【环境需求】
①rpm -ivh bind-9.3.6-4.P1.el5.rpm
②rpm -ivh bind-utils-9.3.6-4.P1.el5.i386.rpm(默认已安装)
③rpm -ivh bind-chroot-9.3.6-4.P1.el5.i386.rpm
④rpm -ivh caching-nameserver-9.3.6-4.P1.el5.i386.rpm
(生成区域配置样例文件)
【安装后】
根目录: /var/named/chroot/
配置样例文件:/var/named/chroot/etc/named.caching-nameserver.conf
区域配置文件:/var/named/chroot/etc/named.rfc1912.zones
区域样例文件:/var/named/chroot/var/named/localhost.zone(localdomain.zone)
【配置过程】
①cp -pv named.caching-nameserver.conf named.conf
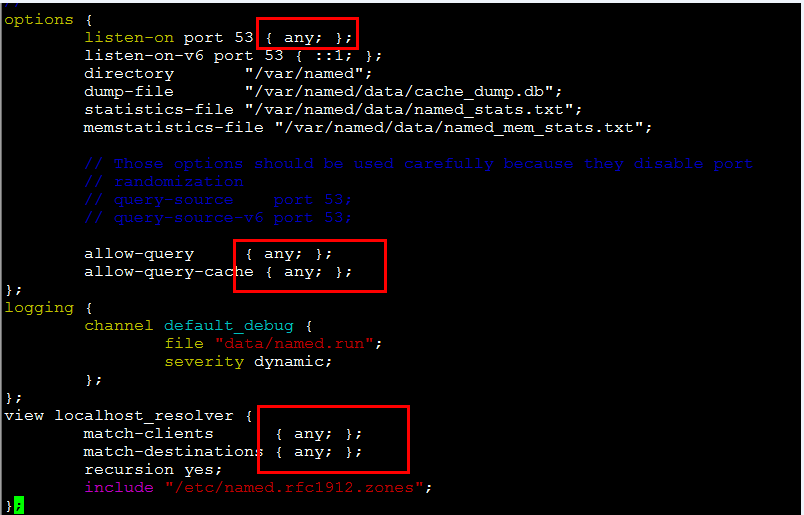
②vim named.conf(配置DNS服务配置文件)
③vim named.rfc1912.zones(区域配置文件--->添加区域
--->abc.com)
④cp -pv localhost.zone abc.com.zone(产生区域文件
--->abc.com.zone)
⑤vim abc.com.zone(配置区域文件--->abc.com.zone)
注意:修改配置文件后执行rndc reload 不重启重新加载配置文件
⑥service named start
⑦chkconfig named on
配置样例一:基本的区域配置
①vim /var/named/chroot/etc/named.rfc1912.zones
②cp -pv localhost.zone abc.com.zone
vim /var/named/chroot/var/named/abc.com.zone
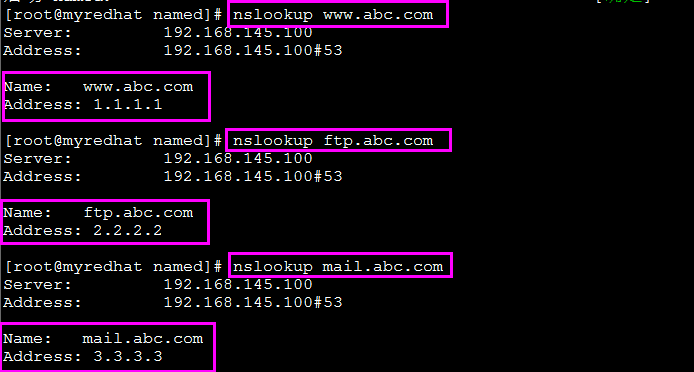
③解析测试
vim /etc/resolv.conf-----> nameserver 192.168.145.100
配置样例二:反向DNS解析配置
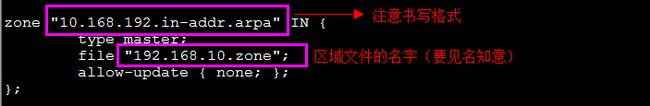
①vim /var/named/chroot/etc/named.rfc1912.zones
②vim /var/named/chroot/etc/named.conf
③cp -pv name.local 192.168.10.zone
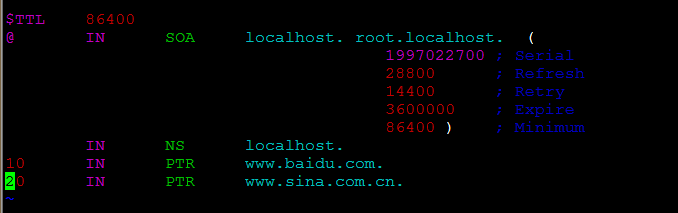
vim /var/named/chroot/var/named/192.168.10.zone
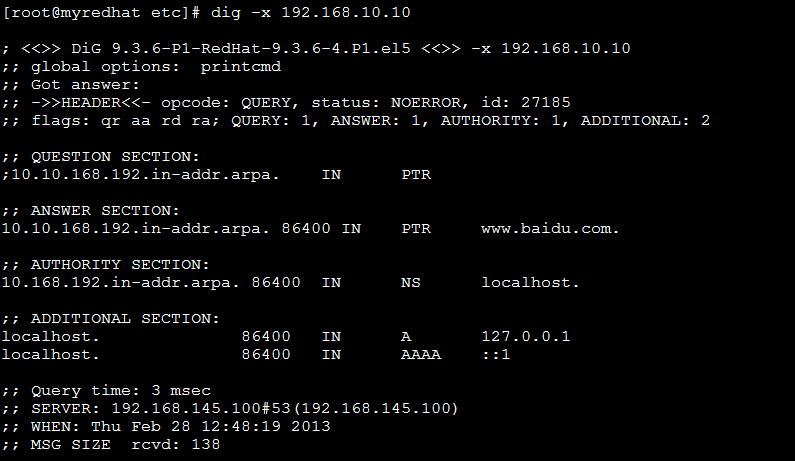
④解析测试
vim /etc/resolv.conf-----> nameserver 192.168.145.100
配置样例三:ACL、视图的概念应用实例
【实验拓扑】
【实验设备】
H3C防火墙一台(内网出口路由器)
Red Hat Enterprise Linux Server release 5.4 (DNS服务器)
Win Service 2003 虚拟机一台(测试PC)
【实验目的】
①理解DNS服务器的视图的概念.
②实现外部访问内部服务器,DNS解析时进行地址伪装,转为内网
出扣路由器的外口接口地址,保证内网服务器的安全.
【DNS服务器配置】
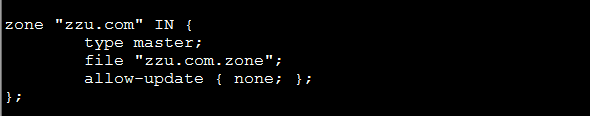
①vim /var/named/chroot/etc/named.rfc1912.zones
②vim /var/named/chroot/etc/named.conf
③cp -pv localhost.zone zzu.com.zone
vim /var/named/chroot/var/named/zzu.com.zone
④cp -pv localhost.zone zzu.com.zone1
vim /var/named/chroot/var/named/zzu.com.zone1
【防火墙配置】
#
sysname firew
#
firewall packet-filter enable
firewall packet-filter default permit
#
insulate
#
firewall statistic system enable
#
ip http shutdown
#
radius scheme system
server-type extended
#
domain system
#
local-user admin
password cipher .]@USE=B,53Q=^Q`MAF4<1!!
service-type telnet terminal
level 3
service-type ftp
#
interface Aux0
async mode flow
#
interface Ethernet0/0
ip address 192.168.102.254 255.255.255.0
#
interface Ethernet0/1
ip address 61.130.130.1 255.255.255.0
nat server protocol udp global 61.130.130.1 dns inside 192.168.102.100 dns
#
interface Ethernet0/2
#
interface Ethernet0/3
#
interface Ethernet0/4
#
interface Encrypt1/0
#
interface NULL0
#
firewall zone local
set priority 100
#
firewall zone trust
add interface Ethernet0/0
add interface Ethernet0/1
set priority 85
#
firewall zone untrust
set priority 5
#
firewall zone DMZ
set priority 50
#
firewall interzone local trust
#
firewall interzone local untrust
#
firewall interzone local DMZ
#
firewall interzone trust untrust
#
firewall interzone trust DMZ
#
firewall interzone DMZ untrust
#
FTP server enable
#
user-interface con 0
user-interface aux 0
user-interface vty 0 4
authentication-mode scheme
#
return
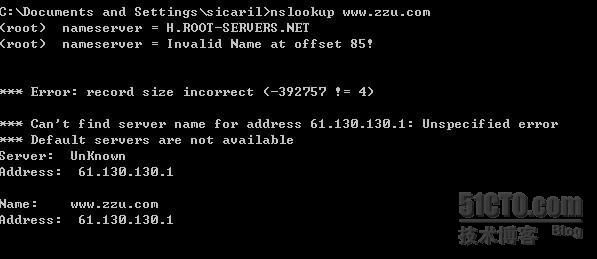
【解析测试】
当主机ip是lan-view视图允许的地址范围时(192.168.102.0/24)
当内部局域网主机访问内网www服务器时,nslookup解析结果得到的服务器ip为DNS在内网的地址
当内部局域网主机访问内网mail服务器时,nslookup解析结果得到的服务器ip为MAIL在内网的地址
当主机ip不是lan-view视图允许的地址范围时,将会匹配外部视图,
Nslookup得到的www服务器的地址是内网出口路由器的开口地址.