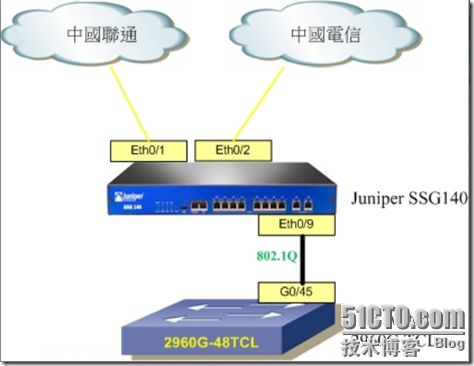
Juniper firewall多進單出配置。想法是這樣的用一台firewall將這幾條ISP線路都接入,再通過一個trunk口出來,通過一台L2 switch劃分出幾個VLAN,分別對應不同的ISP線路。這樣做的好處就不多说了,最起码省了在firewall上使用的端口吧,嘎嘎。可能你會擔心端口帶寬問題。試驗用的是Juniper SSG140 一共有10個端口,前8個為百兆帶寬,最後2個為千兆端口,所以這樣的架構不存在端口帶寬瓶頸問題。
架構圖如下
這裡簡要介紹下試驗環境。
網通線路:ip:192.168.20.200/24
電信線路:ip:192.168.30.200/24
VLAN2 對應Eth0/1網通線路 Eth0/9.1 VLAN2 192.168.2.0/24
VLAN3對應Eth0/2電信線路 Eth0/9.2 VLAN3 192.168.3.0/24
其中便與管理將Eeh0/0也做了配製,NAT模式 ip:192.168.1.1/24
也將Eth0/3做了配製,ROUTE模式 且增加了路由及策略
這裡增加的配置和試驗需要配置的不構成影響
firewall配置如下:
set admin name "netscreen"
set admin password "nKVUM2rwMUzPcrkG5sWIHdCtqkAibn"
set admin auth web timeout 0
set admin auth server "Local"
set admin format dos
set zone "Trust" vrouter "trust-vr"
set zone "Untrust" vrouter "trust-vr"
set zone "DMZ" vrouter "trust-vr"
set zone "VLAN" vrouter "trust-vr"
set zone "Untrust-Tun" vrouter "trust-vr"
set zone "Trust" tcp-rst
set zone "Untrust" block
unset zone "Untrust" tcp-rst
set zone "MGT" block
set zone "DMZ" tcp-rst
set zone "VLAN" block
unset zone "VLAN" tcp-rst
set zone "Untrust" screen tear-drop
set zone "Untrust" screen syn-flood
set zone "Untrust" screen ping-death
set zone "Untrust" screen ip-filter-src
set zone "Untrust" screen land
set zone "V1-Untrust" screen tear-drop
set zone "V1-Untrust" screen syn-flood
set zone "V1-Untrust" screen ping-death
set zone "V1-Untrust" screen ip-filter-src
set zone "V1-Untrust" screen land
set interface "ethernet0/0" zone "Trust" //設置端口
set interface "ethernet0/1" zone "Untrust"
set interface "ethernet0/2" zone "Untrust"
set interface "ethernet0/3" zone "Untrust"
set interface "ethernet0/4" zone "HA"
set interface "ethernet0/9" zone "Trust"
set interface "ethernet0/9.1" tag 2 zone "Trust"
set interface "ethernet0/9.2" tag 3 zone "Trust"
set interface "ethernet0/9.3" tag 4 zone "Trust"
set interface ethernet0/0 ip 192.168.1.1/24
set interface ethernet0/0 nat
unset interface vlan1 ip
set interface ethernet0/1 ip 192.168.20.200/24 //端口route模式配置
set interface ethernet0/1 route
set interface ethernet0/2 ip 192.168.30.200/24
set interface ethernet0/2 route
set interface ethernet0/3 ip 10.129.21.200/24
set interface ethernet0/3 route
set interface ethernet0/9.1 ip 192.168.2.1/24 //端口NAT模式配置
set interface ethernet0/9.1 nat
set interface ethernet0/9.2 ip 192.168.3.1/24
set interface ethernet0/9.2 nat
set interface ethernet0/9.3 ip 192.168.4.1/24
set interface ethernet0/9.3 nat
set interface ethernet0/9.1 mtu 1500
unset interface vlan1 bypass-others-ipsec
unset interface vlan1 bypass-non-ip
set interface ethernet0/0 ip manageable
set interface ethernet0/1 ip manageable //配製各個端口管理地址及允許服務
set interface ethernet0/2 ip manageable
set interface ethernet0/3 ip manageable
unset interface ethernet0/9 ip manageable
set interface ethernet0/9.1 ip manageable
set interface ethernet0/9.2 ip manageable
set interface ethernet0/9.3 ip manageable
set interface ethernet0/1 manage ping
set interface ethernet0/1 manage telnet
set interface ethernet0/1 manage web
set interface ethernet0/2 manage ping
set interface ethernet0/2 manage telnet
set interface ethernet0/2 manage web
set interface ethernet0/3 manage ping
set interface ethernet0/3 manage telnet
set interface ethernet0/3 manage web
unset interface ethernet0/9 manage ping
unset interface ethernet0/9 manage ssh
unset interface ethernet0/9 manage telnet
unset interface ethernet0/9 manage snmp
unset interface ethernet0/9 manage ssl
unset interface ethernet0/9 manage web
unset interface ethernet0/9.1 manage ssh
unset interface ethernet0/9.1 manage snmp
unset interface ethernet0/9.1 manage ssl
unset interface ethernet0/9.2 manage ssh
unset interface ethernet0/9.2 manage snmp
unset interface ethernet0/9.2 manage ssl
unset interface ethernet0/9.3 manage ssh
unset interface ethernet0/9.3 manage snmp
unset interface ethernet0/9.3 manage ssl
set interface ethernet0/0 dhcp server service //各個端口DHCP配置
set interface ethernet0/9.1 dhcp server service
set interface ethernet0/9.2 dhcp server service
set interface ethernet0/0 dhcp server enable
set interface ethernet0/9.1 dhcp server enable
set interface ethernet0/9.2 dhcp server enable
set interface ethernet0/0 dhcp server option lease 1440
set interface ethernet0/0 dhcp server option gateway 192.168.1.1
set interface ethernet0/0 dhcp server option netmask 255.255.255.0
set interface ethernet0/0 dhcp server option dns1 10.128.2.101
set interface ethernet0/0 dhcp server option dns2 10.128.2.100
set interface ethernet0/9.1 dhcp server option lease 1440
set interface ethernet0/9.1 dhcp server option gateway 192.168.2.1
set interface ethernet0/9.1 dhcp server option netmask 255.255.255.0
set interface ethernet0/9.1 dhcp server option dns1 221.6.4.66
set interface ethernet0/9.2 dhcp server option lease 1440
set interface ethernet0/9.2 dhcp server option gateway 192.168.3.1
set interface ethernet0/9.2 dhcp server option netmask 255.255.255.0
set interface ethernet0/9.2 dhcp server option dns1 221.6.4.65
set interface ethernet0/9.2 dhcp server option dns2 221.6.4.66
set interface ethernet0/0 dhcp server ip 192.168.1.50 to 192.168.1.100
set interface ethernet0/9.1 dhcp server ip 192.168.2.50 to 192.168.2.100
set interface ethernet0/9.2 dhcp server ip 192.168.3.50 to 192.168.3.100
unset interface ethernet0/0 dhcp server config next-server-ip
unset interface ethernet0/9.1 dhcp server config next-server-ip
unset interface ethernet0/9.2 dhcp server config next-server-ip
unset flow no-tcp-seq-check
set flow tcp-syn-check
unset flow tcp-syn-bit-check
set flow reverse-route clear-text prefer
set flow reverse-route tunnel always
set pki authority default scep mode "auto"
set pki x509 default cert-path partial
set address "Trust" "192.168.1.0/24" 192.168.1.0 255.255.255.0
set address "Trust" "192.168.2.0/24" 192.168.2.0 255.255.255.0
set address "Trust" "192.168.3.0/24" 192.168.3.0 255.255.255.0
set ike respond-bad-spi 1
set ike ikev2 ike-sa-soft-lifetime 60
unset ike ikeid-enumeration
unset ike dos-protection
unset ipsec access-session enable
set ipsec access-session maximum 5000
set ipsec access-session upper-threshold 0
set ipsec access-session lower-threshold 0
set ipsec access-session dead-p2-sa-timeout 0
unset ipsec access-session log-error
unset ipsec access-session info-exch-connected
unset ipsec access-session use-error-log
set vrouter "untrust-vr"
exit
set vrouter "trust-vr"
exit
set url protocol websense
exit
set policy id 4 name "0/0 TO 0/1" from "Trust" to "Untrust" "192.168.1.0/24" "Any" "ANY" permit log //策略配製
set policy id 4
exit
set policy id 1 name "any to any" from "Trust" to "Untrust" "Any" "Any" "ANY" permit log
set policy id 1 disable
set policy id 1
exit
set policy id 2 name "VLAN2 TO 0/1" from "Trust" to "Untrust" "192.168.2.0/24" "Any" "ANY" permit log
set policy id 2
exit
set policy id 3 name "VLAN3 TO 0/2" from "Trust" to "Untrust" "192.168.3.0/24" "Any" "ANY" permit log
set policy id 3
exit
set nsmgmt bulkcli reboot-timeout 60
set ssh version v2
set config lock timeout 5
unset license-key auto-update
set snmp port listen 161
set snmp port trap 162
set vrouter "untrust-vr"
exit
set vrouter "trust-vr"
set source-routing enable
unset add-default-route
set route 10.0.0.0/8 interface ethernet0/3 gateway 10.129.21.254 //路由配置
set route 0.0.0.0/0 interface ethernet0/1 gateway 192.168.20.1 metric 10
set route source 192.168.2.0/24 interface ethernet0/1 gateway 192.168.20.1 permanent
set route source 192.168.3.0/24 interface ethernet0/2 gateway 192.168.30.1 permanent
驗證,分別接入VLAN中通過ping命令,并通過拔插網線驗證走的哪一條線路。沒有問題。试验成功。嘎嘎
这个实验最要紧的设置就是那几句基于原地址的路由了,不过公司如果要实际应用建议设置policy时候不要any到any了。
应大家的要求今天重新实验上图。
interface设置:
端口上DHCP设置:
路由配置:
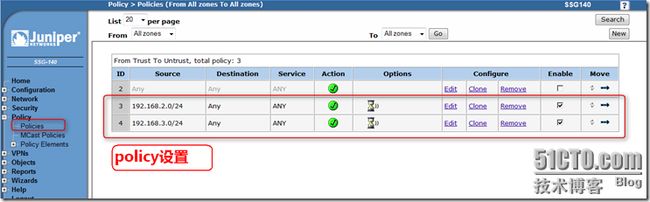
policy设置:
game over,就是这么简单!
![clip_image001[1] Juniper Firewall多进单出配制实例_第2张图片](http://img.e-com-net.com/image/info3/961964e6d4ab4efab1a693ac73c5c3dc.jpg)