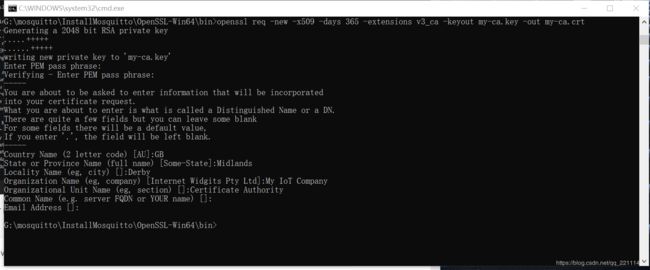
OPENSSL签发证书CA流程
$# First off,generate our own certificate authority certificate and key
$openssl req -new -x509 -days 365 -extensions v3_ca -keyout my-ca.key -out my-ca.crt
$# Now generate a private key for use by out MQTT server
$ openssl genrsa -out server.key 2048
$ # Generate a signing request to send to the certificate authority
$ openssl req -out server.csr -key server.key -new
$ # Send the CSR to the CA,they will sign it,or sign it with your own ca:
$ openssl x509 -req -in server.csr -CA my-ca.crt -CAkey my-ca.key -CAcreateserial -out server.crt -days 180
$ # Certificates are generated,now edit your config file:
$ vi mosquitto.conf
port 8883
cafile my-ca.crt
certfile server.crt
keyfile server.key
# If you want clients to privide a certificate before connecting:
#require_certificate true
$#Run mosquitto using that config on your server,then to publish:
$ mosquitto_pub --cafile my-ca.crt -h mqtt.example.net -t hello -m world
5. 生成p12格式证书
$openssl pkcs12 -export -inkey client.key -in client.crt -out client.pfx
$openssl pkcs12 -export -inkey server.key -in server.crt -out server.pfx
6.生成pem格式证书
有时需要用到pem格式的证书,可以用以下方式合并证书文件(crt)和私钥文件(key)来生成
$cat client.crt client.key> client.pem
$cat server.crt server.key > server.pem
7.PFX文件转换为X509证书文件和RSA密钥文件
$openssl pkcs12 -in server.pfx -nodes -out server.pem
$openssl rsa -in server.pem -out server2.key
$openssl x509 -in server.pem -out server2.crt
生成
服务端证书:ca.crt, server.key, server.crt, server.pem, server.pfx
客户端证书:ca.crt, client.key, client.crt, client.pem, client.pfx