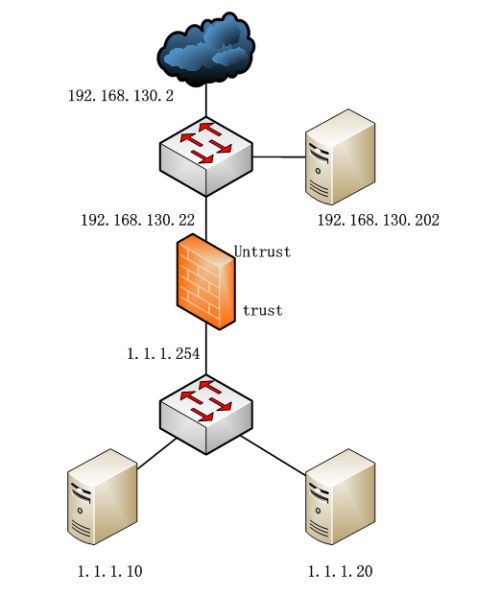
1、实验拓扑图
2、实验配置
2.1、内网服务器访问Internet
set system host-name SRX1
set system time-zone Asia/Shanghai
set system name-server 114.114.114.114
set system services ssh
set system services web-management http
set system ntp server 62.201.225.9
set interfaces ge-0/0/0 unit 0 family inet address 192.168.130.22/24
set interfaces ge-0/0/1 unit 0 family inet address 1.1.1.254/24
set routing-options static route 0.0.0.0/0 next-hop 192.168.130.2
set security nat source rule-set Source-NAT from zone trust
set security nat source rule-set Source-NAT to zone untrust
set security nat source rule-set Source-NAT rule Source-NAT-Rule match source-address 1.1.1.0/24
set security nat source rule-set Source-NAT rule Source-NAT-Rule then source-nat interface
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match source-address any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match destination-address any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match application any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy then permit
set security zones security-zone untrust host-inbound-traffic system-services ping
set security zones security-zone untrust host-inbound-traffic system-services ssh
set security zones security-zone untrust host-inbound-traffic system-services http
set security zones security-zone untrust interfaces ge-0/0/0.0
set security zones security-zone trust host-inbound-traffic system-services ping
set security zones security-zone trust host-inbound-traffic system-services ssh
set security zones security-zone trust host-inbound-traffic system-services http
set security zones security-zone trust interfaces ge-0/0/1.0
2.2、对外提供3389服务
set security nat static rule-set static-nat from zone untrust
set security nat static rule-set static-nat rule Outside10-TO-Inside10-rule match destination-address 192.168.130.10/32
set security nat static rule-set static-nat rule Outside10-TO-Inside10-rule then static-nat prefix 1.1.1.10/32
set security nat proxy-arp interface ge-0/0/0.0 address 192.168.130.10/32
set security zones security-zone trust address-book address Outside10-TO-Inside10-address 1.1.1.10/32
set security zones security-zone trust address-book address-set Outside10-TO-Inside10-address-set address Outside10-TO-Inside10-address
set applications application Outside10-TO-Inside10-application term 3389 protocol tcp
set applications application Outside10-TO-Inside10-application term 3389 destination-port 3389
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match source-address any
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match destination-address Outside10-TO-Inside10-address-set
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match application Outside10-TO-Inside10-application
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy then permit
2.3、内网服务器通过192.168.130.10访问1.1.1.10的3389服务
set security nat source rule-set Source-NAT to zone trust
set security nat static rule-set static-nat from zone trust
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match source-address any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match destination-address any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match application any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy then permit
2.4、1.1.1.20对外提供3389服务,内网服务器通过192.168.130.20访问1.1.1.20的3389服务
set security nat static rule-set static-nat from zone trust
set security nat static rule-set static-nat from zone untrust
set security nat static rule-set static-nat rule Outside20-TO-Inside20-rule match destination-address 192.168.130.20/32
set security nat static rule-set static-nat rule Outside20-TO-Inside20-rule then static-nat prefix 1.1.1.20/32
set security nat proxy-arp interface ge-0/0/0.0 address 192.168.130.20/32
set security zones security-zone trust address-book address Outside20-TO-Inside20-address 1.1.1.20/32
set security zones security-zone trust address-book address-set Outside20-TO-Inside20-address-set address Outside20-TO-Inside20-address
set applications application Outside20-TO-Inside20-application term 3389 protocol tcp
set applications application Outside20-TO-Inside20-application term 3389 destination-port 3389
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match source-address any
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match destination-address Outside20-TO-Inside20-address-set
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match application Outside20-TO-Inside20-application
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy then permit
3、总结
Static NAT映射后,内网服务器无法通过外网IP访问内网服务器:需要在untrust和trust两个方向同时做Source NAT和Static NAT。
最终配置如下:
root@SRX1# show | display set
set version 12.1X44.4
set system host-name SRX1
set system time-zone Asia/Shanghai
set system root-authentication encrypted-password "$1$rzXSdTNv$xhvtt2I62Mf/LJCFfq.Xz/"
set system name-server 114.114.114.114
set system services ssh
set system services web-management http
set system ntp server 62.201.225.9
set interfaces ge-0/0/0 unit 0 family inet address 192.168.130.22/24
set interfaces ge-0/0/1 unit 0 family inet address 1.1.1.254/24
set routing-options static route 0.0.0.0/0 next-hop 192.168.130.2
set security nat source rule-set Source-NAT from zone trust
set security nat source rule-set Source-NAT to zone trust
set security nat source rule-set Source-NAT to zone untrust
set security nat source rule-set Source-NAT rule Source-NAT-Rule match source-address 1.1.1.0/24
set security nat source rule-set Source-NAT rule Source-NAT-Rule then source-nat interface
set security nat static rule-set static-nat from zone trust
set security nat static rule-set static-nat from zone untrust
set security nat static rule-set static-nat rule Outside10-TO-Inside10-rule match destination-address 192.168.130.10/32
set security nat static rule-set static-nat rule Outside10-TO-Inside10-rule then static-nat prefix 1.1.1.10/32
set security nat static rule-set static-nat rule Outside20-TO-Inside20-rule match destination-address 192.168.130.20/32
set security nat static rule-set static-nat rule Outside20-TO-Inside20-rule then static-nat prefix 1.1.1.20/32
set security nat proxy-arp interface ge-0/0/0.0 address 192.168.130.10/32
set security nat proxy-arp interface ge-0/0/0.0 address 192.168.130.20/32
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match source-address any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match destination-address any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy match application any
set security policies from-zone trust to-zone untrust policy Source-NAT-Plicy then permit
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match source-address any
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match destination-address Outside10-TO-Inside10-address-set
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy match application Outside10-TO-Inside10-application
set security policies from-zone untrust to-zone trust policy Outside10-TO-Inside10-policy then permit
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match source-address any
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match destination-address Outside20-TO-Inside20-address-set
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy match application Outside20-TO-Inside20-application
set security policies from-zone untrust to-zone trust policy Outside20-TO-Inside20-policy then permit
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match source-address any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match destination-address any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy match application any
set security policies from-zone trust to-zone trust policy Source-NAT-Plicy then permit
set security zones security-zone untrust host-inbound-traffic system-services ping
set security zones security-zone untrust host-inbound-traffic system-services ssh
set security zones security-zone untrust host-inbound-traffic system-services http
set security zones security-zone untrust interfaces ge-0/0/0.0
set security zones security-zone trust address-book address Outside10-TO-Inside10-address 1.1.1.10/32
set security zones security-zone trust address-book address Outside20-TO-Inside20-address 1.1.1.20/32
set security zones security-zone trust address-book address-set Outside10-TO-Inside10-address-set address Outside10-TO-Inside10-address
set security zones security-zone trust address-book address-set Outside20-TO-Inside20-address-set address Outside20-TO-Inside20-address
set security zones security-zone trust host-inbound-traffic system-services ping
set security zones security-zone trust host-inbound-traffic system-services ssh
set security zones security-zone trust host-inbound-traffic system-services http
set security zones security-zone trust interfaces ge-0/0/1.0
set applications application Outside10-TO-Inside10-application term 3389 protocol tcp
set applications application Outside10-TO-Inside10-application term 3389 destination-port 3389
set applications application Outside20-TO-Inside20-application term 3389 protocol tcp
set applications application Outside20-TO-Inside20-application term 3389 destination-port 3389