部署kube-apiserver
部署kube-apiserver
1. 创建kube-apiserver证书
1)创建kube-apiserver证书签名请求
# api-server启用双向TLS认证
[root@kubenode1 ~]# mkdir -p /etc/kubernetes/apiserver
[root@kubenode1 ~]# cd /etc/kubernetes/apiserver/
[root@kubenode1 apiserver]# touch apiserver-csr.json
# hosts字段不为空时,指定授权使用该证书的ip与域名列表;
# 加入集群个节点ip,1次生成证书分发即可;
# 前端ha节点也需要与apiserver通信;
# 同时指定集群内部多个域名与kube-apiserver注册的名为kubernetes的服务ip(Service Cluster IP),一般是--service-cluster-ip-range 选项值指定的网段的第一个IP
[root@kubenode1 apiserver]# vim apiserver-csr.json
{
"CN": "kubernetes",
"hosts": [
"127.0.0.1",
"172.30.200.10",
"172.30.200.11",
"172.30.200.12",
"172.30.200.21",
"172.30.200.22",
"172.30.200.23",
"169.169.0.1",
"kubernetes",
"kubernetes.default",
"kubernetes.default.svc",
"kubernetes.default.svc.cluster",
"kubernetes.default.svc.cluster.local"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"ST": "ChengDu",
"L": "ChengDu",
"O": "k8s",
"OU": "cloudteam"
}
]
}
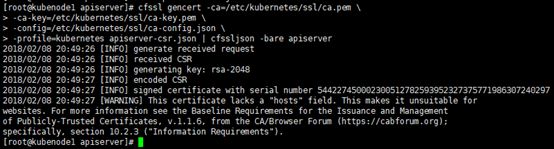
2)生成kube-apiserver证书与私钥
[root@kubenode1 apiserver]# cfssl gencert -ca=/etc/kubernetes/ssl/ca.pem \ -ca-key=/etc/kubernetes/ssl/ca-key.pem \ -config=/etc/kubernetes/ssl/ca-config.json \ -profile=kubernetes apiserver-csr.json | cfssljson -bare apiserver
# 分发apiserver.pem,apiserver-key.pem [root@kubenode1 apiserver]# scp apiserver.pem apiserver-key.pem [email protected]:/etc/kubernetes/apiserver/ [root@kubenode1 apiserver]# scp apiserver.pem apiserver-key.pem [email protected]:/etc/kubernetes/apiserver/
2. 配置kube-apiserver的systemd unit文件
相关可执行文件在部署kubectl时已部署完成。
1)创建kube-apiserver使用的客户端token文件
kubelet 启动时向 kube-apiserver发送注册信息,在双向的TLS加密通信环境中需要认证,手工为kubelet生成证书/私钥在node节点较少且数量固定时可行,采用TLS Bootstrapping 机制,可使大量的node节点自动完成向kube-apiserver的注册请求。
原理:kubelet 首次启动时向 kube-apiserver 发送 TLS Bootstrapping 请求,kube-apiserver 验证 kubelet 请求中的 token 是否与它配置的 token.csv 一致,如果一致则自动为 kubelet生成证书和秘钥。
[root@kubenode1 ~]# mkdir -p /etc/kubernetes/bootstrap
[root@kubenode1 ~]# cd /etc/kubernetes/bootstrap/
[root@kubenode1 bootstrap]# cat > token.csv << EOF
${BOOTSTRAP_TOKEN},kubelet-bootstrap,10001,"system:kubelet-bootstrap"
EOF
# 分发
[root@kubenode1 ~]# scp /etc/kubernetes/bootstrap/token.csv [email protected]:/etc/kubernetes/bootstrap/
[root@kubenode1 ~]# scp /etc/kubernetes/bootstrap/token.csv [email protected]:/etc/kubernetes/bootstrap/
2)配置kube-apiserver的systemd unit文件
[root@kubenode1 ~]# touch /usr/lib/systemd/system/kube-apiserver.service [root@kubenode1 ~]# vim /usr/lib/systemd/system/kube-apiserver.service [Unit] Description=Kubernetes API Server Documentation=https://github.com/GoogleCloudPlatform/kubernetes After=network.target [Service] User=root EnvironmentFile=/usr/local/kubernetes/kube-apiserver.conf ExecStart=/usr/local/kubernetes/bin/kube-apiserver $KUBE_API_ARGS Restart=on-failure RestartSec=5 Type=notify LimitNOFILE=65536 [Install] WantedBy=multi-user.target # 启动参数文件; # --admission-control:kuberneres集群的准入控制机制,各控制模块以插件的形式依次生效,集群时必须包含ServiceAccount; # --bind-address:不能为 127.0.0.1;在本地址的6443端口开启https服务,默认值0.0.0.0; # --insecure-port=0:禁用不安全的http服务,默认开启,端口8080,设置为0禁用; --secure-port=6443:https安全端口,默认即6443,0表示禁用; # --authorization-mode:在安全端口使用 RBAC 授权模式,未通过授权的请求拒绝; # --service-cluster-ip-range:指定 Service Cluster IP 地址段,该地址段外部路由不可达; # --service-node-port-range:指定 NodePort 的端口范围; # --storage-backend:持久化存储类型,v1.6版本后默认即etcd3; # --enable-swagger-ui:设置为true时,启用swagger-ui网页,可通过apiserver的usl/swagger-ui访问,默认为false; # --allow-privileged:设置为true时,kubernetes允许在Pod中运行拥有系统特权的容器应用; # --audit-log-*:审计日志相关; # --event-ttl:apiserver中各时间保留时间,默认即1h,通常用于审计与追踪; # --logtostderr:默认为true,输出到stderr,不输出到日志; # --log-dir:日志目录; # --v:日志级别 [root@kubenode1 ~]# touch /usr/local/kubernetes/kube-apiserver.conf [root@kubenode1 ~]# vim /usr/local/kubernetes/kube-apiserver.conf KUBE_API_ARGS="--admission-control=NamespaceLifecycle,LimitRanger,ServiceAccount,DefaultStorageClass,ResourceQuota,NodeRestriction \ --advertise-address=172.30.200.21 \ --bind-address=172.30.200.21 \ --insecure-port=0 \ --authorization-mode=Node,RBAC \ --runtime-config=rbac.authorization.k8s.io/v1beta1 \ --kubelet-https=true \ --token-auth-file=/etc/kubernetes/bootstrap/token.csv \ --service-cluster-ip-range=169.169.0.0/16 \ --service-node-port-range=10000-60000 \ --tls-cert-file=/etc/kubernetes/apiserver/apiserver.pem \ --tls-private-key-file=/etc/kubernetes/apiserver/apiserver-key.pem \ --client-ca-file=/etc/kubernetes/ssl/ca.pem \ --service-account-key-file=/etc/kubernetes/ssl/ca-key.pem \ --etcd-cafile=/etc/kubernetes/ssl/ca.pem \ --etcd-certfile=/etc/kubernetes/apiserver/apiserver.pem \ --etcd-keyfile=/etc/kubernetes/apiserver/apiserver-key.pem \ --storage-backend=etcd3 \ --etcd-servers=https://172.30.200.21:2379,https://172.30.200.22:2379,https://172.30.200.23:2379 \ --enable-swagger-ui=true \ --allow-privileged=true \ --apiserver-count=3 \ --audit-log-maxage=30 \ --audit-log-maxbackup=3 \ --audit-log-maxsize=100 \ --audit-log-path=/var/lib/audit.log \ --event-ttl=1h \ --logtostderr=false \ --log-dir=/var/log/kubernetes/apiserver \ --v=2 1>>/var/log/kubernetes/apiserver/kube-apiserver.log 2>&1" # 创建日志目录 [root@kubenode1 ~]# mkdir -p /var/log/kubernetes/apiserver
3. 启动并验证
[root@kubenode1 ~]# systemctl daemon-reload [root@kubenode1 ~]# systemctl enable kube-apiserver [root@kubenode1 ~]# systemctl start kube-apiserver [root@kubenode1 ~]# systemctl status kube-apiserver