Spring OAuth2--密码模式 实战
1.OAuth2协议简介:
OAuth是一种用来规范令牌(Token)发放的授权机制,目前最新版本为2.0,不兼容1.0,主要有四种授权模式:授权码模式、简化模式、密码模式和客户端模式。我这边的前端系统是通过用户名和密码来登录系统的,所以这里只介绍密码模式
2.密码模式简介:
在密码模式中,用户向客户端提供用户名和密码,客户端通过用户名和密码到认证服务器获取令牌。流程如下:

如上图所示,密码模式包含了三个步骤:
(A)用户访问客户端,提供URI连接包含用户名和密码信息给授权服务器
(B)授权服务器对客户端进行身份验证
(C)授权通过,返回access_token给客户端
3.搭建服务
3.1 pom.xml文件(SpringBoot+SpringSecurity+OAuth2+Redis)
<?xml version="1.0" encoding="UTF-8"?>
<project xmlns="http://maven.apache.org/POM/4.0.0" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0</modelVersion>
<parent>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-parent</artifactId>
<version>2.1.6.RELEASE</version>
<relativePath/> <!-- lookup parent from repository -->
</parent>
<groupId>demo</groupId>
<artifactId>security</artifactId>
<version>0.0.1-SNAPSHOT</version>
<name>security</name>
<description>Demo project for Spring Boot</description>
<properties>
<java.version>1.8</java.version>
<spring-cloud.version>Greenwich.SR1</spring-cloud.version>
</properties>
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.cloud</groupId>
<artifactId>spring-cloud-starter-oauth2</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.cloud</groupId>
<artifactId>spring-cloud-starter-security</artifactId>
</dependency>
<dependency>
<groupId>org.apache.commons</groupId>
<artifactId>commons-lang3</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-data-redis</artifactId>
</dependency>
<dependency>
<groupId>io.jsonwebtoken</groupId>
<artifactId>jjwt</artifactId>
<version>0.9.1</version>
</dependency>
</dependencies>
<dependencyManagement>
<dependencies>
<dependency>
<groupId>org.springframework.cloud</groupId>
<artifactId>spring-cloud-dependencies</artifactId>
<version>${
spring-cloud.version}</version>
<type>pom</type>
<scope>import</scope>
</dependency>
</dependencies>
</dependencyManagement>
<build>
<plugins>
<plugin>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-maven-plugin</artifactId>
</plugin>
</plugins>
</build>
</project>
3.2 配置文件(你们需要换成自己的redis配置,用来存放认证信息)
spring:
redis:
host: 127.0.0.1
port: 6379
password: KCl9HfqbVnhQ5c3n
database: 0
3.3 我们需要定义一个WebSecurity类型的安全配置类
package com.example.demo.security.config;
import com.example.demo.security.service.UserDetailService;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.context.annotation.Bean;
import org.springframework.core.annotation.Order;
import org.springframework.security.authentication.AuthenticationManager;
import org.springframework.security.config.annotation.authentication.builders.AuthenticationManagerBuilder;
import org.springframework.security.config.annotation.web.builders.HttpSecurity;
import org.springframework.security.config.annotation.web.configuration.EnableWebSecurity;
import org.springframework.security.config.annotation.web.configuration.WebSecurityConfigurerAdapter;
import org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder;
import org.springframework.security.crypto.password.PasswordEncoder;
@EnableWebSecurity
@Order(2)
public class SecurityConfig extends WebSecurityConfigurerAdapter {
@Autowired
private UserDetailService userDetailService;
@Bean
public PasswordEncoder passwordEncoder() {
return new BCryptPasswordEncoder();
}
@Bean
@Override
public AuthenticationManager authenticationManagerBean() throws Exception {
return super.authenticationManagerBean();
}
@Override
protected void configure(HttpSecurity http) throws Exception {
http.requestMatchers()
.antMatchers("/oauth/**")
.and()
.authorizeRequests()
.antMatchers("/oauth/**").authenticated()
.and()
.csrf().disable();
}
@Override
protected void configure(AuthenticationManagerBuilder auth) throws Exception {
auth.userDetailsService(userDetailService).passwordEncoder(passwordEncoder());
}
}
该类继承了WebSecurityConfigurerAdapter适配器,重写了几个方法,并且使用@EnableWebSecurity注解标注,开启了和Web相关的安全配置。
上面代码中,我们首先注入了UserDetailService,这个类下面会介绍到,这里先略过。
然后我们定义了一个PasswordEncoder类型的Bean,该类是一个接口,定义了几个和密码加密校验相关的方法,这里我们使用的是Spring Security内部实现好的BCryptPasswordEncoder。BCryptPasswordEncoder的特点就是,对于一个相同的密码,每次加密出来的加密串都不同:
public static void main(String[] args) {
String password = "123456";
PasswordEncoder encoder = new BCryptPasswordEncoder();
System.out.println(encoder.encode(password));
System.out.println(encoder.encode(password));
}
$2a$10$TgKIGaJrL8LBFT8bEj8gH.3ctyo1PpSTw4fs4o6RuMOE4R665HdpS
$2a$10$ZEcCOMVVIV5SfoXPXih92uGJfVeaugMr/PydhYnLvsCroS9xWjOIq
我们也可以自己实现PasswordEncoder接口,这里为了方便就直接使用BCryptPasswordEncoder了
接着我们注册了一个authenticationManagerBean,因为密码模式需要使用到这个Bean。
在SecurityConfig 类中,我们还重写了WebSecurityConfigurerAdapter类的configure(HttpSecurity http)方法,其中requestMatchers().antMatchers("/oauth/**")的含义是:SecurityConfig 安全配置类只对/oauth/开头的请求有效。
最后我们重写了configure(AuthenticationManagerBuilder auth)方法,指定了userDetailsService和passwordEncoder
3.4 定义一个资源服务器的配置类
package com.example.demo.security.config;
import org.springframework.context.annotation.Configuration;
import org.springframework.security.config.annotation.web.builders.HttpSecurity;
import org.springframework.security.oauth2.config.annotation.web.configuration.EnableResourceServer;
import org.springframework.security.oauth2.config.annotation.web.configuration.ResourceServerConfigurerAdapter;
@Configuration
@EnableResourceServer
public class ResourceServerConfig extends ResourceServerConfigurerAdapter {
@Override
public void configure(HttpSecurity http) throws Exception {
http.csrf().disable()
.requestMatchers().antMatchers("/**")
.and()
.authorizeRequests()
.antMatchers("/**").authenticated();
}
}
ResourceServerConfig 继承了ResourceServerConfigurerAdapter,并重写了configure(HttpSecurity http)方法,通过requestMatchers().antMatchers("/")的配置表明该安全配置对所有请求都生效。**类上的@EnableResourceServer用于开启资源服务器相关配置。
3.5 SecurityConfig和ResourceServerConfig的区别
上面两个Config配置都是用来拦截请求的,一个只拦截以"/oauth/**"开头的请求,一个拦截所有请求,这两者功能类似,那请求到底先走谁,我们看代码
@Order(100)
public abstract class WebSecurityConfigurerAdapter implements WebSecurityConfigurer {
......
}
@Configuration
public class ResourceServerConfiguration extends WebSecurityConfigurerAdapter implements Ordered {
private int order = 3;
......
}
在Spring中,数字越小,优先级越高,也就是说ResourceServerConfig的优先级要高于SecurityConfig,这也就意味着所有请求都会被ResourceServerConfig过滤器链处理,包括/oauth/开头的请求。这显然不是我们要的效果,我们原本是希望以/oauth/开头的请求由SecurityConfig过滤器链处理,剩下的其他请求由ResourceServerConfig过滤器链处理。
所以我们需要提高SecurityConfig的优先级(增加@Order(2))
@Order(2)
@EnableWebSecurity
public class SecurityConfigextends WebSecurityConfigurerAdapter {
......
}
3.6 定义一个和认证服务器相关的安全配置类
package com.example.demo.security.config;
import com.example.demo.security.service.UserDetailService;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.context.annotation.Bean;
import org.springframework.context.annotation.Configuration;
import org.springframework.context.annotation.Primary;
import org.springframework.data.redis.connection.RedisConnectionFactory;
import org.springframework.security.authentication.AuthenticationManager;
import org.springframework.security.crypto.password.PasswordEncoder;
import org.springframework.security.oauth2.config.annotation.configurers.ClientDetailsServiceConfigurer;
import org.springframework.security.oauth2.config.annotation.web.configuration.AuthorizationServerConfigurerAdapter;
import org.springframework.security.oauth2.config.annotation.web.configuration.EnableAuthorizationServer;
import org.springframework.security.oauth2.config.annotation.web.configurers.AuthorizationServerEndpointsConfigurer;
import org.springframework.security.oauth2.provider.token.DefaultTokenServices;
import org.springframework.security.oauth2.provider.token.TokenStore;
import org.springframework.security.oauth2.provider.token.store.redis.RedisTokenStore;
@Configuration
@EnableAuthorizationServer
public class AuthorizationServerConfig extends AuthorizationServerConfigurerAdapter {
@Autowired
private AuthenticationManager authenticationManager;
@Autowired
private RedisConnectionFactory redisConnectionFactory;
@Autowired
private UserDetailService userDetailService;
@Autowired
private PasswordEncoder passwordEncoder;
@Override
public void configure(ClientDetailsServiceConfigurer clients) throws Exception {
clients.inMemory()
.withClient("auth")
.secret(passwordEncoder.encode("123456"))
.authorizedGrantTypes("password", "refresh_token")
.scopes("all");
}
@Override
public void configure(AuthorizationServerEndpointsConfigurer endpoints) {
endpoints.tokenStore(tokenStore())
.userDetailsService(userDetailService)
.authenticationManager(authenticationManager)
.tokenServices(defaultTokenServices());
}
/**
* 认证服务器生成的令牌将被存储到Redis中
* @return
*/
@Bean
public TokenStore tokenStore() {
return new RedisTokenStore(redisConnectionFactory);
}
@Primary
@Bean
public DefaultTokenServices defaultTokenServices() {
DefaultTokenServices tokenServices = new DefaultTokenServices();
tokenServices.setTokenStore(tokenStore());
// 开启刷新令牌的支持
tokenServices.setSupportRefreshToken(true);
// 令牌有效时间为60 * 60 * 24
tokenServices.setAccessTokenValiditySeconds(60 * 60 * 24);
// 刷新令牌有效时间为60 * 60 * 24 * 7秒
tokenServices.setRefreshTokenValiditySeconds(60 * 60 * 24 * 7);
return tokenServices;
}
}
AuthorizationServerConfig继承AuthorizationServerConfigurerAdapter适配器,使用@EnableAuthorizationServer注解标注,开启认证服务器相关配置
AuthorizationServerConfig配置类中重点需要介绍的是configure(ClientDetailsServiceConfigurer clients)方法。该方法主要配置了:
客户端从认证服务器获取令牌的时候,必须使用client_id为auth,client_secret为123456的标识来获取;
该client_id支持password模式获取令牌,并且可以通过refresh_token来获取新的令牌;
在获取client_id为auth的令牌的时候,scope只能指定为all,否则将获取失败;
3.7 在定义好这三个配置类后,我们还需要定义一个用于校验用户名密码的类,也就是上面提到的UserDetailService,
package com.example.demo.security.service;
import com.example.demo.security.entity.AuthUser;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.security.core.authority.AuthorityUtils;
import org.springframework.security.core.userdetails.User;
import org.springframework.security.core.userdetails.UserDetails;
import org.springframework.security.core.userdetails.UserDetailsService;
import org.springframework.security.core.userdetails.UsernameNotFoundException;
import org.springframework.security.crypto.password.PasswordEncoder;
import org.springframework.stereotype.Service;
@Service
public class UserDetailService implements UserDetailsService {
@Autowired
private PasswordEncoder passwordEncoder;
@Override
public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException {
AuthUser user = new AuthUser();
user.setUsername(username);
user.setPassword(this.passwordEncoder.encode("123456"));
return new User(username, user.getPassword(), user.isEnabled(),
user.isAccountNonExpired(), user.isCredentialsNonExpired(),
user.isAccountNonLocked(), AuthorityUtils.commaSeparatedStringToAuthorityList("user:add"));
}
}
该类主要就是重写loadUserByUsername()方法,去数据库查询有没有当前用户,并且返回一个UserDetails对象,该对象也是一个接口,包含一些用于描述用户信息的方法,源码如下:
//
// Source code recreated from a .class file by IntelliJ IDEA
// (powered by Fernflower decompiler)
//
package org.springframework.security.core.userdetails;
import java.io.Serializable;
import java.util.Collection;
import org.springframework.security.core.GrantedAuthority;
public interface UserDetails extends Serializable {
// 获取用户包含的权限,返回权限集合,权限是一个继承了GrantedAuthority的对象
Collection getAuthorities();
String getPassword();
String getUsername();
// 判断账户是否未过期,未过期返回true反之返回false
boolean isAccountNonExpired();
// 判断账户是否未锁定
boolean isAccountNonLocked();
// 判断用户凭证是否没过期,即密码是否未过期
boolean isCredentialsNonExpired();
// 判断用户是否可用
boolean isEnabled();
}
3.8 实际开发中,我们会直接用系统的用户对象,我这边自定义一个对象AuthUser(也可以直接使用Spring Security提供的UserDetails接口实现类)
package com.example.demo.security.entity;
import java.io.Serializable;
public class AuthUser implements Serializable {
private static final long serialVersionUID = -1748289340320186418L;
private String username;
private String password;
private boolean accountNonExpired = true;
private boolean accountNonLocked= true;
private boolean credentialsNonExpired= true;
private boolean enabled= true;
public static long getSerialVersionUID() {
return serialVersionUID;
}
public String getUsername() {
return username;
}
public void setUsername(String username) {
this.username = username;
}
public String getPassword() {
return password;
}
public void setPassword(String password) {
this.password = password;
}
public boolean isAccountNonExpired() {
return accountNonExpired;
}
public void setAccountNonExpired(boolean accountNonExpired) {
this.accountNonExpired = accountNonExpired;
}
public boolean isAccountNonLocked() {
return accountNonLocked;
}
public void setAccountNonLocked(boolean accountNonLocked) {
this.accountNonLocked = accountNonLocked;
}
public boolean isCredentialsNonExpired() {
return credentialsNonExpired;
}
public void setCredentialsNonExpired(boolean credentialsNonExpired) {
this.credentialsNonExpired = credentialsNonExpired;
}
public boolean isEnabled() {
return enabled;
}
public void setEnabled(boolean enabled) {
this.enabled = enabled;
}
}
3.9 最后写一个Controller,用来验证我们的拦截是否生效(下面三个类都需要)
package com.example.demo.security.controller;
import com.example.demo.security.entity.Response;
import com.example.demo.security.exception.AuthException;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.security.oauth2.provider.token.ConsumerTokenServices;
import org.springframework.util.StringUtils;
import org.springframework.web.bind.annotation.DeleteMapping;
import org.springframework.web.bind.annotation.GetMapping;
import org.springframework.web.bind.annotation.RestController;
import javax.servlet.http.HttpServletRequest;
import java.security.Principal;
@RestController
public class SecurityController {
@Autowired
private ConsumerTokenServices consumerTokenServices;
@GetMapping("oauth/test")
public String testOauth() {
return "oauth";
}
@GetMapping("getUserInfo")
public Principal currentUser(Principal principal) {
return principal;
}
@DeleteMapping("loginOut")
public Response loginOut(HttpServletRequest request) throws AuthException {
String authorization = request.getHeader("Authorization");
String token = StringUtils.replace(authorization, "bearer ", "");
Response response = new Response();
if (!consumerTokenServices.revokeToken(token)) {
throw new AuthException("退出登录失败");
}
return response.message("退出登录成功");
}
}
Response类:
package com.example.demo.security.entity;
import java.util.HashMap;
public class Response extends HashMap<String, Object> {
private static final long serialVersionUID = -8713837118340960775L;
public Response message(String message) {
this.put("message", message);
return this;
}
public Response data(Object data) {
this.put("data", data);
return this;
}
@Override
public Response put(String key, Object value) {
super.put(key, value);
return this;
}
public String getMessage() {
return String.valueOf(get("message"));
}
public Object getData() {
return get("data");
}
}
异常类:
package com.example.demo.security.exception;
public class AuthException extends Exception{
private static final long serialVersionUID = -6916154462432027437L;
public AuthException(String message){
super(message);
}
}
4.Postman测试
4.1 使用PostMan发送 localhost:8080/oauth/token POST请求,请求参数如下所示:
grant_type填password,表示密码模式,然后填写用户名和密码,根据我们定义的UserDetailService逻辑,这里用户名随便填,密码必须为123456。
一定要在请求头中配置Authorization信息,否则请求将返回401
值为Basic加空格加client_id:client_secret(就是在AuthorizationServerConfig类configure(ClientDetailsServiceConfigurer clients)方法中定义的client和secret)经过base64加密后的值
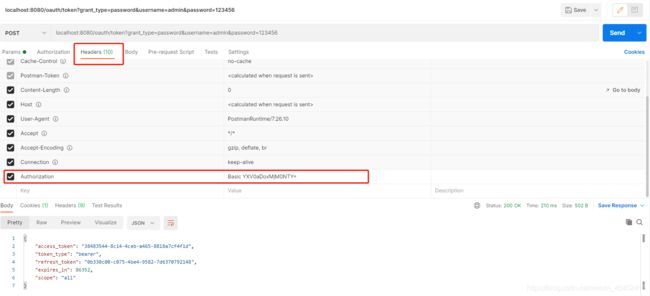
转换base64连接地址
4.2 使用PostMan发送 localhost:8080/getUserInfo GET请求,先不带令牌看看返回什么:

上面返回401异常,下面我们在请求头中添加如下圈红的内容,成功返回数据
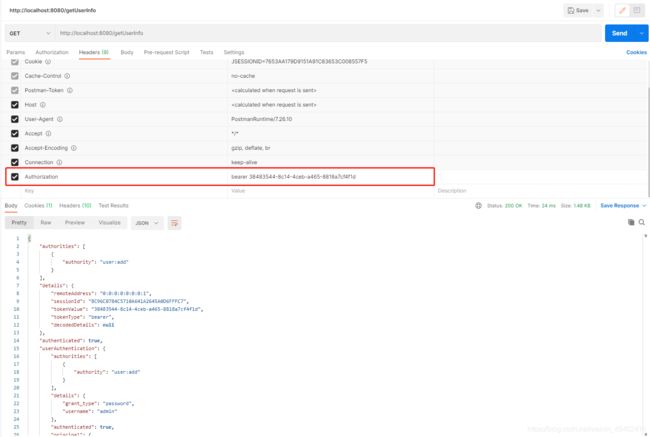
Authorization值的格式为token_type access_token
4.3 我们使用PostMan发送 localhost:8080/oauth/test GET请求,头部携带Authorization

可以看到,虽然我们在请求头中已经带上了正确的令牌,但是并没有成功获取到资源,正如前面所说的那样,/oauth/开头的请求由SecurityConfig定义的过滤器链处理,它不受资源服务器配置管理,所以使用令牌并不能成功获取到资源
4.4 测试注销令牌
使用PostMan发送 localhost:8080/loginOut DELETE请求,并在请求头中携带令牌
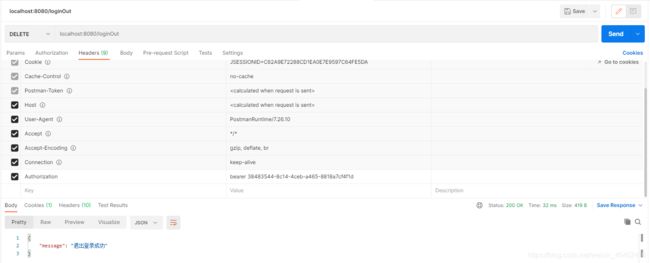
注销令牌后,原先的access_token和refresh_token都会马上失效,并且Redis也被清空
4.5 测试令牌刷新
因为我们上面注销了令牌,所以在此之前再次获取一次令牌

然后使用refresh_token去换取新的令牌,使用PostMan发送 localhost:8080/oauth/token POST请求,请求参数如下:

成功获取到了新的令牌
本文参考文献:https://www.kancloud.cn/mrbird/spring-cloud/1263689
