- 管家婆订货易在线商城 VshopProcess 任意文件上传漏洞复现
0xSecl
漏洞复现v1安全web安全
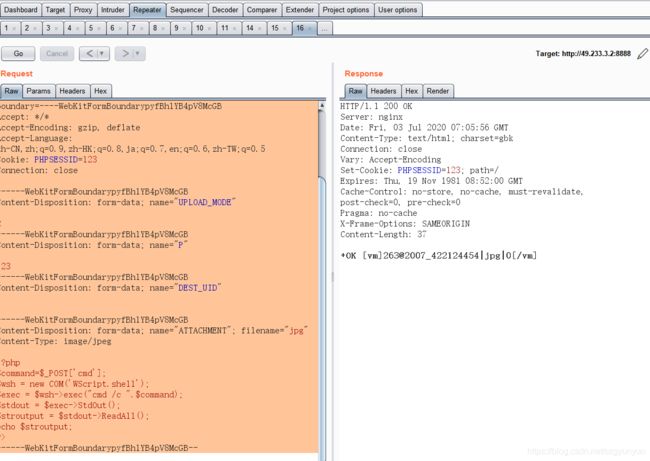
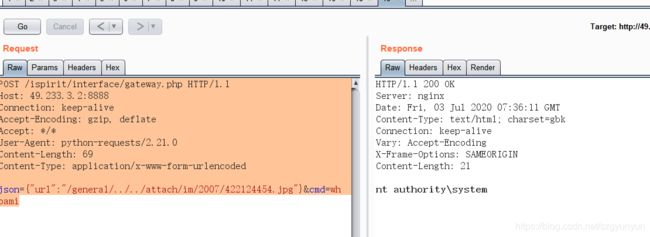
0x01产品简介管家婆订货易,帮助传统企业构建专属的订货平台,PC+微信+APP+小程序+h5商城5网合一,无缝对接线下的管家婆ERP系统,让用户订货更高效。支持业务员代客下单,支持多级推客分销,以客带客,拓展渠道。让企业的生意更轻松。0x02漏洞概述管家婆订货易在线商城VshopProcess.ashx接口处存在任意文件上传漏洞,未经身份认证的攻击者可以通过该漏洞,上传恶意后门文件,深入利用可造
- 2025年渗透测试面试题总结-2025年HW(护网面试) 15(题目+回答)
独行soc
2025年护网面试职场和发展web安全安全linux渗透测试网络安全
安全领域各种资源,学习文档,以及工具分享、前沿信息分享、POC、EXP分享。不定期分享各种好玩的项目及好用的工具,欢迎关注。目录2025年HW(护网面试)151.实习经历2.CNVD证书类型3.登录窗口渗透测试流程4.验证码绕过实战手法技术型绕过(自动化)逻辑型绕过(手动测试)5.WAF绕过能力说明6.职业发展规划7.技术成长周期8.漏洞复现与运营2025年HW(护网面试)151、有没有实习过?在
- Apache Kafka Connect接口存在任意文件读取漏洞与SSRF漏洞CVE-2025-27817
sublime88
漏洞复现apachekafka分布式安全web安全网络sql
@[toc]免责声明:请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。1.ApacheKafka简介微信公众号搜索:南风漏洞复现文库该文章南风漏洞复现文库公众号首发ApacheKafka是一个分布式的流式数据平台,可以用于构建实时的数据管道和流式应用程序
- Apache Solr stream.url SSRF与任意文件读取漏洞(附pythonEXP脚本)
MD@@nr丫卡uer
渗透测试
漏洞背景ApacheSolr是一个开源的搜索服务,使用Java语言开发。ApacheSolr的某些功能存在过滤不严格,在ApacheSolr未开启认证的情况下,攻击者可直接构造特定请求开启特定配置,并最终造成SSRF或文件读取漏洞。目前互联网已公开漏洞poc,建议相关用户及时采取措施阻止攻击。fofa查询app="APACHE-Solr"影响范围ApacheSolr所有版本漏洞复现首先访问,获取实
- ffmpeg ,结合 SSRF任意文件读取漏洞
德古拉的杂货铺
渗透测试篇ffmpeg安全漏洞视频处理
ffmpeg,结合SSRF任意文件读取漏洞前言一、ffmpeg是什么?FFmpeg背景知识简介HLS(HTTPLiveStreaming)二、使用步骤CentOS7下的安装三、ffmpeg任意文件读取漏洞复现环境搭建漏洞利用修复建议前言初衷:最近空闲,想通过vulhub靶场进行学习,猛的看到ffmpeg,很熟悉。在2018年开发的堡垒机时,曾经用过它进行视频文件的处理。于是决定从它开始练习写博客。
- CVE-2017-15715 apache httpd换行解析漏洞复现
afei00123
#漏洞复现
目录1.漏洞概述2.影响版本3.漏洞等级4.漏洞复现4.1Vulhub搭建漏洞环境4.2CVE-2017-15715换行解析漏洞利用5.漏洞修复1.漏洞概述在Apachehttpd2.4.0至2.4.29中,在中指定的表达式可以将'$'与恶意文件名中的换行符匹配,而不是仅匹配文件名的末尾。该漏洞的出现是由于apache在修复后缀名解析漏洞时,用正则来匹配后缀。在解析php时,xxx.php\x0A
- Apache Solr stream.url 存在任意文件读取漏洞
sublime88
漏洞复现solrapacheweb安全
文章目录ApacheSolrstream.url存在任意文件读取漏洞1.ApacheSolr简介2.漏洞描述3.影响版本4.fofa查询语句5.漏洞复现6.POC&EXP7.整改意见8.往期回顾ApacheSolrstream.url存在任意文件读取漏洞1.ApacheSolr简介微信公众号搜索:南风漏洞复现文库该文章南风漏洞复现文库公众号首发Solr采用Java5开发,是建立在ApacheLuc
- weblogic漏洞复现(CVE-2020-2555)
墨痕诉清风
渗透常识研究python开发语言
漏洞环境:fofa自己找,server=weblogicport=7001一、漏洞简介该反序列化的gadget存在与coherence包中。具体可以见分析构造chain类似于common-collection的chain,可以照葫芦画瓢。mvn好像不能下载coherence包,很奇怪,直接下jar包就行。反序列化的对象,通过t3发送给weblogic即可。所以,这个只是生成payload的工具二、
- 【漏洞复现】Palo Alto Networks Expedition 远程命令执行漏洞(CVE-2024-9463)
点燃银河尽头的篝火(●'◡'●)
#漏洞复现网络PaloAltoExpedition远程命令执行漏洞复现web安全漏洞
免责声明请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任。工具来自网络,安全性自测,如有侵权请联系删除。本次测试仅供学习使用,如若非法他用,与平台和本文作者无关,需自行负责!!!0x01产品介绍PaloAltoNetworksExpedition是一款强大的工具,帮助用户有效地迁移和优化网络安全策略
- PaloAlto-Expedition OS命令注入漏洞复现(CVE-2025-0107)
iSee857
漏洞复现安全web安全
免责申明:本文所描述的漏洞及其复现步骤仅供网络安全研究与教育目的使用。任何人不得将本文提供的信息用于非法目的或未经授权的系统测试。作者不对任何由于使用本文信息而导致的直接或间接损害承担责任。如涉及侵权,请及时与我们联系,我们将尽快处理并删除相关内容。前言:我们建立了一个更多,更全的知识库。每日追踪最新的安全漏洞并提供批量性检测脚本。更多详情:https://pc.fenchuan8.com/#/i
- CVE-2020-17519源码分析与漏洞复现(Flink 任意文件读取)
漏洞概览漏洞名称:ApacheFlinkRESTAPI任意文件读取漏洞CVE编号:CVE-2020-17519CVSS评分:7.5影响版本:ApacheFlink1.11.0、1.11.1、1.11.2修复版本:≥1.11.3或≥1.12.0漏洞类型:路径遍历(PathTraversal)根本原因:JobManager的REST接口未对用户输入路径进行规范化校验,导致通过双重URL编码(%252f
- Emlog Pro 任意文件上传漏洞(CVE-2023-44974)
Point13reak
CVE复现网络安全安全系统安全web安全
靶机地址前来挑战!应急响应靶机训练-Web1漏洞原理/admin/plugin.php中存在任意文件上传漏洞使得攻击者能够通过上传构建的PHP文件来执行任意代码漏洞利用webshell上传(PHP木马)影响版本EmlogPro2.2.0修复方案更新当前系统或软件至最新版漏洞复现&#
- CVE-2017-12629-XXE源码分析与漏洞复现
网安spinage
Vulhub靶场web安全java网络安全漏洞solrxxe
漏洞概述漏洞名称:ApacheSolrXML实体注入漏洞(XXE)漏洞编号:CVE-2017-12629CVSS评分:9.8影响版本:ApacheSolr&defType=xmlparserSolr路由到XmlQParserPlugin处理请求:publicQParsercreateParser(Stringqstr,SolrParamslocalParams,SolrParamsparams,S
- 服务攻防-中间件安全&CVE 复现&Apache&Tomcat&Nginx
@Camelus
渗透与攻防apache中间件安全web安全安全威胁分析
目录前言:(一)Nginx-文件解析&命令执行1、Nginx文件解析漏洞复现1.1nginx解析漏洞(CVE-2013-4547)1.2Nginx文件解析漏洞复现1.3Nginx任意代码执行漏洞(CVE-2021-23017)Nginx1.1.9DNS解析漏洞(CVE-2021-23017)修复日记_迷路小书虫的技术博客_51CTO博客(二)Apache-RCE&目录遍历&文件解析1、Apache
- MS16-075 漏洞 复现过程
浩策
提权&&权限维持web安全安全网络安全安全架构密码学
目录一、MS16-075漏洞概述二、为什么称之为“甜土豆”提权?三、MS16-075漏洞复现步骤1.下载POC和EXP2.编译与准备EXP3.利用MS16-075漏洞提权(本地执行)4.将POC转换为CobaltStrikePayload四、通过CobaltStrike进行提权的详细步骤1.上传工具至目标主机2.执行提权命令3.利用CS内置模块提权五、提权成功后的进一步操作总结一、MS16-075
- CNVD-2025-04094:Ollama未授权访问漏洞复现
gaynell
漏洞复现安全系统安全网络安全语言模型
文章目录CNVD-2025-04094:Ollama未授权访问漏洞复现0x01前言0x02漏洞描述0x03影响版本0x04漏洞环境0x05漏洞复现1.访问漏洞环境2.复现0x06修复建议CNVD-2025-04094:Ollama未授权访问漏洞复现0x01前言免责声明:请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负
- vulfocus漏洞学习——redis 未授权访问 (CNVD-2015-07557)
c30%00
学习
目录一、漏洞介绍二、影响版本三、漏洞复现1.使用脚本四、漏洞原理一、漏洞介绍Redis是一个免费开源的键值存储数据库,数据默认存到内存中,用简单的C语言编写,能通过网络访问。该漏洞的成因是:在默认情况下,Redis会绑定到0.0.0.0:6379,这意味着Redis会直接暴露到公网上,而此时如果又没有设置密码认证,会导致任意用户在可以访问到目标服务器的情况下未授权访问Redis并读取Redis的数
- Apache Apisix 安全漏洞(CVE-2020-13945)
星球守护者
漏洞复现apachejava安全
文章目录0x01漏洞介绍0x02影响版本0x03漏洞编号0x04漏洞查询0x05漏洞环境0x06漏洞复现0x07修复建议免责声明摘抄0x01漏洞介绍ApacheApisix是Apache基金会的一个云原生的微服务API网关服务。该软件基于OpenResty和etcd来实现,具备动态路由和插件热加载,适合微服务体系下的API管理。ApacheAPISIX存在安全漏洞,该漏洞源于用户启用了管理API并
- WordPress_Relevanssi Sql注入漏洞复现(CVE-2025-4396)
iSee857
漏洞复现安全web安全
免责申明:本文所描述的漏洞及其复现步骤仅供网络安全研究与教育目的使用。任何人不得将本文提供的信息用于非法目的或未经授权的系统测试。作者不对任何由于使用本文信息而导致的直接或间接损害承担责任。如涉及侵权,请及时与我们联系,我们将尽快处理并删除相关内容。前言:我们建立了一个更多,更全的知识库。每日追踪最新的安全漏洞并提供批量性检测脚本。更多详情:https://pc.fenchuan8.com/#/i
- Ruby On Rails代码执行漏洞(CVE-2020-8163)技术分析与研判防护
东方隐侠安全团队-千里
【一】病毒木马·防护处置·蓝队rubyonrails安全web安全
漏洞简介RubyonRails是Rails团队的一套基于Ruby语言的开源Web应用框架。RubyonRails5.0.1之前版本存在代码注入漏洞。远程攻击者可利用该漏洞发送特制请求执行任意代码。影响范围Rails<5.0.1环境搭建参考https://github.com/QianliZLP/CVE-2020-8163-即可漏洞复现Exp:exploit.rb#
- WordPress_depicter Sql注入漏洞复现(CVE-2025-2011)
iSee857
漏洞复现安全web安全
免责申明:本文所描述的漏洞及其复现步骤仅供网络安全研究与教育目的使用。任何人不得将本文提供的信息用于非法目的或未经授权的系统测试。作者不对任何由于使用本文信息而导致的直接或间接损害承担责任。如涉及侵权,请及时与我们联系,我们将尽快处理并删除相关内容。前言:我们建立了一个更多,更全的知识库。每日追踪最新的安全漏洞并提供批量性检测脚本。更多详情:https://pc.fenchuan8.com/#/i
- SysAid On-Prem XML注入漏洞复现(CVE-2025-2776)
iSee857
漏洞复现xml安全web安全
免责申明:本文所描述的漏洞及其复现步骤仅供网络安全研究与教育目的使用。任何人不得将本文提供的信息用于非法目的或未经授权的系统测试。作者不对任何由于使用本文信息而导致的直接或间接损害承担责任。如涉及侵权,请及时与我们联系,我们将尽快处理并删除相关内容。前言:我们建立了一个更多,更全的知识库。每日追踪最新的安全漏洞并提供批量性检测脚本。更多详情:https://pc.fenchuan8.com/#/i
- WordPress MasterStudy LMS插件 SQL注入漏洞复现(CVE-2024-1512)
0xSecl
漏洞复现v1sql安全web安全
0x01产品简介WordPress和WordPressplugin都是WordPress基金会的产品。WordPress是一套使用PHP语言开发的博客平台。该平台支持在PHP和MySQL的服务器上架设个人博客网站。WordPressplugin是一个应用插件。0x02漏洞概述WordPressPluginMasterStudyLMS3.2.5版本及之前版本存在安全漏洞,该漏洞源于对用户提供的参数转
- Tomcat DOS漏洞复现(CVE-2025-31650)
iSee857
漏洞复现tomcatjava安全web安全
免责申明:本文所描述的漏洞及其复现步骤仅供网络安全研究与教育目的使用。任何人不得将本文提供的信息用于非法目的或未经授权的系统测试。作者不对任何由于使用本文信息而导致的直接或间接损害承担责任。如涉及侵权,请及时与我们联系,我们将尽快处理并删除相关内容。前言:我们建立了一个更多,更全的知识库。每日追踪最新的安全漏洞并提供批量性检测脚本。更多详情:https://pc.fenchuan8.com/#/i
- 【漏洞复现】Apache Tomcat 远程代码执行(CVE-2025-24813)
李火火安全阁
漏洞复现Web安全apachetomcat
文章目录前言免责声明一、漏洞描述二、影响范围三、利用条件四、环境配置五、漏洞复现六、修复方式前言该漏洞可导致非默认配置的Tomcat被攻击者进行利用,使用反序列化的内容实现RCE免责声明在网络安全领域,技术文章应谨慎使用,遵守法律法规,严禁非法网络活动。未经授权,不得利用文中信息进行入侵,造成的任何后果,由使用者自行承担,本文作者不负责。提供的工具仅限学习使用,严禁外用。一、漏洞描述CVE-202
- Ivanti Connect Secure 堆栈溢出致远程代码执行漏洞复现(CVE-2025-0282)(附脚本)
iSee857
漏洞复现安全web安全
0x01产品描述:IvantiConnectSecure,以前称为PulseConnectSecure,是一款提供SSLVPN解决方案的产品。它允许远程用户通过一个安全的通道访问企业资源,确保数据在传输过程中的加密和安全。IvantiConnectSecure是由PulseSecure公司开发的,该公司后来被Ivanti收购,因此产品名称发生了变化。IvantiPolicySecure则是一个网络
- CNVD-2020-10487复现(Apache Tomcat文件包含漏洞)
afei00123
#漏洞复现
目录1.漏洞概述2.影响范围3.风险等级4.漏洞复现4.1.tomcat环境搭建4.2.POC利用测试5.POC分析6.配合文件上传漏洞拿shell7.修复建议8.漏洞链接1.漏洞概述2020年2月20日,国家信息安全漏洞共享平台(CNVD)发布了ApacheTomcat文件包含漏洞(CNVD-2020-10487/CVE-2020-1938)。该漏洞是由于TomcatAJP协议存在缺陷造成的。攻
- Apache-OFBiz授权不当导致RCE (CVE-2024-38856)
iSee857
漏洞复现apache
0x01漏洞描述:ApacheOFBiz18.12.14之前版本存在命令执行漏洞,该漏洞源于ControlServlet和RequestHandler函数,在处理请求中存在授权错误,导致未经身份验证的远程攻击者通过构造特殊URL来覆盖最终的渲染视图,从而执行任意代码0x02影响版本:ApacheOFBiz<=18.12.140x03搜索语句:app="Apache_OFBiz"0x04漏洞复现:P
- 【漏洞复现】Apache OFBiz 路径遍历导致RCE漏洞(CVE-2024-36104)
从不学安全
漏洞复现安全
0x01产品简介ApacheOFBiz是一个功能强大、易于定制和扩展的开源ERP系统,适用于各种类型的企业。通过利用最新的技术标准和开源项目,ApacheOFBiz为企业提供了一个高效、稳定、灵活的电子商务平台解决方案。0x02漏洞概述ApacheOFBiz18.12.14之前版本存在命令执行漏洞,该漏洞源于org.apache.ofbiz.webapp.control.ControlFilter
- CVE-2024-36104 Apache OFBiz路径遍历RCE漏洞复现(附POC)
CatalyzeSec
web安全安全
漏洞描述Apache_OFBiz是一套基于通用架构的企业应用程序,使用通用数据,逻辑和流程组件。应用程序的松散耦合特性使这些组件易于理解,扩展和定制。由于对HTTP请求URL中的特殊字符(如;、%2e)限制不当,威胁者可构造恶意请求利用该漏洞,成功利用可能导致远程代码执行。影响版本ApacheOFBiz<18.12.14FOFAapp="Apache_OFBiz"POCPOST/webtools/
- 异常的核心类Throwable
无量
java源码异常处理exception
java异常的核心是Throwable,其他的如Error和Exception都是继承的这个类 里面有个核心参数是detailMessage,记录异常信息,getMessage核心方法,获取这个参数的值,我们可以自己定义自己的异常类,去继承这个Exception就可以了,方法基本上,用父类的构造方法就OK,所以这么看异常是不是很easy
package com.natsu;
- mongoDB 游标(cursor) 实现分页 迭代
开窍的石头
mongodb
上篇中我们讲了mongoDB 中的查询函数,现在我们讲mongo中如何做分页查询
如何声明一个游标
var mycursor = db.user.find({_id:{$lte:5}});
迭代显示游标数
- MySQL数据库INNODB 表损坏修复处理过程
0624chenhong
tomcatmysql
最近mysql数据库经常死掉,用命令net stop mysql命令也无法停掉,关闭Tomcat的时候,出现Waiting for N instance(s) to be deallocated 信息。查了下,大概就是程序没有对数据库连接释放,导致Connection泄露了。因为用的是开元集成的平台,内部程序也不可能一下子给改掉的,就验证一下咯。启动Tomcat,用户登录系统,用netstat -
- 剖析如何与设计人员沟通
不懂事的小屁孩
工作
最近做图烦死了,不停的改图,改图……。烦,倒不是因为改,而是反反复复的改,人都会死。很多需求人员不知该如何与设计人员沟通,不明白如何使设计人员知道他所要的效果,结果只能是沟通变成了扯淡,改图变成了应付。
那应该如何与设计人员沟通呢?
我认为设计人员与需求人员先天就存在语言障碍。对一个合格的设计人员来说,整天玩的都是点、线、面、配色,哪种构图看起来协调;哪种配色看起来合理心里跟明镜似的,
- qq空间刷评论工具
换个号韩国红果果
JavaScript
var a=document.getElementsByClassName('textinput');
var b=[];
for(var m=0;m<a.length;m++){
if(a[m].getAttribute('placeholder')!=null)
b.push(a[m])
}
var l
- S2SH整合之session
灵静志远
springAOPstrutssession
错误信息:
Caused by: org.springframework.beans.factory.BeanCreationException: Error creating bean with name 'cartService': Scope 'session' is not active for the current thread; consider defining a scoped
- xmp标签
a-john
标签
今天在处理数据的显示上遇到一个问题:
var html = '<li><div class="pl-nr"><span class="user-name">' + user
+ '</span>' + text + '</div></li>';
ulComme
- Ajax的常用技巧(2)---实现Web页面中的级联菜单
aijuans
Ajax
在网络上显示数据,往往只显示数据中的一部分信息,如文章标题,产品名称等。如果浏览器要查看所有信息,只需点击相关链接即可。在web技术中,可以采用级联菜单完成上述操作。根据用户的选择,动态展开,并显示出对应选项子菜单的内容。 在传统的web实现方式中,一般是在页面初始化时动态获取到服务端数据库中对应的所有子菜单中的信息,放置到页面中对应的位置,然后再结合CSS层叠样式表动态控制对应子菜单的显示或者隐
- 天-安-门,好高
atongyeye
情感
我是85后,北漂一族,之前房租1100,因为租房合同到期,再续,房租就要涨150。最近网上新闻,地铁也要涨价。算了一下,涨价之后,每次坐地铁由原来2块变成6块。仅坐地铁费用,一个月就要涨200。内心苦痛。
晚上躺在床上一个人想了很久,很久。
我生在农
- android 动画
百合不是茶
android透明度平移缩放旋转
android的动画有两种 tween动画和Frame动画
tween动画;,透明度,缩放,旋转,平移效果
Animation 动画
AlphaAnimation 渐变透明度
RotateAnimation 画面旋转
ScaleAnimation 渐变尺寸缩放
TranslateAnimation 位置移动
Animation
- 查看本机网络信息的cmd脚本
bijian1013
cmd
@echo 您的用户名是:%USERDOMAIN%\%username%>"%userprofile%\网络参数.txt"
@echo 您的机器名是:%COMPUTERNAME%>>"%userprofile%\网络参数.txt"
@echo ___________________>>"%userprofile%\
- plsql 清除登录过的用户
征客丶
plsql
tools---preferences----logon history---history 把你想要删除的删除
--------------------------------------------------------------------
若有其他凝问或文中有错误,请及时向我指出,
我好及时改正,同时也让我们一起进步。
email : binary_spac
- 【Pig一】Pig入门
bit1129
pig
Pig安装
1.下载pig
wget http://mirror.bit.edu.cn/apache/pig/pig-0.14.0/pig-0.14.0.tar.gz
2. 解压配置环境变量
如果Pig使用Map/Reduce模式,那么需要在环境变量中,配置HADOOP_HOME环境变量
expor
- Java 线程同步几种方式
BlueSkator
volatilesynchronizedThredLocalReenTranLockConcurrent
为何要使用同步? java允许多线程并发控制,当多个线程同时操作一个可共享的资源变量时(如数据的增删改查), 将会导致数据不准确,相互之间产生冲突,因此加入同步锁以避免在该线程没有完成操作之前,被其他线程的调用, 从而保证了该变量的唯一性和准确性。 1.同步方法&
- StringUtils判断字符串是否为空的方法(转帖)
BreakingBad
nullStringUtils“”
转帖地址:http://www.cnblogs.com/shangxiaofei/p/4313111.html
public static boolean isEmpty(String str)
判断某字符串是否为空,为空的标准是 str==
null
或 str.length()==
0
- 编程之美-分层遍历二叉树
bylijinnan
java数据结构算法编程之美
import java.util.ArrayList;
import java.util.LinkedList;
import java.util.List;
public class LevelTraverseBinaryTree {
/**
* 编程之美 分层遍历二叉树
* 之前已经用队列实现过二叉树的层次遍历,但这次要求输出换行,因此要
- jquery取值和ajax提交复习记录
chengxuyuancsdn
jquery取值ajax提交
// 取值
// alert($("input[name='username']").val());
// alert($("input[name='password']").val());
// alert($("input[name='sex']:checked").val());
// alert($("
- 推荐国产工作流引擎嵌入式公式语法解析器-IK Expression
comsci
java应用服务器工作Excel嵌入式
这个开源软件包是国内的一位高手自行研制开发的,正如他所说的一样,我觉得它可以使一个工作流引擎上一个台阶。。。。。。欢迎大家使用,并提出意见和建议。。。
----------转帖---------------------------------------------------
IK Expression是一个开源的(OpenSource),可扩展的(Extensible),基于java语言
- 关于系统中使用多个PropertyPlaceholderConfigurer的配置及PropertyOverrideConfigurer
daizj
spring
1、PropertyPlaceholderConfigurer
Spring中PropertyPlaceholderConfigurer这个类,它是用来解析Java Properties属性文件值,并提供在spring配置期间替换使用属性值。接下来让我们逐渐的深入其配置。
基本的使用方法是:(1)
<bean id="propertyConfigurerForWZ&q
- 二叉树:二叉搜索树
dieslrae
二叉树
所谓二叉树,就是一个节点最多只能有两个子节点,而二叉搜索树就是一个经典并简单的二叉树.规则是一个节点的左子节点一定比自己小,右子节点一定大于等于自己(当然也可以反过来).在树基本平衡的时候插入,搜索和删除速度都很快,时间复杂度为O(logN).但是,如果插入的是有序的数据,那效率就会变成O(N),在这个时候,树其实变成了一个链表.
tree代码:
- C语言字符串函数大全
dcj3sjt126com
cfunction
C语言字符串函数大全
函数名: stpcpy
功 能: 拷贝一个字符串到另一个
用 法: char *stpcpy(char *destin, char *source);
程序例:
#include <stdio.h>
#include <string.h>
int main
- 友盟统计页面技巧
dcj3sjt126com
技巧
在基类调用就可以了, 基类ViewController示例代码
-(void)viewWillAppear:(BOOL)animated
{
[super viewWillAppear:animated];
[MobClick beginLogPageView:[NSString stringWithFormat:@"%@",self.class]];
- window下在同一台机器上安装多个版本jdk,修改环境变量不生效问题处理办法
flyvszhb
javajdk
window下在同一台机器上安装多个版本jdk,修改环境变量不生效问题处理办法
本机已经安装了jdk1.7,而比较早期的项目需要依赖jdk1.6,于是同时在本机安装了jdk1.6和jdk1.7.
安装jdk1.6前,执行java -version得到
C:\Users\liuxiang2>java -version
java version "1.7.0_21&quo
- Java在创建子类对象的同时会不会创建父类对象
happyqing
java创建子类对象父类对象
1.在thingking in java 的第四版第六章中明确的说了,子类对象中封装了父类对象,
2."When you create an object of the derived class, it contains within it a subobject of the base class. This subobject is the sam
- 跟我学spring3 目录贴及电子书下载
jinnianshilongnian
spring
一、《跟我学spring3》电子书下载地址:
《跟我学spring3》 (1-7 和 8-13) http://jinnianshilongnian.iteye.com/blog/pdf
跟我学spring3系列 word原版 下载
二、
源代码下载
最新依
- 第12章 Ajax(上)
onestopweb
Ajax
index.html
<!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd">
<html xmlns="http://www.w3.org/
- BI and EIM 4.0 at a glance
blueoxygen
BO
http://www.sap.com/corporate-en/press.epx?PressID=14787
有机会研究下EIM家族的两个新产品~~~~
New features of the 4.0 releases of BI and EIM solutions include:
Real-time in-memory computing –
- Java线程中yield与join方法的区别
tomcat_oracle
java
长期以来,多线程问题颇为受到面试官的青睐。虽然我个人认为我们当中很少有人能真正获得机会开发复杂的多线程应用(在过去的七年中,我得到了一个机会),但是理解多线程对增加你的信心很有用。之前,我讨论了一个wait()和sleep()方法区别的问题,这一次,我将会讨论join()和yield()方法的区别。坦白的说,实际上我并没有用过其中任何一个方法,所以,如果你感觉有不恰当的地方,请提出讨论。
&nb
- android Manifest.xml选项
阿尔萨斯
Manifest
结构
继承关系
public final class Manifest extends Objectjava.lang.Objectandroid.Manifest
内部类
class Manifest.permission权限
class Manifest.permission_group权限组
构造函数
public Manifest () 详细 androi
- Oracle实现类split函数的方
zhaoshijie
oracle
关键字:Oracle实现类split函数的方
项目里需要保存结构数据,批量传到后他进行保存,为了减小数据量,子集拼装的格式,使用存储过程进行保存。保存的过程中需要对数据解析。但是oracle没有Java中split类似的函数。从网上找了一个,也补全了一下。
CREATE OR REPLACE TYPE t_split_100 IS TABLE OF VARCHAR2(100);
cr