k8s——ingress
- Ingress简介
-
- Ingress组成
-
- ingress
- ingress-controller
- Ingress工作原理
- 部署nginx-ingress-controller
-
- 部署ingress-controller pod及相关资源
- 修改clusterRole资源配置
- ingress暴露服务的方式
- 采用方式二:DaemonSet+HostNetwork+nodeselector
-
- 指定nginx-ingress-controller运行在node02节点
- 修改Deployment为Daemonset,指定节点运行,并开启 hostNetwork
- 所有node节点上传nginx-ingress-controller镜像压缩包ingree.contro.tar.gz.到/opt/ingress目录,并解压和加载镜像
- 启动nginx-ingress-controller
- 创建ingress规则
-
- 创建一个deployment和svc
- 创建ingress
- 做端口映射并访问测试
- 查看nginx-ingress-controller
- 采用方式三:Deployment+NodePort模式的Service
-
- 下载nginx-ingress-controller和ingress-nginx暴露端口配置文件
- 在所有node节点上传镜像包ingress-controller-0.30.0.tar到/opt/ingress-nodeport目录,并加载镜像
- 启动nginx-ingress-controller
- 创建deployment、service和ingress的yaml资源
- 做端口映射并访问测试
- ingress http代理访问虚拟主机
- ingress https代理访问
-
- 创建工作目录
- 创建ssl证书
- 创建secret资源进行存储
- 创建deployment、service和ingress的yaml资源
- 做端口映射并访问测试
- nginx进行BasicAuth(访问前输入用户和密码)
-
- 创建工作目录
- 生成用户密码文件,创建secret资源进行存储
- 创建ingress资源
- 做端口映射并访问测试
- nginx进行重写
-
Ingress简介
service的作用
- 对集群内部,它不断跟踪pod的变化,更新endpoint中对应pod的对象,提供了ip不断变化的pod的服务发现机制
- 对集群外部,他类似负载均衡器,可以在集群内外部对pod进行访问
外部访问k8s集群内的服务
- NodePort:测试环境使用还行,当有几十上百的服务在集群中运行时,NodePort的端口管理就是个灾难
- LoadBalancer:受限于云平台,且通常在云平台部署LoadBalancer还需要额外的费用
- Ingress:可以简单理解为service的service,它其实就是一组基于域名和URL路径,把用户的请求转发到一个或多个service的规则
Ingress组成
ingress
- ingress是一个APr对象,通过yaml文件来配置,ingress对象的作用是定义请求如何转发到service的规则,可以理解为配置模板
- ingress通过http或https暴露集群内部service,给service提供外部URL、负载均衡、SSL/TLs能力以及基于域名的反向代理。ingress要依靠ingress-controller来具体实现以上功能
ingress-controller
- ingress-controller是具体实现反向代理及负载均衡的程序,对ingress定义的规则进行解析,根据配置的规则来实现请求转发
- ingress -controller并不是kes自带的组件,实际上ingress-controller只是一个统称,用户可以选择不同的ingress-controller实现,目前,由k8s维护的ingress-controller只有google云的ccz与ingress-nginx两个,其他还有很多第三方维护的ingres-controller,具体可以参考官方文档。但是不管哪一种ingress-controller,实现的机制都大同小异,只是在具体配置上有差异
- 一般来说,ingress-controller的形式都是一个pod,里面跑着daemon程序和反向代理程序。daemcn负责不断监控集群的变化,根据ingress对象生成配置并应用新配置到反向代理,比如ingress -nginx就是动态生成nginx配置,动态更新upstrea,并在需要的时候reloada程序应用新配置。为了方便,后面的例子都以k8s官方维护的ingress-nginx为例
- Ingress-Nginx github 地址:https://github.com/kubernetes/ingress-nginx**
Ingress-Nginx官方网站:https:/kubernetes.github.io/ingress-nginx/
5.总结: ingress-controller才是负责具体转发的组件,通过各种方式将它暴露在集群入口,外部对集群的请求流量会先到
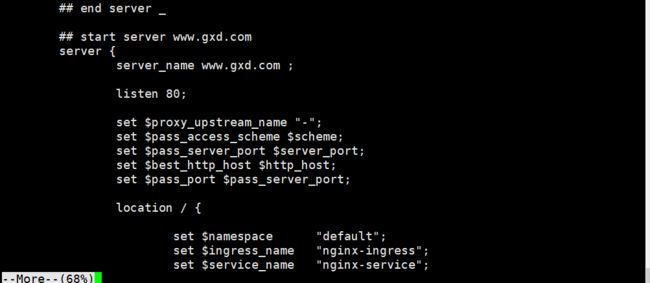
Ingress工作原理
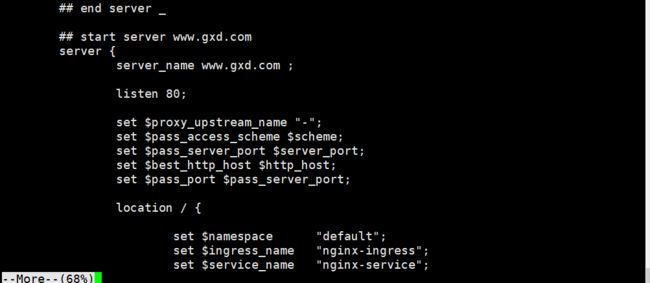
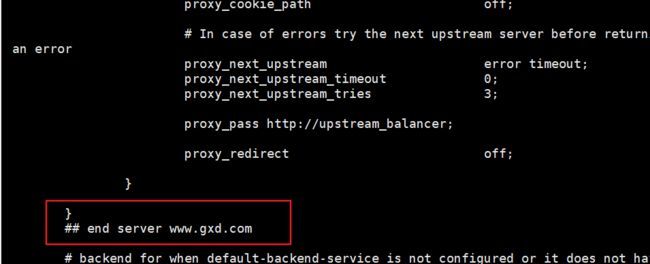
- ingress-controller通过和 kubernetes APIServer 交互,动态的去感知集群中ingress规则变化
- 然后读取它,按照自定义的规则,规则就是写明了哪个域名对应哪个service,生成一段nginx配置
- 再写到nginx-ingress-controller的pod里,这个ingress-controller的pod里运行着一个nginx服务,控制器会把生成的nginx配置写入/etc/nginx.conf文件中
- 然后reload一下使配置生效。以此达到域名区分配置和动态更新的作用
部署nginx-ingress-controller
部署ingress-controller pod及相关资源
1.mkdir /opt/ingress
2.cd /opt/ingress
==========================================================
官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.25.0/deploy/static/mandatory.yaml
上面可能无法下载,可用国内的gitee
3.wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.25.0/deploy/static/mandatory.yaml
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/mandatory.yaml

修改clusterRole资源配置
vim mandatory.yaml
....
- apiGroups:
- ""
resources:
-services
verbs:
- get
- list
- watch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses
verbs:
- get
- list
- watch
- apiGroups:
- ""
resources:
- events
verbs:
- create
- patch
- apiGroups:
- "extensions"
- "networking.k8s.io"
resources:
- ingresses/ status
verbs:
- update

ingress暴露服务的方式
- Deployment+LoadBalancer模式的Service
如果要把ingress部署在公有云,那用这种方式比较合适。用Deployment部署ingress-controller,创建一个type为 LoadBalancer的 service关联这组pod。大部分公有云,都会为 LoadBalancer的 service自动创建一个负载均衡器,通常还绑定了公网地址。只要把域名解析指向该地址,就实现了集群服务的对外暴露
- DaemonSet+HostNetwork+nodeselector
用DaemonSet结合nodeselector来部署ingress-controller到特定的node 上,然后使用Hostiletwork直接把该pod与宿主机node的网络打通,直接使用宿主机的80/433端口就能访问服务。这时,ingress-controller所在的node机器就很类似传统架构的边缘节点,比如机房入口的nginx服务器。该方式整个请求链路最简单,性能相对NodePort模式更好。缺点是由于直接利用宿主机节点的网络和端口,一个node只能部署一个ingress-controller pod。比较适合大并发的生产环境使用
- Deployment+NodePort模式的Service
1)同样用deployment模式部署ingres-controller,并创建对应的服务,但是type为NodePort。这样,ingress就会暴露在集群节点ip的特定端口上
2)由于nodeport暴露的端口是随机端口,一般会在前面再搭建一套负载均衡器来转发请求。该方式一般用于宿主机是相对固定的环境ip地址不变的场景
3)NodePort方式暴露ingress虽然简单方便,但是NodePort多了一层NAT,在请求量级很大时可能对性能会有一定影响
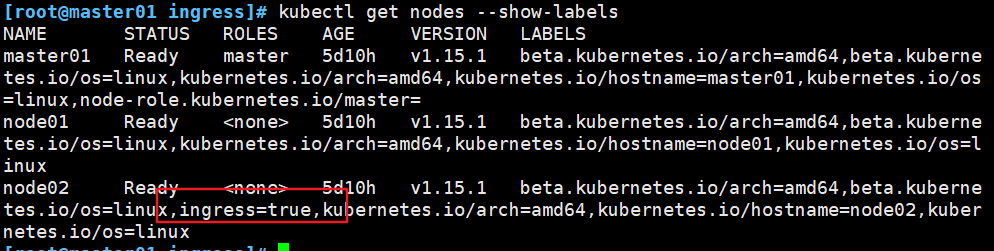
采用方式二:DaemonSet+HostNetwork+nodeselector
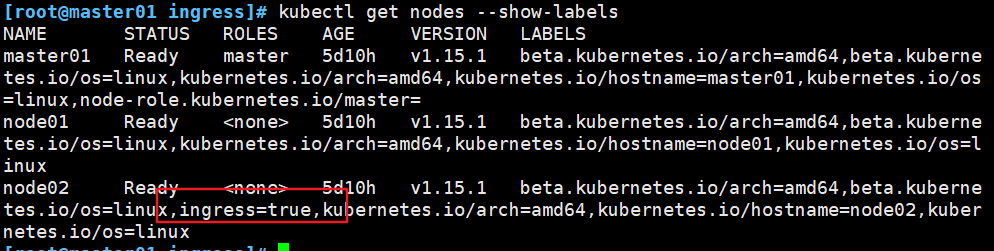
指定nginx-ingress-controller运行在node02节点
kubectl label node node02 ingress=true
kubectl get nodes
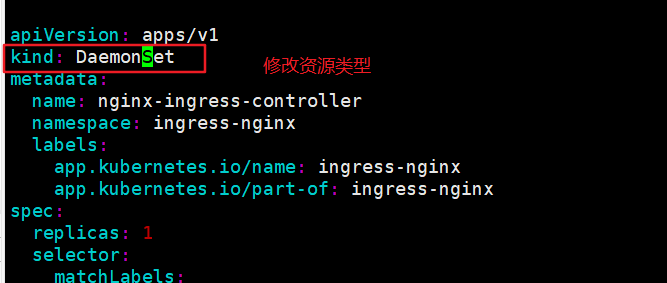
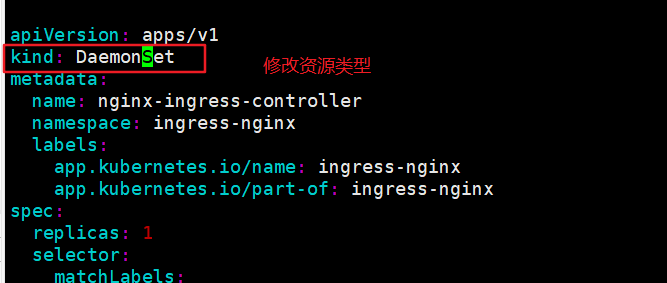
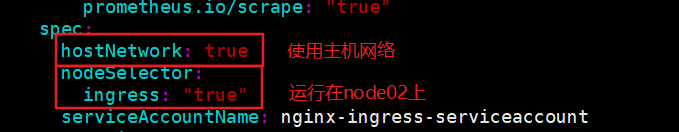
修改Deployment为Daemonset,指定节点运行,并开启 hostNetwork
vim mandatory.yaml
...
apiversion: apps/vl
kind: Daemonset
...
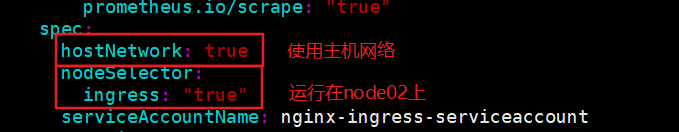
hostNetwork: true
nodeSelector:
ingress: "true"
...
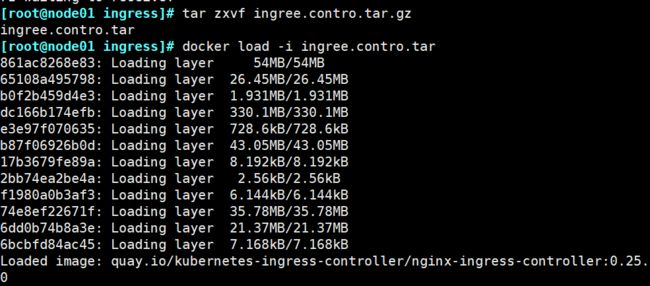
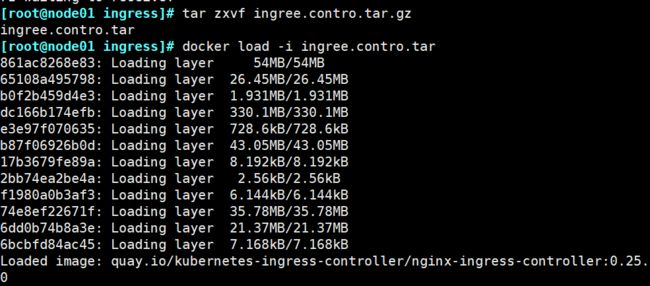
所有node节点上传nginx-ingress-controller镜像压缩包ingree.contro.tar.gz.到/opt/ingress目录,并解压和加载镜像
mkdir /opt/ingress
cd /opt/ingress
tar zxvf ingree.contro.tar.gz
docker load -i ingree.contro.tar
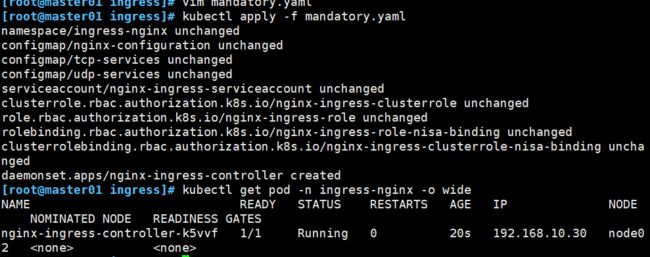
启动nginx-ingress-controller
#主节点
kubectl apply -f mandatory.yaml
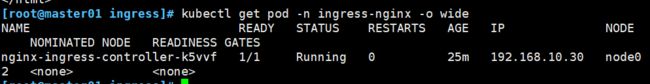
kubectl get pod -n ingress-nginx -o wide
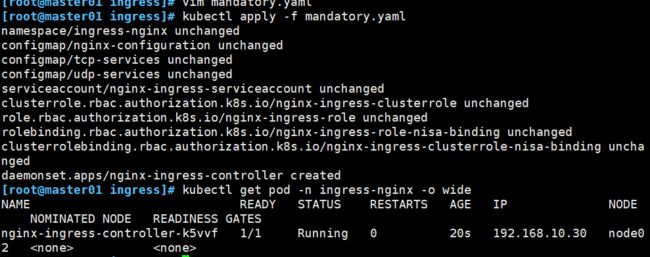
到node02节点查看
netstat -natp | grep nginx
==========================================================
由于配置了hostnetwork, nginx已经在 node主机本地监听团/443/8181端口。其中 8181 是nginx-controller默认配置的一个defaultbackend (Ingress资源没有匹配的 rule 对象时,流量就会被导向这个default backend)
这样,只要访问 node主机有公网 TP,就可以直接映射域名来对外网暴露服务了。如果要nginx高可用的话,可以在多个node39上部署,并在前面再搭建一套LVS+keepalive做负载均衡。

创建ingress规则
创建一个deployment和svc
在主节点创建
vim service-nginx.yaml
==========================================================
apiVersion: apps/v1
kind: Deployment
metadata:
labels:
run: nginx-app
name: nginx-app
spec:
replicas: 2
selector:
matchLabels:
app: nginx
template:
metadata:
labels:
app: nginx
spec:
containers:
- image: nginx
name: nginx-app
ports:
- containerPort: 80
---
apiVersion: v1
kind: Service
metadata :
name: nginx-service
spec:
type: ClusterIP
ports :
- port: 7777
targetPort: 80
selector :
app: nginx
==========================================================
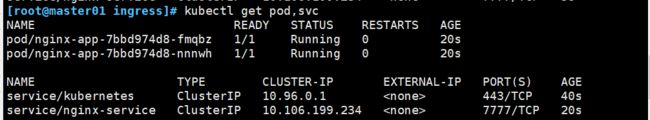
kubectl apply -f service-nginx.yaml
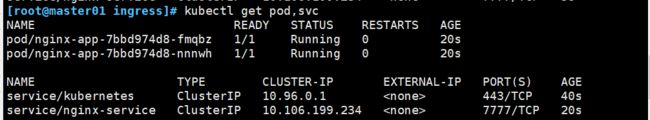
kubectl get pod,svc
创建ingress
vim ingress-1.yaml
==========================================================
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: nginx-ingress
spec:
rules:
- host: www.gxd.com
http:
paths:
- path: /
backend:
serviceName: nginx-service
servicePort: 80
==========================================================
kubectl apply -f ingress-1.yaml
kubectl get pod,svc,ingress

做端口映射并访问测试
echo '192.168.10.30 www.gxd.com' >> /etc/hosts
curl www.gxd.com

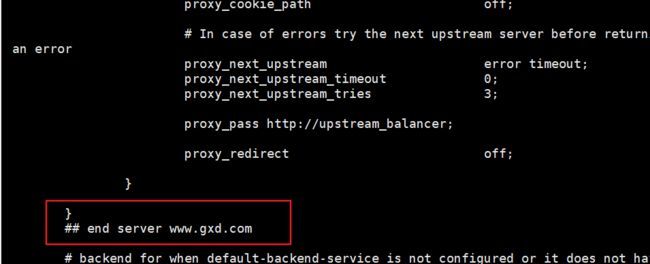
查看nginx-ingress-controller
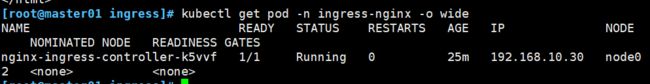
kubectl get pod -n ingress-nginx -o wide
kubectl exec -it nginx-ingress-controller-k5vvf -n ingress-nginx bash
采用方式三:Deployment+NodePort模式的Service
下载nginx-ingress-controller和ingress-nginx暴露端口配置文件
在主节点
mkdir /opt/ingress-nodeport
cd /opt/ingress-nodeport
官方下载地址:
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/mandatory.yaml
wget https://raw.githubusercontent.com/kubernetes/ingress-nginx/nginx-0.30.0/deploy/static/provider/baremetal/service-nodeport.yaml
国内 gitee 资源地址:
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/mandatory.yaml
wget https://gitee.com/mirrors/ingress-nginx/raw/nginx-0.30.0/deploy/static/provider/baremetal/service-nodeport.yaml

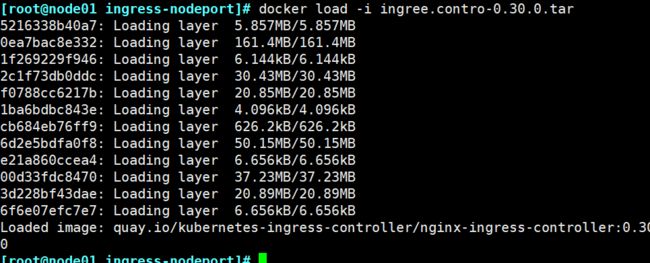
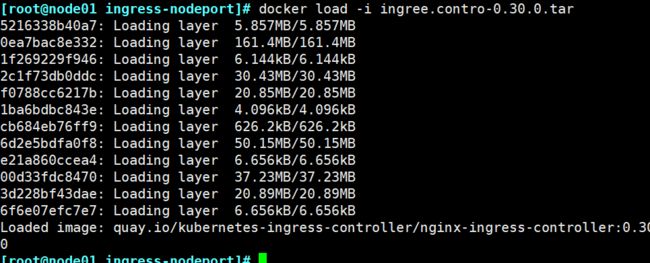
在所有node节点上传镜像包ingress-controller-0.30.0.tar到/opt/ingress-nodeport目录,并加载镜像
在所有node节点
mkdir /opt/ingress-nodeport
cd /opt/ingress-nodeport
tar zxvf ingree.contro-0.30.0.tar.gz
docker load -i ingree.contro-0.30.0.tar
启动nginx-ingress-controller
kubectl apply -f mandatory.yaml
kubectl apply -f service-nodeport.yaml

创建deployment、service和ingress的yaml资源
vim ingress-nginx.yaml
==========================================================
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: nginx-app
spec:
replicas: 2
template:
metadata:
labels:
name: nginx
spec:
containers:
- name: nginx
image: nginx
imagePullPolicy: IfNotPresent
ports:
- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:
name: nginx-svc
spec:
ports:
- port: 80
targetPort: 80
protocol: TCP
selector:
name: nginx
---
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: nginx-test
spec:
rules:
- host: www.gxd111.com
http:
paths:
- path: /
backend:
serviceName: nginx-svc
servicePort: 80
==========================================================kubectl apply -f ingress-nginx.yaml
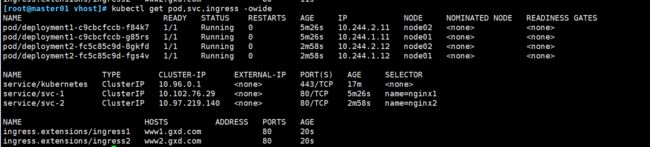
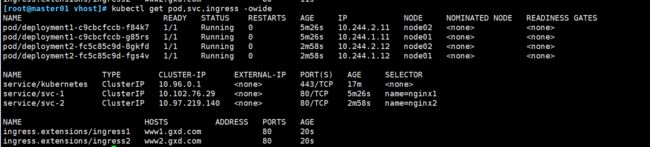
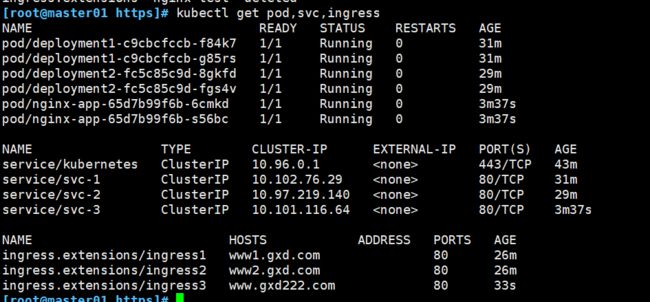
kubectl get pod,svc,ingress -owide

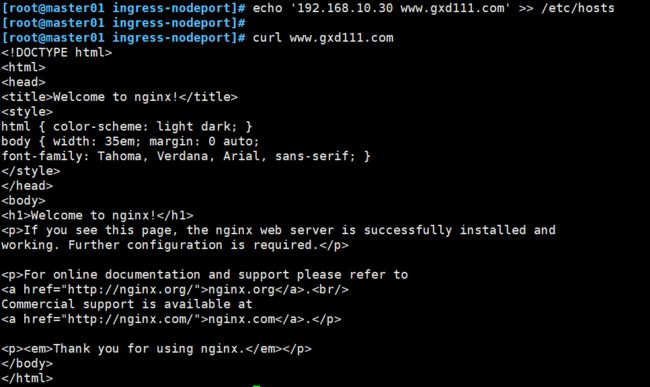
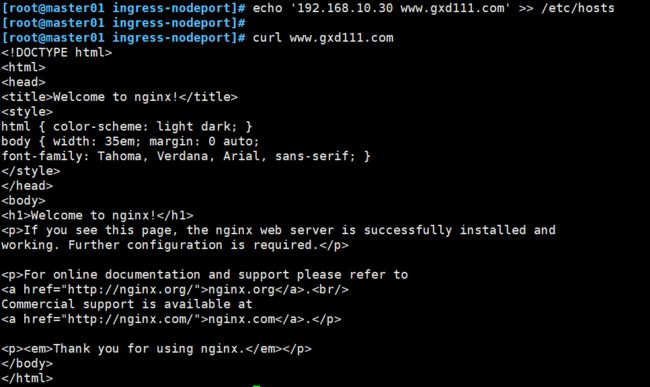
做端口映射并访问测试
echo '192.168.10.30 www.gxd111.com' >> /etc/hosts
curl www.gxd111.com
ingress http代理访问虚拟主机
mkdir /opt/ingress-nodeport/vhost
cd /opt/ingress-nodeport/vhost
==========================================================
vim demo1.yaml
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: deployment1
spec:
replicas: 2
template:
metadata:
labels:
name: nginx1
spec:
containers:
- name: nginx1
image: nginx
ports:
- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:
name: svc-1
spec:
ports:
- port: 80
protocol: TCP
targetPort: 80
selector:
name: nginx1
type: ClusterIP
==========================================================
vim demo2.yaml
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: deployment2
spec:
replicas: 2
template:
metadata:
labels:
name: nginx2
spec:
containers:
- name: nginx2
image: nginx
ports:
- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:
name: svc-2
spec:
ports:
- port: 80
protocol: TCP
targetPort: 80
selector:
name: nginx2
type: ClusterIP
==========================================================
创建ingress资源
vim ingress-nginx.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress1
spec:
rules:
- host: www1.gxd.com
http:
paths:
- path: /
backend:
serviceName: svc-1
servicePort: 80
---
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress2
spec:
rules:
- host: www2.gxd.com
http:
paths:
- path: /
backend:
serviceName: svc-2
servicePort: 80
==========================================================
kubectl apply -f demo1.yaml
kubectl apply -f demo2.yaml
kubectl apply -f ingress-nginx.yaml
kubectl get pod,svc,ingress
echo '192.168.10.30 www1.gxd.com ' >> /etc/hosts
echo '192.168.10.30 www2.gxd.com ' >> /etc/hosts
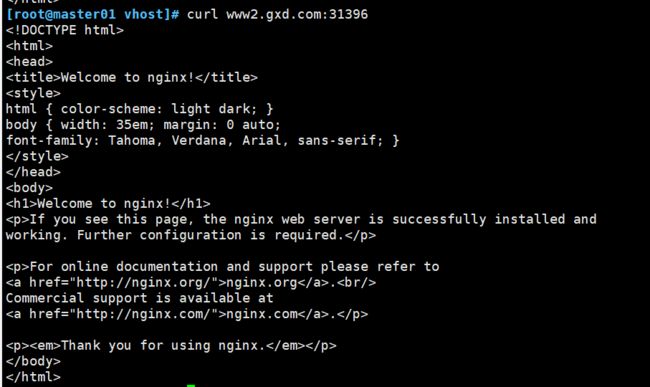
curl www1.gxd.com:31396
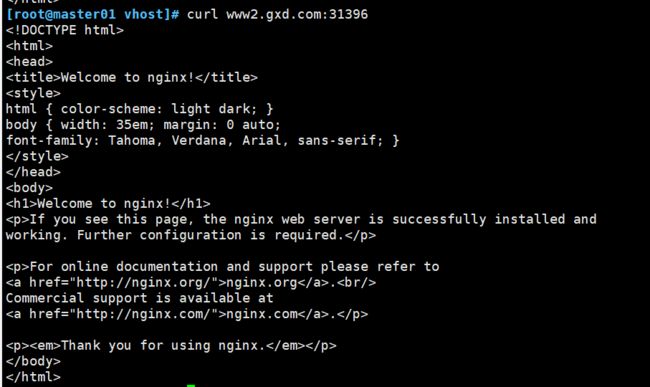
curl www2.gxd.com:31396
ingress https代理访问
创建工作目录
mkdir /opt/ingress-nodeport/https
cd /opt/ingress-nodeport/https
创建ssl证书
openssl req -x509 -sha256 -nodes -days 365 -newkey rsa:2048 -keyout tls.key -out tls.crt -subj "/CN=nginXsvc/O=nginxsvc"

创建secret资源进行存储
kubectl create secret tls tls-secret
kubectl get secret
kubectl describe secret tls-secret

创建deployment、service和ingress的yaml资源
vim demo3.yaml
==========================================================
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: nginx-app
spec:
replicas: 2
template:
metadata:
labels:
name: nginx
spec:
containers:
- name: nginx
image: nginx
imagePullPolicy: IfNotPresent
ports:
- containerPort: 80
---
apiVersion: v1
kind: Service
metadata:
name: svc-3
spec:
ports:
- port: 80
targetPort: 80
protocol: TCP
selector:
name: nginx
---
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress3
spec:
tls:
- hosts:
- www.gxd222.com
secretName: tls-secret
rules:
- host: www.gxd222.com
http:
paths:
- path: /
backend:
serviceName: svc-3
servicePort: 80
==========================================================kubectl apply -f demo3.yaml
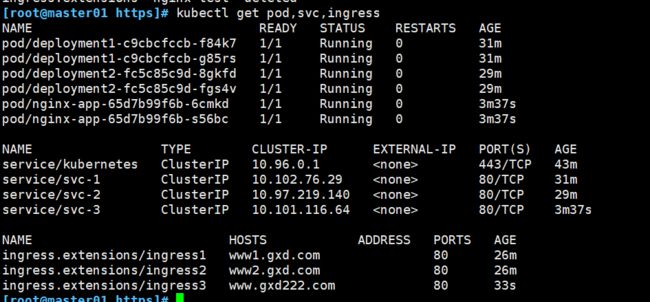
kubectl get pod,svc,ingress
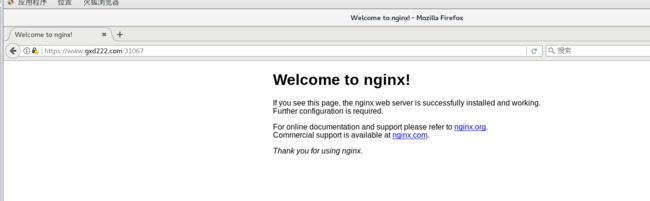
做端口映射并访问测试
echo '192.168.10.30 www.gxd222.com' >> /etc/hosts
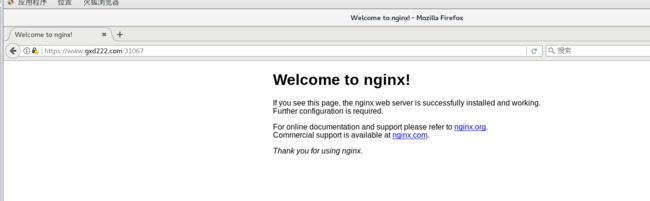
在浏览器访问 https://www.gxd222.com:31067
点击高级选项,确认安全例外即可
nginx进行BasicAuth(访问前输入用户和密码)
创建工作目录
mkdir /opt/ingress-nodeport/basic-auth
cd /opt/ingress-nodeport/basic-auth
生成用户密码文件,创建secret资源进行存储
yum install -y httpd
htpasswd -c auth gxd
kubectl create secret generic basic-auth
kubectl get secret
kubectl describe secret basic-auth

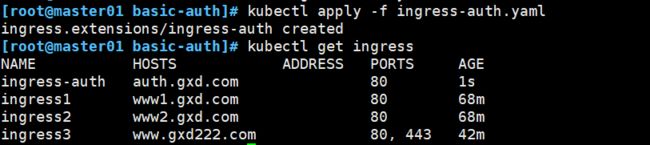
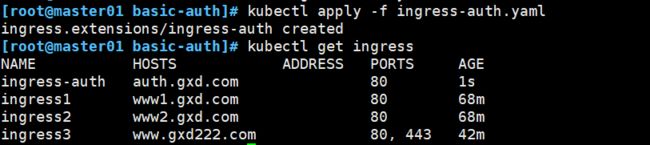
创建ingress资源
//具体详细设置方法可参考官网https://kubernetes.github.io/ingress-nginx/examples/auth/basic/
vim ingress-auth.yaml
==========================================================
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: ingress-auth
annotations:
nginx.ingress.kubernetes.io/auth-type: basic
nginx.ingress.kubernetes.io/auth-secret: basic-auth
nginx.ingress.kubernetes.io/auth-realm: 'Authentication Required - gxd'
spec:
rules:
- host: auth.gxd.com
http:
paths:
- path: /
backend:
serviceName: svc-2
servicePort: 80
==========================================================
kubectl apply -f ingress-auth.yaml
kubectl get ingress
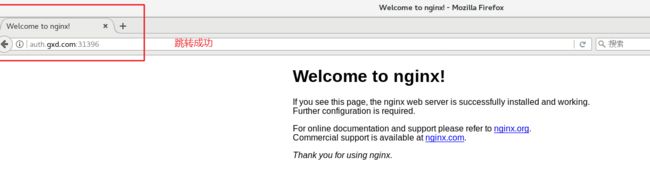
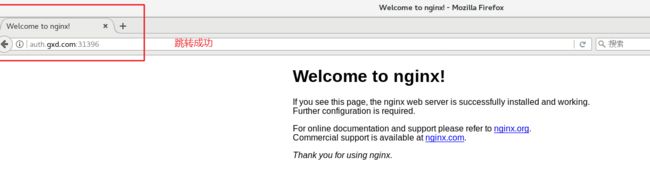
做端口映射并访问测试
echo '192.168.10.30 auth.gxd.com' >> /etc/hosts
在浏览器访问 http://auth.gxd.com:31396


nginx进行重写
配置说明
nginx.ingress.kubernetes.io/rewrite-target:<字符串>
nginx.ingress . kubernetes.io/ssl-redirect:<布尔值>指示位置部分是否仅可访问sSL(当Ingress包含证书时,默认为true)nginx.ingress . kubernetes.io/force-ssl-redirect:<布尔值>
nginx.ingress .kubernetes.io/app-root:<字符串>
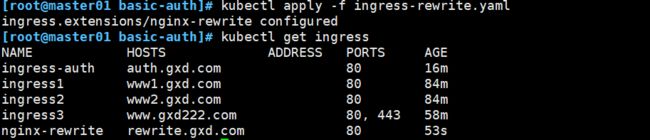
编写yaml文件
vim ingress-rewrite.yaml
==========================================================
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: nginx-rewrite
annotations:
nginx.ingress.kubernetes.io/rewrite-target: http://auth.gxd.com:31396
spec:
rules:
- host: rewrite.gxd.com
http:
paths:
- path: /
backend:
serviceName: ggggg
servicePort: 1111
==========================================================
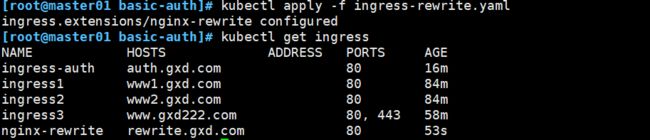
kubectl apply -f ingress-rewrite.yaml
kubectl get ingress
做端口映射并访问测试
echo '192.168.10.30 rewrite.gxd.com' >> /etc/hosts
在浏览器访问 http://rewrite.gxd.com