Jarvis OJ AndroidNormal逆向总结
在mainactivity处发现stringFromJIN,我们要找到.so文件用IDA进行查看。

在lib内看到有多个不同版本的.so文件,并且每一个里面都有libhello-libs.so。
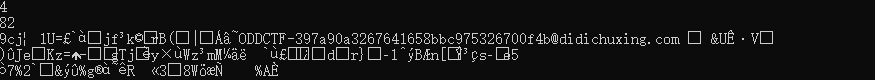
我们通常分析armeabi-v7a。在该题中有一个简便方法就是当我们打开v8a结尾中的.so文件时,放到任意二进制编译工具中,如winhex。会在字符串中直接找到flag。
我们用IDA打开v7a中的.so文件。
定位到关键函数之后,F5查看伪代码
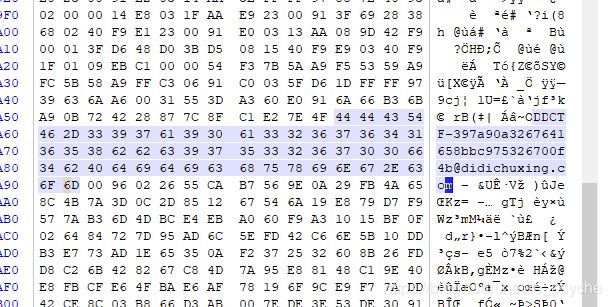
把byte_66c与byte_722的值dump下来之后。
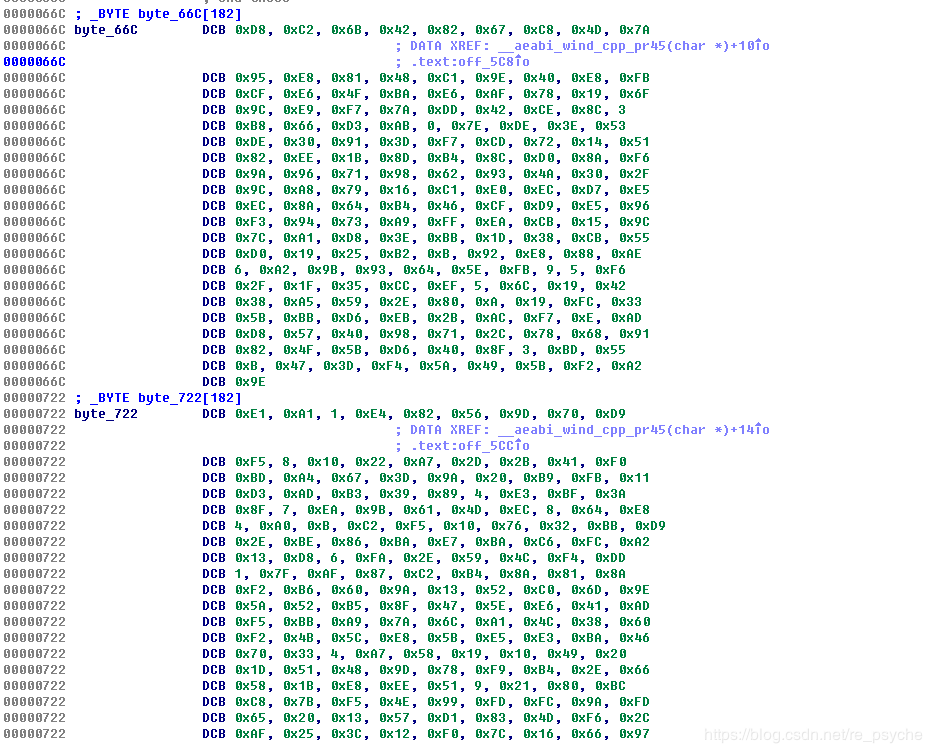
直接py大法好:
p = [0xD8, 0xC2, 0x6B, 0x42, 0x82, 0x67, 0xC8, 0x4D, 0x7A,0x95,
0xE8, 0x81, 0x48, 0xC1, 0x9E, 0x40, 0xE8, 0xFB,0xCF, 0xE6,
0x4F, 0xBA, 0xE6, 0xAF, 0x78, 0x19, 0x6F,0x9C, 0xE9, 0xF7,
0x7A, 0xDD, 0x42, 0xCE, 0x8C, 0x03,0xB8, 0x66, 0xD3, 0xAB,
0x00, 0x7E, 0xDE, 0x3E, 0x53,0xDE, 0x30, 0x91, 0x3D, 0xF7,
0xCD, 0x72, 0x14, 0x51,0x82, 0xEE, 0x1B, 0x8D, 0xB4, 0x8C,
0xD0, 0x8A, 0xF6,0x9A, 0x96, 0x71, 0x98, 0x62, 0x93, 0x4A,
0x30, 0x2F,0x9C, 0xA8, 0x79, 0x16, 0xC1, 0xE0, 0xEC, 0xD7,
0xE5,0xEC, 0x8A, 0x64, 0xB4, 0x46, 0xCF, 0xD9, 0xE5, 0x96,
0xF3, 0x94, 0x73, 0xA9, 0xFF, 0xEA, 0xCB, 0x15, 0x9C,
0x7C, 0xA1, 0xD8, 0x3E, 0xBB, 0x1D, 0x38, 0xCB, 0x55,
0xD0, 0x19, 0x25, 0xB2, 0xB, 0x92, 0xE8, 0x88, 0xAE,
0x06, 0xA2, 0x9B, 0x93, 0x64, 0x5E, 0xFB, 0x09, 0x05, 0xF6,
0x2F, 0x1F, 0x35, 0xCC, 0xEF, 0x05, 0x6C, 0x19, 0x42,
0x38, 0xA5, 0x59, 0x2E, 0x80, 0x0A, 0x19, 0xFC, 0x33,
0x5B, 0xBB, 0xD6, 0xEB, 0x2B, 0xAC, 0xF7, 0x0E, 0xAD,
0xD8, 0x57, 0x40, 0x98, 0x71, 0x2C, 0x78, 0x68, 0x91,
0x82, 0x4F, 0x5B, 0xD6, 0x40, 0x8F, 0x03, 0xBD, 0x55,
0xB, 0x47, 0x3D, 0xF4, 0x5A, 0x49, 0x5B, 0xF2, 0xA2,
0x9E]
q= [0xE1, 0xA1, 0x01, 0xE4, 0x82, 0x56, 0x9D, 0x70, 0xD9,
0xF5, 0x08, 0x10, 0x22, 0xA7, 0x2D, 0x2B, 0x41, 0xF0,
0xBD, 0xA4, 0x67, 0x3D, 0x9A, 0x20, 0xB9, 0xFB, 0x11,
0xD3, 0xAD, 0xB3, 0x39, 0x89, 0x04, 0xE3, 0xBF, 0x3A,
0x8F, 0x07, 0xEA, 0x9B, 0x61, 0x4D, 0xEC, 0x08, 0x64, 0xE8,
0x04, 0xA0, 0x0B, 0xC2, 0xF5, 0x10, 0x76, 0x32, 0xBB, 0xD9,
0x2E, 0xBE, 0x86, 0xBA, 0xE7, 0xBA, 0xC6, 0xFC, 0xA2,
0x13, 0xD8, 0x06, 0xFA, 0x2E, 0x59, 0x4C, 0xF4, 0xDD,
0x01, 0x7F, 0xAF, 0x87, 0xC2, 0xB4, 0x8A, 0x81, 0x8A,
0xF2, 0xB6, 0x60, 0x9A, 0x13, 0x52, 0xC0, 0x6D, 0x9E,
0x5A, 0x52, 0xB5, 0x8F, 0x47, 0x5E, 0xE6, 0x41, 0xAD,
0xF5, 0xBB, 0xA9, 0x7A, 0x6C, 0xA1, 0x4C, 0x38, 0x60,
0xF2, 0x4B, 0x5C, 0xE8, 0x5B, 0xE5, 0xE3, 0xBA, 0x46,
0x70, 0x33, 0x04, 0xA7, 0x58, 0x19, 0x10, 0x49, 0x20,
0x1D, 0x51, 0x48, 0x9D, 0x78, 0xF9, 0xB4, 0x2E, 0x66,
0x58, 0x1B, 0xE8, 0xEE, 0x51, 0x09, 0x21, 0x80, 0xBC,
0xC8, 0x7B, 0xF5, 0x4E, 0x99, 0xFD, 0xFC, 0x9A, 0xFD,
0x65, 0x20, 0x13, 0x57, 0xD1, 0x83, 0x4D, 0xF6, 0x2C,
0xAF, 0x25, 0x3C, 0x12, 0xF0, 0x7C, 0x16, 0x66, 0x97,
0x7F, 0x6A, 0x02, 0xBC, 0x98, 0x52, 0xD7, 0xE3, 0x56]
c=[]
j=0
flag=''
for i in range(0,len(p)):
c.append(p[i]^q[i])
if c[i]==0:
print(i)
for i in c:
flag +=chr(i)
print(flag)