Acegi是Spring Framework 下
最成熟的安全系统,它提供了强大灵活的
企业级安全服务,如: 1 :
完善的认证和授权机制, 2 :
Http资源访问控制, 3 :
Method 调用访问控制, 4 :
Access Control List (ACL) 基于对象实例的访问控制, 5 :
Yale Central Authentication Service (CAS) 耶鲁单点登陆, 6 :
X509 认证, 7 :
当前所有流行容器的认证适配器, 8 :
Channel Security频道安全管理等功能。 具体 :
- Http资源访问控制 http://apps:8080/index.htm -> for public http://apps:8080/user.htm -> for authorized user
- 方法调用访问控制 public void getData() -> all user public void modifyData() -> supervisor only
- 对象实例保护 order.getValue() < $100 -> all user order.getValue() > $100 -> supervisor only
Acegi是非入侵式安全架构 因为 :
- 基于Servlet Filter和Spring aop, 使商业逻辑和安全逻辑分开,结构更清晰
- 使用Spring 来代理对象,能方便地保护方法调用
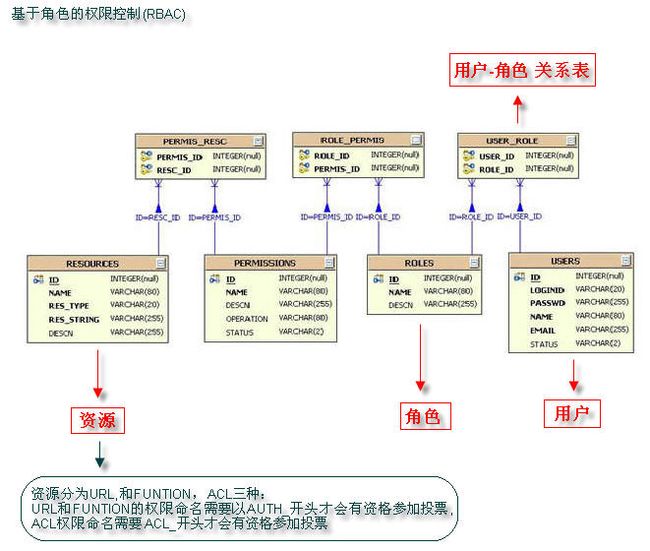
基于角色的权限控制(RBAC) : Acegi 自带的 sample 表设计很简单: users表{username,password,enabled} authorities表{username,authority},这样简单的设计无法适应复杂的权限需求,故SpringSide选用RBAC模型对权限控制数据库表进行扩展。 RBAC(Role-Based Access Control)引入了ROLE的概念,使User(用户)和Permission(权限)分离,一个用户拥有多个角色,一个角色拥有有多个相应的权限,从而减少了权限管理的复杂度,可更灵活地支持安全策略。
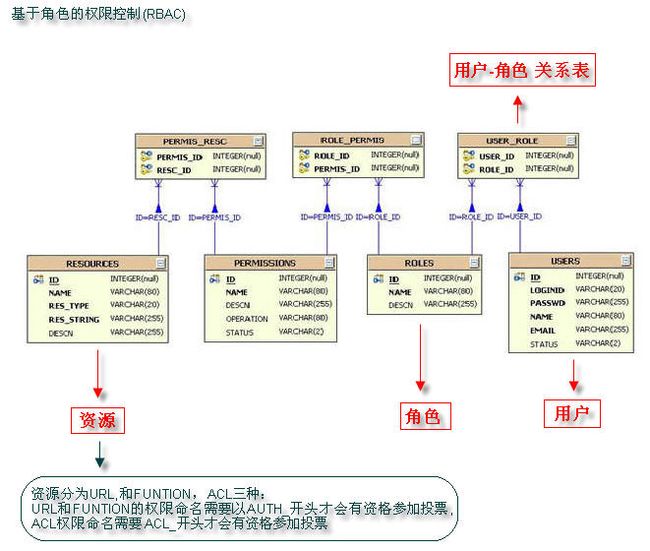 同时,我们也引入了resource(资源)的概念,一个资源对应多个权限,资源分为ACL,URL,和FUNTION三种。注意,URL和FUNTION的权限命名需要以AUTH_开头才会有资格参加投票, 同样的ACL权限命名需要ACL_开头。 2.1 在Web.xml中的配置 :
同时,我们也引入了resource(资源)的概念,一个资源对应多个权限,资源分为ACL,URL,和FUNTION三种。注意,URL和FUNTION的权限命名需要以AUTH_开头才会有资格参加投票, 同样的ACL权限命名需要ACL_开头。 2.1 在Web.xml中的配置 :
1) FilterToBeanProxy Acegi通过实现了Filter接口的FilterToBeanProxy提供一种特殊的使用Servlet Filter的方式,它委托Spring中的Bean -- FilterChainProxy来完成过滤功能,这好处是简化了web.xml的配置,并且充分利用了Spring IOC的优势。FilterChainProxy包含了处理认证过程的filter列表,每个filter都有各自的功能。
1
 <
filter
>
2
<
filter
>
2
 <
filter
-
name
>
securityFilter
filter
-
name
>
3
<
filter
-
name
>
securityFilter
filter
-
name
>
3
 <
filter
-
class
>
org.acegisecurity.util.FilterToBeanProxy
filter
-
class
>
4
<
filter
-
class
>
org.acegisecurity.util.FilterToBeanProxy
filter
-
class
>
4
 <
init
-
param
>
5
<
init
-
param
>
5
 <
param
-
name
>
targetClass
param
-
name
>
6
<
param
-
name
>
targetClass
param
-
name
>
6
 <
param
-
value
>
org.acegisecurity.util.FilterChainProxy
param
-
value
>
7
<
param
-
value
>
org.acegisecurity.util.FilterChainProxy
param
-
value
>
7
 init
-
param
>
8
init
-
param
>
8
 filter
>
filter
>
2) filter-mapping 限定了FilterToBeanProxy的URL匹配模式,
1
 <
filter
-
mapping
>
2
<
filter
-
mapping
>
2
 <
filter
-
name
>
securityFilter
filter
-
name
>
3
<
filter
-
name
>
securityFilter
filter
-
name
>
3
 <
url
-
pattern
>/
j_security_check
url
-
pattern
>
4
<
url
-
pattern
>/
j_security_check
url
-
pattern
>
4
 filter
-
mapping
>
5
filter
-
mapping
>
5
 6
6
 <
filter
-
mapping
>
7
<
filter
-
mapping
>
7
 <
filter
-
name
>
securityFilter
filter
-
name
>
8
<
filter
-
name
>
securityFilter
filter
-
name
>
8

 <
url
-
pattern
>/
dwr
/**/
/* 9
<
url
-
pattern
>/
dwr
/**/
/* 9 10
10 11
11 12
12 securityFilter 13
securityFilter 13 *.html 14
*.html 14 15
15 16
16 17
17 securityFilter 18
securityFilter 18 *.jsp 19
*.jsp 19
3) HttpSessionEventPublisher 的HttpSessionEventPublisher用于发布HttpSessionApplicationEvents和HttpSessionDestroyedEvent事件给spring的applicationcontext。
1
 <
listener
>
2
<
listener
>
2
 <
listener
-
class
>
org.acegisecurity.ui.session.HttpSessionEventPublisher
listener
-
class
>
3
<
listener
-
class
>
org.acegisecurity.ui.session.HttpSessionEventPublisher
listener
-
class
>
3
 listener
>
4
listener
>
4

注:appfuse1.9.3中没有发现这个 监听器 -------------------------------------- 2.2 : 在applicationContext-acegi-security.xml中 2.2.1 FILTER CHAIN FilterChainProxy会按顺序来调用这些filter,使这些filter能享用Spring ioc的功能, CONVERT_URL_TO_LOWERCASE_BEFORE_COMPARISON定义了url比较前先转为小写, PATTERN_TYPE_APACHE_ANT定义了使用Apache ant的匹配模式
1
 <
bean id
=
"
filterChainProxy
"
class
=
"
org.acegisecurity.util.FilterChainProxy
"
>
2
<
bean id
=
"
filterChainProxy
"
class
=
"
org.acegisecurity.util.FilterChainProxy
"
>
2
 <
property name
=
"
filterInvocationDefinitionSource
"
>
3
<
property name
=
"
filterInvocationDefinitionSource
"
>
3
 <
value
>
4
<
value
>
4
 CONVERT_URL_TO_LOWERCASE_BEFORE_COMPARISON
5
CONVERT_URL_TO_LOWERCASE_BEFORE_COMPARISON
5
 PATTERN_TYPE_APACHE_ANT
6
PATTERN_TYPE_APACHE_ANT
6

 /** */
/**=httpSessionContextIntegrationFilter,authenticationProcessingFilter, 7
/** */
/**=httpSessionContextIntegrationFilter,authenticationProcessingFilter, 7 basicProcessingFilter,rememberMeProcessingFilter,anonymousProcessingFilter, 8
basicProcessingFilter,rememberMeProcessingFilter,anonymousProcessingFilter, 8 exceptionTranslationFilter,filterInvocationInterceptor,securityEnforcementFilter 9
exceptionTranslationFilter,filterInvocationInterceptor,securityEnforcementFilter 9 10
10 11
11
这里补充一段别人的教程 : 其中对web路径请求的认证中,我们需要了解一下
securityEnforcementFilter
1
 <
bean id
=
"
securityEnforcementFilter
"
class
=
"
net.sf.acegisecurity.intercept.web.SecurityEnforcementFilter
"
>
2
<
bean id
=
"
securityEnforcementFilter
"
class
=
"
net.sf.acegisecurity.intercept.web.SecurityEnforcementFilter
"
>
2
 <
property name
=
"
filterSecurityInterceptor
"
>
3
<
property name
=
"
filterSecurityInterceptor
"
>
3
 <
ref local
=
"
filterInvocationInterceptor
"
/>
4
<
ref local
=
"
filterInvocationInterceptor
"
/>
4
 property
>
5
property
>
5
 6
6
 <
property name
=
"
authenticationEntryPoint
"
>
7
<
property name
=
"
authenticationEntryPoint
"
>
7
 <
ref local
=
"
authenticationProcessingFilterEntryPoint
"
/>
8
<
ref local
=
"
authenticationProcessingFilterEntryPoint
"
/>
8
 property
>
9
property
>
9
 bean
>
bean
>
这里,主要是
filterInvocationInterceptor,
1
 <
bean id
=
"
filterInvocationInterceptor
"
class
=
"
net.sf.acegisecurity.intercept.web.FilterSecurityInterceptor
"
>
2
<
bean id
=
"
filterInvocationInterceptor
"
class
=
"
net.sf.acegisecurity.intercept.web.FilterSecurityInterceptor
"
>
2
 <
property name
=
"
authenticationManager
"
><
ref bean
=
"
authenticationManager
"
/>
property
>
3
<
property name
=
"
authenticationManager
"
><
ref bean
=
"
authenticationManager
"
/>
property
>
3
 <
property name
=
"
accessDecisionManager
"
><
ref local
=
"
httpRequestAccessDecisionManager
"
/>
property
>
4
<
property name
=
"
accessDecisionManager
"
><
ref local
=
"
httpRequestAccessDecisionManager
"
/>
property
>
4
 <
property name
=
"
objectDefinitionSource
"
>
5
<
property name
=
"
objectDefinitionSource
"
>
5
 <
value
>
6
<
value
>
6
 CONVERT_URL_TO_LOWERCASE_BEFORE_COMPARISON
7
CONVERT_URL_TO_LOWERCASE_BEFORE_COMPARISON
7
 PATTERN_TYPE_APACHE_ANT
8
PATTERN_TYPE_APACHE_ANT
8
 /
wo.html
=
ROLE_ANONYMOUS,ROLE_USER
9
/
wo.html
=
ROLE_ANONYMOUS,ROLE_USER
9
 /
index.jsp
=
ROLE_ANONYMOUS,ROLE_USER
10
/
index.jsp
=
ROLE_ANONYMOUS,ROLE_USER
10
 /
hello.htm
=
ROLE_ANONYMOUS,ROLE_USER
11
/
hello.htm
=
ROLE_ANONYMOUS,ROLE_USER
11
 /
logoff.jsp
=
ROLE_ANONYMOUS,ROLE_USER
12
/
logoff.jsp
=
ROLE_ANONYMOUS,ROLE_USER
12
 /
switchuser.jsp
=
ROLE_SUPERVISOR
13
/
switchuser.jsp
=
ROLE_SUPERVISOR
13
 /
j_acegi_switch_user
=
ROLE_SUPERVISOR
14
/
j_acegi_switch_user
=
ROLE_SUPERVISOR
14
 /
acegilogin.jsp
*=
ROLE_ANONYMOUS,ROLE_USER
15
/
acegilogin.jsp
*=
ROLE_ANONYMOUS,ROLE_USER
15

 /** */
/**=ROLE_USER 16
/** */
/**=ROLE_USER 16 17
17 18
18
在此,主要对
objectDefinitionSource值进行处理。这里配置了很多path=role , 其作用就是在请求指定的路径时,
是需要当前用户具有对应的角色的,如果具有相应角色,则正常访问。否则跳转至 这里需要说明的就是/index.jsp=
ROLE_
ANONYMOUS,
ROLE_USER 这里的角色,
ROLE_是标记,ANONYMOUS 是角色名称。
ANONYMOUS是只可以匿名访问,
这个角色无需定义。 而ROLE_USER 中的USER则是用户定义的,接下来我们介绍这部分: 用户角色管理: acegi security提供了用户角色的获取接口,以及一个缺省的实现(包括对应的数据库表定义)
1
 <
bean id
=
"
jdbcDaoImpl
"
class
=
"
net.sf.acegisecurity.providers.dao.jdbc.JdbcDaoImpl
"
>
2
<
bean id
=
"
jdbcDaoImpl
"
class
=
"
net.sf.acegisecurity.providers.dao.jdbc.JdbcDaoImpl
"
>
2
 <
property name
=
"
dataSource
"
><
ref bean
=
"
dataSource
"
/>
property
>
3
<
property name
=
"
dataSource
"
><
ref bean
=
"
dataSource
"
/>
property
>
3
 bean
>
bean
>
可参看这里的net.sf.acegisecurity.providers.dao.jdbc.JdbcDaoImpl,需要注意的是这个dao的实现是同acegi security提供的表定义一致的。
如果这个角色和用户处理模型不能满足自己的需要,自己可以提供自己的实现。只需要将
1 <bean id="jdbcDaoImpl" class="net.sf.acegisecurity.providers.dao.jdbc.JdbcDaoImpl">
<bean id="jdbcDaoImpl" class="net.sf.acegisecurity.providers.dao.jdbc.JdbcDaoImpl">
修改成自己类实现即可。
从严格意义上来说,以下权限部分的介绍应该不在acegi security处理的范围之内,不过acegi security是提供了相应的机制的: 权限管理 权限在acegi security 主要以acl的概念出现:即 access control list
1
 <
bean id
=
"
basicAclExtendedDao
"
class
=
"
net.sf.acegisecurity.acl.basic.jdbc.JdbcExtendedDaoImpl
"
>
2
<
bean id
=
"
basicAclExtendedDao
"
class
=
"
net.sf.acegisecurity.acl.basic.jdbc.JdbcExtendedDaoImpl
"
>
2
 <
property name
=
"
dataSource
"
><
ref bean
=
"
dataSource
"
/>
property
>
3
<
property name
=
"
dataSource
"
><
ref bean
=
"
dataSource
"
/>
property
>
3
 bean
>
4
bean
>
4

这个类实现中有acl的产生,获取和删除操作 应用数据权限的处理: 如果我们应用数据的权限要借助于acegi security 来实现的话,那主要工作就是调用 basicAclExtendedDao 中的相关方法。阅读basicAclExtendedDao即可明白。
以上简要的介绍了一下自己学习acegi security的一些了解。自己最后得出的结论是,如果自己的应用规模很小,完全可以不用acegi security。如果要用acegi security,很多时候是需要重新实现自己的权限和用户模型的。
引入别人教程完毕
2.2.2 基础认证
1) authenticationManager 起到认证管理的作用,它将验证的功能委托给多个Provider,并通过遍历Providers, 以保证获取不同来源的身份认证,若某个Provider能成功确认当前用户的身份,authenticate()方法会返回一个完整的包含用户授权信息的Authentication对象,否则会抛出一个AuthenticationException。 Acegi提供了不同的AuthenticationProvider的实现,如:
1
 DaoAuthenticationProvider 从数据库中读取用户信息验证身份
2
DaoAuthenticationProvider 从数据库中读取用户信息验证身份
2
 AnonymousAuthenticationProvider 匿名用户身份认证
3
AnonymousAuthenticationProvider 匿名用户身份认证
3
 RememberMeAuthenticationProvider 已存cookie中的用户信息身份认证
4
RememberMeAuthenticationProvider 已存cookie中的用户信息身份认证
4
 AuthByAdapterProvider 使用容器的适配器验证身份
5
AuthByAdapterProvider 使用容器的适配器验证身份
5
 CasAuthenticationProvider 根据Yale中心认证服务验证身份, 用于实现单点登陆
6
CasAuthenticationProvider 根据Yale中心认证服务验证身份, 用于实现单点登陆
6
 JaasAuthenticationProvider 从JASS登陆配置中获取用户信息验证身份
7
JaasAuthenticationProvider 从JASS登陆配置中获取用户信息验证身份
7
 RemoteAuthenticationProvider 根据远程服务验证用户身份
8
RemoteAuthenticationProvider 根据远程服务验证用户身份
8
 RunAsImplAuthenticationProvider 对身份已被管理器替换的用户进行验证
9
RunAsImplAuthenticationProvider 对身份已被管理器替换的用户进行验证
9
 X509AuthenticationProvider 从X509认证中获取用户信息验证身份
10
X509AuthenticationProvider 从X509认证中获取用户信息验证身份
10
 TestingAuthenticationProvider 单元测试时使用
TestingAuthenticationProvider 单元测试时使用
1
 <
bean id
=
"
authenticationManager
"
class
=
"
org.acegisecurity.providers.ProviderManager
"
>
2
<
bean id
=
"
authenticationManager
"
class
=
"
org.acegisecurity.providers.ProviderManager
"
>
2
 <
property name
=
"
providers
"
>
3
<
property name
=
"
providers
"
>
3
 <
list
>
4
<
list
>
4
 <
ref local
=
"
daoAuthenticationProvider
"
/>
5
<
ref local
=
"
daoAuthenticationProvider
"
/>
5
 <
ref local
=
"
anonymousAuthenticationProvider
"
/>
6
<
ref local
=
"
anonymousAuthenticationProvider
"
/>
6
 <
ref local
=
"
rememberMeAuthenticationProvider
"
/>
7
<
ref local
=
"
rememberMeAuthenticationProvider
"
/>
7
 list
>
8
list
>
8
 property
>
9
property
>
9
 bean
>
bean
>
每个认证者会对自己指定的证明信息进行认证,如DaoAuthenticationProvider仅对UsernamePasswordAuthenticationToken这个证明信息进行认证。 2) daoAuthenticationProvider 进行简单的基于数据库的身份验证。DaoAuthenticationProvider获取数据库中的账号密码并进行匹配,若成功则在通过用户身份的同时返回一个包含授权信息的Authentication对象,否则身份验证失败,抛出一个AuthenticatiionException。
1
 <
bean id
=
"
daoAuthenticationProvider
"
class
=
"
org.acegisecurity.providers.dao.DaoAuthenticationProvider
"
>
2
<
bean id
=
"
daoAuthenticationProvider
"
class
=
"
org.acegisecurity.providers.dao.DaoAuthenticationProvider
"
>
2
 <
property name
=
"
userDetailsService
"
ref
=
"
jdbcDaoImpl
"
/>
3
<
property name
=
"
userDetailsService
"
ref
=
"
jdbcDaoImpl
"
/>
3
 <
property name
=
"
userCache
"
ref
=
"
userCache
"
/>
4
<
property name
=
"
userCache
"
ref
=
"
userCache
"
/>
4
 <
property name
=
"
passwordEncoder
"
ref
=
"
passwordEncoder
"
/>
5
<
property name
=
"
passwordEncoder
"
ref
=
"
passwordEncoder
"
/>
5
 bean
>
bean
>
3)
passwordEncoder 使用加密器对用户输入的明文进行加密。Acegi提供了三种加密器:
1
 a : PlaintextPasswordEncoder—默认,不加密,返回明文.
2
a : PlaintextPasswordEncoder—默认,不加密,返回明文.
2
 b : ShaPasswordEncoder—哈希算法(SHA)加密
3
b : ShaPasswordEncoder—哈希算法(SHA)加密
3
 c : Md5PasswordEncoder—消息摘要(MD5)加密
c : Md5PasswordEncoder—消息摘要(MD5)加密
1
 <
bean id
=
"
passwordEncoder
"
class
=
"
org.acegisecurity.providers.encoding.Md5PasswordEncoder
"
/>
<
bean id
=
"
passwordEncoder
"
class
=
"
org.acegisecurity.providers.encoding.Md5PasswordEncoder
"
/>
4)
jdbcDaoImpl 用于在数据中获取用户信息。 acegi提供了用户及授权的表结构,但是您也可以自己来实现。通过
usersByUsernameQuery这个SQL 得到你的
(用户ID,密码,状态信息);通过
authoritiesByUsernameQuery这个SQL得到你的(
用户ID,授权信息)
1
 <
bean id
=
"
jdbcDaoImpl
"
class
=
"
org.acegisecurity.userdetails.jdbc.JdbcDaoImpl
"
>
2
<
bean id
=
"
jdbcDaoImpl
"
class
=
"
org.acegisecurity.userdetails.jdbc.JdbcDaoImpl
"
>
2
 <
property name
=
"
dataSource
"
ref
=
"
dataSource
"
/>
3
<
property name
=
"
dataSource
"
ref
=
"
dataSource
"
/>
3
 <
property name
=
"
usersByUsernameQuery
"
>
4
<
property name
=
"
usersByUsernameQuery
"
>
4
 <
value
>
select loginid,passwd,
1
from users where loginid
=
?
value
>
5
<
value
>
select loginid,passwd,
1
from users where loginid
=
?
value
>
5
 property
>
6
property
>
6
 <
property name
=
"
authoritiesByUsernameQuery
"
>
7
<
property name
=
"
authoritiesByUsernameQuery
"
>
7
 <
value
>
8
<
value
>
8
 select u.loginid,p.name from users u,roles r,permissions p,
9
select u.loginid,p.name from users u,roles r,permissions p,
9
 user_role ur,role_permis rp where u.id
=
ur.user_id and
10
user_role ur,role_permis rp where u.id
=
ur.user_id and
10
 r.id
=
ur.role_id and p.id
=
rp.permis_id and r.id
=
rp.role_id and
11
r.id
=
ur.role_id and p.id
=
rp.permis_id and r.id
=
rp.role_id and
11
 p.status
=
'
1
'
and u.loginid
=?
12
p.status
=
'
1
'
and u.loginid
=?
12
 value
>
13
value
>
13
 property
>
14
property
>
14
 bean
>
bean
>
5) userCache & resourceCache 缓存用户和资源相对应的权限信息。每当请求一个受保护资源时,daoAuthenticationProvider就会被调用以获取用户授权信息。如果每次都从数据库获取的话,那代价很高,对于不常改变的用户和资源信息来说,最好是把相关授权信息缓存起来。(详见 2.6.3 资源权限定义扩展 ) userCache提供了两种实现: NullUserCache和EhCacheBasedUserCache, NullUserCache实际上就是不进行任何缓存,EhCacheBasedUserCache是使用Ehcache来实现缓功能。
1
 <
bean id
=
"
userCacheBackend
"
class
=
"
org.springframework.cache.ehcache.EhCacheFactoryBean
"
>
2
<
bean id
=
"
userCacheBackend
"
class
=
"
org.springframework.cache.ehcache.EhCacheFactoryBean
"
>
2
 <
property name
=
"
cacheManager
"
ref
=
"
cacheManager
"
/>
3
<
property name
=
"
cacheManager
"
ref
=
"
cacheManager
"
/>
3
 <
property name
=
"
cacheName
"
value
=
"
userCache
"
/>
4
<
property name
=
"
cacheName
"
value
=
"
userCache
"
/>
4
 bean
>
5
bean
>
5
 6
6
 <
bean id
=
"
userCache
"
class
=
"
org.acegisecurity.providers.dao.cache.EhCacheBasedUserCache
"
autowire
=
"
byName
"
>
7
<
bean id
=
"
userCache
"
class
=
"
org.acegisecurity.providers.dao.cache.EhCacheBasedUserCache
"
autowire
=
"
byName
"
>
7
 <
property name
=
"
cache
"
ref
=
"
userCacheBackend
"
/>
8
<
property name
=
"
cache
"
ref
=
"
userCacheBackend
"
/>
8
 bean
>
9
bean
>
9
 10
10
 <
bean id
=
"
resourceCacheBackend
"
class
=
"
org.springframework.cache.ehcache.EhCacheFactoryBean
"
>
11
<
bean id
=
"
resourceCacheBackend
"
class
=
"
org.springframework.cache.ehcache.EhCacheFactoryBean
"
>
11
 <
property name
=
"
cacheManager
"
ref
=
"
cacheManager
"
/>
12
<
property name
=
"
cacheManager
"
ref
=
"
cacheManager
"
/>
12
 <
property name
=
"
cacheName
"
value
=
"
resourceCache
"
/>
13
<
property name
=
"
cacheName
"
value
=
"
resourceCache
"
/>
13
 bean
>
14
bean
>
14
 15
15
 <
bean id
=
"
resourceCache
"
class
=
"
org.springside.modules.security.service.acegi.cache.ResourceCache
"
autowire
=
"
byName
"
>
16
<
bean id
=
"
resourceCache
"
class
=
"
org.springside.modules.security.service.acegi.cache.ResourceCache
"
autowire
=
"
byName
"
>
16
 <
property name
=
"
cache
"
ref
=
"
resourceCacheBackend
"
/>
17
<
property name
=
"
cache
"
ref
=
"
resourceCacheBackend
"
/>
17
 bean
>
bean
>
6)
basicProcessingFilter 用于处理HTTP头的认证信息,如从
Spring远程协议(如Hessian和Burlap)或
普通的浏览器如IE,Navigator的HTTP头中获取用户 信息,将他们转交给通过
authenticationManager属性装配的认证管理器。如果认证成功,会
将一个Authentication对象放到会话中 ,否则,如果认证失败,会将控制
转交给认证入口点(通过authenticationEntryPoint属性装配)
1
 <
bean id
=
"
basicProcessingFilter
"
class
=
"
org.acegisecurity.ui.basicauth.BasicProcessingFilter
"
>
2
<
bean id
=
"
basicProcessingFilter
"
class
=
"
org.acegisecurity.ui.basicauth.BasicProcessingFilter
"
>
2
 <
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
<
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
 <
property name
=
"
authenticationEntryPoint
"
ref
=
"
basicProcessingFilterEntryPoint
"
/>
4
<
property name
=
"
authenticationEntryPoint
"
ref
=
"
basicProcessingFilterEntryPoint
"
/>
4
 bean
>
bean
>
7) basicProcessingFilterEntryPoint 通过向浏览器发送一个HTTP401(未授权)消息,提示用户登录。 处理基于HTTP的授权过程, 在当验证过程出现异常后的"去向",通常实现转向、在response里加入error信息等功能。
1
 <
bean id
=
"
basicProcessingFilterEntryPoint
"
2
<
bean id
=
"
basicProcessingFilterEntryPoint
"
2
 class
=
"
org.acegisecurity.ui.basicauth.BasicProcessingFilterEntryPoint
"
>
3
class
=
"
org.acegisecurity.ui.basicauth.BasicProcessingFilterEntryPoint
"
>
3
 <
property name
=
"
realmName
"
value
=
"
SpringSide Realm
"
/>
4
<
property name
=
"
realmName
"
value
=
"
SpringSide Realm
"
/>
4
 bean
>
bean
>
8) authenticationProcessingFilterEntryPoint 当抛出AccessDeniedException时,将用户重定向到登录界面。属性loginFormUrl配置了一个登录表单的URL,当需要用户登录时,authenticationProcessingFilterEntryPoint会将用户重定向到该URL
1
 <
bean id
=
"
authenticationProcessingFilterEntryPoint
"
2
<
bean id
=
"
authenticationProcessingFilterEntryPoint
"
2
 class
=
"
org.acegisecurity.ui.webapp.AuthenticationProcessingFilterEntryPoint
"
>
3
class
=
"
org.acegisecurity.ui.webapp.AuthenticationProcessingFilterEntryPoint
"
>
3
 <
property name
=
"
loginFormUrl
"
>
4
<
property name
=
"
loginFormUrl
"
>
4
 <
value
>/
security
/
login.jsp
value
>
5
<
value
>/
security
/
login.jsp
value
>
5
 property
>
6
property
>
6
 <
property name
=
"
forceHttps
"
value
=
"
false
"
/>
7
<
property name
=
"
forceHttps
"
value
=
"
false
"
/>
7
 bean
>
bean
>
2.2.3 HTTP安全请求
1) httpSessionContextIntegrationFilter 每次request前 HttpSessionContextIntegrationFilter从Session中获取Authentication对象,在request完后, 又把Authentication对象保存到Session中供下次request使用,此filter必须其他Acegi filter前使用,使之能跨越多个请求。
1
 <
bean id
=
"
httpSessionContextIntegrationFilter
"
2
<
bean id
=
"
httpSessionContextIntegrationFilter
"
2
 class
=
"
org.acegisecurity.context.HttpSessionContextIntegrationFilter
"
/>
class
=
"
org.acegisecurity.context.HttpSessionContextIntegrationFilter
"
/>
2) httpRequestAccessDecisionManager 经过投票机制来决定是否可以访问某一资源(URL或方法)。allowIfAllAbstainDecisions为false时如果有一个或以上的decisionVoters投票通过,则授权通过。可选的决策机制有ConsensusBased和UnanimousBased
1
 <
bean id
=
"
httpRequestAccessDecisionManager
"
class
=
"
org.acegisecurity.vote.AffirmativeBased
"
>
2
<
bean id
=
"
httpRequestAccessDecisionManager
"
class
=
"
org.acegisecurity.vote.AffirmativeBased
"
>
2
 <
property name
=
"
allowIfAllAbstainDecisions
"
value
=
"
false
"
/>
3
<
property name
=
"
allowIfAllAbstainDecisions
"
value
=
"
false
"
/>
3
 <
property name
=
"
decisionVoters
"
>
4
<
property name
=
"
decisionVoters
"
>
4
 <
list
>
5
<
list
>
5
 <
ref bean
=
"
roleVoter
"
/>
6
<
ref bean
=
"
roleVoter
"
/>
6
 list
>
7
list
>
7
 property
>
8
property
>
8
 bean
>
bean
>
3) roleVoter 必须是以rolePrefix设定的value开头的权限才能进行投票,如AUTH_ , ROLE_
1
 <
bean id
=
"
roleVoter
"
class
=
"
org.acegisecurity.vote.RoleVoter
"
>
2
<
bean id
=
"
roleVoter
"
class
=
"
org.acegisecurity.vote.RoleVoter
"
>
2
 <
property name
=
"
rolePrefix
"
value
=
"
AUTH_
"
/>
3
<
property name
=
"
rolePrefix
"
value
=
"
AUTH_
"
/>
3
 bean
>
bean
>
4)exceptionTranslationFilter 异常转换过滤器,主要是处理AccessDeniedException和AuthenticationException,将给每个异常找到合适的"去向"
1
 <
bean id
=
"
exceptionTranslationFilter
"
class
=
"
org.acegisecurity.ui.ExceptionTranslationFilter
"
>
2
<
bean id
=
"
exceptionTranslationFilter
"
class
=
"
org.acegisecurity.ui.ExceptionTranslationFilter
"
>
2
 <
property name
=
"
authenticationEntryPoint
"
ref
=
"
authenticationProcessingFilterEntryPoint
"
/>
3
<
property name
=
"
authenticationEntryPoint
"
ref
=
"
authenticationProcessingFilterEntryPoint
"
/>
3
 bean
>
bean
>
5) authenticationProcessingFilter 和servlet spec差不多,处理登陆请求.当身份验证成功时,AuthenticationProcessingFilter会在会话中放置一个Authentication对象,并且重定向到登录成功页面 authenticationFailureUrl定义登陆失败时转向的页面 defaultTargetUrl定义登陆成功时转向的页面 filterProcessesUrl定义登陆请求的页面 rememberMeServices用于在验证成功后添加cookie信息
1
 <
bean id
=
"
authenticationProcessingFilter
"
class
=
"
org.acegisecurity.ui.webapp.AuthenticationProcessingFilter
"
>
2
<
bean id
=
"
authenticationProcessingFilter
"
class
=
"
org.acegisecurity.ui.webapp.AuthenticationProcessingFilter
"
>
2
 <
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
<
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
 <
property name
=
"
authenticationFailureUrl
"
>
4
<
property name
=
"
authenticationFailureUrl
"
>
4
 <
value
>/
security
/
login.jsp
?
login_error
=
1
value
>
5
<
value
>/
security
/
login.jsp
?
login_error
=
1
value
>
5
 property
>
6
property
>
6
 <
property name
=
"
defaultTargetUrl
"
>
7
<
property name
=
"
defaultTargetUrl
"
>
7
 <
value
>/
admin
/
index.jsp
value
>
8
<
value
>/
admin
/
index.jsp
value
>
8
 property
>
9
property
>
9
 <
property name
=
"
filterProcessesUrl
"
>
10
<
property name
=
"
filterProcessesUrl
"
>
10
 <
value
>/
j_acegi_security_check
value
>
11
<
value
>/
j_acegi_security_check
value
>
11
 property
>
12
property
>
12
 <
property name
=
"
rememberMeServices
"
ref
=
"
rememberMeServices
"
/>
13
<
property name
=
"
rememberMeServices
"
ref
=
"
rememberMeServices
"
/>
13
 bean
>
bean
>
6) filterInvocationInterceptor 在执行转向url前检查objectDefinitionSource中设定的用户权限信息。首先,objectDefinitionSource中定义了访问URL需要的属性信息(这里的属性信息仅仅是标志,告诉accessDecisionManager要用哪些voter来投票)。然后,authenticationManager掉用自己的provider来对用户的认证信息进行校验。最后,有投票者根据用户持有认证和访问url需要的属性,调用自己的voter来投票,决定是否允许访问。
1
 <
bean id
=
"
filterInvocationInterceptor
"
class
=
"
org.acegisecurity.intercept.web.FilterSecurityInterceptor
"
>
2
<
bean id
=
"
filterInvocationInterceptor
"
class
=
"
org.acegisecurity.intercept.web.FilterSecurityInterceptor
"
>
2
 <
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
<
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
3
 <
property name
=
"
accessDecisionManager
"
ref
=
"
httpRequestAccessDecisionManager
"
/>
4
<
property name
=
"
accessDecisionManager
"
ref
=
"
httpRequestAccessDecisionManager
"
/>
4
 <
property name
=
"
objectDefinitionSource
"
ref
=
"
filterDefinitionSource
"
/>
5
<
property name
=
"
objectDefinitionSource
"
ref
=
"
filterDefinitionSource
"
/>
5
 bean
>
bean
>
7)filterDefinitionSource(详见 2.6.3 资源权限定义扩展) 自定义DBFilterInvocationDefinitionSource从数据库和cache中读取保护资源及其需要的访问权限信息
1
 <
bean id
=
"
filterDefinitionSource
"
2
<
bean id
=
"
filterDefinitionSource
"
2
 class
=
"
org.springside.modules.security.service.acegi.DBFilterInvocationDefinitionSource
"
>
3
class
=
"
org.springside.modules.security.service.acegi.DBFilterInvocationDefinitionSource
"
>
3
 <
property name
=
"
convertUrlToLowercaseBeforeComparison
"
value
=
"
true
"
/>
4
<
property name
=
"
convertUrlToLowercaseBeforeComparison
"
value
=
"
true
"
/>
4
 <
property name
=
"
useAntPath
"
value
=
"
true
"
/>
5
<
property name
=
"
useAntPath
"
value
=
"
true
"
/>
5
 <
property name
=
"
acegiCacheManager
"
ref
=
"
acegiCacheManager
"
/>
6
<
property name
=
"
acegiCacheManager
"
ref
=
"
acegiCacheManager
"
/>
6
 bean
>
bean
>
2.2.4 方法调用安全控制
(详见 2.6.3 资源权限定义扩展)
1) methodSecurityInterceptor 在执行方法前进行拦截,检查用户权限信息
1
 <
bean id
=
"
methodSecurityInterceptor
"
2
<
bean id
=
"
methodSecurityInterceptor
"
2
 class
=
"
org.acegisecurity.intercept.method.aopalliance.MethodSecurityInterceptor
"
>
3
class
=
"
org.acegisecurity.intercept.method.aopalliance.MethodSecurityInterceptor
"
>
3
 <
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
4
<
property name
=
"
authenticationManager
"
ref
=
"
authenticationManager
"
/>
4
 <
property name
=
"
accessDecisionManager
"
ref
=
"
httpRequestAccessDecisionManager
"
/>
5
<
property name
=
"
accessDecisionManager
"
ref
=
"
httpRequestAccessDecisionManager
"
/>
5
 <
property name
=
"
objectDefinitionSource
"
ref
=
"
methodDefinitionSource
"
/>
6
<
property name
=
"
objectDefinitionSource
"
ref
=
"
methodDefinitionSource
"
/>
6
 bean
>
bean
>
2) methodDefinitionSource 自定义MethodDefinitionSource从cache中读取权限
1
 <
bean id
=
"
methodDefinitionSource
"
2
<
bean id
=
"
methodDefinitionSource
"
2
 class
=
"
org.springside.modules.security.service.acegi.DBMethodDefinitionSource
"
>
3
class
=
"
org.springside.modules.security.service.acegi.DBMethodDefinitionSource
"
>
3
 <
property name
=
"
acegiCacheManager
"
ref
=
"
acegiCacheManager
"
/>
4
<
property name
=
"
acegiCacheManager
"
ref
=
"
acegiCacheManager
"
/>
4
 bean
>
bean
>
出处:http://www.blogjava.net/liuwentao253/archive/2006/06/06/50770.html
 同时,我们也引入了resource(资源)的概念,一个资源对应多个权限,资源分为ACL,URL,和FUNTION三种。注意,URL和FUNTION的权限命名需要以AUTH_开头才会有资格参加投票, 同样的ACL权限命名需要ACL_开头。 2.1 在Web.xml中的配置 :
同时,我们也引入了resource(资源)的概念,一个资源对应多个权限,资源分为ACL,URL,和FUNTION三种。注意,URL和FUNTION的权限命名需要以AUTH_开头才会有资格参加投票, 同样的ACL权限命名需要ACL_开头。 2.1 在Web.xml中的配置 :