upload-labs靶场-Pass-08关-思路以及过程
开始前的小准备
upload-labs靶场 是PHP环境运行的,所以我准备了一个PHP脚本和一张图片
图片好准备,PHP脚本如果不想写的话可以用我的这个获取当前时间的PHP脚本
header("content-type:text/html;charset=utf-8");
date_default_timezone_set("PRC");//设置时区
echo "当前时间为:";
$today = date("Y-m-d D h:i:s A ");
echo $today;
?>
图片默认不清楚放大看!!!
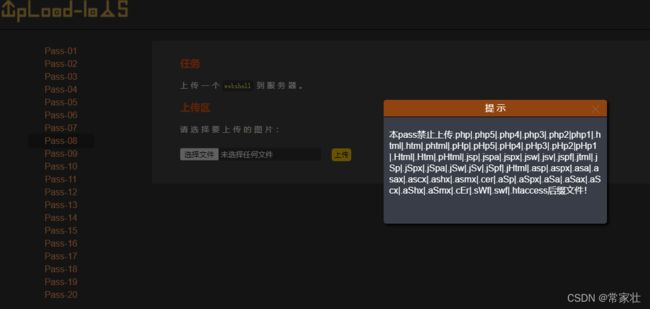
Pass-08
$is_upload = false;
$msg = null;
if (isset($_POST['submit'])) {
if (file_exists(UPLOAD_PATH)) {
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml",".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']);
$file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = trim($file_ext); //首尾去空
if (!in_array($file_ext, $deny_ext)) {
$temp_file = $_FILES['upload_file']['tmp_name'];
$img_path = UPLOAD_PATH.'/'.date("YmdHis").rand(1000,9999).$file_ext;
if (move_uploaded_file($temp_file, $img_path)) {
$is_upload = true;
} else {
$msg = '上传出错!';
}
} else {
$msg = '此文件类型不允许上传!';
}
} else {
$msg = UPLOAD_PATH . '文件夹不存在,请手工创建!';
}
}
这关之前的方法基本上是用不了的
通关过程:
这关其实是利用 Windows系统一个命名特性,Windows系统如果文件名+"::$DATA"会把::$DATA之后的数据当成文件流处理,不会检测后缀名,且保持::$DATA之前的文件名,他的目的就是不检查后缀名
举个例子:
上传文件名为:测试.php::$DATA到Windows系统会自动去掉末尾的::$DATA变成"测试.php或者xxx.php"
通关完成!