【Spring Security】从入门到精通
文章目录
- 【前言】
- 【正文】
-
- 一、简介
- 二、入门案例
-
- (一)创建maven工程
- (二)配置 pom.xml 文件
- (三)创建登录成功后的页面 index.html
- (四)配置springmvc的核心控制器 web.xml
- (五)配置自动配置 spring-security.xml
- (六)测试结果
- 三、进阶案例
-
- (一)配置可匿名访问的资源
-
- (1)案例要求:
- (2)实现配置:
-
- 第一步:在项目中创建js、css目录并在两个目录下提供任意一些测试文件
- 第二步:配置 spring-security.xml
- (二)自定义登录页
-
- (1)案例要求:
- (2)实现配置:
-
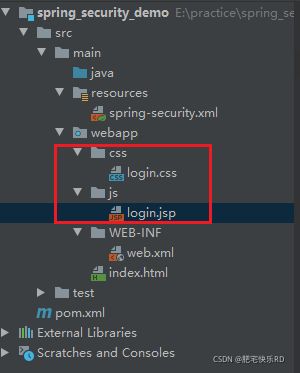
- 第一步:提供login.html作为项目的登录页面
- 第二步:修改spring-security.xml文件
-
- 1:指定login.html页面可以匿名访问,否则无法访问
- 2:关闭盗链安全请求
- 3:加入表单登录信息的配置
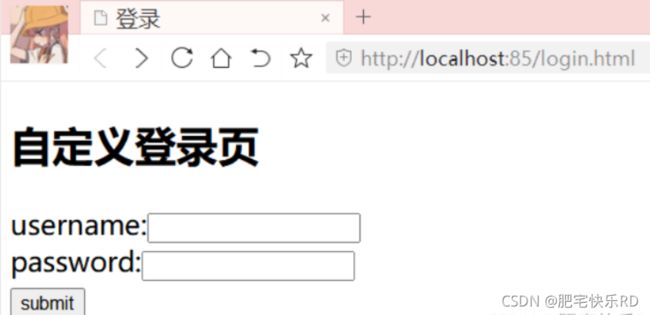
- 第三步:测试结果
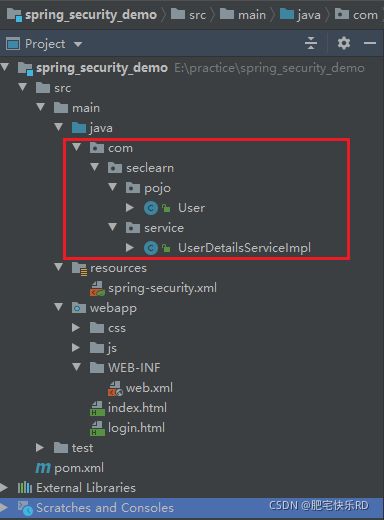
- (三)从数据库查询用户信息
-
- (1)案例要求:
- (2)实现配置:
-
- 第一步:创建java bean对象
- 第二步:定义UserService类,实现UserDetailsService接口
- 第三步:修改spring-security.xml文件
- (四)对密码进行加密
-
- (1)常见加密方式
- (2)MD5加密
-
- 第一步:导入MD5Utils工具类
- 第二步:创建测试类
- 第三步:测试结果
- (3)bcrypt加密
-
- 第一步:修改spring-security.xml文件
- 第二步:创建测试类
- 第三步:测试结果
- 第四步:修改UserService实现类
- 第五步:测试结果
- (五)配置多种校验规则(对页面)
-
- (1)案例要求:
- (2)实现配置:
-
- 第一步:修改spring-security.xml文件
- 第二步:测试结果
- (六)注解方式权限控制(对类)
-
- (1)案例要求:
- (2)实现配置:
-
- 第一步:在spring-security.xml文件中配置组件扫描,用于扫描Controller
- 第二步:在spring-security.xml文件中开启权限注解支持
- 第三步:创建Controller类并在Controller的方法上加入注解(@PreAuthorize)进行权限控制
- 第四步:测试结果
- (七)退出登录
-
- (1)案例要求:
- (2)实现配置:
-
- 第一步:index.html定义退出登录链接
- 第二步:配置spring-security.xml文件
- 第三步:粗诶结果
- 【总结】
-
-
- 1:配置可匿名访问的资源(不需要登录,权限 角色 就可以访问)
- 2:使用指定的登录页面(login.html)
- 3:从数据库查询用户信息
- 4:对密码进行加密
- 5:配置多种校验规则(对访问的页面做权限控制)
- 6:注解方式权限控制(对访问的Controller类做权限控制)
- 7:退出登录
-
【前言】
Spring Security是 Spring提供的安全认证服务的框架。 使用Spring Security可以帮助我们来简化认证和授权的过程。本文将对Spring Security进行从入门到进阶的讲解。
【正文】
一、简介
- SpringSecurity是Spring家族的一个安全框架, 简化我们开发里面的认证和授权过程
- SpringSecurity内部封装了Filter(只需要在web.xml容器中配置一个过滤器–代理过滤器,真实的过滤器在spring的容器中配置)
- 常见的安全框架
• Spring的 SpringSecurity:https://spring.io/projects/spring-security/
• Apache的Shiro: http://shiro.apache.org/
二、入门案例
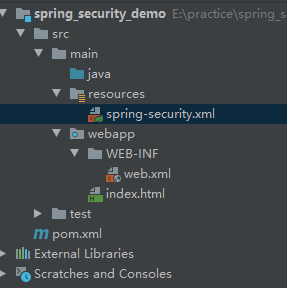
(一)创建maven工程
(二)配置 pom.xml 文件
<project xmlns="http://maven.apache.org/POM/4.0.0"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://maven.apache.org/POM/4.0.0 http://maven.apache.org/xsd/maven-4.0.0.xsd">
<modelVersion>4.0.0modelVersion>
<groupId>com.securitylearngroupId>
<artifactId>spring_security_demoartifactId>
<version>1.0-SNAPSHOTversion>
<packaging>warpackaging>
<properties>
<spring.version>5.0.5.RELEASEspring.version>
<project.build.sourceEncoding>UTF-8project.build.sourceEncoding>
<maven.compiler.source>1.8maven.compiler.source>
<maven.compiler.target>1.8maven.compiler.target>
properties>
<dependencies>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-coreartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-webartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-webmvcartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-context-supportartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-testartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframeworkgroupId>
<artifactId>spring-jdbcartifactId>
<version>${spring.version}version>
dependency>
<dependency>
<groupId>org.springframework.securitygroupId>
<artifactId>spring-security-webartifactId>
<version>5.0.5.RELEASEversion>
dependency>
<dependency>
<groupId>org.springframework.securitygroupId>
<artifactId>spring-security-configartifactId>
<version>5.0.5.RELEASEversion>
dependency>
<dependency>
<groupId>javax.servletgroupId>
<artifactId>servlet-apiartifactId>
<version>2.5version>
<scope>providedscope>
dependency>
dependencies>
<build>
<plugins>
<plugin>
<groupId>org.apache.tomcat.mavengroupId>
<artifactId>tomcat7-maven-pluginartifactId>
<configuration>
<port>85port>
<path>/path>
configuration>
plugin>
plugins>
build>
project>
(三)创建登录成功后的页面 index.html
DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Titletitle>
head>
<body>
<h2>登录成功h2>
body>
html>
(四)配置springmvc的核心控制器 web.xml
在web.xml 中主要配置 SpringMVC 的 DispatcherServlet 和用于整合第三方框架的DelegatingFilterProxy代理过滤器,
真正的过滤器在spring的配置文件,用于整合Spring Security。
<web-app xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns="http://java.sun.com/xml/ns/javaee"
xsi:schemaLocation="http://java.sun.com/xml/ns/javaee http://java.sun.com/xml/ns/javaee/web-app_3_0.xsd"
id="WebApp_ID" version="3.0">
<filter>
<filter-name>springSecurityFilterChainfilter-name>
<filter-class>org.springframework.web.filter.DelegatingFilterProxyfilter-class>
filter>
<filter-mapping>
<filter-name>springSecurityFilterChainfilter-name>
<url-pattern>/*url-pattern>
filter-mapping>
<servlet>
<servlet-name>springmvcservlet-name>
<servlet-class>org.springframework.web.servlet.DispatcherServletservlet-class>
<init-param>
<param-name>contextConfigLocationparam-name>
<param-value>classpath:spring-security.xmlparam-value>
init-param>
<load-on-startup>1load-on-startup>
servlet>
<servlet-mapping>
<servlet-name>springmvcservlet-name>
<url-pattern>*.dourl-pattern>
servlet-mapping>
web-app>
(五)配置自动配置 spring-security.xml
在 spring-security.xml 中主要配置 Spring Security 的拦截规则和认证管理器;
自动配置,使用表达式的方式完成授权,只要具有ROLE_ADMIN的角色权限才能访问系统中的所有功能;
授权管理器,指定用户名admin,密码admin,具有ROLE_ADMIN的角色权限
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:context="http://www.springframework.org/schema/context"
xmlns:mvc="http://www.springframework.org/schema/mvc"
xmlns:security="http://www.springframework.org/schema/security"
xsi:schemaLocation="http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans.xsd
http://www.springframework.org/schema/mvc
http://www.springframework.org/schema/mvc/spring-mvc.xsd
http://www.springframework.org/schema/context
http://www.springframework.org/schema/context/spring-context.xsd
http://www.springframework.org/schema/security
http://www.springframework.org/schema/security/spring-security.xsd">
<security:http auto-config="true" use-expressions="true">
<security:intercept-url pattern="/**" access="hasRole('ROLE_ADMIN')">security:intercept-url>
security:http>
<security:authentication-manager>
<security:authentication-provider>
<security:user-service>
<security:user name="admin" authorities="ROLE_ADMIN" password="{noop}admin">security:user>
security:user-service>
security:authentication-provider>
security:authentication-manager>
beans>
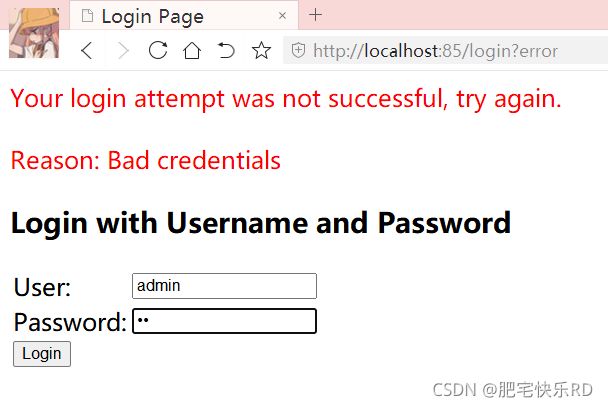
(六)测试结果
登录失败:
三、进阶案例
(一)配置可匿名访问的资源
- 不需要登录权限和角色,就可以访问的资源
(1)案例要求:
指定 js和css 目录下的文件可以在没有认证的情况下任意访问
(2)实现配置:
第一步:在项目中创建js、css目录并在两个目录下提供任意一些测试文件
第二步:配置 spring-security.xml
指定哪些资源可以匿名访问
<security:http security="none" pattern="/js/**" />
<security:http security="none" pattern="/css/**" />
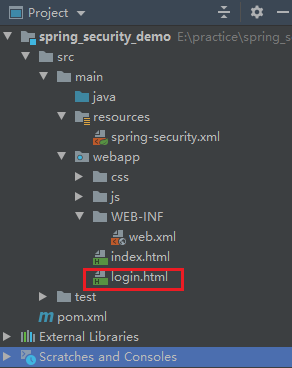
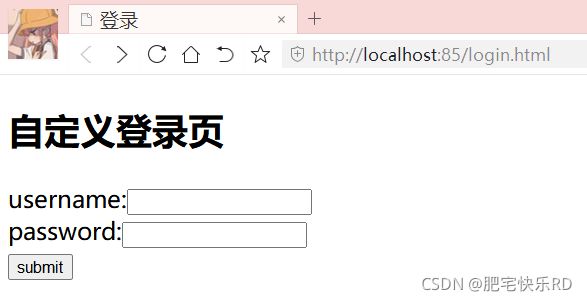
(二)自定义登录页
(1)案例要求:
提供login.html作为项目的登录页面
1:用户名是username
2:密码是password
3:登录的url是login.do
(2)实现配置:
第一步:提供login.html作为项目的登录页面
login.html:
DOCTYPE html>
<html>
<head>
<meta charset="UTF-8">
<title>登录title>
head>
<body>
<form action="/login.do" method="post">
username:<input type="text" name="username"><br>
password:<input type="password" name="password"><br>
<input type="submit" value="submit">
form>
body>
html>
第二步:修改spring-security.xml文件
1:指定login.html页面可以匿名访问,否则无法访问
<security:http security="none" pattern="/login.html" />
2:关闭盗链安全请求
Spring-security采用盗链机制,其中_csrf使用token标识和随机字符,每次访问页面都会随机生成,然后和服务器进行比较,成功可以访问,不成功不能访问。
<security:csrf disabled="true" />
3:加入表单登录信息的配置
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:context="http://www.springframework.org/schema/context"
xmlns:mvc="http://www.springframework.org/schema/mvc"
xmlns:security="http://www.springframework.org/schema/security"
xsi:schemaLocation="http://www.springframework.org/schema/beans
http://www.springframework.org/schema/beans/spring-beans.xsd
http://www.springframework.org/schema/mvc
http://www.springframework.org/schema/mvc/spring-mvc.xsd
http://www.springframework.org/schema/context
http://www.springframework.org/schema/context/spring-context.xsd
http://www.springframework.org/schema/security
http://www.springframework.org/schema/security/spring-security.xsd">
<security:http security="none" pattern="/js/**" />
<security:http security="none" pattern="/css/**" />
<security:http security="none" pattern="/login.html" />
<security:http auto-config="true" use-expressions="true">
<security:intercept-url pattern="/**" access="hasRole('ROLE_ADMIN')">security:intercept-url>
<security:form-login login-page="/login.html"
username-parameter="username"
password-parameter="password"
login-processing-url="/login.do"
default-target-url="/index.html"
authentication-failure-url="/login.html"
always-use-default-target="true"/>
<security:csrf disabled="true">security:csrf>
security:http>
<security:authentication-manager>
<security:authentication-provider>
<security:user-service>
<security:user name="admin" authorities="ROLE_ADMIN" password="{noop}admin">security:user>
security:user-service>
security:authentication-provider>
security:authentication-manager>
beans>
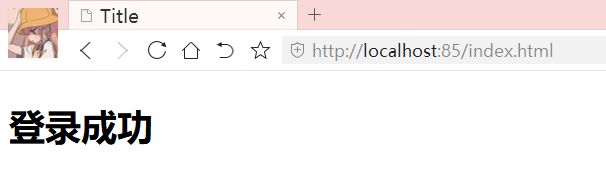
第三步:测试结果
(三)从数据库查询用户信息
(1)案例要求:
如果我们要从数据库动态查询用户信息,就必须按照spring security框架的要求提供一个实现UserDetailsService接口的实现类,并按照框架的要求进行配置即可。框架会自动调用实现类中的方法并自动进行密码校验。
(2)实现配置:
第一步:创建java bean对象
package com.seclearn.pojo;
/**
* @program: spring_security_demo
* @description:
* @author: txg
* @create: 2021-10-21 16:01
**/
public class User {
private String username;
private String password;
private String telephone;
@Override
public String toString() {
return "User{" +
"username='" + username + '\'' +
", password='" + password + '\'' +
", telephone='" + telephone + '\'' +
'}';
}
public String getUsername() {
return username;
}
public void setUsername(String username) {
this.username = username;
}
public String getPassword() {
return password;
}
public void setPassword(String password) {
this.password = password;
}
public String getTelephone() {
return telephone;
}
public void setTelephone(String telephone) {
this.telephone = telephone;
}
}
第二步:定义UserService类,实现UserDetailsService接口
UserDetailsService接口
在spring配置文件中注册UserService,指定其作为认证过程中根据用户名查询用户信息的处理类。
当我们进行登录操作时,spring security框架会调用UserService的loadUserByUsername方法查询用户信息,并根据此方法中提供的数据库中的密码和用户页面输入的表单密码进行比对来实现认证操作。
package com.seclearn.service;
import org.springframework.security.core.GrantedAuthority;
import org.springframework.security.core.authority.SimpleGrantedAuthority;
import org.springframework.security.core.userdetails.UserDetails;
import org.springframework.security.core.userdetails.UserDetailsService;
import org.springframework.security.core.userdetails.UsernameNotFoundException;
import org.springframework.stereotype.Service;
import java.util.ArrayList;
import java.util.HashMap;
import java.util.List;
import java.util.Map;
/**
* @program: spring_security_demo
* @description: 基于数据库的认证
* @author: txg
* @create: 2021-10-21 16:01
**/
@Service //声明bean对象,id就是类名首字母小写 id="userDetailsService"
public class UserDetailsServiceImpl implements UserDetailsService {
//模拟数据库中的用户数据
static Map<String, com.seclearn.pojo.User> map = new HashMap<>();
static {
com.seclearn.pojo.User user1 = new com.seclearn.pojo.User();
user1.setUsername("admin");
user1.setPassword("admin");
user1.setTelephone("123");
com.seclearn.pojo.User user2 = new com.seclearn.pojo.User();
user2.setUsername("txg");
user2.setPassword("txg");
user1.setTelephone("321");
map.put(user1.getUsername(), user1);
map.put(user2.getUsername(), user2);
}
@Override
public UserDetails loadUserByUsername(String username) throws UsernameNotFoundException {
//表示从数据库查询数据 模拟
com.seclearn.pojo.User user = map.get(username);
if (user == null) {
return null; //用户不存在只需要返回null,框架会自动跳转到登录页
}
String password = "{noop}" + user.getPassword();
//角色:角色是权限的集合
List<GrantedAuthority> lists = new ArrayList<>();
lists.add(new SimpleGrantedAuthority("add"));
lists.add(new SimpleGrantedAuthority("delete")); //用权限名称表示权限,直接使用权限名称即可
lists.add(new SimpleGrantedAuthority("ROLE_ADMIN")); //用角色表示权限时,需增加“ROLE_”前缀
//使用框架提供的User 实现UserDetail接口
return new org.springframework.security.core.userdetails.User(user.getUsername(),password,lists);
}
}
第三步:修改spring-security.xml文件
<security:authentication-manager>
<security:authentication-provider user-service-ref="userDetailServiceImpl">
security:authentication-provider>
security:authentication-manager>
如果没有配置扫描包,需要配置:
<context:component-scan base-package="com.seclearn">context:component-scan>
(四)对密码进行加密
(1)常见加密方式
前面我们使用的密码都是明文的,这是非常不安全的;一般情况下用户的密码需要进行加密后再保存到数据库中。
常见的密码加密方式有:
3DES、AES、DES:使用对称加密算法,可以通过解密来还原出原始密码;MD5、SHA1:使用单向HASH算法,无法通过计算还原出原始密码,但是可以建立彩虹表进行查表破解;MD5:可进行加盐加密,保证安全;
(2)MD5加密
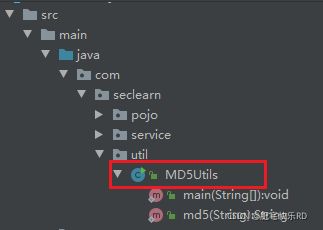
第一步:导入MD5Utils工具类
package com.seclearn.util;
import java.math.BigInteger;
import java.security.MessageDigest;
import java.security.NoSuchAlgorithmException;
public class MD5Utils {
/**
* 使用md5的算法进行加密
*/
public static String md5(String plainText) {
byte[] secretBytes = null;
try {
secretBytes = MessageDigest.getInstance("md5").digest(
plainText.getBytes());
} catch (NoSuchAlgorithmException e) {
throw new RuntimeException("没有md5这个算法!");
}
String md5code = new BigInteger(1, secretBytes).toString(16);// 16进制数字
// 如果生成数字未满32位,需要前面补0
for (int i = 0; i < 32 - md5code.length(); i++) {
md5code = "0" + md5code;
}
return md5code;
}
public static void main(String[] args) {
System.out.println(md5("1234"));
}
}
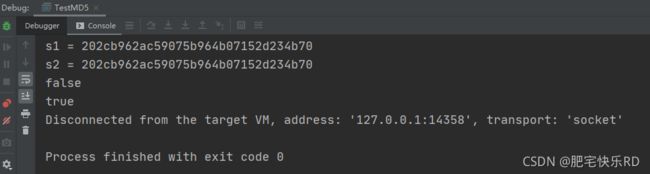
第二步:创建测试类
package com.seclearn;
import com.seclearn.util.MD5Utils;
/**
* @program: spring_security_demo
* @description: 测试类
* @author: txg
* @create: 2021-10-21 20:40
**/
public class TestMD5 {
public static void main(String[] args) {
String s1 = MD5Utils.md5("123");
String s2 = MD5Utils.md5("123");
System.out.println("s1 = " + s1);
System.out.println("s2 = " + s2);
System.out.println(s1 == s2);
System.out.println(s1.equals(s2));
}
}
第三步:测试结果
同样的密码值,盐值不同,加密的结果不同。
(3)bcrypt加密
bcrypt: 将salt随机并混入最终加密后的密码,验证时也无需单独提供之前的salt,从而无需单独处理salt问题
Spring security中的BCryptPasswordEncoder方法采用SHA-256 +随机盐+密钥对密码进行加密。
SHA系列是Hash算法,不是加密算法,使用加密算法意味着可以解密(这个与编码/解码一样),但是采用Hash处理,其过程是不可逆的。
(1)加密(encode): 注册用户时,使用SHA-256+随机盐+密钥把用户输入的密码进行hash处理,得到密码的hash值,然后将其存入数据库中。
(2)密码匹配(matches): 用户登录时,密码匹配阶段并没有进行密码解密(因为密码经过Hash处理,是不可逆的),而是使用相同的算法把用户输入的密码进行hash处理,得到密码的hash值,然后将其与从数据库中查询到的密码hash值进行比较。如果两者相同,说明用户输入的密码正确。
这正是为什么处理密码时要用hash算法,而不用加密算法。因为这样处理即使数据库泄漏,黑客也很难破解密码。
第一步:修改spring-security.xml文件
指定密码加密对象
<security:authentication-manager>
<security:authentication-provider user-service-ref="userService">
<security:password-encoder ref="passwordEncoder">security:password-encoder>
security:authentication-provider>
security:authentication-manager>
<bean id="passwordEncoder" class="org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder" />
第二步:创建测试类
package com.seclearn;
import org.junit.Test;
import org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder;
/**
* @program: spring_security_demo
* @description:
* @author: txg
* @create: 2021-10-21 21:31
**/
public class TestSpringSecurity {
// SpringSecurity加盐加密
@Test
public void testSpringSecurity(){
BCryptPasswordEncoder encoder = new BCryptPasswordEncoder();
String s = encoder.encode("abc");
System.out.println(s);
String s1 = encoder.encode("abc");
System.out.println(s1);
// 进行判断 先生成一个,复制到这里做比对
boolean b = encoder.matches("abc", "$2a$10$dyIf5fOjCRZs/pYXiBYy8uOiTa1z7I.mpqWlK5B/0icpAKijKCgxe");
System.out.println(b);
}
}
第三步:测试结果
$2a$10$/bTVvqqlH9UiE0ZJZ7N2Me3RIgUCdgMheyTgV0B4cMCSokPa.6oCa
加密后字符串的长度为固定的
60位;
$是分割符,无意义;
2a是bcrypt加密版本号;
10是cost的值;
而后的前22位是salt值;
再然后的字符串就是密码的密文了。
第四步:修改UserService实现类
将密码设置为加密后的密文
static {
com.seclearn.pojo.User user1 = new com.seclearn.pojo.User();
user1.setUsername("admin");
user1.setPassword("$2a$10$BkHeHArjzunbXzlgTtxi9.PUSV7nPn56w6fA4hEkuN8wd6EbtQeyi");
user1.setTelephone("123");
com.seclearn.pojo.User user2 = new com.seclearn.pojo.User();
user2.setUsername("txg");
user2.setPassword("$2a$10$BljUMVT6/IXyLBOuUGRRfeLbt8ytfgiMccNOz8rXXdP.dGCbetGU.");
user1.setTelephone("321");
map.put(user1.getUsername(), user1);
map.put(user2.getUsername(), user2);
}
//String password = "{noop}" + user.getPassword();
String password = user.getPassword();
第五步:测试结果
再重新install项目,重新运行之后再次输入账号密码,可以登录成功。
(五)配置多种校验规则(对页面)
(1)案例要求:
对访问的页面做权限控制
(2)实现配置:
为了测试方便,首先在项目的webapp文件夹下面创建 a.html、b.html、c.html、d.html几个页面
第一步:修改spring-security.xml文件
<security:http auto-config="true" use-expressions="true">
<security:intercept-url pattern="/index.html" access="isAuthenticated()" />
<security:intercept-url pattern="/a.html" access="isAuthenticated()" />
<security:intercept-url pattern="/b.html" access="hasAuthority('add')" />
<security:intercept-url pattern="/c.html" access="hasRole('ROLE_ADMIN')" />
<security:intercept-url pattern="/d.html" access="hasRole('ABC')" />
security:http>
第二步:测试结果
登录后可以访问a.html,b.html,c.html,不能访问d.html
(六)注解方式权限控制(对类)
Spring Security除了可以在配置文件中配置权限校验规则,还可以使用注解方式控制类中方法的调用。
(1)案例要求:
对访问的Controller类中的某个方法做权限控制
(2)实现配置:
第一步:在spring-security.xml文件中配置组件扫描,用于扫描Controller
<context:component-scan base-package="com.seclearn"/>
<mvc:annotation-driven />
第二步:在spring-security.xml文件中开启权限注解支持
<security:global-method-security pre-post-annotations="enabled" />
第三步:创建Controller类并在Controller的方法上加入注解(@PreAuthorize)进行权限控制
package com.seclearn.controller;
import org.springframework.security.access.prepost.PostAuthorize;
import org.springframework.security.access.prepost.PreAuthorize;
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.bind.annotation.RestController;
/**
* @program: spring_security_demo
* @description:
* @author: txg
* @create: 2021-10-22 10:54
**/
@RestController
@RequestMapping("/hello")
//@PreAuthorize("isAuthenticated()") //必须通过认证,也可在xml配置文件中配置
public class HelloController {
@RequestMapping("/add")
//@PostAuthorize() //来之后认证 下面的是来之前认证
@PreAuthorize("hasAuthority('add')") //表示用户必须拥有add权限才能调用当前方法
public String add(){
System.out.println("add……");
return "success";
}
//没有采用细粒度权限控制注解,可以访问,不认证也是可以的
@RequestMapping("/update")
//@PreAuthorize("hasRole('ROLE_ADMIN')") //表示用户必须拥有ROLE_ADMIN角色才能调用当前方法
public String update(){
System.out.println("update……");
return "success";
}
@RequestMapping("/delete")
@PreAuthorize("hasRole('ABC')") //表示用户必须拥有ABC角色才能调用当前方法
public String delete(){
System.out.println("delete……");
return "success";
}
}
第四步:测试结果
(七)退出登录
(1)案例要求:
用户完成登录后Spring Security框架会记录当前用户认证状态为已认证状态,即表示用户登录成功了。
现在要求,退出登录后,将用户的账号注销,再次访问需要重新登录
(2)实现配置:
第一步:index.html定义退出登录链接
DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>Titletitle>
head>
<body>
登录成功!<br>
<a href="/logout.do">退出登录a>
body>
html>
第二步:配置spring-security.xml文件
<!—
授权注销操作
logout:退出登录
logout-url:退出登录操作对应的请求路径
logout-success-url:退出登录后的跳转页面
invalidate-session="true" 默认为true,用户在退出后Http session失效
-->
<security:logout logout-url="/logout.do" logout-success-url="/login.html" invalidate-session="true"/>
第三步:粗诶结果
通过上面的配置可以发现,如果用户要退出登录,只需要请求/logout.do这个URL地址就可以,同时会将当前session失效,最后页面会跳转到login.html页面。
【总结】
对上面的案例进行总结:
1:配置可匿名访问的资源(不需要登录,权限 角色 就可以访问)
<security:http security="none" pattern="/js/**">security:http>
<security:http security="none" pattern="/css/**">security:http>
<security:http security="none" pattern="/login.html">security:http>
2:使用指定的登录页面(login.html)
<security:form-login login-page="/login.html"
username-parameter="username"
password-parameter="password"
login-processing-url="/login.do"
default-target-url="/index.html"
authentication-failure-url="/login.html"
always-use-default-target="true"/>
3:从数据库查询用户信息
<security:authentication-manager>
<security:authentication-provider user-service-ref="userService">
<security:password-encoder ref="bCryptPasswordEncoder">security:password-encoder>
security:authentication-provider>
security:authentication-manager>
4:对密码进行加密
<bean id="bCryptPasswordEncoder" class="org.springframework.security.crypto.bcrypt.BCryptPasswordEncoder">bean>
5:配置多种校验规则(对访问的页面做权限控制)
<security:intercept-url pattern="/index.html" access="isAuthenticated()">security:intercept-url>
<security:intercept-url pattern="/a.html" access="isAuthenticated()">security:intercept-url>
<security:intercept-url pattern="/b.html" access="hasAuthority('add')">security:intercept-url>
<security:intercept-url pattern="/c.html" access="hasRole('ROLE_ADMIN')">security:intercept-url>
<security:intercept-url pattern="/d.html" access="hasRole('ABC')">security:intercept-url>
6:注解方式权限控制(对访问的Controller类做权限控制)
<security:global-method-security pre-post-annotations="enabled">security:global-method-security>
7:退出登录
<security:logout logout-url="/logout.do" logout-success-url="/login.html" invalidate-session="true">security:logout>
以上就是Spring Security的知识介绍啦,欢迎阅读~