令可以查看到获得的地址。
查看路由表,可以看到一条指向192.168.20.0的路由条目