C/C++编程:libssh2学习(linux + clion + cmake)
文章目录
- 环境配置
- 使用
-
- 使用libssh2库实现支持密码参数的ssh2客户端
- 显示如何进行SSH2连接的示例
- 到目标主机上执行命令
- 参考
环境配置
3、开始:
$ wget https://www.libssh2.org/snapshots/libssh2-1.9.0-20210118.tar.gz
$ tar -xvf libssh2-1.9.0-20210118.tar.gz
$ cd libssh2-1.9.0-20210118/
// 前提是系统中有了 autoconf, automake and libtool
$ autoreconf -fi
$ ./configure
$ make
使用
使用libssh2库实现支持密码参数的ssh2客户端
工具:clion
2、cmakelist
cmake_minimum_required(VERSION 3.16)
project(ssh2_learn)
set(CMAKE_CXX_STANDARD 11)
include_directories(/usr/local/include)
link_directories(/usr/local/lib)
add_executable(${PROJECT_NAME} main.cpp)
target_link_libraries (${PROJECT_NAME} -lssh2)
3、main.cpp
#include \n\n"
struct termios _saved_tio;
int tio_saved = 0;
static int _raw_mode(void)
{
int rc;
struct termios tio;
rc = tcgetattr(fileno(stdin), &tio);
if (rc != -1) {
_saved_tio = tio;
tio_saved = 1;
cfmakeraw(&tio);
rc = tcsetattr(fileno(stdin), TCSADRAIN, &tio);
}
return rc;
}
static int _normal_mode(void)
{
if (tio_saved)
return tcsetattr(fileno(stdin), TCSADRAIN, &_saved_tio);
return 0;
}
int main (int argc, char *argv[])
{
int sock = 0;
unsigned long hostaddr = 0;
short port = 22;
char *username = NULL;
char *password = NULL;
struct sockaddr_in sin;
LIBSSH2_SESSION *session;
LIBSSH2_CHANNEL *channel;
int nfds = 1;
char buf;
LIBSSH2_POLLFD *fds = NULL;
/* Struct winsize for term size */
struct winsize w_size;
struct winsize w_size_bck;
/* For select on stdin */
fd_set set;
struct timeval timeval_out;
timeval_out.tv_sec = 0;
timeval_out.tv_usec = 10;
printf(COPYRIGHT);
if (argc > 4) {
hostaddr = inet_addr(argv[1]);
port = htons(atoi(argv[2]));
username = argv[3];
password = argv[4];
}
else {
fprintf(stderr, "Usage: %s ip port user password\n", basename(argv[0]));
return -1;
}
if (libssh2_init (0) != 0) {
fprintf (stderr, "libssh2 initialization failed\n");
return -1;
}
sock = socket (AF_INET, SOCK_STREAM, 0);
sin.sin_family = AF_INET;
sin.sin_port = port;
sin.sin_addr.s_addr = hostaddr;
if (connect(sock, (struct sockaddr *) &sin, sizeof(struct sockaddr_in)) != 0) {
fprintf (stderr, "Failed to established connection!\n");
return -1;
}
/* Open a session */
session = libssh2_session_init();
if (libssh2_session_startup (session, sock) != 0) {
fprintf(stderr, "Failed Start the SSH session\n");
return -1;
}
/* Authenticate via password */
if (libssh2_userauth_password(session, username, password) != 0) {
fprintf(stderr, "Failed to authenticate\n");
close(sock);
goto ERROR;
}
/* Open a channel */
channel = libssh2_channel_open_session(session);
if ( channel == NULL ) {
fprintf(stderr, "Failed to open a new channel\n");
close(sock);
goto ERROR;
}
/* Request a PTY */
if (libssh2_channel_request_pty( channel, "xterm") != 0) {
fprintf(stderr, "Failed to request a pty\n");
close(sock);
goto ERROR;
}
/* Request a shell */
if (libssh2_channel_shell(channel) != 0) {
fprintf(stderr, "Failed to open a shell\n");
close(sock);
goto ERROR;
}
if (_raw_mode() != 0) {
fprintf(stderr, "Failed to entered in raw mode\n");
close(sock);
goto ERROR;
}
while (1) {
FD_ZERO(&set);
FD_SET(fileno(stdin),&set);
ioctl(fileno(stdin), TIOCGWINSZ, &w_size);
if ((w_size.ws_row != w_size_bck.ws_row) ||
(w_size.ws_col != w_size_bck.ws_col)) {
w_size_bck = w_size;
libssh2_channel_request_pty_size(channel, w_size.ws_col, w_size.ws_row);
}
if ((fds = static_cast<LIBSSH2_POLLFD *>(malloc(sizeof(LIBSSH2_POLLFD)))) == NULL)
break;
fds[0].type = LIBSSH2_POLLFD_CHANNEL;
fds[0].fd.channel = channel;
fds[0].events = LIBSSH2_POLLFD_POLLIN;
fds[0].revents = LIBSSH2_POLLFD_POLLIN;
if (libssh2_poll(fds, nfds, 0) >0) {
libssh2_channel_read(channel, &buf, 1);
fprintf(stdout, "%c", buf);
fflush(stdout);
}
if (select(fileno(stdin)+1,&set,NULL,NULL,&timeval_out) > 0)
if (read(fileno(stdin), &buf, 1) > 0)
libssh2_channel_write(channel, &buf, 1);
free (fds);
if (libssh2_channel_eof(channel) == 1)
break;
}
if (channel) {
libssh2_channel_free (channel);
channel = NULL;
}
_normal_mode();
libssh2_exit();
return 0;
ERROR:
libssh2_session_disconnect(session, "Session Shutdown, Thank you for playing");
libssh2_session_free(session);
return -1;
}
使用libssh2库实现支持密码参数的ssh2客户端
显示如何进行SSH2连接的示例
https://github.com/libssh2/libssh2/blob/master/example/ssh2.c
工具:clion
1、创建一个工程,并将源码中的libssh2_config.h复制到目录中 (\libssh2-1.8.2\example\libssh2_config.h-----编译成功后libssh2_config.h.in生成的)
2、cmakelist
cmake_minimum_required(VERSION 3.16)
project(ssh2_learn)
set(CMAKE_CXX_STANDARD 11)
include_directories(/usr/local/include)
link_directories(/usr/local/lib)
add_executable(${PROJECT_NAME} main.cpp)
target_link_libraries (${PROJECT_NAME} -lssh2)
3、main.cpp
/*
*显示如何进行SSH2连接的示例。
*
*示例代码具有主机名,用户名,密码
*和复制路径的默认值,但是您可以在命令行上指定它们,例如:
*
* "ssh2 host user password [-p|-i|-k]"
*/
#include "libssh2_config.h"
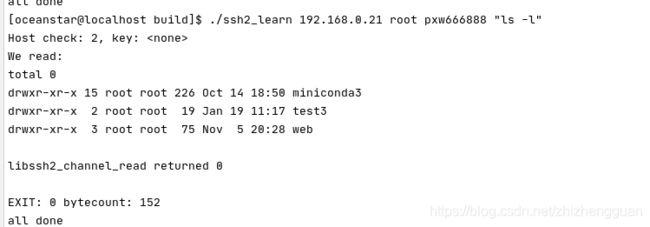
#include 到目标主机上执行命令
此例子为源码中的例子: https://github.com/libssh2/libssh2/blob/master/example/ssh2_exec.c
工具:clion
1、创建一个工程,并将源码中的libssh2_config.h复制到目录中
2、cmakelist
cmake_minimum_required(VERSION 3.16)
project(ssh2_learn)
set(CMAKE_CXX_STANDARD 11)
include_directories(/usr/local/include)
link_directories(/usr/local/lib)
add_executable(${PROJECT_NAME} main.cpp)
target_link_libraries (${PROJECT_NAME} -lssh2)
3、将https://github.com/libssh2/libssh2/blob/master/example/ssh2_exec.c拷贝到main.cpp中
/*
* Sample showing how to use libssh2 to execute a command remotely.
*
* The sample code has fixed values for host name, user name, password
* and command to run.
*
* Run it like this:
*
* $ ./ssh2_exec 127.0.0.1 user password "uptime"
*
*/
#include "libssh2_config.h"
#include " );
/*****
* At this point, we could verify that 'check' tells us the key is
* fine or bail out.
*****/
}
else {
/* eeek, do cleanup here */
return 3;
}
libssh2_knownhost_free(nh);
if ( strlen(password) != 0 ) {
/* We could authenticate via password */
while ((rc = libssh2_userauth_password(session, username, password)) ==
LIBSSH2_ERROR_EAGAIN);
if (rc) {
fprintf(stderr, "Authentication by password failed.\n");
goto shutdown;
}
}
else {
/* Or by public key */
while ((rc = libssh2_userauth_publickey_fromfile(session, username,
"/home/user/"
".ssh/id_rsa.pub",
"/home/user/"
".ssh/id_rsa",
password)) ==
LIBSSH2_ERROR_EAGAIN);
if (rc) {
fprintf(stderr, "\tAuthentication by public key failed\n");
goto shutdown;
}
}
#if 0
libssh2_trace(session, ~0 );
#endif
/* Exec non-blocking on the remove host */
while( (channel = libssh2_channel_open_session(session)) == NULL &&
libssh2_session_last_error(session,NULL,NULL,0) ==
LIBSSH2_ERROR_EAGAIN )
{
waitsocket(sock, session);
}
if( channel == NULL )
{
fprintf(stderr,"Error\n");
exit( 1 );
}
while( (rc = libssh2_channel_exec(channel, commandline)) ==
LIBSSH2_ERROR_EAGAIN )
{
waitsocket(sock, session);
}
if( rc != 0 )
{
fprintf(stderr,"Error\n");
exit( 1 );
}
for( ;; )
{
/* loop until we block */
int rc;
do
{
char buffer[0x4000];
rc = libssh2_channel_read( channel, buffer, sizeof(buffer) );
if( rc > 0 )
{
int i;
bytecount += rc;
fprintf(stderr, "We read:\n");
for( i=0; i < rc; ++i )
fputc( buffer[i], stderr);
fprintf(stderr, "\n");
}
else {
if( rc != LIBSSH2_ERROR_EAGAIN )
/* no need to output this for the EAGAIN case */
fprintf(stderr, "libssh2_channel_read returned %d\n", rc);
}
}
while( rc > 0 );
/* this is due to blocking that would occur otherwise so we loop on
this condition */
if( rc == LIBSSH2_ERROR_EAGAIN )
{
waitsocket(sock, session);
}
else
break;
}
exitcode = 127;
while( (rc = libssh2_channel_close(channel)) == LIBSSH2_ERROR_EAGAIN )
waitsocket(sock, session);
if( rc == 0 )
{
exitcode = libssh2_channel_get_exit_status( channel );
libssh2_channel_get_exit_signal(channel, &exitsignal,
NULL, NULL, NULL, NULL, NULL);
}
if (exitsignal)
fprintf(stderr, "\nGot signal: %s\n", exitsignal);
else
fprintf(stderr, "\nEXIT: %d bytecount: %d\n", exitcode, bytecount);
libssh2_channel_free(channel);
channel = NULL;
shutdown:
libssh2_session_disconnect(session,
"Normal Shutdown, Thank you for playing");
libssh2_session_free(session);
#ifdef WIN32
closesocket(sock);
#else
close(sock);
#endif
fprintf(stderr, "all done\n");
libssh2_exit();
return 0;
}
4、编译运行
参考
使用libssh2库实现支持密码参数的ssh2客户端
使用 libssh2 拷贝文件到不同机器(类似 scp)
libssh