一、相关介绍
1.简介
SSH是一个安全协议,在进行数据传输时,会对数据包进行加密处理,加密后在进行数据传输。确保了数据传输安全。那SSH服务主要功能有哪些呢?
1)提供远程连接的服务
linux远程连接: ssh telnet
windows的远程连接: RDP (remote desktop)、向日葵、teamviewer
2)对传输数据进行加密
2.ssh和telnet
1)使用telnet连接服务器
#安装telnet服务
[root@NFS ~]# yum install -y telnet-server
#启动
[root@NFS ~]# systemctl start telnet.socket
#telnet只支持普通用户登录,创建用户
[root@NFS ~]# useradd lhd
[root@NFS ~]# echo 123 | passwd --stdin lhd
Changing password for user lhd.
passwd: all authentication tokens updated successfully.
#连接测试
[c:\~]$ telnet 10.0.0.31 23
Connecting to 10.0.0.31:23...
Connection established.
To escape to local shell, press 'Ctrl+Alt+]'.
Kernel 3.10.0-957.el7.x86_64 on an x86_64
NFS login: lhd
Password: 123
[lhd@NFS ~]$ su -
#筛选去重命令
[root@NFS ~]# echo "vviimm //eettcc//ssyyssccoonnffiigg//nneettwwoorrkk--ssccrriippttss//iiffccffgg--eetthh00" | sed -nr 's#(.)(.)#\1#gp'
vim /etc/sysconfig/network-scripts/ifcfg-eth0
2)ssh和telnet两者区别
#telnet:
不能使用root用户登录,只能使用普通用户
数据包没有进行加密,传输都是明文的
#ssh:
可以使用任意用户登录
数据传输都是加密的
二、ssh相关命令
1.ssh客户端和服务端
SSH有客户端与服务端,我们将这种模式称为C/S架构,ssh客户端支持Windows、Linux、Mac等平台。
在ssh客户端中包含 ssh|slogin远程登陆、scp远程拷贝、sftp文件传输、ssh-copy-id秘钥分发等应用程序。
2.ssh命令
[root@web01 ~]# ssh [email protected] -p 22
#命令拆分
ssh #命令
root #系统用户(如果不写,就使用当前服务器的当前用户)
@ #分隔符
172.16.1.31 #远程主机的IP
-p #指定端口(终端不支持)
22 #端口(默认22)
-o StrictHostKeyChecking=no #首次访问时不验证身份
3.xshell连接不上虚拟机怎么办?
1)查网络
ping ip
tcping ip port
2)查端口
telnet
tcping ip port
3)检查网卡是否启动
ip a
4)虚拟网络编辑器
查看子网IP和网关
5)查看windows虚拟网卡
vmnat8
6)防火墙
三、scp命令
1.简介
scp客户端命令:远程拷贝
类似于rsync,scp全量,rsync增量
scp支持推和拉
2.scp推
#把当前目录下的hostname_ip.sh文件推送到172.16.1.31机器的/tmp目录下
[root@web01 ~]# scp hostname_ip.sh 172.16.1.31:/tmp
#注意:
与rsync不同,推送时不论是加 / 还是不加 / ,推送的都是目录
如果想推送目录下的文件,则使用 *
3.scp拉
[root@web01 ~]# scp 172.16.1.31:/tmp/1.txt ./
#注意:
与rsync不同,拉取时不论是加 / 还是不加 / ,拉取的都是目录
如果想拉取目录下的文件,则使用 *
4.常用参数
-P 指定端口,默认22端口可不写
-r 表示递归拷贝目录
-p 表示在拷贝文件前后保持文件或目录属性不变
-l 限制传输使用带宽(默认kb)
[root@web01 /tmp]# scp -l 8096 1.txt 172.16.1.31:/tmp/
[email protected]'s password:
1.txt 12% 64MB 1.0MB/s 07:19 ETA
5.总结
1)scp通过ssh协议加密方式进行文件或目录拷贝。
2)scp连接时的用户作为为拷贝文件或目录的权限。
3)scp支持数据推送和拉取,每次都是全量拷贝,效率较低。
四、sftp命令
1.终端连接
#文件传输命令
sftp:/root>
#下载文件
sftp:/root> get hostname_ip.sh
Fetching /root/hostname_ip.sh to hostname_ip.sh
sftp: received 497 ؖ½ؠin 0.01 seconds
#上传文件
sftp:/root> put
2.服务器之间连接
#连接
[root@web01 ~]# sftp [email protected]
[email protected]'s password:
Connected to 172.16.1.31.
#操作远程连接过去的机器
sftp> pwd
Remote working directory: /root
sftp> ls -l
-rw------- 1 root root 1429 Jul 6 02:17 anaconda-ks.cfg
-rw-r--r-- 1 root root 497 Aug 5 20:15 hostname_ip.sh
-rw-r--r-- 1 root root 727290 Aug 15 01:15 sersync2.5.4_64bit_binary_stable_final.tar.gz
#如果想操作本机,则在命令前加一个 l
sftp> lls -l
total 8
-rw-r--r-- 1 root root 0 Aug 18 00:25 1.txt
-rw-------. 1 root root 1429 Jul 6 02:17 anaconda-ks.cfg
-rw-r--r--. 1 root root 497 Aug 5 20:15 hostname_ip.sh
#拉取命令
sftp> get 1.txt ./
#当使用拉取命令的时候,前面的是远程服务器,后面的是本地服务器
#推送命令
sftp> put 1.txt ./
#当使用put的时候,前面的是本地服务器,后面的是远程服务器
3.文件传输工具
#图形化工具
1)xftp
2)filezilla
3)flashfxp
4.命令对比
#rz/sz:
1)不能上传4G以上的文件
2)不能断点续传
3)不能上传文件夹
#sftp:
1)能上传大于4G的文件
2)能断点续传
3)可以上传文件夹
1.方式一:基于用户名密码远程连接
#需要知道服务器的IP,端口,系统用户,用户密码才能链接远程主机
[root@NFS ~]# ssh [email protected] -p 2222
[email protected]'s password:
Last login: Tue Aug 18 00:44:33 2020 from 10.0.0.1
[root@web01 ~]#
#设置密码
1)复杂的密码(容易忘记)
2)简单的密码(容易被破解)
3)每台机器密码都不一样
4)密码是动态的
5)密码三个月一变
6)密码错误三次,锁定用户
7)密码肯定是没有规律的
2.基于密钥的方式
默认情况下,通过ssh客户端命令登陆远程服务器,需要提供远程系统上的帐号与密码,但为了降低密码泄露的机率和提高登陆的方便性,建议使用密钥验证方式。
1)生成密钥对
[root@web01 ~]# ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa.
Your public key has been saved in /root/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:n618dqJXK1Z1mvHcv31VadZTBwni3gXEghWSp9+HTj4 root@web01
The key's randomart image is:
+---[RSA 2048]----+
| .++++..o |
| ooo.... o|
| o.. . =|
| .. . ..==|
| S.....oB=|
| ..o+ * =|
| o+.+ .o|
| . .E o +|
| +* = .+|
+----[SHA256]-----+
2)将公钥发送至免密登录的服务器
#方式一:手动复制
[root@web01 ~]# cat .ssh/id_rsa.pub #查看公钥
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDbOLFAuHJy6xtGOBFIWALpyWNyR3ixgULtv9uVMELre1iVv6S/fBT3YqKR6naX1y1oyhWBD6njMhXDANuG9OQ/ABTHrgOJrF5JMY1AS9jI5DrMaIdfoBXcmck6RuID5yddlLiA6VdeHI8ndtth7bu6Ed50otviNbzF7NG7chX9oGbju6uGMY12pb0BKCtJaJ9qycGJOZCi8OyrIycJBexsiC+DYOwvXjmtdRtf7KNBnHSDDEIsywQNku1/WXUE0l4CMoZ/zjgO19fdxfdbCT4qAWTz0r9CDUzhEFIVZgz73KLahy+IXIhNupHXf0VcrS3h11rWDUrOeIw2oIZHEPz3 root@web01
#将公钥写到要连接的机器
[root@NFS ~]# vim .ssh/authorized_keys
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDbOLFAuHJy6xtGOBFIWALpyWNyR3ixgULtv9uVMELre1iVv6S/fBT3YqKR6naX1y1oyhWBD6njMhXDANuG9OQ/ABTHrgOJrF5JMY1AS9jI5DrMaIdfoBXcmck6RuID5yddlLiA6VdeHI8ndtth7bu6Ed50otviNbzF7NG7chX9oGbju6uGMY12pb0BKCtJaJ9qycGJOZCi8OyrIycJBexsiC+DYOwvXjmtdRtf7KNBnHSDDEIsywQNku1/WXUE0l4CMoZ/zjgO19fdxfdbCT4qAWTz0r9CDUzhEFIVZgz73KLahy+IXIhNupHXf0VcrS3h11rWDUrOeIw2oIZHEPz3 root@web01
#授权
[root@NFS ~]# chmod 600 .ssh/authorized_keys
#连接测试
[root@web01 ~]# ssh 172.16.1.31
Last failed login: Tue Aug 18 00:51:38 CST 2020 from 10.0.0.1 on ssh:notty
There was 1 failed login attempt since the last successful login.
Last login: Mon Aug 17 23:39:28 2020 from 172.16.1.7
#方式二:命令推送公钥
[root@web01 ~]# ssh-copy-id -i .ssh/id_rsa.pub [email protected] #命令推送公钥
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: ".ssh/id_rsa.pub"
The authenticity of host '172.16.1.41 (172.16.1.41)' can't be established.
ECDSA key fingerprint is SHA256:mOtCaBS+53EDW9mKoXVj4v5Q1E1fYB0DexMHr/WzTc4.
ECDSA key fingerprint is MD5:75:12:f6:05:4c:5d:66:6f:21:0d:8e:0f:fc:bb:36:d6.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
[root@web01 ~]#
#连接测试
[root@web01 ~]# ssh 172.16.1.41
Last login: Mon Aug 17 23:32:44 2020 from 10.0.0.1
六、ssh免密登录练习
1.需求
1.恢复快照
2.m01连接web01,backup,NFS做免密登录
3.连接的用户是名字的缩写
2.环境准备
| 主机 | 角色 | IP |
|---|---|---|
| m01 | 免密登录 | 10.0.0.61 |
| backup | 备份服务器 | 10.0.0.41 |
| NFS | NFS服务器 | 10.0.0.31 |
| web01 | web服务器 | 10.0.0.7 |
3.创建统一用户
[root@m01 ~]# useradd jh
[root@m01 ~]# passwd jh
Changing password for user jh.
New password:
BAD PASSWORD: The password is a palindrome
Retype new password:
passwd: all authentication tokens updated successfully.
[root@web01 ~]# useradd jh
[root@文web01 ~]# passwd jh
Changing password for user jh.
New password:
BAD PASSWORD: The password is a palindrome
Retype new password:
passwd: all authentication tokens updated successfully.
[root@NFS ~]# useradd jh
[root@NFS ~]# passwd jh
Changing password for user jh.
New password:
BAD PASSWORD: The password is a palindrome
Retype new password:
passwd: all authentication tokens updated successfully.
[root@backup ~]# useradd jh
[root@backup ~]# passwd jh
Changing password for user jh.
New password:
BAD PASSWORD: The password is a palindrome
Retype new password:
passwd: all authentication tokens updated successfully.
4.m01配置backup免密登录
1.切换用户
[root@m01 ~]# su - jh
2.生成验证树
[jh@m01 ~]$ ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (/home/jh/.ssh/id_rsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/jh/.ssh/id_rsa.
Your public key has been saved in /home/jh/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:Km6/mnGgGEZs5tc1sU9Qf6mzTyMZo5LCPRduDgEQIXw jh@m01
The key's randomart image is:
+---[RSA 2048]----+
|.. +o o.. |
|...E. + . . |
| =. . + . . o |
|= . o + o |
|.o ... .So = |
|.o......+ o * |
|. . ooo* = + o |
| ..=. B + . |
| .+oo. . . |
+----[SHA256]-----+
3.命令推送密钥
[jh@m01 ~]$ ssh-copy-id -i .ssh/id_rsa.pub [email protected]
/bin/ssh-copy-id: INFO: Source of key(s) to be installed: ".ssh/id_rsa.pub"
/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
5.m01配置NFS免密登录
1.命令推送密钥
[jh@m01 ~]$ ssh-copy-id -i .ssh/id_rsa.pub [email protected]
/bin/ssh-copy-id: INFO: Source of key(s) to be installed: ".ssh/id_rsa.pub"
The authenticity of host '10.0.0.31 (10.0.0.31)' can't be established.
ECDSA key fingerprint is SHA256:g6buQ4QMSFl+5MMAh8dTCmLtkIfdT8sgRFYc6uCzV3c.
ECDSA key fingerprint is MD5:5f:d7:ad:07:e8:fe:d2:49:ec:79:2f:d4:91:59:c5:03.
Are you sure you want to continue connecting (yes/no)? yes
/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
5m01配置web01免密登录
1.命令推送密钥
[jh@m01 ~]$ ssh-copy-id -i .ssh/id_rsa.pub [email protected]
/bin/ssh-copy-id: INFO: Source of key(s) to be installed: ".ssh/id_rsa.pub"
The authenticity of host '10.0.0.7 (10.0.0.7)' can't be established.
ECDSA key fingerprint is SHA256:g6buQ4QMSFl+5MMAh8dTCmLtkIfdT8sgRFYc6uCzV3c.
ECDSA key fingerprint is MD5:5f:d7:ad:07:e8:fe:d2:49:ec:79:2f:d4:91:59:c5:03.
Are you sure you want to continue connecting (yes/no)? yes
/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
6.测试
1.m01免密登录web01测试连接
[jh@m01 ~]$ ssh [email protected]
Last login: Mon Aug 17 19:28:43 2020 from 10.0.0.61
[jh@web01 ~]$ logout
Connection to 10.0.0.7 closed.
2.m01免密登录NFS测试连接
[jh@m01 ~]$ ssh [email protected]
Last login: Mon Aug 17 19:25:58 2020 from 10.0.0.61
[jh@NFS ~]$ logout
Connection to 10.0.0.31 closed.
3.m01免密登录backup测试连接
[jh@m01 ~]$ ssh [email protected]
Last login: Mon Aug 17 19:24:11 2020 from 10.0.0.61
[jh@backup ~]$ logout
Connection to 10.0.0.41 closed.
4.退出登录
[jh@m01 ~]$
七、ssh免密场景
1.场景介绍
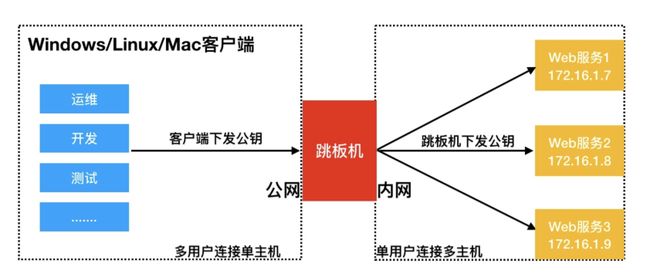
实践场景,用户通过Windows/MAC/Linux客户端连接跳板机免密码登录,跳板机连接后端无外网的Linux主机实现免密登录,架构图如下。
实践多用户登陆一台服务器无密码
实践单用户登陆多台服务器免密码
2.windows使用xshell免密登陆服务器
1.xshell --> 工具 --> 新建用户密钥生成向导
2.下一步 --> 生成公钥对
3.下一步 --> 密钥信息(给密钥起名字,加密码)
4.xshell --> 工具 --> 查看密钥用户管理者
5.密钥属性 --> 公钥
6.将公钥复制到服务器的.ssh目录下的authorized_keys文件
7.授权文件
3,跳板机脚本
#!/bin/bash
#jumpserver
lb01=10.0.0.5
lb02=10.0.0.6
web01=10.0.0.7
web02=10.0.0.8
web03=10.0.0.9
nfs=10.0.0.31
backup=10.0.0.41
db01=10.0.0.51
m01=10.0.0.61
zabbix=10.0.0.71
menu(){
cat <<-EOF
+-------------------------+
| 1) lb01 |
| 2) lb02 |
| 3) web01 |
| 4) web02 |
| 5) web03 |
| 6) nfs |
| 7) backup |
| 8) db01 |
| 9) m01 |
| 10) zabbix |
| h) help |
+-------------------------+
EOF
}
#菜单函数
menu
#连接函数
connect(){
ping -c 1 -w 1 $1 &>/dev/null
if [ $? -eq 0 ];then
ssh root@$1
else
echo -e "\033[5;4;40;31m 别连了,我的哥,$2:$1机器都没开!!!\033[0m"
fi
}
#控制不让输入ctrl+c,z
trap "" HUP INT TSTP
while true
do
read -p "请输入要连接的主机编号:" num
case $num in
1|lb01)
connect $lb01 lb01
;;
2|lb02)
connect $lb02 lb02
;;
3|web01)
connect $web01 web01
;;
4|web02)
connect $web02 web02
;;
5|web03)
connect $web03 web03
;;
6|nfs)
connect $nfs nfs
;;
7|backup)
connect $backup backup
;;
8|db01)
connect $db01 db01
;;
9|m01)
connect $m01 m01
;;
10|zabbix)
connect $zabbix zabbix
;;
h|help)
clear
menu
;;
close)
break
;;
esac
done
八、免交互expect
1.安装expect
[root@m01 ~]# yum install -y expect
2.编写脚本
[root@m01 ~]# vim xunjian.exp
九、免交互sshpass[扩展]
1.安装
[root@m01 ~]# yum install -y sshpass
2.命令参数
[root@m01 ~]# sshpass -p 1 ssh [email protected]
[option]
-p:指定密码
-f:从文件中取密码
-e:从环境变量中取密码
-P:设置密码提示
#当连接不上时,可能是因为没有主机信息文件,则加入ssh免交互参数
[root@m01 ~]# sshpass -p 1 ssh -o StrictHostKeyChecking=no [email protected]
十、ssh安全优化
1.优化内容
SSH作为远程连接服务,通常我们需要考虑到该服务的安全,所以需要对该服务进行安全方面的配置。
1.更改远程连接登陆的端口
2.禁止ROOT管理员直接登录
3.密码认证方式改为密钥认证
4.重要服务不使用公网IP地址
5.使用防火墙限制来源IP地址
2.配置
[root@m01 ~]# vim /etc/ssh/sshd_config
#修改ssh端口
Port 2222
#禁止使用root登录服务器
PermitRootLogin no
#禁止使用密码登录服务器
PasswordAuthentication no
# 禁止ssh进行dns反向解析,影响ssh连接效率参数
UseDNS no
# 禁止GSS认证,减少连接时产生的延迟
GSSAPIAuthentication no