四台测试服务器:mail、www、主dns、从DNS
主DNS: 192.168.1.27
www: 192.168.1.28
mail: 192.168.1.29
从DNS: 192.168.1.34
主、从dns上安装bind
yum install bind
一、使用新创建配置文件的方式配置DNS
以下操作在主DNS上实现
1、把原配置文件打成bak
[root@localhost ~]# mv /etc/named.conf /etc/named.conf.bak
2、重新建主配置文件named.conf
[root@localhost ~]# vim /etc/named.conf
options {
directory "/var/named";
};
zone "." IN { #根解析
type hint;
file "named.ca"; #根解析文件路径
};
zone "localhost." IN { #本机正向解析
type master;
file "named.localhost"; #本机正向解析的文件路径
};
zone "1.0.0.127.in-addr.arpa." IN { #本机反向解析
type master;
file "named.loopback"; #本机反向解析的文件路径
};
3、修改/etc/named.conf的属主属组和权限
[root@localhost ~]# chown root:named /etc/named.conf
[root@localhost ~]# chmod 640 /etc/named.conf
4、检查配置文件是否有语法错误
[root@localhost ~]# service named configtest
zone localhost/IN: loaded serial 0
zone 1.0.0.127.in-addr.arpa/IN: loaded serial 0
5、启动named服务
[root@localhost ~]# service named start
Generating /etc/rndc.key: [确定]
启动 named: [确定]
6、添加区域到配置文件中/etc/named.conf
zone "shamereedwine.com." IN {
type master;
file "shamereedwine.com.zone";
};
7、创建区域文件shamereedwine.com.zone
cd /var/named目录中
vim shamereedwine.com.zone
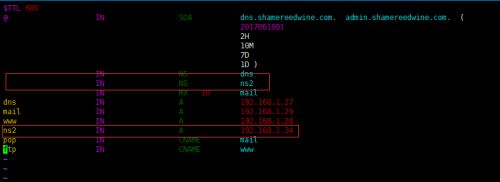
$TTL 600
@ IN SOA dns.shamereedwine.com. admin.shamereedwine.com. (
2017061801
2H
10M
7D
1D )
@ IN NS dns
@ IN MX 10 mail
dns IN A 192.168.1.27
mail IN A 192.168.1.29
www IN A 192.168.1.28
pop IN CNAME mail
ftp IN CNAME www
8、修改区域文件shamereedwine.com.zone的属组和属主
[root@localhost named]# chown root:named shamereedwine.com.zone
[root@localhost named]# chmod 640 shamereedwine.com.zone
9、检查语法是否有错误
[root@localhost named]# service named configtest
zone localhost/IN: loaded serial 0
zone 1.0.0.127.in-addr.arpa/IN: loaded serial 0
zone shamereedwine.com/IN: loaded serial 2017061801
10、重新启动named服务
[root@localhost named]# service named restart
停止 named:. [确定]
启动 named: [确定]
11、使用dig命令测试dns解析
[root@localhost named]# dig -t NS shamereedwine.com
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.62.rc1.el6_9.2 <<>> -t NS shamereedwine.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 52704
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; QUESTION SECTION:
;shamereedwine.com. IN NS
;; ANSWER SECTION:
shamereedwine.com. 600 IN NS dns.shamereedwine.com.
;; ADDITIONAL SECTION:
dns.shamereedwine.com. 600 IN A 192.168.1.27
;; Query time: 1 msec
;; SERVER: 192.168.1.27#53(192.168.1.27)
;; WHEN: Mon Jun 19 07:49:56 2017
;; MSG SIZE rcvd: 69
12、使用dig命令解析pop.shamereedwine.com
[root@localhost named]# dig -t A pop.shamereedwine.com
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.62.rc1.el6_9.2 <<>> -t A pop.shamereedwine.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 16672
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 2, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION:
;pop.shamereedwine.com. IN A
;; ANSWER SECTION:
pop.shamereedwine.com. 600 IN CNAME mail.shamereedwine.com.
mail.shamereedwine.com. 600 IN A 192.168.1.29
;; AUTHORITY SECTION:
shamereedwine.com. 600 IN NS dns.shamereedwine.com.
;; ADDITIONAL SECTION:
dns.shamereedwine.com. 600 IN A 192.168.1.27
;; Query time: 1 msec
;; SERVER: 192.168.1.27#53(192.168.1.27)
;; WHEN: Mon Jun 19 07:54:39 2017
;; MSG SIZE rcvd: 108
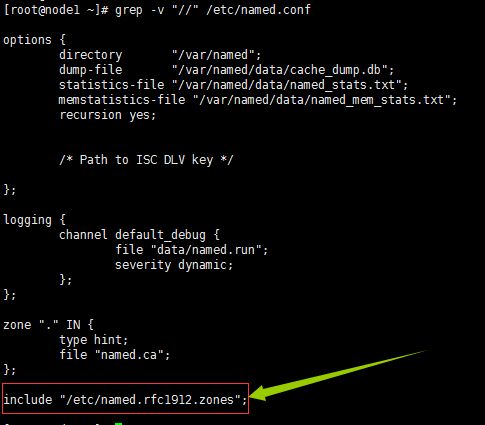
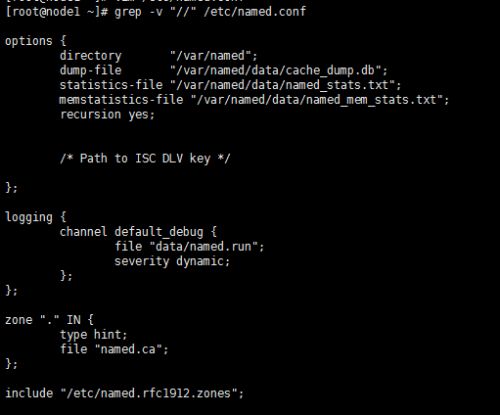
二、使用原有配置文件配置DNS
以下操作在主DNS上实现
1、vim /etc/named.conf
options {
directory "/var/named";
dump-file "/var/named/data/cache_dump.db";
statistics-file "/var/named/data/named_stats.txt";
memstatistics-file "/var/named/data/named_mem_stats.txt";
recursion yes;
/* Path to ISC DLV key */
};
logging {
channel default_debug {
file "data/named.run";
severity dynamic;
};
};
zone "." IN {
type hint;
file "named.ca";
};
include "/etc/named.rfc1912.zones";
2、vim /etc/named.rfc1912.zones #在该主配置文件的扩展配置文件里加入shamereedwine.com的域
zone "shamereedwine.com" IN {
type master;
file "shamereedwine.com.zone";
};
3、创建区域文件 #创建shamereedwine.com.zone
cd /var/named
vim shamereedwine.com.zone
$TTL 600
@ IN SOA dns.shamereedwine.com. admin.shamereedwine.com. (
2017061801
1H
5M
3D
12H )
IN NS dns
IN MX 10 mail
dns IN A 192.168.1.27
mail IN A 192.168.1.29
www IN A 192.168.1.28
pop IN CNAME mail
ftp IN CNAME www
chown root:named shamereedwine.com.zone #改变该区域的属主和属组
chown 640 shamereedwine.com.zone #改变权限
4、检查配置文件和区域文件
named-checkconf
named-checkzone "shamereedwine.com" shamereedwine.com.zone
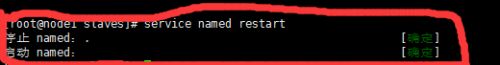
5、重新启动named服务
service named restart
6、测试解析
[root@dns named]# dig -t NS shamereedwine.com
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.62.rc1.el6_9.2 <<>> -t NS shamereedwine.com
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 240
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 0, ADDITIONAL: 1
;; QUESTION SECTION:
;shamereedwine.com. IN NS
;; ANSWER SECTION:
shamereedwine.com. 600 IN NS dns.shamereedwine.com.
;; ADDITIONAL SECTION:
dns.shamereedwine.com. 600 IN A 192.168.1.27
;; Query time: 0 msec
;; SERVER: 192.168.1.27#53(192.168.1.27)
;; WHEN: Wed May 4 02:25:01 2016
;; MSG SIZE rcvd: 69
7、使用nslookup 查看
[root@dns named]# nslookup
> set q=A
> www.shamereedwine.com
Server: 192.168.1.27
Address: 192.168.1.27#53
Name: www.shamereedwine.com
Address: 192.168.1.28
> set q=MX
> shamereedwine.com
Server: 192.168.1.27
Address: 192.168.1.27#53
shamereedwine.com mail exchanger = 10 mail.shamereedwine.com.
> q
Server: 192.168.1.27
Address: 192.168.1.27#53
8、配置反向解析配置文件
vim /etc/named.rfc1912.zones
加入下面所示的反向解析区域参数
zone "1.168.192.in-addr.arpa" IN {
type master;
file "192.168.1.zone";
};
9、配置反向解析区域文件
cd /var/named
vim 192.168.1.zone
$TTL 600
@ IN SOA dns.shamereedwine.com. dnsadmin.shamereedwine.com. (
2017061801
1H
5M
3D
12H )
IN NS dns.shamereedwine.com.
27 IN PTR dns.shamereedwine.com.
28 IN PTR www.shamereedwine.com.
29 IN PTR mail.shamereedwine.com .
chown root:named 192.168.1.zone #更改属主和属组
chmod 640 192.168.1.zone #设置权限
10、测试主配置文件和区域文件的正确性
service named configtest
zone localhost.localdomain/IN: loaded serial 0
zone localhost/IN: loaded serial 0
zone 1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.ip6.arpa/IN: loaded serial 0
zone 1.0.0.127.in-addr.arpa/IN: loaded serial 0
zone 0.in-addr.arpa/IN: loaded serial 0
zone shamereedwine.com/IN: loaded serial 2017061801
zone 1.168.192.in-addr.arpa/IN: loaded serial 2017061801
11、重启服务
service named reload
12、测试反向解析 #解析192.168.1.27
[root@dns named]# dig -x 192.168.1.27
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.62.rc1.el6_9.2 <<>> -x 192.168.1.27
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 42817
;; flags: qr aa rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 1
;; QUESTION SECTION: #请求
;27.1.168.192.in-addr.arpa. IN PTR
;; ANSWER SECTION: #应答
27.1.168.192.in-addr.arpa. 600 IN PTR dns.shamereedwine.com.
;; AUTHORITY SECTION:
1.168.192.in-addr.arpa. 600 IN NS dns.shamereedwine.com.
;; ADDITIONAL SECTION:
dns.shamereedwine.com. 600 IN A 192.168.1.27
;; Query time: 24 msec
;; SERVER: 192.168.1.27#53(192.168.1.27)
;; WHEN: Wed May 4 04:38:55 2016
;; MSG SIZE rcvd: 108
13、使用dig模拟区域传送
[root@dns named]# dig -t axfr shamereedwine.com @192.168.1.27
; <<>> DiG 9.8.2rc1-RedHat-9.8.2-0.62.rc1.el6_9.2 <<>> -t axfr shamereedwine.com @192.168.1.27
;; global options: +cmd
shamereedwine.com. 600 IN SOA dns.shamereedwine.com. admin.shamereedwine.com. 2017061801 3600 300 259200 43200
shamereedwine.com. 600 IN NS dns.shamereedwine.com.
shamereedwine.com. 600 IN MX 10 mail.shamereedwine.com.
dns.shamereedwine.com. 600 IN A 192.168.1.27
ftp.shamereedwine.com. 600 IN CNAME www.shamereedwine.com.
mail.shamereedwine.com. 600 IN A 192.168.1.29
pop.shamereedwine.com. 600 IN CNAME mail.shamereedwine.com.
www.shamereedwine.com. 600 IN A 192.168.1.28
shamereedwine.com. 600 IN SOA dns.shamereedwine.com. admin.shamereedwine.com. 2017061801 3600 300 259200 43200
;; Query time: 249 msec
;; SERVER: 192.168.1.27#53(192.168.1.27)
;; WHEN: Wed May 4 04:48:31 2016
;; XFR size: 9 records (messages 1, bytes 240)
三、配置主从同步服务器
主dns服务器: 192.168.1.27
从dns服务器: 192.168.1.34
yum install bind
1、打开主dns服务器192.168.1.27的主区域文件,添加一条从DNS服务器NS和A记录
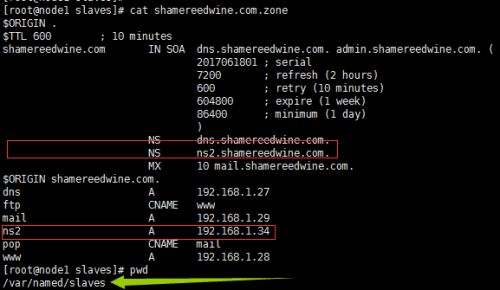
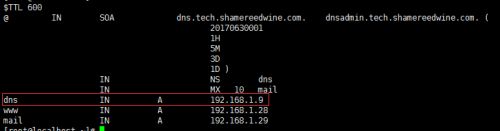
vim /var/named/shamereedwine.com.zone,如下图所示:
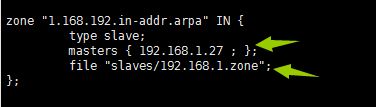
2、从DNS服务器192.168.1.34修改DNS主配置文件,改后的主配置文件如下图所示:
3、修改主区域配置文件的扩展配置文件/etc/named.rfc1912.zones,添加一个区域,
分别指定主DNS服务器地址192.168.1.27和区域文件的所在路径 /var/named/slaves/shamereedwine.com.zone
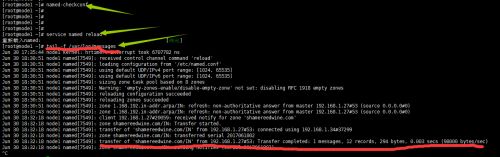
4、启动服务
注意:从服务器不需要创建区域数据文件,自动从主服务器同步
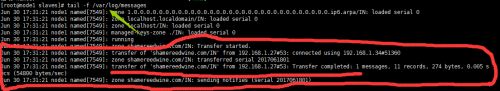
5、查看系统日志
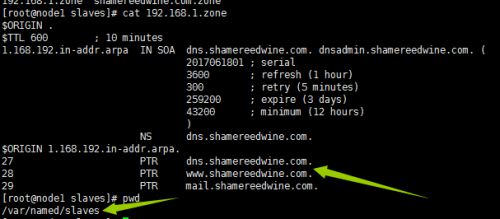
6、可以看到从dns的区域数据文件已经传到/var/named/slaves目录下,文件为shamereedwine.com.zone
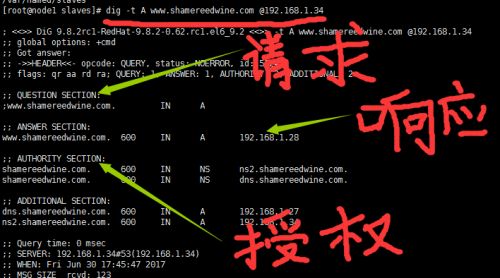
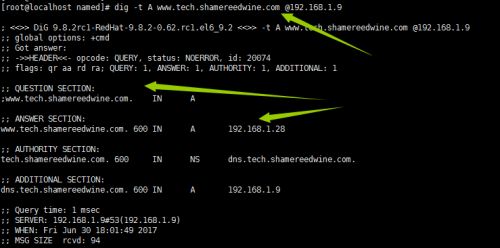
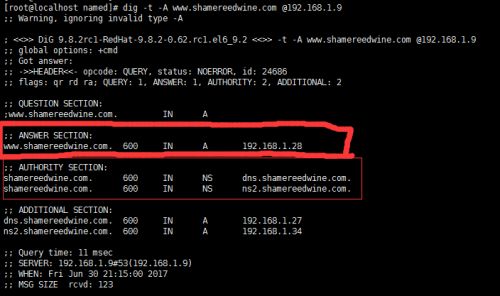
7、在从DNS上做解析测试,解析www.shamereedwine.com的域名,如下图所示:
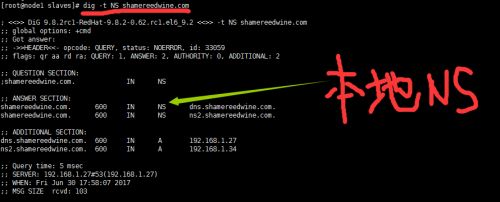
8、查找本地NS记录,可以看到有两个DNS服务器
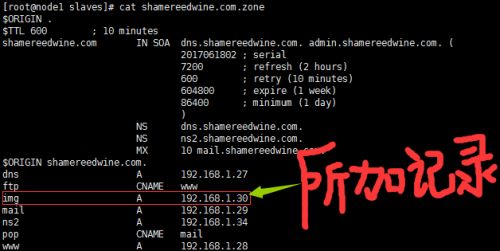
9、测试同步,在主DNS上的正向区域文件/var/named/shamereedwine.com.zone文件里,加一条A记录,并把序号加1.
从DNS的/var/named/slaves/shamereedwine.com.zone文件下:可以看到所加的A记录以成功同步到从dns的区域配置文件中
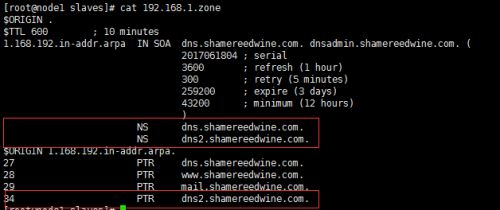
10、编辑反向区域数据文件/etc/named.rfc1912.zones,加上反向区域解析的参数,主DNS的地址192.168.1.27,
从DNS区域数据文件的路径/var/named/slaves/192.168.1.zone
11、检查区域文件是否有语法错误、重启服务、查看日志,如下图所示:
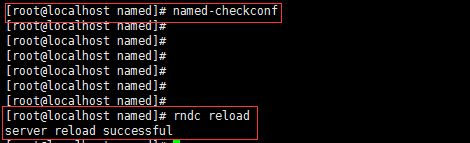
named-checkconf
service named reload
tail -f /var/log/messages
12、到区域文件的主目录/var/named/slaves下,可以看到192.168.1.zone已经从主DNS服务器192.168.1.27同步过来
13、测试反向区域同步:
在主DNS192.168.1.27的方向区域数据文件里添加dns2的反向区域数据文件的A记录并把序列号加1
从DNS的反向解析配置文件,/var/named/slaves/192.168.1.zone
14、设置访问控制列表
区域传送控制:
allow-transfer { IP: };
四、配置rndc来管理BIND
rndc:密钥
rndc:持有一半密钥,保存于rndc的配置文件中
BIND:持有一半密钥,保存于主配置文件中
rndc的配置文件/etc/rndc.conf
CentOS,RHEL: 密钥文件
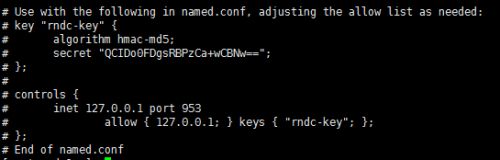
1、使用rndc生成主配置文件
![]()
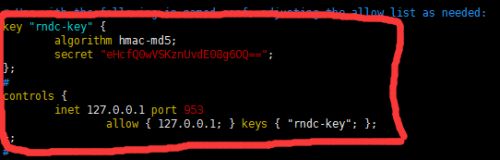
2、把下面的一段代码,黏贴到主DNS的配置文件/etc/named.conf里,
3、把上面所加代码去掉注释
五、BIND子域授权的实现
在父域的配置文件中添加如下项:
授权的子区域名称
子区域的名称服务器
子区域的名称服务器的IP地址
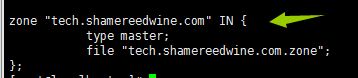
1、打开主DNS的正向区域数据文件,加入下图所示的代码,配置一个tech.shamereedwine.com的授权子域
vim shamereedwine.com.zone
2、在为授权子域提供DNS服务的服务器
(1)、192.168.1.9上安装bind
![]()
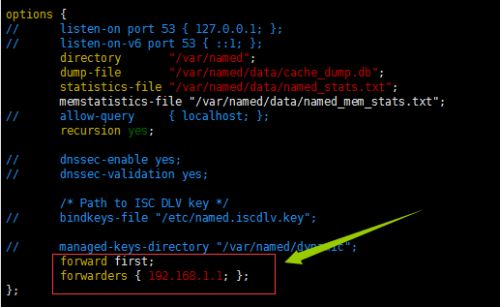
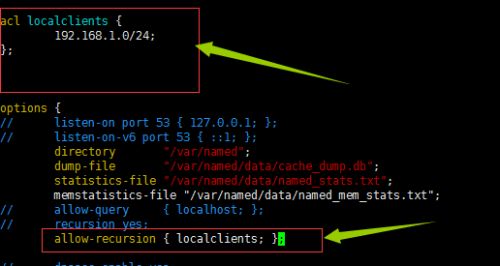
(2)、编辑主配置文件/etc/named.conf,如下图所示:
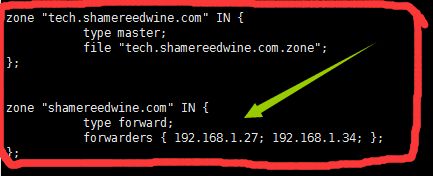
(3)、编辑/etc/named.rfc1912.zones扩展文件,加入下图所示的代码
(4)、编辑区域数据文件
vim /var/named/tech.shamereedwine.com.zone
(5)、修改该区域数据文件tech.shamereedwine.com.zone的属主、属组和权限
(6)、启动bind
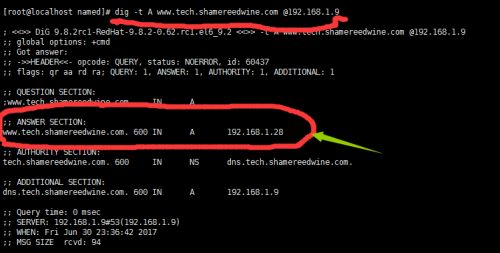
3、使用该区域服务器解析子区域www.tech.shamereedwine.com,可以看到解析正常,如下图所示:
六、配置区域转发:
配置区域转发: 转发域
解析某本机不负责的区域内的名称时不转发给根,而是转发给特定的主机:
zone "ZONE NAME" IN {
type forward;
forwarders { DNS_SERVER; };
forward only|first ;
配置转发的方式:
转发非本机负责解析的所有区域:
options {
forward only|first;
forwarders { IP; }
转发某特定区域:
zone “特定区域” IN {
type forward;
forwarders {IP;}
forward only|first ; }
}
允许使用转发的前提:本机要在对方的允许的递归主机列表中:
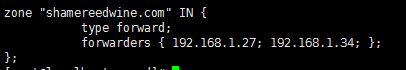
1、在子域DNS服务器192.168.1.9上 的扩展配置文件/etc/named.rfc1912.zones中,
配置转发区域,加入的代码如下图所示:
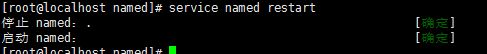
2、检查配置文件并重启named服务
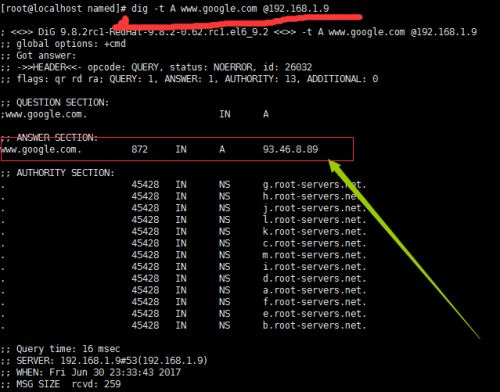
3、测试转发,如下图所示,表示正常!
4、在子域DNS服务器192.168.1.9上测试本机和互联网上的域名都可以转发
编辑主配置文件 vim /etc/named.conf,加入下面的代码
注意:所加的代码要放到option里面
编辑扩展配置文件/etc/named.rfc1912.zones,代码保持如下图所示:
5、子域DNS服务器192.168.1.9重启服务
6、解析父域www.shamereedwine.com
7、解析互联网www.google.com
8、解析自己的域
七、安全控制选项
allow-transfer {};
通常都需要启用,
allow-query {};
此项通常仅用于服务器是缓存名称服务器时,只开放查询功能给本地客户端:
allow-recursion {};
定义递归白名单;
allow-update { none; };
定义允许动态更新区域数据文件的主机白名单
ACL: BIND支持使用访问控制列表
acl ACL_NAME {
172.16.0.0/16;
192.168.0.0/24
127.0.0.0/8;
};
访问控制列表只有定义后才能使用:通常放到/etc/named.conf的上面
BIND有四个内置的acl:
any:任何主机
none:无一主机
local:本机
localnet:本机的所在的网络
定义acl里的网段机器可以递归,修改主配置文件/etc/named.conf,加入下面所示的代码: