esp8266(MQTT固件)通过at指令连接阿里云平台
使用记录
-
- esp8266模组
- 固件烧录工具准备
- 串口调试助手
- 阿里云账户及物联网设备申请
- 开启MQTT通信
-
- 方式一 阿里云直接获取连接参数
- 方式二 阿里云三元组计算连接参数
- 严重注意
实验:esp8266 连接阿里云。
准备工作:
- esp8266 wifi模组
- 固件烧录工具
- 串口调试助手
- 阿里云账号及物联网设备申请
esp8266模组
某宝随便买个,多的是:
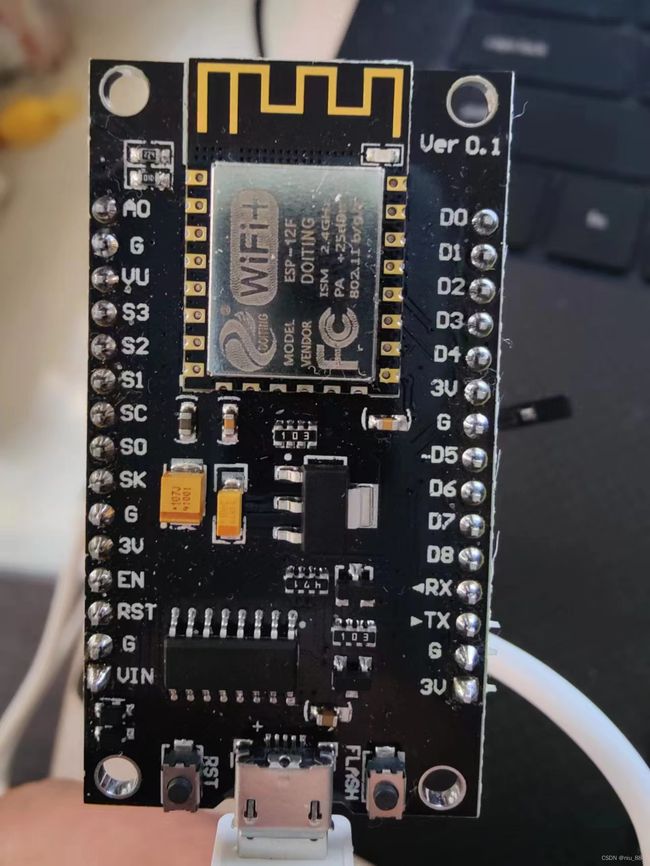
usb连接到电脑上之后,可以识别到串口,说明有固件。
固件烧录工具准备
由于新买的模组,芯片内的固件可能并不是我们想要的,此时可自行官网下载固件及烧录。
固件地址:https://docs.ai-thinker.com/%E5%9B%BA%E4%BB%B6%E6%B1%87%E6%80%BB
本人使用的固件: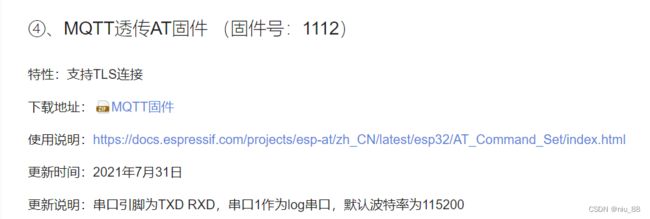
固件下载之后,需使用官方提供的烧录工具,地址:https://docs.ai-thinker.com/%E5%BC%80%E5%8F%91%E5%B7%A5%E5%85%B72
选择这个下载,具体使用方式网上很多。
上述两个即可烧录我们准备使用的固件。
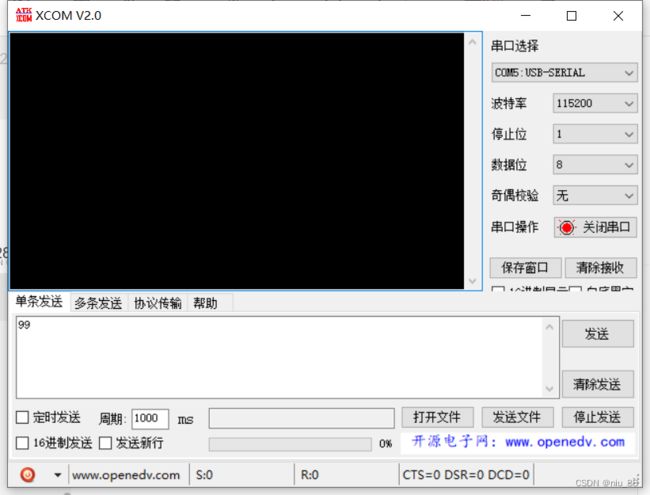
串口调试助手
阿里云账户及物联网设备申请
主要是物联网产品与设备的申请,具体详细步骤网上很多,不再啰嗦,看下图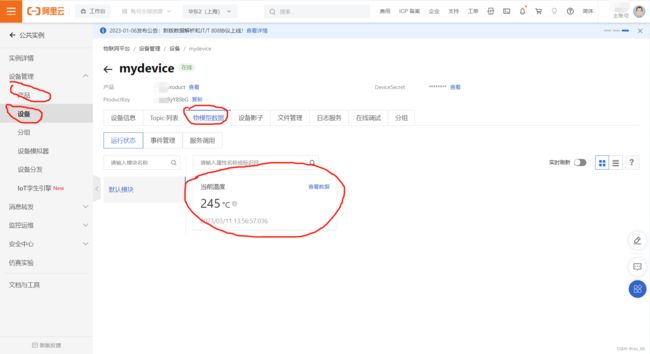
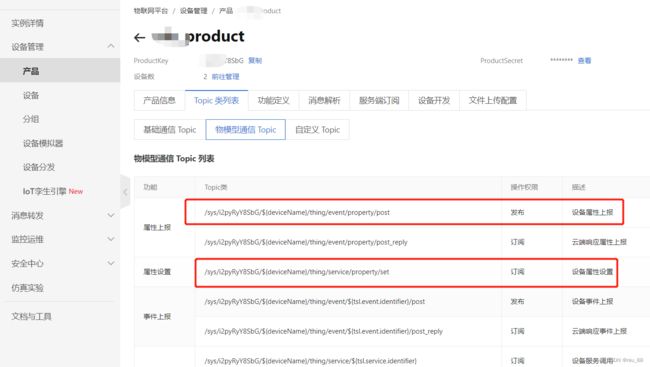
本人使用设备中的物模型,Topic使用物模型自带的:
开启MQTT通信
基本要使用的指令:
| 指令 | 含义 |
|---|---|
| AT\r\n | 测试 |
| AT+RST\r\n | 复位 |
| AT+GMR\r\n | 查询当前使用版本 |
| AT+CWMODE=1\r\n | 设置station模式,可以连接热点 |
| AT+CWJAP=“wifi”,“passwd”\r\n | 连接热点 |
| AT+MQTTUSERCFG=0,1,“clientId”,“username”,“password”,0,0,“”\r\n | 设置MQTT连接参数 |
| AT+MQTTSUB=0,“topic”,0\r\n | 订阅主题 |
| AT+MQTTPUB=0,“topic”,“msg”,0,0\r\n | 发布主题 |
| AT+MQTTCLEAN=0\r\n | 断开连接 |
| AT+MQTTCONN?\r\n | 查询连接 |
| AT+MQTTSUB?\r\n | 查询订阅的主题 |
方式一 阿里云直接获取连接参数
包括:clientId、username、passwd、mqttHostUrl、port
获取方式:

点击查看,则你所需要的都在里面:
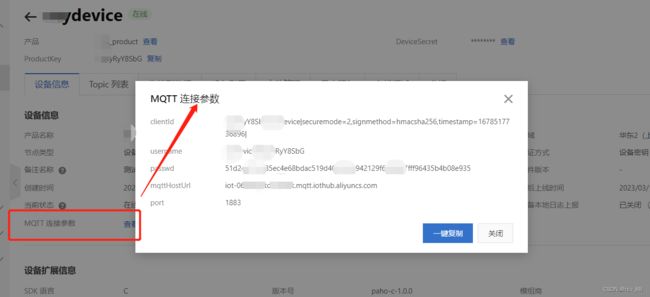
好了,开始连接,使用上面的命令一一对号即可:
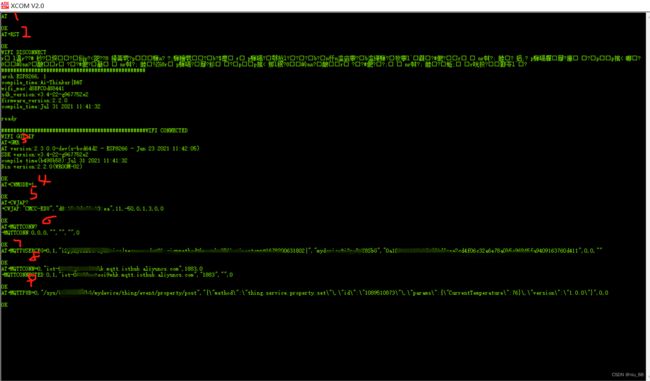
命令1:测试
命令2:复位
命令3:查询当前版本
命令4:设置wifi工作模式为station
命令5:查询是否连接wifi,没有的话,要连接,使用上述命令,本人已连接
命令6:查询MQTT是否连接
命令7:配置MQTT连接参数,使用上面获取到的clienId,username,passwd
命令8:连接MQTT,使用上面获取到的mqttHostUrl,port
命令9:向云端发布主题
云端是否收到主题消息?查看下图:
在未获取到主题之前,物模型中的温度是245

在主题发布之后(发布的主题中的温度是76),物模型中的温度变成了76,说明主题接收正常

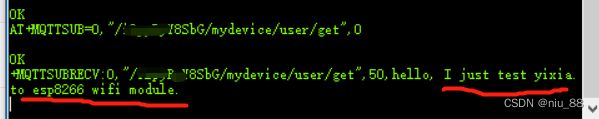
设备端订阅主题,可自行测试,留下截图:
订阅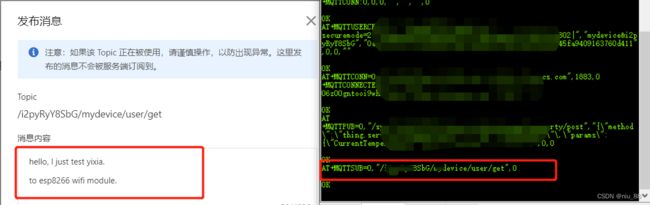
云端发布主题消息:
hello, I just test yixia.
to esp8266 wifi module.
方式二 阿里云三元组计算连接参数
计算方式很多,本人介绍其中一种通过c程序计算得到的参数。
三元组,即:
- ProductKey
- DeviceName
- DeviceSecret
在添加阿里云设备之后,这三个参数即可生成。
计算
aiot_mqtt_sign.c
/*
* Copyright (C) 2015-2019 Alibaba Group Holding Limited
*/
#include aiot_mqtt_sign.h
#ifndef __AIOT_MQTT_SIGN_H
#define __AIOT_MQTT_SIGN_H
int aiotMqttSign(const char *productKey, const char *deviceName, const char *deviceSecret,
char clientId[150], char username[64], char password[65]);
#endif
main.c
#include "aiot_mqtt_sign.h"
#include 填入三元组,即可编译生成所需要的clientId,username,passwd
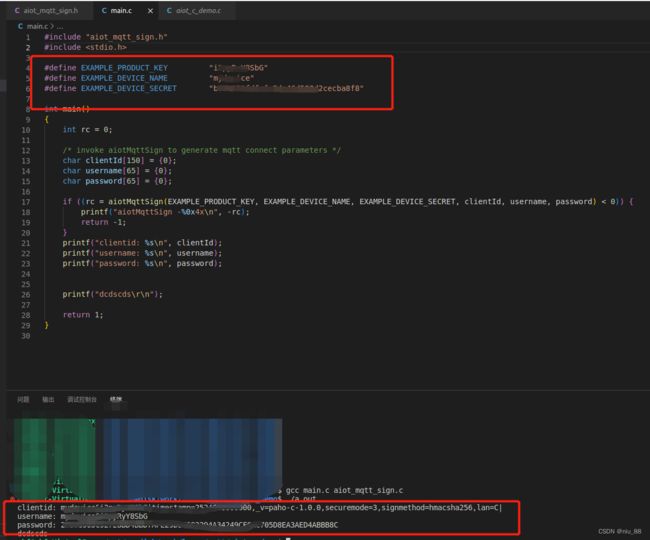
后面的步骤参数上面。
严重注意
有一个需要特别注意的点,就是at指令包含的字符串中的逗号(,)需要转义字符转换,不能直接使用,如:
"sfefr,rgtgt" //此处直接使用会有问题
'sfefr\,rgtgt' //此处使用正确