linux 安全审计以及加固工具 lynis 使用介绍
0x00 概述
Lynis是一款Unix系统的安全审计以及加固工具,能够进行深层次的安全扫描,其目的是检测潜在的时间并对未来的系统加固提供建议。这款软件会扫描一般系统信息,脆弱软件包以及潜在的错误配置。
该软件面向系统admin,审计人员,安全官,安全专家。
特征:
- 漏洞扫描
- 系统加固
- 入侵检测
- 中心管理
- 自定义行为规划
- 报告
- 安全面板
- 持续监测
- 技术支持
目标:
- 自动安全审计
- 符合性测试
- 漏洞侦测
有助于:
- 配置管理
- 软件补丁管理
- 系统加固
- 渗透测试
- 恶意软件扫描
- 入侵检测
0x01 安装
详细查看其操作手册: https://cisofy.com/documentation/lynis/get-started/
方式1 git下载使用
git clone https://github.com/CISOfy/lynis方式2 直接下载tar包,解压使用
wget https://github.com/CISOfy/lynis/archive/2.7.5.tar.gz
tar -zxvf 2.7.5.tar.gz0x02 试用
进入lynis的目录,输入./lynis即可
我们一般试用./lynis audit system来进行对系统的全盘扫描,这种扫描方式会产生一系列人机交互,无法自动化扫描。
故我们在其后加上参数-Q即快速扫描,从而自动化扫描。
以下是常用的lynis的参数:
| Parameter | Abbreviated | Description |
|---|---|---|
| --auditor "Given name Surname" | 配发审计人员的名字 | |
| --checkall | -c | 开始检查 |
| --check-update | 更新 | |
| --cronjob | 计划任务 (includes -c -Q) | |
| --help | -h | 帮助 |
| --manpage | 用户手册 | |
| --nocolors | 无配色 | |
| --pentest | 低权限渗透测试扫描 | |
| --quick | -Q | 自动模式 |
| --quiet | 静默且自动模式 | |
| --reverse-colors | 浅色背景配色模式 | |
| --version | -V | 版本号 |
如果要进行深层次的检查的话,可能需要让lynis处于root权限运行,那么我们只要
sudo cp -R /path/to/lynis /usr/local/lynis
即可将lynis置于root权限中,如此一来就可以进行深层次的检查了。
0x03 审计报告&日志
lynis将会进行深层次的审计,并将报告呈现在标准输出、日志文件以及审计报告文件中。
标准输出
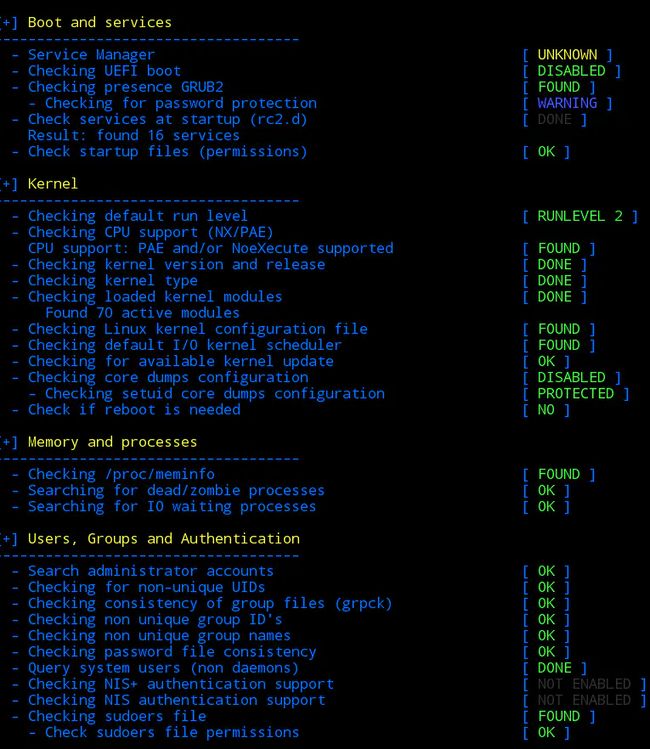
我们执行lynis时将会在屏幕上打印出本次审计的结果,测试的结果包括[OK or WARNING] [Found or Not Found] [Value]。如下图:
日志文件
扫描完毕后我们会生成一个日志文件以及一个扫描报告。日志文件中对比标准输出,会有更多的信息,这些信息适用于更深层次的检查。
日志里会有事件操作的执行时间,测试失败或跳过的原因,内部测试的输出,对于配置选项不恰当该如何修改的建议,威胁指数。
我们对该文件进行输出,查看其中的告警(WARNING)以及建议(SUGGESTION)
# grep Warning /var/log/lynis.log
[11:12:37] Warning: apt-get check returned a non successful exit code. [test:PKGS-7390] [details:M] [solution:-]
[11:13:41] Warning: Couldn't find 2 responsive nameservers [test:NETW-2705] [details:L] [solution:-]
[11:13:43] Warning: PHP option expose_php is possibly turned on, which can reveal useful information for attackers. [test:PHP-2372] [details:M] [solution:-]
# grep Suggestion /var/log/lynis.log
[11:12:26] Suggestion: Set a password on GRUB bootloader to prevent altering boot configuration (e.g. boot in single user mode without password) [test:BOOT-5122] [details:-] [solution:-]
[11:12:27] Suggestion: Install a PAM module for password strength testing like pam_cracklib or pam_passwdqc [test:AUTH-9262] [details:-] [solution:-]
[11:12:27] Suggestion: Configure minimum password age in /etc/login.defs [test:AUTH-9286] [details:-] [solution:-]
[11:12:27] Suggestion: Configure maximum password age in /etc/login.defs [test:AUTH-9286] [details:-] [solution:-]
[11:12:28] Suggestion: Default umask in /etc/login.defs could be more strict like 027 [test:AUTH-9328] [details:-] [solution:-]
[11:12:28] Suggestion: Default umask in /etc/init.d/rc could be more strict like 027 [test:AUTH-9328] [details:-] [solution:-]
[11:12:28] Suggestion: To decrease the impact of a full /home file system, place /home on a separated partition [test:FILE-6310] [details:-] [solution:-]
[11:12:28] Suggestion: To decrease the impact of a full /tmp file system, place /tmp on a separated partition [test:FILE-6310] [details:-] [solution:-]
[11:12:28] Suggestion: To decrease the impact of a full /var file system, place /var on a separated partition [test:FILE-6310] [details:-] [solution:-]
[11:12:28] Suggestion: Disable drivers like USB storage when not used, to prevent unauthorized storage or data theft [test:STRG-1840] [details:-] [solution:-]
[11:12:28] Suggestion: Disable USB devices authorization, to prevent unauthorized storage or data theft [test:STRG-1840] [details:-] [solution:-]
[11:12:36] Suggestion: Purge old/removed packages (5 found) with aptitude purge or dpkg --purge command. This will cleanup old configuration files, cron jobs and startup scripts. [test:PKGS-7346] [details:-] [solution:-]
[11:12:36] Suggestion: Install debsums utility for the verification of packages with known good database. [test:PKGS-7370] [details:-] [solution:-]
[11:12:37] Suggestion: Run apt-get to perform a manual package database consistency check. [test:PKGS-7390] [details:-] [solution:-]
[11:13:40] Suggestion: Check if system is up-to-date, security updates test (apt-check) gives an unexpected result [test:PKGS-7392] [details:-] [solution:-]
[11:13:40] Suggestion: Install package apt-show-versions for patch management purposes [test:PKGS-7394] [details:-] [solution:-]
[11:13:41] Suggestion: Check your resolv.conf file and fill in a backup nameserver if possible [test:NETW-2705] [details:-] [solution:-]
[11:13:41] Suggestion: Install ARP monitoring software like arpwatch [test:NETW-3032] [details:-] [solution:-]
[11:13:41] Suggestion: Access to CUPS configuration could be more strict. [test:PRNT-2307] [details:-] [solution:-]
[11:13:41] Suggestion: Configure a firewall/packet filter to filter incoming and outgoing traffic [test:FIRE-4590] [details:-] [solution:-]
[11:13:42] Suggestion: Install Apache mod_evasive to guard webserver against DoS/brute force attempts [test:HTTP-6640] [details:-] [solution:-]
[11:13:42] Suggestion: Install Apache mod_qos to guard webserver against Slowloris attacks [test:HTTP-6641] [details:-] [solution:-]
[11:13:42] Suggestion: Install Apache mod_spamhaus to guard webserver against spammers [test:HTTP-6642] [details:-] [solution:-]
[11:13:42] Suggestion: Install Apache modsecurity to guard webserver against web application attacks [test:HTTP-6643] [details:-] [solution:-]
[11:13:43] Suggestion: Change the expose_php line to: expose_php = Off [test:PHP-2372] [details:-] [solution:-]
[11:13:43] Suggestion: Change the allow_url_fopen line to: allow_url_fopen = Off, to disable downloads via PHP [test:PHP-2376] [details:-] [solution:-]
[11:13:44] Suggestion: Check what deleted files are still in use and why. [test:LOGG-2190] [details:-] [solution:-]
[11:13:44] Suggestion: Although inetd is not running, make sure no services are enabled in /etc/inetd.conf [test:INSE-8006] [details:-] [solution:-]
[11:13:44] Suggestion: Add a legal banner to /etc/issue, to warn unauthorized users [test:BANN-7126] [details:-] [solution:-]
[11:13:44] Suggestion: Add legal banner to /etc/issue.net, to warn unauthorized users [test:BANN-7130] [details:-] [solution:-]
[11:13:44] Suggestion: Enable process accounting [test:ACCT-9622] [details:-] [solution:-]
[11:13:44] Suggestion: Enable sysstat to collect accounting (no results) [test:ACCT-9626] [details:-] [solution:-]
[11:13:44] Suggestion: Enable auditd to collect audit information [test:ACCT-9628] [details:-] [solution:-]
[11:13:45] Suggestion: Determine if automation tools are present for system management [test:TOOL-5002] [details:-] [solution:-]
[11:13:45] Suggestion: One or more sysctl values differ from the scan profile and could be tweaked [test:KRNL-6000] [details:-] [solution:-]
[11:13:45] Suggestion: Harden compilers like restricting access to root user only [test:HRDN-7222] [details:-] [solution:-]
审计报告
执行审计程序之后,lynis会对其发现进行收集并获得其他数据点,数据会被存储在报告文件中。不过这个文件读起来比较吃力,采用的是 数据名=值 的方式,要是一个数据有多个值,则在其后加个[]。如下图:
若是使用lynis企业版,可以产生更多的报告格式。
0x04 配置文件
我们可以针对不同的操作系统、系统定位以及安全等级定制不同的配置文件。如果不通过--profile来指定配置文件的话,就会使用默认的配置文件default.prf。我们可以通过修改这个默认配置文件来满足我们的需求。
0x05 插件
正常lynis控制器进行独立测试并共享输出时,插件会获取信息。随后信息会被收集和处理,随后安全智能能够适用于数据收集并与中心节点相关联。
lynis能够使用插件模块化支持拓展其功能。
阶段1:
阶段1是插件初始化,该插件能hook进已有的测试,收集信息。
阶段2:
测试结束后,插件能够获取最后一次机会去完成其工作。插件也能独立使用,仅仅在阶段1执行。
启用插件
在profile里启用插件,plugin=
0x06 Lynis企业版
需要购买Key。用了企业版之后可以拥有其他功能了,如插件功能,中心系统功能,定制报告功能以及安全面板功能。其用户界面是基于web的。
0x07 优劣
优势
- 开源
- 多平台
- 能够产生告警和建议
- 整合大量审计模块,对操作系统进行多样化审计
- 支持模块,可以进行自定义扫描
- 企业版有web界面
劣势
- 每个审计项都不深入,需要具体的扩展
- 许多功能需要使用企业版,收费暂时无法体验