windows下weblogic单双向ssl设置
1. ssl原理个人理解
网上关于ssl原理讲的很详细,由于我仅仅需要配置weblogic的ssl,所以对ssl没有做深入的理解,以下仅是我个人对ssl的一些理解,不保证正确性。
ssl协议是保证客户端和服务器能够实现安全传输的一个协议,客户端向服务器发送请求后服务器会返回一个证书,里面包含必要信息密钥来验证身份,证明你的确是老大,而验证身份就需要有一个公证员,那么CA机构就是这个公证员。因此,必须要有的东西是CA的证书和服务器的证书。有的情况下,服务器也需要验证访问它的客户端的身份和信息,正如有的老大要确认你就是我的小弟,这时就需要客户端证书了。
总之,如果仅需要CA证书和服务器证书,那就是单向ssl。如果还需要客户端证书,那就是双向ssl。
2. 必备软件
openssl工具用来制作密钥、CA根证书。网上直接搜索openssl下载即可。
3. 单向ssl配置
安装openssl,然后cmd进入安装目录的bin目录下面。新建文件夹ca。
建立CA证书
1.创建私钥
D:\OpenSSL\bin>openssl genrsa -out ca/ca-key.pem 1024
Loading 'screen' into random state - done
Generating RSA private key, 1024 bit long modulus
.....++++++
........................................++++++
e is 65537 (0x10001)2.创建证书请求
D:\OpenSSL\bin>openssl req -new -out ca/ca-req.csr -key ca/ca-key.pem -config openssl.cnf
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:CN
State or Province Name (full name) [Some-State]:BJ
Locality Name (eg, city) []:HD
Organization Name (eg, company) [Internet Widgits Pty Ltd]:CAROOT
Organizational Unit Name (eg, section) []:CA
Common Name (eg, YOUR name) []:Trigl
Email Address []://直接回车,不配置
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []://直接回车,不配置
An optional company name []://直接回车,不配置3.生成CA自签名证书
D:\OpenSSL\bin>openssl x509 -req -in ca/ca-req.csr -out ca/ca-cert.pem -signkey
ca/ca-key.pem -days 3650
Loading 'screen' into random state - done
Signature ok
subject=/C=CN/ST=BJ/L=HD/O=CAROOT/OU=CA/CN=Trigl
Getting Private key制作服务器证书
4.用keytool工具生成密钥
D:\OpenSSL\bin>keytool -genkey -alias sso -validity 365 -keyalg RSA -keysize 1024 -keypass 123456 -storepass 123456 -keystore sso.jks
您的名字与姓氏是什么?
[Unknown]: Trigl
您的组织单位名称是什么?
[Unknown]: CAROOT
您的组织名称是什么?
[Unknown]: CA
您所在的城市或区域名称是什么?
[Unknown]: HD
您所在的州或省份名称是什么?
[Unknown]: BJ
该单位的两字母国家代码是什么
[Unknown]: CN
CN=Trigl, OU=CAROOT, O=CA, L=HD, ST=BJ, C=CN 正确吗?
[否]: y5.用keytool工具生成证书请求
D:\OpenSSL\bin>keytool -certreq -alias sso -sigalg MD5withRSA -file sso.csr -keypass 123456 -keystore sso.jks -storepass 123456 6.根据证书请求,生成服务器证书
D:\OpenSSL\bin>openssl x509 -req -in sso.csr -out sso.pem -CA ca/ca-cert.pem -CAkey ca/ca-key.pem -days 3650 -set_serial 1
Loading 'screen' into random state - done
Signature ok
subject=/C=CN/ST=BJ/L=HD/O=CA/OU=CAROOT/CN=Trigl
Getting CA Private Key向keystore密钥库中导入证书
7.导入CA证书
D:\OpenSSL\bin>keytool -import -v -trustcacerts -keypass 123456 -storepass 123456 -alias root -file ca/ca-cert.pem -keystore sso.jks
所有者:CN=Trigl, OU=CA, O=CAROOT, L=HD, ST=BJ, C=CN
签发人:CN=Trigl, OU=CA, O=CAROOT, L=HD, ST=BJ, C=CN
序列号:9b6ef80677f56488
有效期: Tue Nov 03 16:27:12 CST 2015 至Fri Oct 31 16:27:12 CST 2025
证书指纹:
MD5:33:83:B9:67:2C:B9:C7:5A:1A:0B:2D:CB:87:03:06:0B
SHA1:3C:47:DE:9F:5A:A3:93:93:AD:7A:F0:93:99:25:B0:5F:D2:EC:3A:A9
签名算法名称:MD5withRSA
版本: 1
信任这个认证? [否]: y
认证已添加至keystore中
[正在存储 sso.jks]8.导入服务器证书
D:\OpenSSL\bin>keytool -import -v -trustcacerts -storepass 123456 -alias sso -file sso.pem -keystore sso.jks
认证已添加至keystore中
[正在存储 sso.jks]9.导入CA验签信息
D:\OpenSSL\bin>keytool -import -alias sso-ca -trustcacerts -file ca/ca-cert.pem -keystore ssotrust.jks
输入keystore密码:
再次输入新密码:
所有者:CN=Trigl, OU=CA, O=CAROOT, L=HD, ST=BJ, C=CN
签发人:CN=Trigl, OU=CA, O=CAROOT, L=HD, ST=BJ, C=CN
序列号:9b6ef80677f56488
有效期: Tue Nov 03 16:27:12 CST 2015 至Fri Oct 31 16:27:12 CST 2025
证书指纹:
MD5:33:83:B9:67:2C:B9:C7:5A:1A:0B:2D:CB:87:03:06:0B
SHA1:3C:47:DE:9F:5A:A3:93:93:AD:7A:F0:93:99:25:B0:5F:D2:EC:3A:A9
签名算法名称:MD5withRSA
版本: 1
信任这个认证? [否]: y
认证已添加至keystore中10.以上步骤会产生两个密钥库文件:sso.jks和ssotrust.jks,在weblogic中ssl的配置中用到。首先将这两个文件复制到weblogci域的根目录下面,即:
D:\Weblogic\Middleware\user_projects\domains\base_domain下面
启动weblogic的ssl监听端口
11.登陆weblogic页面,首先进入如下页面启动ssl监听端口
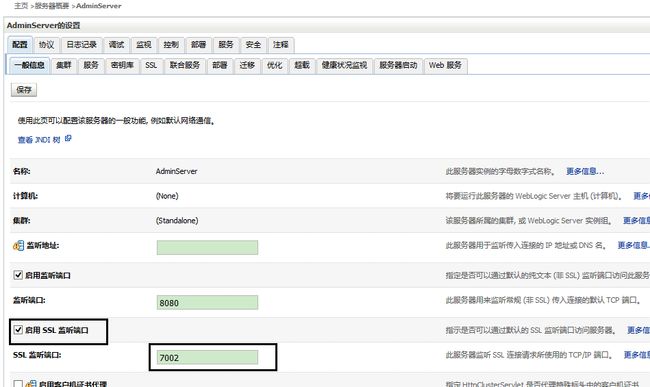
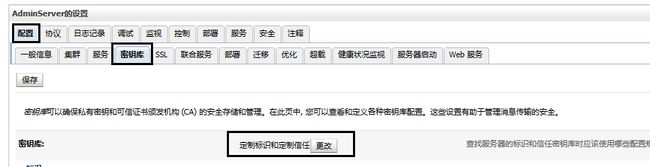
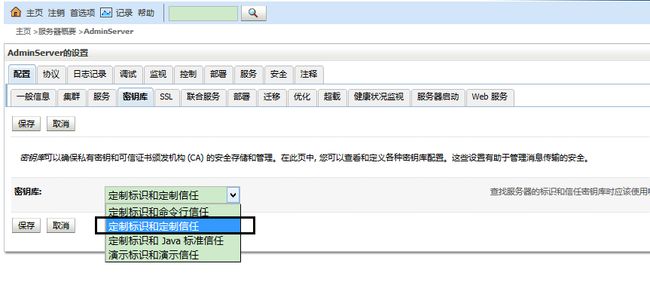
配置weblogi的密钥库
然后填写相应的标识密钥库和信任密钥库,这里填入的密钥库文件就是前面产生的sso.jks和ssotrust.jks两个文件,密码是之前设置的123456,填写完成后记得保存

配置weblogic的ssl
13.进入ssl配置页面,如下图所示,密钥别名就是前面定义好的名字,这里是sso,密码还是123456

浏览器验证
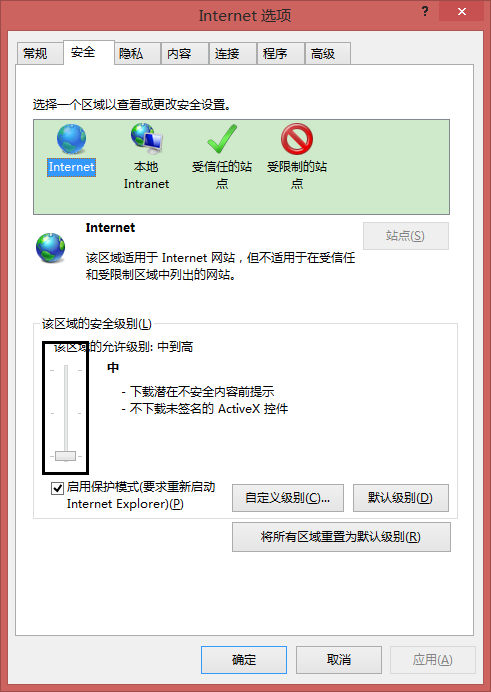
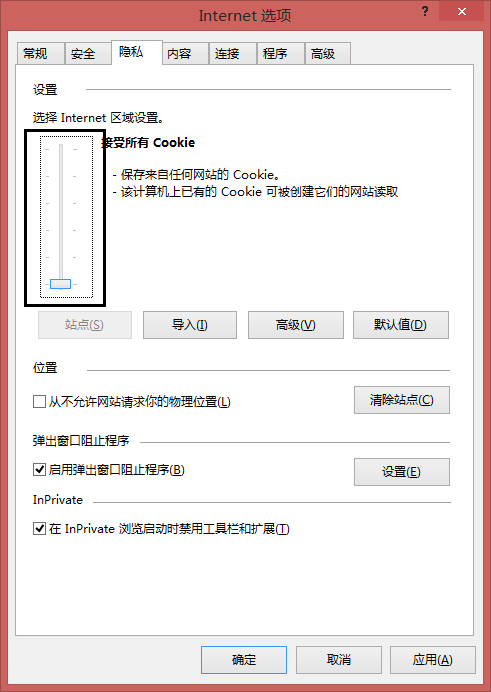
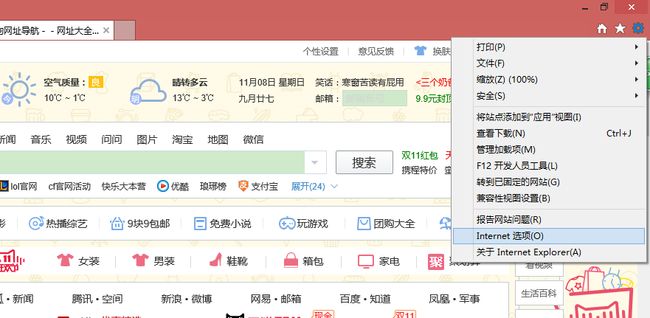
14.到这里,单向 ssl配置就完成了,在浏览器中输入https://localhost:7002/console访问控制台进行测试,但是一般浏览器默认的安全等级是比较高的,所有可能无法访问,我们需要手动降低浏览器安全等级,以ie为例:
选择Internet选项
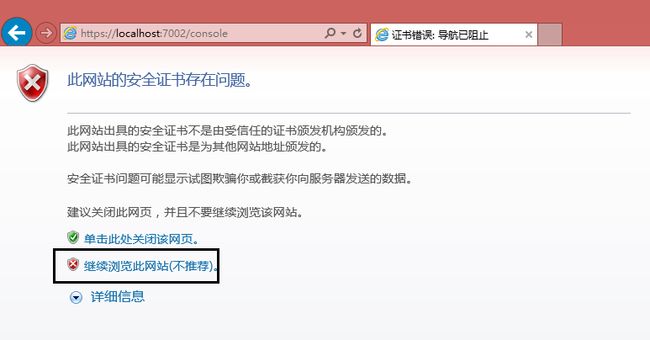
这时候就可以输入https://localhost:7002/console进行验证了,如下图:
4. 双向ssl配置
制作客户端证书
1.产生客户端对应的私钥
D:\OpenSSL\bin>openssl genrsa -out user-key.pem 1024
Loading 'screen' into random state - done
Generating RSA private key, 1024 bit long modulus
...............++++++
........................................++++++
e is 65537 (0x10001)2.根据私钥产生证书请求csr文件
D:\OpenSSL\bin>openssl req -new -out user-req.csr -key user-key.pem
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [AU]:CN
State or Province Name (full name) [Some-State]:BJ
Locality Name (eg, city) []:HD
Organization Name (eg, company) [Internet Widgits Pty Ltd]:CAROOT
Organizational Unit Name (eg, section) []:CA
Common Name (eg, YOUR name) []:admin//登陆帐户名
Email Address []:
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:
An optional company name []:3.使用openssl之前制作的ca根证书对证书请求文件进行签证
D:\OpenSSL\bin>openssl x509 -req -in user-req.csr -out user-cert.pem -signkey us
er-key.pem -CA ca/ca-cert.pem -CAkey ca/ca-key.pem -CAcreateserial -days 3650
Loading 'screen' into random state - done
Signature ok
subject=/C=CN/ST=BJ/L=HD/O=CAROOT/OU=CA/CN=admin
Getting Private key
Getting CA Private Key4.将签证之后的证书文件user-cert.pem导出为p12格式文件(p12格式可以被浏览器识别并安装到证书库中)
D:\OpenSSL\bin>openssl pkcs12 -export -clcerts -in user-cert.pem -inkey user-key
.pem -out user.p12
Loading 'screen' into random state - done
Enter Export Password://不输入
Verifying - Enter Export Password://不输入5.将签证之后的证书文件user-cert.pem导入至信任秘钥库中(这里由于没有去ca认证中心购买个人证书,所以只有导入信任库才可进行双向ssl交互)
D:\OpenSSL\bin>keytool -import -alias user -trustcacerts -file user-cert.pem -ke
ystore ssotrust.jks
输入keystore密码:
认证已添加至keystore中6.需要把最后增加证书的信任秘钥库exampletrust.jks重新复制到domain目录下。
weblogic控制台双向ssl配置
7.进入weblogic控制台如下页面,进入ssl配置页面,点击高级

选择双向客户机证书行为中的请求客户机证书并强制使用,这样就强制客户端浏览器提供证书,修改完成记得保存

8.接下来,双击刚才生成的p12文件,即在目录D:\OpenSSL\bin里面的user.p12,将用户证书安装到浏览器的证书库中,一直点击下一步即可

9.以上就完成了双向ssl的相关配置,可以在具体java代码中调用相关文件