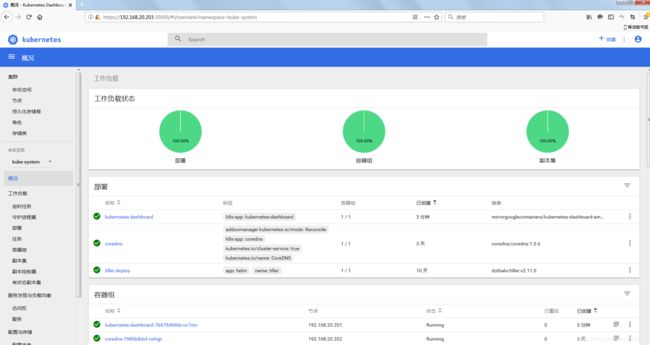
部署Kubernetes Dashboard 及监控组件 Heapster
部署Dashboard
项目地址:https://github.com/kubernetes/dashboard
1.下载官方提供的 Dashboard 组件部署的 yaml 文件
wget https://raw.githubusercontent.com/kubernetes/dashboard/v1.10.1/src/deploy/recommended/kubernetes-dashboard.yaml
也可以使用Kubernetes中addon库中的yaml文件部署,地址在这里dashboard addon
2.修改 yaml 文件中的镜像
由于国内防火墙的问题导致无法从k8s.gcr.io仓库中拉取镜像,因此需要修改镜像源:

也可以修改成阿里的地址:
registry.cn-hangzhou.aliyuncs.com/google_containers
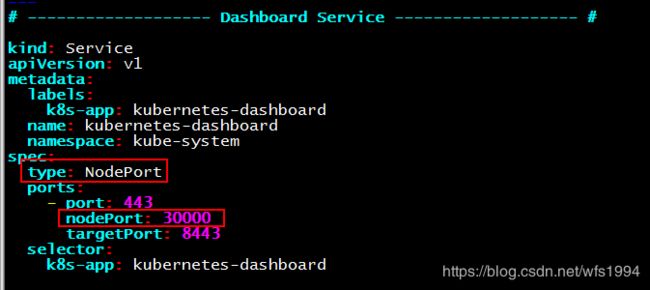
3.修改 yaml 文件中的 Dashboard Service,暴露服务使外部能够访问
Dashboard有多种方式可以访问:
kubectl proxy方式:只支持127.0.0.1和localhost为来源地址的方式访问,需要配置SSH隧道,比较麻烦,不建议使用。Node Port方式:该方式容易配置,只建议在开发环境的环境中使用。本文采用这种方式实现。Ingress方式:通过Ingress Controller来暴露应用,比较灵活,是最推荐的方式,但较复杂。参考文章API Server方式:由于API服务器是公开的,可以从外部访问,是比较推荐的方式。参考文章
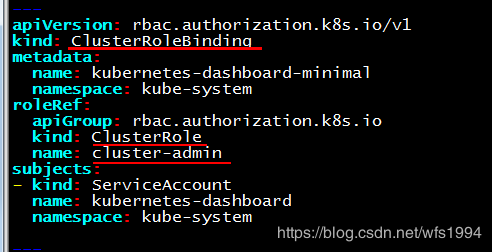
4.修改yaml文件中的授权
默认的RoleBinding定义了Dashboard的角色绑定,其名称为kubernetes-dashboard-minimal,roleRef中为被绑定的角色,也叫kubernetes-dashboard-minimal,subjects中为绑定的用户:kubernetes-dashboard。
这样我们在启Dashboard后看到很多权限错误提示,主要是system:serviceaccount:kube-system:kubernetes-dashboard的权限不足引起的。
我们可以更改RoleBinding修改为ClusterRoleBinding,并且修改roleRef中的kind和name,使用cluster-admin这个非常牛逼的CusterRole(超级用户权限,其拥有访问kube-apiserver的所有权限):
5.启动 Dashboard
kubectl apply -f kubernetes-dashboard.yaml
6.访问 Dashboard
地址:https://
注意:dashboard的默认webui证书是自动生成的,由于时间和名称存在问题,导致谷歌和ie浏览器无法打开登录界面,经过测试Firefox可以正常打开,稍后解决这个问题。

7.获取登录 Dashboard 的令牌 (Token)
命令:kubectl -n kube-system describe secret $(kubectl -n kube-system get secret |grep 'dashboard-token' |awk '{print $1}')
# kubectl -n kube-system describe secret $(kubectl -n kube-system get secret |grep 'dashboard-token' |awk '{print $1}')
Name: kubernetes-dashboard-token-bwcp5
Namespace: kube-system
Labels:
Annotations: kubernetes.io/service-account.name: kubernetes-dashboard
kubernetes.io/service-account.uid: 8b0e6813-1d4e-11e9-b75b-000c29e44b03
Type: kubernetes.io/service-account-token
Data
====
ca.crt: 1359 bytes
namespace: 11 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJrdWJlcm5ldGVzLWRhc2hib2FyZC10b2tlbi1id2NwNSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50LnVpZCI6IjhiMGU2ODEzLTFkNGUtMTFlOS1iNzViLTAwMGMyOWU0NGIwMyIsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXN5c3RlbTprdWJlcm5ldGVzLWRhc2hib2FyZCJ9.DZgBItO6c0VkBZWFFH4W69vwCvdNI7hKxB0K15yWJBKXONg1MALYd8nAoLC6iiq8xz3DdHjAeAfBgv8efj5GxfW1vcRFgClV9NlVxnZ9B8L0MBIERLuYTlWGPk7ZSWknTFe165GIBEGFoTdt4gvHpLbazbHaotBV3ze863MrNIECTIJMe0yAzUcKmY2biGmB_TD4-kxrF_0mAwEFPU7NFKdogxsKlfJ4CF04KjHOklwbp6XIpsVR-c28rD62FHTKXY8pv5U7THh1uPaqzQJOLgft-OXhnlMIuXKywoKBi01yACIPeoobikFVezJZfBNodpi4tuLppNClKZ4nSU_24g
解决谷歌浏览器无法访问的问题
前面在第六步的时候我们提到过dashboard的默认webui证书是自动生成的,由于时间和名称存在问题,导致谷歌和ie浏览器无法打开登录界面。
通过谷歌浏览器访问,发现居然无法继续:

通过Firefox发现证书是0001年1月签发的,怀疑其他浏览器打不开和证书过期有关系。
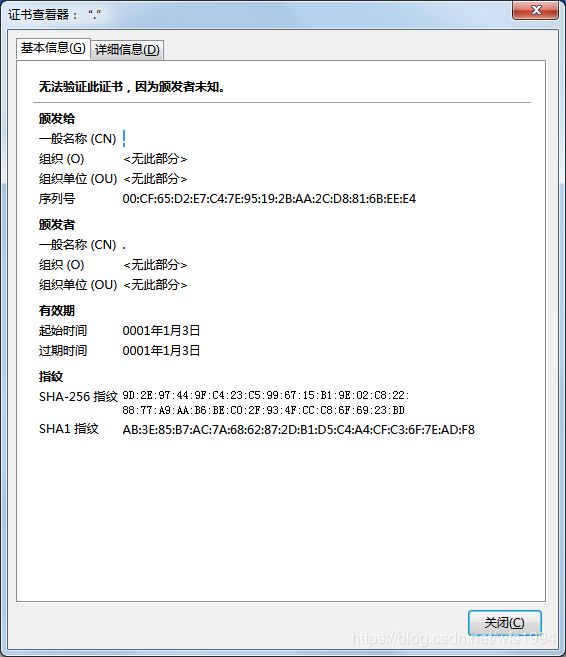
解决证书过期问题
(1)生成证书:通过openssl生成自签名证书
openssl genrsa -out dashboard.key 2048
openssl req -x509 -new -nodes -key dashboard.key -subj "/CN=192.168.20.203" -days 3650 -out dashboard.crt
(2)删除dashboard服务,修改配置文件:将配置文件中创建secret的配置文件信息去掉
kubectl delete -f kubernetes-dashboard.yaml
将配置文件中如下内容注释或删除:
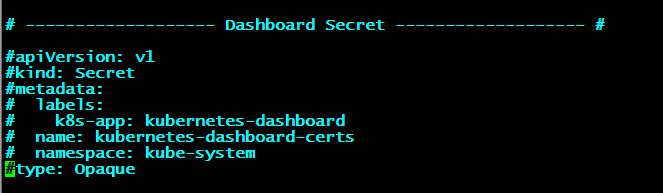
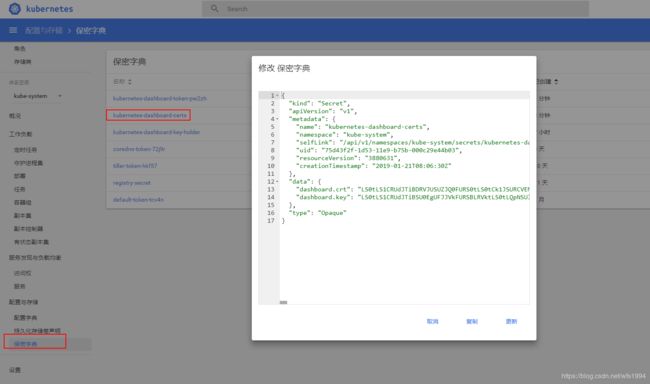
(3)重现生成secret:创建同名称的secret,名称为: kubernetes-dashboard-certs
kubectl -n kube-system create secret generic kubernetes-dashboard-certs --from-file=dashboard.key --from-file=dashboard.crt
(4)重新生成
kubectl apply -f kubernetes-dashboard.yaml

如上通过重新生成secret,解决了由于证书过期导致的谷歌浏览器无法访问的问题,再此基础上我们可以通过查看kubernetes-dashboard-certs的YAML文件,将里面的内容添加到kubernetes-dashboard.yaml文件中。
完整的配置文件如下所示:
# cat kubernetes-dashboard.yaml
# ------------------- Dashboard Secret ------------------- #
kind: Secret
apiVersion: v1
metadata:
name: kubernetes-dashboard-certs
namespace: kube-system
data:
dashboard.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURCVENDQWUyZ0F3SUJBZ0lKQUkwRGF0SUpQRGdwTUEwR0NTcUdTSWIzRFFFQkN3VUFNQmt4RnpBVkJnTlYKQkFNTURqRTVNaTR4TmpndU1qQXVNakF6TUI0WERURTVNREV4T0RBeE5UZzFPVm9YRFRJNU1ERXhOVEF4TlRnMQpPVm93R1RFWE1CVUdBMVVFQXd3T01Ua3lMakUyT0M0eU1DNHlNRE13Z2dFaU1BMEdDU3FHU0liM0RRRUJBUVVBCkE0SUJEd0F3Z2dFS0FvSUJBUUM2Qlhvd3U5eWY1aVF1aGRNSERuNHJaR1Jnb0g3UlZiMTQzVTRMVENndTJwTG0KQ3JFZGJUMWw2K1kwQ3lXWkxYNytFeTBSS0ZsL3BReXdIc1pqUk5FUXVVS0NXd2pTVVJKVWJMQ01oQnIxK0ptTApQSEx5NE1pcWR1UW1MSnJYbFg3QmtTN0g3OCt4ZUsrNGxLUWVibVJrQ3o4dlBDRmNZcmNHUEJTR0VyMTk4eWhwCnNXT2RMWHhNL0xmTDV6MGZjeGxZb1FWUlIzUjVUN1NqQVgvS3dJOFVHb3M3RUlXa2RMQzNnUndnN0xHMDVwTjcKa2ZBby9zT3hPQ09wQ0pJTUlnbFRaLzcvN1hBZllrUGJ4U1JPWGZ6bmw3NGtsZENIeWR0bGFaVXQrbVJ6SnFMagpwcXVxTy9uYnY4QmxqUXhUNzJNRC9zOWx5ZHJFa3ArRGplVzhUcjBOQWdNQkFBR2pVREJPTUIwR0ExVWREZ1FXCkJCUU9kK1pBa1d6QkFTNDlMT1JsMzNUVmYvN3lXVEFmQmdOVkhTTUVHREFXZ0JRT2QrWkFrV3pCQVM0OUxPUmwKMzNUVmYvN3lXVEFNQmdOVkhSTUVCVEFEQVFIL01BMEdDU3FHU0liM0RRRUJDd1VBQTRJQkFRQ0Q4Nkg1RHlCUQoyZ05rVW1HTFVJTllFZjVxT2g5N3g5NzMvdkgyc2RuRGFBTGxTcUduT2kxUWFzV2laMW5FZmJaZXVFcDcrajZHCmdmNmlKbDVyRnBGcnBSa1o3aUFiSFpTSGRqQktOVG1RZ3hZTU9NUzR5dmhuaXlHWGJsZjNITzlsdHlHd2xjVWQKRDYzaTRwOGdZY0I0c0ZxdVgwWnhCWkQ1WHViTVpuSjdIeFBxemJ3Y3Azd2JoK0d1dmRzbkg2T3djUDBVSUdGdgpTTFQyUVNQRlNDWnlWc0RaUE5yNDFhZ08yYWkzRldmdHQySXF4d2I1UVprMk1NaWdkelNiWTBjclA2b2xDY1ozClA2VStpVmR4VVBVL2tMZkxvVGllYm04Zkx5UXFmR0Q5bjU2TDhOejIyUVhCekNmRGUzTExUWGdvZTRqQk04VVMKRnl6dmE5bXpHSFozCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
dashboard.key: LS0tLS1CRUdJTiBSU0EgUFJJVkFURSBLRVktLS0tLQpNSUlFcEFJQkFBS0NBUUVBdWdWNk1MdmNuK1lrTG9YVEJ3NStLMlJrWUtCKzBWVzllTjFPQzB3b0x0cVM1Z3F4CkhXMDlaZXZtTkFzbG1TMSsvaE10RVNoWmY2VU1zQjdHWTBUUkVMbENnbHNJMGxFU1ZHeXdqSVFhOWZpWml6eHkKOHVESXFuYmtKaXlhMTVWK3daRXV4Ky9Qc1hpdnVKU2tIbTVrWkFzL0x6d2hYR0szQmp3VWhoSzlmZk1vYWJGagpuUzE4VFB5M3krYzlIM01aV0tFRlVVZDBlVSswb3dGL3lzQ1BGQnFMT3hDRnBIU3d0NEVjSU95eHRPYVRlNUh3CktQN0RzVGdqcVFpU0RDSUpVMmYrLysxd0gySkQyOFVrVGwzODU1ZStKSlhRaDhuYlpXbVZMZnBrY3lhaTQ2YXIKcWp2NTI3L0FaWTBNVSs5akEvN1BaY25heEpLZmc0M2x2RTY5RFFJREFRQUJBb0lCQUdKRmpuMjhZUnRmKzNGUQpaV0Z1K0p4MzFzZHRRbEhZbDlZSUk3aTRMT3BEc2lNeE5zd3k3Nkt1Y3RpL29zYy9UNzF0NS9zT2MrbUpDaURvCndTbWtLMFpJZUtoZzYxSWdYaXlYbHRWRTNQRmd1Y3ppekY4ZS9TT0ExNXFMS2VvR0lnYWthakJac2tFeFhyT0cKWXdWb2tFU0I1SWxSbk5Zdm1EMEU5RnEzLzc5UEZTSVNRQmJ4aHNYTkZXSGxFK2VTSzEvcDNBQm5MN0pKVWlaZQpJYXFrajJVdWFueHcxZEVzQWpucEQ5eVVud1ROeWZRcWc2Q1l1MlZzMGFVUk5JQWd6OFg1OUIwUm53RXRyMGlYCkluSHFnVGhOdXp3aWE1SXVyOW9mK3diNnZyZE05dUFDazJFYXYxc0J0eGdSTE1HWlZjdTUrU1BhWkFLcUlKYksKeE9jbUFvRUNnWUVBNHp3NWRMNzJTM0NJWkFKUGN5MEhqVHVBanZmem94NHpFNEF1aVU5UEZzaU5iOUwyaTVObAo0eTZnamxDeFN3SmZpR3IzRnh5UDdvQlhDT3NGOFhCakorOHJ2TlAxM2RtY29yK0tEbURNVGRYRmtWVXlub2pzCng5MGlyL1A1Ukg1bTF0YkVVdUtITE11eEkwS0VIYjZiV29keFhCSk9xNEdSbkNUWS91SXJjLzBDZ1lFQTBaR3QKci9Nb25KbEpmZDRoWlRSUTc2cjdVSlBsSUhLU3hSTG82SXZBeDNrNEJJbWhyQmFFRjl4M1A0NXpQcVBoa2szVwo5cmh1emFJSnBXSWNEVGZ1QnJZYStDbmlScFNIZ0JZRVFnRU5rbHdOR0ZDRmRrRDY1MjE3VjBnUjJrWDRCVlU3CmhsREs3NGs1Y0tBdnFBbVgwNzVnZk5uZHBXSDhBV1YwY1IrSVVsRUNnWUVBbjVlUWt0bjdpUWhFQWxsTkM0czQKbm95SHdlR0xENmtLSGt3TVl3dDhkSGZ1UGZkZ2lLN0JCRW1mSWRTeWNBZitxSVRYZlRmbUxvK2NrUHJmZGE2RgpOV3JZd1Fuc3lCOHB6M1BPdGtKdHVzekVzVW13LzM4VExWdTJIUFd3djlZMnkvU1NkZFA3TkE3ckhlUjlmWlo4CjdadnFsY3VWelFaM0NiOG5WL3Zvb05FQ2dZQlFBMnpySnMyMHJKbndvcVRoZlE0QjA2aE1aWXN2ems3WFM1YjkKWW81aUdwZ1dzMjIweEl2K2lFQkhWZDRPWm9lelVtRG1waGc0RHN2Y0J3OXF4Slh1bmd6Qi8wdlRZdFl4UXphdwo5TEgzMVlseVpSdnZ3SE9MZExPSTZZMVhaeXVBN2IvaVVtcUk5ajJtRUtMaFozZytjZ3RvMzgzT1hSRFlmNkhyCnB2eG5ZUUtCZ1FESURRZlRoZkFoV0tQbzFpbjlYaE9vVFZLQ0hFb2dUL0E0dnZvR2N1QkFRdUY5aWNVMDdtODMKN3FKUXgwelpSUmZMWnVNQnJtNjF2dUhaOG1hdC85SkF5WUpTUnJtU3B4RGNGL2s5NHYxZEVRbkpkd2svejgrbAptS05uNXR3R3ZKTFdyQ0NOR000SEJKZjNWc1pmcWFhV1NJQ1g1VFJlUFNkc0QyUHhXMXcwc2c9PQotLS0tLUVORCBSU0EgUFJJVkFURSBLRVktLS0tLQo=
type: Opaque
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: mirrorgooglecontainers/kubernetes-dashboard-amd64:v1.10.1
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
type: NodePort
ports:
- port: 443
nodePort: 30000
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
部署Heapster
由于缺少 Heapster 插件,当前 dashboard 不能展示 Pod、Nodes 的 CPU、内存等 metric 图形
1.到heapster release 页面下载最新版的heapster:
# wget https://github.com/kubernetes-retired/heapster/archive/v1.5.4.tar.gz
# tar xf v1.5.4.tar.gz
查看部署所用相关配置文件:
# cd heapster-1.5.4/deploy/kube-config/
# ls influxdb/ && ls rbac/
grafana.yaml heapster.yaml influxdb.yaml
heapster-rbac.yaml
新建文件夹,用于存放 Heapster 部署所需的 yaml 文件,将上述文件拷贝至此目录
# mkdir heapster
# ls heapster/
grafana.yaml heapster-rbac.yaml heapster.yaml influxdb.yaml
2.修改 yaml 中 image 的值
# grep 'image:' heapster.yaml
image: mirrorgooglecontainers/heapster-amd64:v1.5.3
# grep 'image:' grafana.yaml
image: mirrorgooglecontainers/heapster-grafana-amd64:v4.4.3
# grep 'image:' influxdb.yaml
image: mirrorgooglecontainers/heapster-influxdb-amd64:v1.3.3
k8s.gcr.io 全部修改为mirrorgooglecontainers或者registry.cn-hangzhou.aliyuncs.com/google_containers
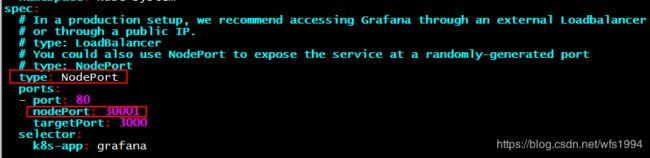
3.修改 grafana.yaml 文件,暴露服务到外部
4.部署 Heapster
# cd heapster/
# kubectl apply -f .
5.查看dashboard

6.访问grafana
地址:http://192.168.20.203:30001

参考链接
https://www.jianshu.com/p/6f42ac331d8a
https://www.jianshu.com/p/c6d560d12d50
https://www.qikqiak.com/post/manual-install-high-available-kubernetes-cluster/