- 03-树1 树的同构
CO₂
PTA树的同构
03-树1树的同构(25分)给定两棵树,请你判断它们是否是同构的。输入格式:输入给出2棵二叉树树的信息。对于每棵树,首先在一行中给出一个非负整数N(≤10),即该树的结点数(此时假设结点从0到N−1编号);随后N行,第i行对应编号第i个结点,给出该结点中存储的1个英文大写字母、其左孩子结点的编号、右孩子结点的编号。如果孩子结点为空,则在相应位置上给出“-”。给出的数据间用一个空格分隔。注意:题目保
- Hbase - 表导出CSV数据
kikiki1
新鲜文章,昨天刚经过线上验证过的,使用它导出了3亿的用户数据出来,花了半个小时,性能还是稳稳的,好了不吹牛皮了,直接上代码吧。MR考查了Hbase的各种MR,没有发现哪一个是能实现的,如果有请通知我,我给他发红包。所以我们只能自己来写一个MR了,编写一个Hbase的MR,官方文档上也有相应的例子。我们用来加以化妆就得到我们想要的了。导出的CSV格式为admin,22,北京admin,23,天津依赖
- 十种常用数据分析模型
耐思nice~
数据分析数据分析人工智能机器学习数学建模
1-线性回归(LinearRegression)场景:预测商品销售额优点:简单易用,结果易于解释缺点:假设线性关系,容易受到异常值影响概念:建立自变量和因变量之间线性关系的模型。公式:[y=b_0+b_1x_1+b_2x_2+...+b_nx_n]代码示例:importpandasaspdfromsklearn.linear_modelimportLinearRegressionfromsklea
- 什么是网关,网关有哪些作用?
oneday&oneday
微服务面试经验分享网络
网关(Gateway)是在计算机网络中用于连接两个独立的网络的设备,它能够在两个不同协议的网络之间传递数据。在互联网中,网关是一个可以连接不同协议的网络的设备,比如说可以连接局域网和互联网,它可以把局域网的内部网络地址转换成互联网上的合法地址,从而使得局域网内的主机可以与外界通信。在计算机系统中,网关可以用于实现负载均衡、安全过滤、协议转换等功能。具体来说,网关可以分为以下几种:应用网关:用于应用
- 哈马斯和真主党官员曝伊朗安全官员策划了对以色列的突袭
聚百宝国际时事谈
《华尔街日报》报道哈马斯和真主党高级成员称伊朗安全官员帮助策划了周六哈马斯对以色列的突然袭击并于上周一在贝鲁特举行的一次会议上批准了这次袭击哈马斯领导人伊斯梅尔·哈尼亚表示哈马斯正处于伟大胜利的边缘伊朗制造的产品由伊朗伊斯兰共和国船只从沙希德·拉吉或霍梅尼港运输到叙利亚拉塔基亚然后从那里运往黎巴嫩南部打击区域与阿尔塔巴兹卸载iSO集装箱的港口区域完全匹配真主党精锐特种部队拉杜安部队已部署到与以色列
- C++ 数组详解:从基础到实战
光の
javajvm前端
一、数组的定义与核心特性(一)什么是数组?数组(Array)是C++中用于存储一组相同类型元素的连续内存空间。它通过一个统一的名称(数组名)和索引(下标)来访问每个元素,是实现批量数据管理的基础工具。(二)核心特性特性说明同类型所有元素必须是同一数据类型(如int、double)连续性元素在内存中连续存放,地址递增(&arr[i+1]=&arr[i]+sizeof(类型))固定大小数组声明时需指定
- 碰一碰发视频、碰一碰写好评源码搭建技术开发,支持OEM贴牌
18538162800余+
音视频矩阵线性代数
在移动互联网时代,便捷的交互体验成为吸引用户的关键。“碰一碰发视频”与“碰一碰写好评”功能借助近场通信(NFC)等技术,为用户带来了全新的操作体验,同时也为商家和内容创作者开辟了高效的推广与互动途径。本文将深入探讨这两项功能背后的技术开发要点。一、核心技术基础1.NFC近场通信技术NFC技术是实现碰一碰交互的基石。它基于ISO14443等协议,让设备在短距离(通常为10厘米以内)内进行安全的数据交
- HTTPS,不可或缺的数据安全锁
Arwen303
SSL证书https网络协议http
一、HTTPS:数字时代的"隐形护卫"在网购时输入银行卡信息、登录社交平台发送私信、通过企业OA系统上传文件,这些日常操作背后都藏着一把无形的"安全锁"——HTTPS。↓https://www.joyssl.com/certificate/select/joyssl-dv-single-free-1.html?nid=59↑(注册码230959,赠送1个月有效期)它如同数据传输的"保险箱",在客户
- SSL证书有效期降到47天?企业单位该如何应对!
一觉醒来,天可能都要塌了?就在4月12日,CA/B论坛(负责管理SSL/TLS证书的行业组织)的服务器证书工作组投票通过了SC-081v3提案,从2026年3月14日开始,SSL/TLS证书的有效期将会从目前的最高398天缩短至47天,SANs(域名/IP)验证数据重复使用期限则会从398天缩短到10天。一、可能影响分析安全风险浏览器警告:当证书过期后,用户访问网站时会收到“不安全”提示,导致流量
- 还在了解什么是SSL证书嘛?一篇文章让你简洁明了的认识SSL
一、SSL基础概念1.SSL的定义SSL(SecureSocketsLayer)是一种安全协议,用于在客户端(如浏览器)与服务器之间建立加密通信。它通过数据加密、身份验证和完整性保护,确保网络传输的安全性。2.SSL与TLS的关系SSL:由网景公司于1994年开发,最后一个版本是SSL3.0。TLS(TransportLayerSecurity):SSL的升级版,由IETF标准化。目前主流版本是T
- 代码签名:保障软件安全与可信的关键防线
Arwen303
代码签名SSL证书ssl网络协议网络
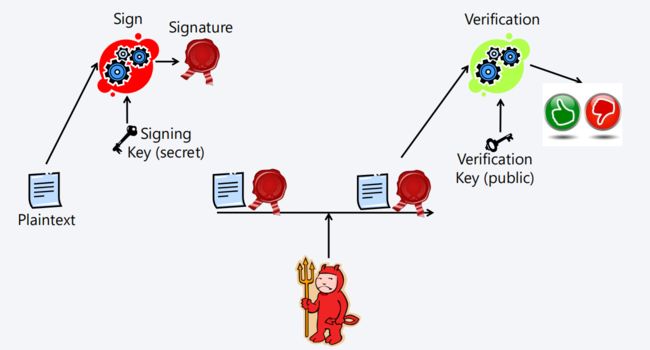
在当今数字化时代,软件应用广泛渗透于各个领域,其安全性与可信度至关重要。代码签名作为一项核心技术手段,犹如软件世界的“数字身份证”,为软件的合法身份与完整性保驾护航。一、代码签名介绍(一)定义与原理代码签名是一种通过数字证书对软件代码进行数字签名的技术。它利用公钥加密体系,开发者使用私钥对代码进行签名,而用户端则通过对应的公钥来验证签名的有效性。当软件被签署后,任何对代码的篡改都会导致签名验证失败
- MySQL主从模式的数据一致性
mysia
MySQL单机的数据一致性MySQL作为一个可插拔的数据库系统,支持插件式的存储引擎,在设计上分为Server层和StorageEngine层。在Server层,MySQL以events的形式记录数据库各种操作的Binlog二进制日志,其基本核心作用有:复制和备份。除此之外,我们结合多样化的业务场景需求,基于Binlog的特性构建了强大的MySQL生态,如:DTS、单元化、异构系统之间实时同步等等
- Java实习模拟面试之创玖科技:前后端交互、数据库、Spring全家桶、性能优化与Linux实战
培风图南以星河揽胜
java面试java面试科技
关键词:JavaScript、JQuery、Ajax、Node.js、MySQL、Oracle、Spring、SpringMVC、SpringBoot、MyBatis、Tomcat、Redis、Nginx、Linux、Git、SAAS系统开发一、面试开场:自我介绍面试官提问:请做个自我介绍,重点突出你的技术栈和项目经验。候选人回答:您好,我是一名计算机科学与技术专业的应届生,具备扎实的Java基础
- Java与机器学习的邂逅:Weka框架入门指南
墨夶
Java学习资料1java机器学习数据挖掘
在这个数据驱动的时代,机器学习已经成为各行业创新和优化的关键技术。而Java,作为一门成熟且广泛应用的编程语言,在企业级应用开发中占据着重要地位。将二者结合起来,利用Java实现机器学习算法,不仅可以充分发挥其强大的生态系统优势,还能为开发者提供一个高效、稳定的开发环境。今天,我们将带您走进Java与机器学习的世界,探索如何使用Weka这一著名的机器学习库来开启您的智能之旅。Weka简介及其优势什
- (C++)list,vector,set,map四种容器的应用——教务管理系统(测试版)(list基础教程)(vector基础教程)(set基础教程)(map基础教程)(STL库教程)
双叶836
STLC++C++基础教学C++项目c++list开发语言数据结构c语言
目录源代码:代码详解:第1步:搭建基础框架和数据结构目标:定义数据结构和全局容器练习任务:第2步:实现学生管理功能(使用map)目标:添加学生和显示学生列表练习任务:第3步:实现课程管理功能(使用vector)目标:添加课程和显示课程列表练习任务:第4步:实现选课功能(使用list)目标:学生选课和退课功能练习任务:主函数:多说一点(重点代码解释):一.list>enrollments;代码详解1
- JavaScript的介绍及嵌入方式
紫罗兰丶
JavaScript介绍JavaScript是运行在浏览器端的脚步语言,JavaScript主要解决的是前端与用户交互的问题,包括使用交互与数据交互。JavaScript是浏览器解释执行的,前端脚本语言还有JScript(微软,IE独有),ActionScript(Adobe公司,需要插件)等。JavaScript嵌入页面的方式1.页面script标签嵌入vara="你好!"2.外部引用
- Java 二维数组详解:从基础语法到实战应用,彻底掌握多维数据结构
大葱白菜
java合集开发语言java后端学习个人开发
作为一名Java开发工程师,你一定在实际开发中遇到过需要处理表格、矩阵、图像像素、游戏地图等场景。这时候,二维数组(2DArray)就派上用场了。本文将带你全面掌握:Java中二维数组的定义与初始化方式二维数组的内存结构与访问机制二维数组的遍历、修改与扩容技巧二维数组在实际业务中的应用场景二维数组与集合类(如List>)的互转常见误区与最佳实践并通过丰富的代码示例和真实项目场景讲解,帮助你写出更高
- 机器学习基础:从数据到智能的入门指南
一、何谓机器学习在我们的日常生活中,机器学习的身影无处不在。当你打开购物软件,它总能精准推荐你可能喜欢的商品;当你解锁手机,人脸识别瞬间完成;当你使用语音助手,它能准确理解你的指令。这些背后,都离不开机器学习的支撑。机器学习是一门让计算机能够从数据中学习并改进的学科。随着传感器技术的飞速发展,我们身边充满了各种传感器,如手机中的摄像头、麦克风,交通监控中的传感器等,它们收集了海量的数据。这些数据就
- HTTPS协议的应用场景分析
Arwen303
https网络协议http
HTTPS协议的应用场景分析一、Web服务与交互网页浏览场景:用户通过浏览器访问各类网站(如门户网站、资讯平台),传输HTML、CSS、JavaScript等静态资源。应用:主流网站普遍采用HTTPS,确保页面内容安全加载。例如,Wikipedia、新浪等站点通过HTTPS防止内容被篡改。安全需求:防止页面被中间人劫持植入恶意广告或脚本。在线表单与用户登录场景:用户提交注册表单、登录账号时传输用户
- Vue3递归组件详解:构建动态树形结构的终极方案
编程随想▿
Vue3vue.js前端javascript前端框架
目录一、什么是递归组件?二、Vue3递归组件实现步骤1.基础实现2.关键点解析三、动态数据实战:渲染树形菜单四、Vue3递归组件的核心注意事项五、高级技巧:异步递归组件六、常见问题排查结语一、什么是递归组件?递归组件是指在组件内部调用自身的特殊组件。它适用于处理嵌套树形数据结构的场景,例如:文件目录系统多级导航菜单组织架构图嵌套评论列表在Vue3中,递归组件通过name属性标识自身,实现模板自引用
- 【k8s学习】Kubernetes新手学习,4小时视频笔记总结
伊丽莎白2015
【学习视频地址】KubernetesTutorialforBeginnersFULLCOURSEin4Hours视频不一定打得开,不过我笔记也很详细了。【笔记内容】1-【k8s学习】Kubernetes学习——核心组件和架构2-【k8s学习】minikube、kubectl、yaml配置文件的介绍3-【k8s学习】在minikube上布署MongoDB和MongoExpress4-【k8s学习】k
- 胡可:跟孩子说一百遍“别跟陌生人走”都没用,你要这么做
妈妈在呀
《不可思议的妈妈》综艺节目里面有一期是关于孩子的安全教育问题,非常引人深思。虽然我们平常都会和孩子说,“不要给陌生人开门,不要拿陌生人的东西。”可是我们从来不知道,这样的反复叮咛到底有没有用。为了测试妈妈们说的话,孩子们到底记住没有,节目组决定找工作人员假扮“坏人”,来一场实打实的安全测试。结果出乎妈妈们意料,孩子们太容易骗了!尽管何洁在离开前,反复告诉七宝,“谁敲门都不许开门。陌生人给的东西不能
- 公路桥梁施工质量管理与控制方法分析
阿卞是宝藏啊
本文还有配套的精品资源,点击获取简介:本文深入探讨了公路桥梁施工中如何实施有效的质量管理与控制,强调了质量管理的重要性,详述了质量控制的理论基础,并概述了施工前后质量策划、材料与设备质量控制、施工过程监控、质量信息管理、问题处理与改进、竣工验收及后期维护的方法。强调了全面质量管理理论与现代信息技术的应用,旨在确保工程安全、可靠与耐久。1.质量管理的重要性1.1市场竞争中的质量要素在当今竞争日益激烈
- ORACLE物化视图materialized view
Caster_Z
oracle
物化视图会占用空间,一半可用于大量数据查询时,减缓主表的查询压力使用。例如创建一个物化视图,让对接单位查询。ONDEMAND:仅在该物化视图“需要”被刷新了,才进行刷新(REFRESH),即更新物化视图,以保证和基表数据的一致性;ONCOMMIT:一旦基表有了COMMIT,即事务提交,则立刻刷新,立刻更新物化视图,使得数据和基表一致。1,创建creatematerializedviewmv_nam
- 多云环境下的统一安全架构设计
TechVision大咖圈
安全架构多云安全合规性统一架构零信任深度防御身份管理
关键词:多云安全、统一架构、零信任、深度防御、身份管理、威胁检测、SIEM、合规性文章目录引言:多云时代的安全挑战多云环境面临的安全挑战统一安全架构设计原则核心安全组件架构多层防护体系设计统一身份管理与访问控制安全监控与威胁检测实施策略与最佳实践总结与展望引言:多云时代的安全挑战在这个"云来云去"的时代,企业就像搬家一样,从单一的云服务商逐渐向多云架构迁移。就好比以前只在一家银行存钱,现在为了"不
- 老鼠记者之神勇鼠者胜海盗猫 读后感
可愛的小秋
杰罗尼摩•斯蒂顿出生在一个老鼠导的描述成,他非常善良,他是《鼠民公报》给老板。他很讨厌旅行,但每次总被别人拉走。这一次,他和他的妹妹菲、表弟赖皮和小侄儿本杰明一起踏上了航海的旅途。他们而且还打败了海盗猫,带回了许多东西安全的回到了家。在这本书里,我很喜欢本杰明。从书中得知,本杰明是一个善于思考、现学现用的一个小老鼠。他也很喜欢看书,许多都是从书里的知识得到的办法。而菲和赖皮去本杰明截然不同,他们旅
- 酒厂生产信息化系统方案
liu854046222
技术解决方案大数据人工智能
一、背景目标白酒作为中国传统的高度酒精饮料,其生产过程复杂且历史悠久。随着消费者对高品质白酒的需求不断增长,以及食品安全和质量监管的日益严格,酒厂面临着提升产品品质、确保生产安全、提高生产效率和降低成本的多重挑战。为了满足市场需求,酒厂需要对原材料进行严格分析和追溯,优化生产流程,并通过数据收集和分析来持续改进生产工艺。目标:原材料优化:通过对原料的深入分析,选择最佳的原料组合,确保白酒的独特风味
- 数据并表技术全面指南:从基础JOIN到分布式数据融合
熊猫钓鱼>_>
分布式
引言在现代数据处理和分析领域,数据并表(TableJoin)技术是连接不同数据源、整合分散信息的核心技术。随着企业数据规模的爆炸式增长和数据源的日益多样化,传统的数据并表方法面临着前所未有的挑战:性能瓶颈、内存限制、数据倾斜、一致性问题等。如何高效、准确地进行大规模数据并表,已成为数据工程师和架构师必须掌握的关键技能。数据并表不仅仅是简单的SQLJOIN操作,它涉及数据建模、算法优化、分布式计算、
- 【Java-多线程】什么是幂等性?
以下是关于幂等性的详细解析:一、幂等性定义幂等性(Idempotence)是指同一操作多次执行所产生的影响与一次执行的效果相同。就像数学中的乘法运算:1×1×1=1,无论乘多少次结果都不变。二、生活化案例外卖订单场景:用户点击"支付"按钮时网络抖动支付系统收到两次相同支付请求如果接口没有幂等性:可能扣除双倍金额具备幂等性的系统:即使收到多次请求,只扣款一次三、技术实现方案1.数据库唯一约束CREA
- 聊天兼职赚钱是真的吗(揭秘兼职聊天赚钱真相)
多职猫
聊天兼职赚钱是真的吗(揭秘兼职聊天赚钱真相)各种兼职赚钱的方式也层出不穷。其中,以聊天兼职为代表的新型兼职方式备受关注。但是,究竟聊天兼职赚钱是真的还是只是一场骗局?本文将深入揭秘,让你了解聊天兼职的真相。推荐一篇找兼职必看的免费教程:《手机兼职,300-500/天,一单一结,大量要人》,在这里可以找到各种数据标注兼职,作业批改兼职,手机聊天兼职等适合大家的岗位1.聊天兼职的诱惑聊天兼职在广告中常
- 怎么样才能成为专业的程序员?
cocos2d-x小菜
编程PHP
如何要想成为一名专业的程序员?仅仅会写代码是不够的。从团队合作去解决问题到版本控制,你还得具备其他关键技能的工具包。当我们询问相关的专业开发人员,那些必备的关键技能都是什么的时候,下面是我们了解到的情况。
关于如何学习代码,各种声音很多,然后很多人就被误导为成为专业开发人员懂得一门编程语言就够了?!呵呵,就像其他工作一样,光会一个技能那是远远不够的。如果你想要成为
- java web开发 高并发处理
BreakingBad
javaWeb并发开发处理高
java处理高并发高负载类网站中数据库的设计方法(java教程,java处理大量数据,java高负载数据) 一:高并发高负载类网站关注点之数据库 没错,首先是数据库,这是大多数应用所面临的首个SPOF。尤其是Web2.0的应用,数据库的响应是首先要解决的。 一般来说MySQL是最常用的,可能最初是一个mysql主机,当数据增加到100万以上,那么,MySQL的效能急剧下降。常用的优化措施是M-S(
- mysql批量更新
ekian
mysql
mysql更新优化:
一版的更新的话都是采用update set的方式,但是如果需要批量更新的话,只能for循环的执行更新。或者采用executeBatch的方式,执行更新。无论哪种方式,性能都不见得多好。
三千多条的更新,需要3分多钟。
查询了批量更新的优化,有说replace into的方式,即:
replace into tableName(id,status) values
- 微软BI(3)
18289753290
微软BI SSIS
1)
Q:该列违反了完整性约束错误;已获得 OLE DB 记录。源:“Microsoft SQL Server Native Client 11.0” Hresult: 0x80004005 说明:“不能将值 NULL 插入列 'FZCHID',表 'JRB_EnterpriseCredit.dbo.QYFZCH';列不允许有 Null 值。INSERT 失败。”。
A:一般这类问题的存在是
- Java中的List
g21121
java
List是一个有序的 collection(也称为序列)。此接口的用户可以对列表中每个元素的插入位置进行精确地控制。用户可以根据元素的整数索引(在列表中的位置)访问元素,并搜索列表中的元素。
与 set 不同,列表通常允许重复
- 读书笔记
永夜-极光
读书笔记
1. K是一家加工厂,需要采购原材料,有A,B,C,D 4家供应商,其中A给出的价格最低,性价比最高,那么假如你是这家企业的采购经理,你会如何决策?
传统决策: A:100%订单 B,C,D:0%
&nbs
- centos 安装 Codeblocks
随便小屋
codeblocks
1.安装gcc,需要c和c++两部分,默认安装下,CentOS不安装编译器的,在终端输入以下命令即可yum install gccyum install gcc-c++
2.安装gtk2-devel,因为默认已经安装了正式产品需要的支持库,但是没有安装开发所需要的文档.yum install gtk2*
3. 安装wxGTK
yum search w
- 23种设计模式的形象比喻
aijuans
设计模式
1、ABSTRACT FACTORY—追MM少不了请吃饭了,麦当劳的鸡翅和肯德基的鸡翅都是MM爱吃的东西,虽然口味有所不同,但不管你带MM去麦当劳或肯德基,只管向服务员说“来四个鸡翅”就行了。麦当劳和肯德基就是生产鸡翅的Factory 工厂模式:客户类和工厂类分开。消费者任何时候需要某种产品,只需向工厂请求即可。消费者无须修改就可以接纳新产品。缺点是当产品修改时,工厂类也要做相应的修改。如:
- 开发管理 CheckLists
aoyouzi
开发管理 CheckLists
开发管理 CheckLists(23) -使项目组度过完整的生命周期
开发管理 CheckLists(22) -组织项目资源
开发管理 CheckLists(21) -控制项目的范围开发管理 CheckLists(20) -项目利益相关者责任开发管理 CheckLists(19) -选择合适的团队成员开发管理 CheckLists(18) -敏捷开发 Scrum Master 工作开发管理 C
- js实现切换
百合不是茶
JavaScript栏目切换
js主要功能之一就是实现页面的特效,窗体的切换可以减少页面的大小,被门户网站大量应用思路:
1,先将要显示的设置为display:bisible 否则设为none
2,设置栏目的id ,js获取栏目的id,如果id为Null就设置为显示
3,判断js获取的id名字;再设置是否显示
代码实现:
html代码:
<di
- 周鸿祎在360新员工入职培训上的讲话
bijian1013
感悟项目管理人生职场
这篇文章也是最近偶尔看到的,考虑到原博客发布者可能将其删除等原因,也更方便个人查找,特将原文拷贝再发布的。“学东西是为自己的,不要整天以混的姿态来跟公司博弈,就算是混,我觉得你要是能在混的时间里,收获一些别的有利于人生发展的东西,也是不错的,看你怎么把握了”,看了之后,对这句话记忆犹新。 &
- 前端Web开发的页面效果
Bill_chen
htmlWebMicrosoft
1.IE6下png图片的透明显示:
<img src="图片地址" border="0" style="Filter.Alpha(Opacity)=数值(100),style=数值(3)"/>
或在<head></head>间加一段JS代码让透明png图片正常显示。
2.<li>标
- 【JVM五】老年代垃圾回收:并发标记清理GC(CMS GC)
bit1129
垃圾回收
CMS概述
并发标记清理垃圾回收(Concurrent Mark and Sweep GC)算法的主要目标是在GC过程中,减少暂停用户线程的次数以及在不得不暂停用户线程的请夸功能,尽可能短的暂停用户线程的时间。这对于交互式应用,比如web应用来说,是非常重要的。
CMS垃圾回收针对新生代和老年代采用不同的策略。相比同吞吐量垃圾回收,它要复杂的多。吞吐量垃圾回收在执
- Struts2技术总结
白糖_
struts2
必备jar文件
早在struts2.0.*的时候,struts2的必备jar包需要如下几个:
commons-logging-*.jar Apache旗下commons项目的log日志包
freemarker-*.jar
- Jquery easyui layout应用注意事项
bozch
jquery浏览器easyuilayout
在jquery easyui中提供了easyui-layout布局,他的布局比较局限,类似java中GUI的border布局。下面对其使用注意事项作简要介绍:
如果在现有的工程中前台界面均应用了jquery easyui,那么在布局的时候最好应用jquery eaysui的layout布局,否则在表单页面(编辑、查看、添加等等)在不同的浏览器会出
- java-拷贝特殊链表:有一个特殊的链表,其中每个节点不但有指向下一个节点的指针pNext,还有一个指向链表中任意节点的指针pRand,如何拷贝这个特殊链表?
bylijinnan
java
public class CopySpecialLinkedList {
/**
* 题目:有一个特殊的链表,其中每个节点不但有指向下一个节点的指针pNext,还有一个指向链表中任意节点的指针pRand,如何拷贝这个特殊链表?
拷贝pNext指针非常容易,所以题目的难点是如何拷贝pRand指针。
假设原来链表为A1 -> A2 ->... -> An,新拷贝
- color
Chen.H
JavaScripthtmlcss
<!DOCTYPE HTML PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd"> <HTML> <HEAD>&nbs
- [信息与战争]移动通讯与网络
comsci
网络
两个坚持:手机的电池必须可以取下来
光纤不能够入户,只能够到楼宇
建议大家找这本书看看:<&
- oracle flashback query(闪回查询)
daizj
oracleflashback queryflashback table
在Oracle 10g中,Flash back家族分为以下成员:
Flashback Database
Flashback Drop
Flashback Table
Flashback Query(分Flashback Query,Flashback Version Query,Flashback Transaction Query)
下面介绍一下Flashback Drop 和Flas
- zeus持久层DAO单元测试
deng520159
单元测试
zeus代码测试正紧张进行中,但由于工作比较忙,但速度比较慢.现在已经完成读写分离单元测试了,现在把几种情况单元测试的例子发出来,希望有人能进出意见,让它走下去.
本文是zeus的dao单元测试:
1.单元测试直接上代码
package com.dengliang.zeus.webdemo.test;
import org.junit.Test;
import o
- C语言学习三printf函数和scanf函数学习
dcj3sjt126com
cprintfscanflanguage
printf函数
/*
2013年3月10日20:42:32
地点:北京潘家园
功能:
目的:
测试%x %X %#x %#X的用法
*/
# include <stdio.h>
int main(void)
{
printf("哈哈!\n"); // \n表示换行
int i = 10;
printf
- 那你为什么小时候不好好读书?
dcj3sjt126com
life
dady, 我今天捡到了十块钱, 不过我还给那个人了
good girl! 那个人有没有和你讲thank you啊
没有啦....他拉我的耳朵我才把钱还给他的, 他哪里会和我讲thank you
爸爸, 如果地上有一张5块一张10块你拿哪一张呢....
当然是拿十块的咯...
爸爸你很笨的, 你不会两张都拿
爸爸为什么上个月那个人来跟你讨钱, 你告诉他没
- iptables开放端口
Fanyucai
linuxiptables端口
1,找到配置文件
vi /etc/sysconfig/iptables
2,添加端口开放,增加一行,开放18081端口
-A INPUT -m state --state NEW -m tcp -p tcp --dport 18081 -j ACCEPT
3,保存
ESC
:wq!
4,重启服务
service iptables
- Ehcache(05)——缓存的查询
234390216
排序ehcache统计query
缓存的查询
目录
1. 使Cache可查询
1.1 基于Xml配置
1.2 基于代码的配置
2 指定可搜索的属性
2.1 可查询属性类型
2.2 &
- 通过hashset找到数组中重复的元素
jackyrong
hashset
如何在hashset中快速找到重复的元素呢?方法很多,下面是其中一个办法:
int[] array = {1,1,2,3,4,5,6,7,8,8};
Set<Integer> set = new HashSet<Integer>();
for(int i = 0
- 使用ajax和window.history.pushState无刷新改变页面内容和地址栏URL
lanrikey
history
后退时关闭当前页面
<script type="text/javascript">
jQuery(document).ready(function ($) {
if (window.history && window.history.pushState) {
- 应用程序的通信成本
netkiller.github.com
虚拟机应用服务器陈景峰netkillerneo
应用程序的通信成本
什么是通信
一个程序中两个以上功能相互传递信号或数据叫做通信。
什么是成本
这是是指时间成本与空间成本。 时间就是传递数据所花费的时间。空间是指传递过程耗费容量大小。
都有哪些通信方式
全局变量
线程间通信
共享内存
共享文件
管道
Socket
硬件(串口,USB) 等等
全局变量
全局变量是成本最低通信方法,通过设置
- 一维数组与二维数组的声明与定义
恋洁e生
二维数组一维数组定义声明初始化
/** * */ package test20111005; /** * @author FlyingFire * @date:2011-11-18 上午04:33:36 * @author :代码整理 * @introduce :一维数组与二维数组的初始化 *summary: */ public c
- Spring Mybatis独立事务配置
toknowme
mybatis
在项目中有很多地方会使用到独立事务,下面以获取主键为例
(1)修改配置文件spring-mybatis.xml <!-- 开启事务支持 --> <tx:annotation-driven transaction-manager="transactionManager" /> &n
- 更新Anadroid SDK Tooks之后,Eclipse提示No update were found
xp9802
eclipse
使用Android SDK Manager 更新了Anadroid SDK Tooks 之后,
打开eclipse提示 This Android SDK requires Android Developer Toolkit version 23.0.0 or above, 点击Check for Updates
检测一会后提示 No update were found