- Ubuntu16.04切换内核启动
StruggleYouth
ubuntu系统操作
1.该命令显示内核的启动顺序zgw@zgw-ThinkPad:~$grepmenuentry/boot/grub/grub.cfgif[x"${feature_menuentry_id}"=xy];thenmenuentry_id_option="--id"menuentry_id_option=""exportmenuentry_id_optionmenuentry'Ubuntu'--class
- Java函数式接口四部曲之Consumer
sundawei2016
java前端开发语言
Consumer是一个函数式接口,位于java.util.function包中。它表示一个接受单个输入参数并且不返回任何结果的操作。Consumer通常用于需要对输入参数执行某些操作但不产生返回值的场景。Consumer接口定义了一个抽象方法:accept(Tt):接受一个类型为T的参数,并对其执行操作。Consumerdisplay=System.out::println;display.acc
- Apache Doris 实现毫秒级查询响应
随风九天
匠心数据库服务javaapacheApacheDoris
1.引言1.1数据分析的重要性随着大数据时代的到来,企业对实时数据分析的需求日益增长。快速、准确地获取数据洞察成为企业在竞争中脱颖而出的关键。传统的数据库系统在处理大规模数据时往往面临性能瓶颈,难以满足实时分析的需求。例如,一个电商公司需要实时监控销售数据以调整库存和营销策略,而传统的数据库可能需要数分钟甚至数小时才能生成报表,这显然无法满足业务需求。1.2ApacheDoris简介ApacheD
- Flink实时流处理入门与实践
随风九天
springjavaFlink实时流
一、引言1.1实时流处理的重要性在当今数据驱动的时代,实时数据处理变得越来越重要。企业需要从不断产生的大量数据中快速提取有价值的信息,以支持决策制定和业务优化。实时流处理技术能够实时处理数据流,提供即时的洞察和响应,从而提高业务效率和竞争力。1.2Flink简介ApacheFlink是一个开源的分布式流处理框架,支持批处理和流处理。Flink提供了高吞吐量、低延迟和精确一次(exactly-onc
- 《Windows命令提示符(CMD)函数全解析与应用研究》
Small踢倒coffee_氕氘氚
经验分享笔记
##摘要本文深入探讨了Windows命令提示符(CMD)的核心功能和应用。文章详细解析了CMD的基本命令、批处理脚本编写技巧以及高级功能,包括网络命令、系统管理命令和磁盘管理命令。通过实际案例研究,展示了CMD在系统管理、网络配置和自动化任务中的广泛应用。研究表明,CMD作为Windows系统的重要工具,在提高工作效率和系统管理能力方面具有显著优势。本文旨在为读者提供全面的CMD使用指南,帮助其更
- FreeRTOS之内存管理
2401_85904908
单片机stm32arm开发开发语言
文章目录选用heap函数pvPortMalloc/vPortFreexPortGetFreeHeapSizexPortGetMinimumEverFreeHeapSizemalloc失败的钩子函数选用文件优点缺点heap_1.c内存分配逻辑简单,执行时间可确定仅能分配内存,无法回收已分配的内存heap_2.c支持动态内存分配,能实现最佳匹配(找到最适合请求大小的空闲内存块)会产生内存碎片,内存分配
- 1分钟看懂React的useEffect变形记
前端CV攻城狮
react.js前端前端框架
useEffect执行时机:组件初始化,组件更新(组件内state变化)useEffect(()=>{})执行时机:组件初始化useEffect(()=>{},[])执行时机:组件初始化,依赖的状态发生变化(X可多个)useEffect(()=>{},[X])执行时机:组件卸载useEffect(()=>{return()=>{console.log(组件卸载)}})执行时机:组件卸载,依赖的状态
- Python学习总结
serve the people
巨人的肩膀python开发语言
第一个python程序print("HelloWorld")#缩进一般4个空格键或者1个tab键,但是所有代码块语句必须是相同的缩进,这个必须严格执行,不同的缩进会导致程序不能运行,不能混用空格和tabifTrue:print("True")else:print("False")python注释符单行注释(行注释)#print("HelloWorld")多行注释(块注释)'''print("Hel
- C++11使用mutex和condition_variable实现线程同步
追烽少年x
C++基础c++
C++11使用mutex和condition_variable实现线程同步在实现项目的过程中,突然有一个问题:C++中A、B、C三个线程模拟购买100张车票,A输出99,B输出98,C输出97,然后又循环A输出96,B95,C94,直到0,使用线程同步,如何实现?这是一种按顺序执行线程的问题,应该实现?代码如下:#include#include#include#include#include//共
- C#使用winform实现简单的梯形图指令编译和执行,带编译器和虚拟机代码
isyoungboy
c#java开发语言
gui效果图,gui代码太长了就不贴了编译结果LD,test3NOT,STORE,TMP1LD,test1OR,LD,TMP1OUT,test2LD,TMP1RST,testLD,TMP1OUT,test22LD,TMP1OUT,test4LD,TMP1CALL,放料编译器代码usingSystem.Collections.Generic;usingSystem.Linq;namespaceLDE
- react基本功
码林鼠
react.js前端javascript
useLayoutEffectuseLayoutEffect用于在浏览器重新绘制屏幕之前同步执行代码。它与useEffect相同,但执行时机不同。主要特点执行时机:useLayoutEffect在DOM更新完成后同步执行,但在浏览器绘制之前。这使得它可以在浏览器渲染之前读取和修改DOM,避免视觉上的闪烁或不一致。适用场景:主要用于需要同步调整布局的副作用操作,例如测量DOM元素的尺寸(如高度、宽度
- AI 驱动的软件测试革命:从自动化到智能化的进阶之路
綦枫Maple
AI+软件测试人工智能自动化运维
引言:软件测试的智能化转型浪潮在数字化转型加速的今天,软件产品的迭代速度与复杂度呈指数级增长。传统软件测试依赖人工编写用例、执行测试的模式,已难以应对快速交付与高质量要求的双重挑战。人工智能技术的突破为测试领域注入了新动能,通过机器学习、深度学习、自然语言处理等技术,测试流程正从“被动验证”向“主动预防”演进。本文将深入探讨AI与软件测试的融合路径,结合技术原理、工具实践与行业趋势,为读者呈现一幅
- java 读取resource文件夹文件_Java 获取Resource目录下的文件解决办法
鬼斧神工119
java读取resource文件夹文件
该楼层疑似违规已被系统折叠隐藏此楼查看此楼Java获取Resource目录下的文件有两种方式:Java代码中的类,要获取Resource资源文件目录下文件绝对路径寻址注意这个/址的是根目录,用绝对路径,可能会出现的问题是,你的程序在windows上可以用,但是在linux不能用,原因在于,你这根目录在windows环境址你的src目录放到linux环境,就可能执行你linux的根目录了,会导致fi
- Nginx如何实现 TCP和UDP代理?
m0_74824755
面试学习路线阿里巴巴nginxtcp/ipudp
文章目录前言Nginx之TCP和UDP代理工作原理示意图配置文件和命令参数注释基本命令配置实例说明TCP代理实例UDP代理实例总结前言Nginx是一个高性能的HTTP和反向代理服务器,同时也支持TCP/UDP代理。在1.9.13版本后,Nginx已经支持端口转发,包括TCP和UDP协议。Nginx的TCP/UDP代理功能允许它作为一个中间人,接收来自客户端的TCP或UDP请求,并将这些请求转发到指
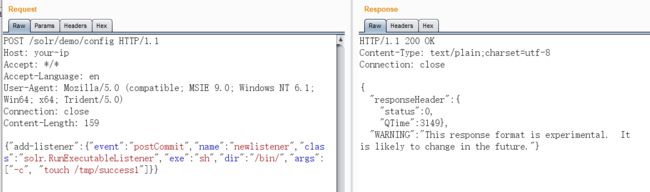
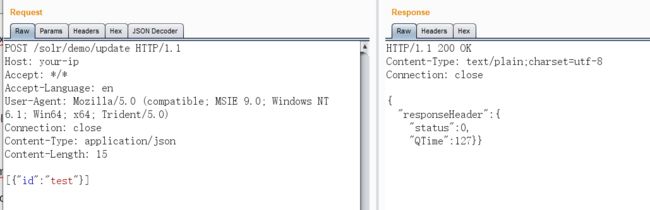
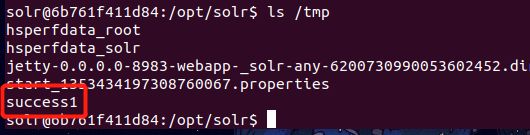
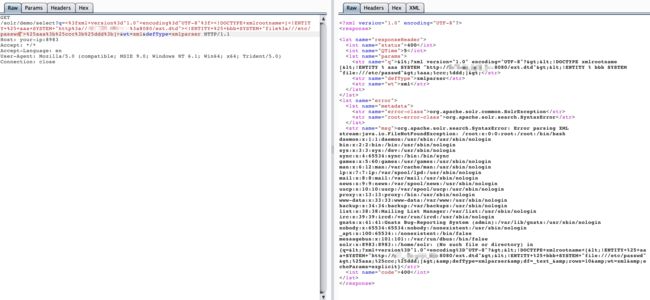
- 2025年渗透测试面试题总结-长某亭科技-安全服务工程师(一面)(题目+回答)
独行soc
2025年渗透测试面试指南面试职场和发展安全红蓝攻防护网2025科技
网络安全领域各种资源,学习文档,以及工具分享、前沿信息分享、POC、EXP分享。不定期分享各种好玩的项目及好用的工具,欢迎关注。目录长某亭科技-安全服务工程师(一面)1.SQL注入原理与代码层面成因原理代码层面成因漏洞触发场景2.XSS漏洞原理(代码层面)原理代码层面成因漏洞触发场景3.OWASPTop10漏洞(2023版)4.SQL注入防御方案5.SQL注入绕过防护6.护网行动工作内容7.学校攻
- 【从零开始学java】第1章,基础知识入门,小白零基础可看,笔记整理
莉莉鸟
java学习
java基础11注释标志符关键字注释注释并不会被执行,是写给人类看的,书写注释是一个很好的习惯平时写代码一定要注意规范单行注释//多行注释/*注释*/文档注释/**注释*/2标识符关键字abstract:用于声明抽象类或抽象方法。assert:用于调试时进行断言。boolean:表示布尔类型(true或false)。break:跳出当前循环或switch语句。byte:表示字节数据类型。case:
- 【技术干货】三大常见网络攻击类型详解:DDoS/XSS/中间人攻击,原理、危害及防御方案
挣扎与觉醒中的技术人
网络安全入门及实战ddosxss前端网络
1.DDoS攻击1.1什么是DDoS攻击?DDoS(DistributedDenialofService,分布式拒绝服务攻击)通过操控大量“僵尸设备”(Botnet)向目标服务器发送海量请求,耗尽服务器资源(带宽、CPU、内存),导致正常用户无法访问服务。1.2攻击原理与分类流量型攻击:如UDP洪水、ICMP洪水,通过发送大量无效数据包占用带宽。协议型攻击:如SYN洪水攻击,利用TCP三次握手漏洞
- 操作系统概述
Wlq0415
操作系统系统架构
操作系统定义操作系统(OS)是管理计算机硬件和软件资源的系统软件,旨在提供一个操作环境,使用户和应用程序能够高效地使用计算机资源。它通过合理组织计算机工作流程、控制程序执行并提供友好接口,确保用户能够顺利进行各种操作。操作系统的作用资源管理:操作系统管理计算机中运行的程序,并分配CPU、内存、输入输出设备等各种软硬件资源,确保它们高效运作。人机接口:为用户提供友好的界面,使用户能够方便地与计算机进
- centos安装mysql报错:mysql-community-client-plugins-8.0、o Presto metadata available for mysql80-community
其实她不懂
centosmysqllinux
执行sudoyum-yinstallmysql-community-server命令刚开始报错mysql-community-client-plugins-8.0.40-1.el7.x86_64.rpm的公钥尚未安装失败的软件包是:mysql-community-client-plugins-8.0.40-1.el7.x86_64GPG密钥配置为:file:///etc/pki/rpm-gpg/R
- 树莓派-C++之异常
lalalaouhei
c++开发语言后端
2021SC@SDUSCC++异常用官方的话来说就是程序在执行过程中产生的问题,换句通俗的话来讲就是程序执行的出现的异常,比如程序崩了、内存泄漏了、数组越界以及其他异常信息的出现,又如运行时耗尽了内存或遇到意外的非法输入。一个简单的例子就是尝试除以零的操作。异常存在于程序的正常功能之外,并要求程序立即处理。不能不处理异常,异常是足够重要的,使程序不能继续正常执行的事件。一、异常处理所谓“处理”,可
- 1:1精准还原!用Python+Adobe Acrobat DC实现PDF转Word全自动化
朴拙Python交易猿
pythonpdfword
以下是您请求的博客文章,包含详细的代码注释及分步解析:1:1精准还原!用Python+AdobeAcrobatDC实现PDF转Word全自动化一、为什么要选择AdobeAcrobatDC?作为PDF标准的制定者,AdobeAcrobatDC在格式转换领域具有无可比拟的优势:精准还原-保持原始布局、字体和格式表格保留-完整保留表格结构和数据批量处理-支持自动化执行重复任务OCR支持-自动识别扫描件中
- Java八股文九:Redis
m78探索者
java八股文
文章目录九、Redis1、数据类型2、Redis如何实现key的过期删除?3、Redis的持久化机制4、如何解决Redis缓存雪崩和缓存穿透?5、如何使用Redis实现消息队列?九、Redis1、数据类型String常用命令:set,get,decr,incr,mget等。Hash常用命令:hget,hset,hgetall等List常用命令:lpush,rpush,lpop,rpop,lrang
- 多进程多线程浏览器(比如 Chrome)
暴走的李丹
线程:是程序执行中一个单一的顺序控制流程,是程序执行流的最小单元。多线程:是指程序中包含多个执行流,即在一个程序中可以同时运行多个不同的线程来执行不同的任务,也就是说允许单个程序创建多个并行执行的线程来完成各自的任务。进程:是应用程序的执行实例,每一个进程都是由私有的虚拟地址空间、代码、数据和其它系统资源所组成。多进程:多进程指的是在同一个时间里,同一个计算机系统中如果允许两个或两个以上的进程处于
- 【5分钟背八股】redis主从复制的原理?持久化RDB和AOF?
熬夜加班写代码
Java面试程序员redisjava后端面试
面试官:Redis主从复制的原理?主从复制机制当一个master实例和一个slave实例连接正常时,master会发送一连串的命令流来保持对slave的更新,以便于将自身数据集的改变复制给slave,:包括客户端的写入、key的过期或被逐出等等。当master和slave之间的连接断开之后,因为网络问题、或者是主从意识到连接超时,slave重新连接上master并会尝试进行部分重同步:这意味着它会
- Java-Define and throw a dedicated exception instead of using a generic one
ZHOU_VIP
MACjava开发语言
为了提高代码的可读性和可维护性,使用自定义异常比使用通用异常更为合适。自定义异常可以帮助你更精确地描述错误情况,并且可以在捕获异常时执行特定的处理逻辑。以下是定义和抛出自定义异常的步骤:定义自定义异常类:创建一个新的类,继承自Exception或RuntimeException类。抛出自定义异常:在需要抛出异常的地方,使用throw关键字抛出自定义异常实例。下面是一个简单的示例,展示了如何定义和抛
- Etherpad开发部署(windows版)
舌尖上的五香
编辑器
项目地址:https://gitcode.com/gh_mirrors/et/etherpad-liteWindows用户可以选择预建的安装包或手动安装。若通过Git克隆,记得执行bin\installOnWindows.bat。start.bat启动Etherpad配置及管理功能配置文件settings.json搜索users,去掉注释重启服务器killallnode测试管理员功能http://
- MAC-禁止百度网盘自动升级更新
ZHOU_VIP
MACjava
通过终端禁用更新服务(推荐)此方法直接移除百度网盘的自动更新组件,无需修改系统文件。步骤:1.关闭百度网盘后台进程按下Command+Space→输入「活动监视器」→搜索BaiduNetdisk或UpdateAgent→结束相关进程。2.删除自动更新配置文件打开终端,依次执行以下命令(按顺序操作):#切换到root权限(输入密码)sudosu#删除百度网盘更新配置文件rm-rf/Library/L
- FastExcel/EasyExcel简介以及源码解析
舌尖上的五香
java
简介官网地址GitHub地址基于MIT协议发展历史由EasyExcel发展而来2018/02/07:发布1.0.02019/09/17:发布2.0.02021/10/21:发布3.0.12024/06/18:发布4.0.02024/11/06:进入维护模式2024/12/05:发布FastExcel1.0.0主要特性高性能读写简单易用流式操作读取执行行数技术原理内存优化:基于流式读取技术,不需要一
- tableau报表第三方免登陆配置
时光不负追梦人
tableau报表java免登陆
获取Tableau凭证,实现报表在第三方的免登陆。分为三步第一步:在Tableau服务器上命令行设置授信白名单配置白名单cdC:\ProgramFiles\Tableau\TableauServer\bintabadminstop//可以配置多个IP,也可以只配置一个;多个时用英文逗号分开且增加一空格tabadminsetwgserver.trusted_hosts"10.88.233.64,10
- C++之list删除元素
csdn_zhangchunfeng
C++VS技术管理索引列表c++
C++之list删除元素对容器list存储的元素执行删除操作的时候,一般都是使用其成员函数实现的:(1)clear():删除list容器中的所有元素(2)remove(value):删除容器中所有为value的元素(3)remove_if():删除容器中满足条件的元素(4)unique():删除容器中相邻的重复元素,只留下一个(5)erase():删除list容器中指定位置处的元素,也可以删除容器
- java线程Thread和Runnable区别和联系
zx_code
javajvmthread多线程Runnable
我们都晓得java实现线程2种方式,一个是继承Thread,另一个是实现Runnable。
模拟窗口买票,第一例子继承thread,代码如下
package thread;
public class ThreadTest {
public static void main(String[] args) {
Thread1 t1 = new Thread1(
- 【转】JSON与XML的区别比较
丁_新
jsonxml
1.定义介绍
(1).XML定义
扩展标记语言 (Extensible Markup Language, XML) ,用于标记电子文件使其具有结构性的标记语言,可以用来标记数据、定义数据类型,是一种允许用户对自己的标记语言进行定义的源语言。 XML使用DTD(document type definition)文档类型定义来组织数据;格式统一,跨平台和语言,早已成为业界公认的标准。
XML是标
- c++ 实现五种基础的排序算法
CrazyMizzz
C++c算法
#include<iostream>
using namespace std;
//辅助函数,交换两数之值
template<class T>
void mySwap(T &x, T &y){
T temp = x;
x = y;
y = temp;
}
const int size = 10;
//一、用直接插入排
- 我的软件
麦田的设计者
我的软件音乐类娱乐放松
这是我写的一款app软件,耗时三个月,是一个根据央视节目开门大吉改变的,提供音调,猜歌曲名。1、手机拥有者在android手机市场下载本APP,同意权限,安装到手机上。2、游客初次进入时会有引导页面提醒用户注册。(同时软件自动播放背景音乐)。3、用户登录到主页后,会有五个模块。a、点击不胫而走,用户得到开门大吉首页部分新闻,点击进入有新闻详情。b、
- linux awk命令详解
被触发
linux awk
awk是行处理器: 相比较屏幕处理的优点,在处理庞大文件时不会出现内存溢出或是处理缓慢的问题,通常用来格式化文本信息
awk处理过程: 依次对每一行进行处理,然后输出
awk命令形式:
awk [-F|-f|-v] ‘BEGIN{} //{command1; command2} END{}’ file
[-F|-f|-v]大参数,-F指定分隔符,-f调用脚本,-v定义变量 var=val
- 各种语言比较
_wy_
编程语言
Java Ruby PHP 擅长领域
- oracle 中数据类型为clob的编辑
知了ing
oracle clob
public void updateKpiStatus(String kpiStatus,String taskId){
Connection dbc=null;
Statement stmt=null;
PreparedStatement ps=null;
try {
dbc = new DBConn().getNewConnection();
//stmt = db
- 分布式服务框架 Zookeeper -- 管理分布式环境中的数据
矮蛋蛋
zookeeper
原文地址:
http://www.ibm.com/developerworks/cn/opensource/os-cn-zookeeper/
安装和配置详解
本文介绍的 Zookeeper 是以 3.2.2 这个稳定版本为基础,最新的版本可以通过官网 http://hadoop.apache.org/zookeeper/来获取,Zookeeper 的安装非常简单,下面将从单机模式和集群模式两
- tomcat数据源
alafqq
tomcat
数据库
JNDI(Java Naming and Directory Interface,Java命名和目录接口)是一组在Java应用中访问命名和目录服务的API。
没有使用JNDI时我用要这样连接数据库:
03. Class.forName("com.mysql.jdbc.Driver");
04. conn
- 遍历的方法
百合不是茶
遍历
遍历
在java的泛
- linux查看硬件信息的命令
bijian1013
linux
linux查看硬件信息的命令
一.查看CPU:
cat /proc/cpuinfo
二.查看内存:
free
三.查看硬盘:
df
linux下查看硬件信息
1、lspci 列出所有PCI 设备;
lspci - list all PCI devices:列出机器中的PCI设备(声卡、显卡、Modem、网卡、USB、主板集成设备也能
- java常见的ClassNotFoundException
bijian1013
java
1.java.lang.ClassNotFoundException: org.apache.commons.logging.LogFactory 添加包common-logging.jar2.java.lang.ClassNotFoundException: javax.transaction.Synchronization
- 【Gson五】日期对象的序列化和反序列化
bit1129
反序列化
对日期类型的数据进行序列化和反序列化时,需要考虑如下问题:
1. 序列化时,Date对象序列化的字符串日期格式如何
2. 反序列化时,把日期字符串序列化为Date对象,也需要考虑日期格式问题
3. Date A -> str -> Date B,A和B对象是否equals
默认序列化和反序列化
import com
- 【Spark八十六】Spark Streaming之DStream vs. InputDStream
bit1129
Stream
1. DStream的类说明文档:
/**
* A Discretized Stream (DStream), the basic abstraction in Spark Streaming, is a continuous
* sequence of RDDs (of the same type) representing a continuous st
- 通过nginx获取header信息
ronin47
nginx header
1. 提取整个的Cookies内容到一个变量,然后可以在需要时引用,比如记录到日志里面,
if ( $http_cookie ~* "(.*)$") {
set $all_cookie $1;
}
变量$all_cookie就获得了cookie的值,可以用于运算了
- java-65.输入数字n,按顺序输出从1最大的n位10进制数。比如输入3,则输出1、2、3一直到最大的3位数即999
bylijinnan
java
参考了网上的http://blog.csdn.net/peasking_dd/article/details/6342984
写了个java版的:
public class Print_1_To_NDigit {
/**
* Q65.输入数字n,按顺序输出从1最大的n位10进制数。比如输入3,则输出1、2、3一直到最大的3位数即999
* 1.使用字符串
- Netty源码学习-ReplayingDecoder
bylijinnan
javanetty
ReplayingDecoder是FrameDecoder的子类,不熟悉FrameDecoder的,可以先看看
http://bylijinnan.iteye.com/blog/1982618
API说,ReplayingDecoder简化了操作,比如:
FrameDecoder在decode时,需要判断数据是否接收完全:
public class IntegerH
- js特殊字符过滤
cngolon
js特殊字符js特殊字符过滤
1.js中用正则表达式 过滤特殊字符, 校验所有输入域是否含有特殊符号function stripscript(s) { var pattern = new RegExp("[`~!@#$^&*()=|{}':;',\\[\\].<>/?~!@#¥……&*()——|{}【】‘;:”“'。,、?]"
- hibernate使用sql查询
ctrain
Hibernate
import java.util.Iterator;
import java.util.List;
import java.util.Map;
import org.hibernate.Hibernate;
import org.hibernate.SQLQuery;
import org.hibernate.Session;
import org.hibernate.Transa
- linux shell脚本中切换用户执行命令方法
daizj
linuxshell命令切换用户
经常在写shell脚本时,会碰到要以另外一个用户来执行相关命令,其方法简单记下:
1、执行单个命令:su - user -c "command"
如:下面命令是以test用户在/data目录下创建test123目录
[root@slave19 /data]# su - test -c "mkdir /data/test123"
- 好的代码里只要一个 return 语句
dcj3sjt126com
return
别再这样写了:public boolean foo() { if (true) { return true; } else { return false;
- Android动画效果学习
dcj3sjt126com
android
1、透明动画效果
方法一:代码实现
public View onCreateView(LayoutInflater inflater, ViewGroup container, Bundle savedInstanceState)
{
View rootView = inflater.inflate(R.layout.fragment_main, container, fals
- linux复习笔记之bash shell (4)管道命令
eksliang
linux管道命令汇总linux管道命令linux常用管道命令
转载请出自出处:
http://eksliang.iteye.com/blog/2105461
bash命令执行的完毕以后,通常这个命令都会有返回结果,怎么对这个返回的结果做一些操作呢?那就得用管道命令‘|’。
上面那段话,简单说了下管道命令的作用,那什么事管道命令呢?
答:非常的经典的一句话,记住了,何为管
- Android系统中自定义按键的短按、双击、长按事件
gqdy365
android
在项目中碰到这样的问题:
由于系统中的按键在底层做了重新定义或者新增了按键,此时需要在APP层对按键事件(keyevent)做分解处理,模拟Android系统做法,把keyevent分解成:
1、单击事件:就是普通key的单击;
2、双击事件:500ms内同一按键单击两次;
3、长按事件:同一按键长按超过1000ms(系统中长按事件为500ms);
4、组合按键:两个以上按键同时按住;
- asp.net获取站点根目录下子目录的名称
hvt
.netC#asp.nethovertreeWeb Forms
使用Visual Studio建立一个.aspx文件(Web Forms),例如hovertree.aspx,在页面上加入一个ListBox代码如下:
<asp:ListBox runat="server" ID="lbKeleyiFolder" />
那么在页面上显示根目录子文件夹的代码如下:
string[] m_sub
- Eclipse程序员要掌握的常用快捷键
justjavac
javaeclipse快捷键ide
判断一个人的编程水平,就看他用键盘多,还是鼠标多。用键盘一是为了输入代码(当然了,也包括注释),再有就是熟练使用快捷键。 曾有人在豆瓣评
《卓有成效的程序员》:“人有多大懒,才有多大闲”。之前我整理了一个
程序员图书列表,目的也就是通过读书,让程序员变懒。 写道 程序员作为特殊的群体,有的人可以这么懒,懒到事情都交给机器去做,而有的人又可
- c++编程随记
lx.asymmetric
C++笔记
为了字体更好看,改变了格式……
&&运算符:
#include<iostream>
using namespace std;
int main(){
int a=-1,b=4,k;
k=(++a<0)&&!(b--
- linux标准IO缓冲机制研究
音频数据
linux
一、什么是缓存I/O(Buffered I/O)缓存I/O又被称作标准I/O,大多数文件系统默认I/O操作都是缓存I/O。在Linux的缓存I/O机制中,操作系统会将I/O的数据缓存在文件系统的页缓存(page cache)中,也就是说,数据会先被拷贝到操作系统内核的缓冲区中,然后才会从操作系统内核的缓冲区拷贝到应用程序的地址空间。1.缓存I/O有以下优点:A.缓存I/O使用了操作系统内核缓冲区,
- 随想 生活
暗黑小菠萝
生活
其实账户之前就申请了,但是决定要自己更新一些东西看也是最近。从毕业到现在已经一年了。没有进步是假的,但是有多大的进步可能只有我自己知道。
毕业的时候班里12个女生,真正最后做到软件开发的只要两个包括我,PS:我不是说测试不好。当时因为考研完全放弃找工作,考研失败,我想这只是我的借口。那个时候才想到为什么大学的时候不能好好的学习技术,增强自己的实战能力,以至于后来找工作比较费劲。我
- 我认为POJO是一个错误的概念
windshome
javaPOJO编程J2EE设计
这篇内容其实没有经过太多的深思熟虑,只是个人一时的感觉。从个人风格上来讲,我倾向简单质朴的设计开发理念;从方法论上,我更加倾向自顶向下的设计;从做事情的目标上来看,我追求质量优先,更愿意使用较为保守和稳妥的理念和方法。
&