GitOps应用实践系列-Argo CD 实践篇
大家好,我是张晋涛。
在前两篇内容中,我分别为大家介绍了 GitOps 的概念用于实施 GitOps 的工具 Argo CD
创建集群
我们通过 KIND(Kubernetes in Docker)工具创建一个用于本地测试的 Kubernetes 集群。使用如下的配置文件,创建一个包含一个 control plane 和三个 work 的集群。
kind: Cluster
apiVersion: kind.x-k8s.io/v1alpha4
nodes:
- role: control-plane
- role: worker
- role: worker
- role: worker使用如下命令进行集群的创建:
➜ (MoeLove) kind create cluster --config=kind-config.yaml
Creating cluster "kind" ...
✓ Ensuring node image (kindest/node:v1.20.2)
✓ Preparing nodes
✓ Writing configuration
✓ Starting control-plane ️
✓ Installing CNI
✓ Installing StorageClass
✓ Joining worker nodes
Set kubectl context to "kind-kind"
You can now use your cluster with:
kubectl cluster-info --context kind-kind
Have a nice day! 执行如下命令等待集群完全 Ready:
➜ (MoeLove) kubectl wait --for=condition=Ready nodes --all部署 Argo CD
待集群状态完全 Ready 后,开始进行 Argo CD 的部署。我们创建一个名为 argocd 的 namespace。
部署
这里可以直接使用 Argo CD 项目中提供的部署文件进行安装。这里需要注意的是 此部署文件中 RBA 的配置中引用了 argocd 这个 namespace,所以如果你是将它部署到其他 namespace 中,那一定要进行对应的修改。
➜ (MoeLove) kubectl create ns argocd
namespace/argocd created
➜ (MoeLove) kubectl -n argocd apply -f https://raw.githubusercontent.com/argoproj/argo-cd/stable/manifests/install.yaml
customresourcedefinition.apiextensions.k8s.io/applications.argoproj.io created
customresourcedefinition.apiextensions.k8s.io/appprojects.argoproj.io created
serviceaccount/argocd-application-controller created
serviceaccount/argocd-dex-server created
serviceaccount/argocd-redis created
serviceaccount/argocd-server created
role.rbac.authorization.k8s.io/argocd-application-controller created
role.rbac.authorization.k8s.io/argocd-dex-server created
role.rbac.authorization.k8s.io/argocd-server created
clusterrole.rbac.authorization.k8s.io/argocd-application-controller created
clusterrole.rbac.authorization.k8s.io/argocd-server created
rolebinding.rbac.authorization.k8s.io/argocd-application-controller created
rolebinding.rbac.authorization.k8s.io/argocd-dex-server created
rolebinding.rbac.authorization.k8s.io/argocd-redis created
rolebinding.rbac.authorization.k8s.io/argocd-server created
clusterrolebinding.rbac.authorization.k8s.io/argocd-application-controller created
clusterrolebinding.rbac.authorization.k8s.io/argocd-server created
configmap/argocd-cm created
configmap/argocd-cmd-params-cm created
configmap/argocd-gpg-keys-cm created
configmap/argocd-rbac-cm created
configmap/argocd-ssh-known-hosts-cm created
configmap/argocd-tls-certs-cm created
secret/argocd-secret created
service/argocd-dex-server created
service/argocd-metrics created
service/argocd-redis created
service/argocd-repo-server created
service/argocd-server created
service/argocd-server-metrics created
deployment.apps/argocd-dex-server created
deployment.apps/argocd-redis created
deployment.apps/argocd-repo-server created
deployment.apps/argocd-server created
statefulset.apps/argocd-application-controller created
networkpolicy.networking.k8s.io/argocd-application-controller-network-policy created
networkpolicy.networking.k8s.io/argocd-dex-server-network-policy created
networkpolicy.networking.k8s.io/argocd-redis-network-policy created
networkpolicy.networking.k8s.io/argocd-repo-server-network-policy created
networkpolicy.networking.k8s.io/argocd-server-network-policy created查看状态
➜ (MoeLove) kubectl -n argocd get deploy
NAME READY UP-TO-DATE AVAILABLE AGE
argocd-dex-server 0/1 1 1 1m
argocd-redis 0/1 1 1 1m
argocd-repo-server 1/1 1 1 1m
argocd-server 0/1 1 1 1m获取密码:
默认情况下安装好的 Argo CD 会启用基于 Basic Auth的身份校验,我们可以在 Secret 资源中找到对应的密码。但需要注意的是 这个名字为 argocd-initial-admin-secret 的 sercret 资源是等到 Pod 处于 Running 状态后才会写入。
# 等待 Pod 全 Ready
➜ (MoeLove) kubectl wait --for=condition=Ready pods --all -n argocd
pod/argocd-application-controller-0 condition met
pod/argocd-dex-server-5fc596bcdd-lnx65 condition met
pod/argocd-redis-5b6967fdfc-mfbrr condition met
pod/argocd-repo-server-98598b6c7-7pmgb condition met
pod/argocd-server-5b4b7b868b-bjmzz condition met
# 获取密码
➜ (MoeLove) kubectl -n argocd get secret argocd-initial-admin-secret -o template="{{ .data.password | base64decode }}"
AFbmuBSmRo1F0Dow通过 UI 访问它
我们可以通过 kubectl port-forward 将 argocd-server 的 443 端口映射到本地的 9080 端口。
➜ (MoeLove) ➜ (MoeLove) kubectl port-forward --address 0.0.0.0 service/argocd-server -n argocd 9080:443这样在浏览器中就可以 ArgoCD dashboard ,这是 username 是 admin, 以及 password 便可以前面提到的『获取密码』章节 。
 img
img
命令行访问:
如果你不喜欢通过浏览器进行操作,那也可以使用 Argo CD 提供的 CLI 工具。
➜ (MoeLove) wget https://github.com/argoproj/argo-cd/releases/download/v2.1.2/argocd-linux-amd64 -O argocd
➜ (MoeLove) chmod +x argocd
➜ (MoeLove) mv argocd /bin/argocd
# 执行这条命令前,我们先通过 kubectl port-forward 进行了端口转发
➜ (MoeLove) argocd login localhost:9080
WARNING: server certificate had error: x509: certificate signed by unknown authority. Proceed insecurely (y/n)? y
Username: admin
Password:
'admin:login' logged in successfully
Context 'localhost:9080' updated部署应用
这里我创建了一个示例项目,完整内容可以在我的 GitHub https://github.com/tao12345666333/argo-cd-demo 获取到。
创建目标 namespace
➜ (MoeLove) kubectl create ns kustomize
namespace/kustomize created创建 app
这里可以选择在 Argo CD 的 UI 中直接配置,也可以使用 Argo CD 的 CLI 来配置,这里我以 CLI 配置为例
➜ (MoeLove) argocd app create argo-cd-demo --repo https://github.com/tao12345666333/argo-cd-demo.git --revision kustomize --path ./kustomization --dest-server https://kubernetes.default.svc --dest-namespace kustomize
application 'argo-cd-demo' created其中:
--repo指定部署应用所使用的仓库地址;--revision指定部署应用所使用的分支,这里我使用了一个名为kustomize的分支;--path部署应用程序用到的 manifest 所在的位置--dest-server目标 Kubernetes 集群的地址--dest-``namespace应用要部署的目标 namespace
查看状态
当 Application 创建完成后,也可以直接在 UI 上看到具体信息:
 img
img
或者通过 argocd 在终端下进行查看:
➜ (MoeLove) argocd app get argo-cd-demo
Name: argo-cd-demo
Project: default
Server: https://kubernetes.default.svc
Namespace: kustomize
URL: https://localhost:8080/applications/argo-cd-demo
Repo: https://github.com/tao12345666333/argo-cd-demo.git
Target: kustomize
Path: ./kustomization
SyncWindow: Sync Allowed
Sync Policy:
Sync Status: OutOfSync from kustomize (e8a2d77)
Health Status: Missing
GROUP KIND NAMESPACE NAME STATUS HEALTH HOOK MESSAGE
Service kustomize argo-cd-demo OutOfSync Missing
apps Deployment kustomize argo-cd-demo OutOfSync Missing 可以看到当前的 Application 状态是 OutOfSync ,所以我们可以为它触发一次 sync 操作,进行首次部署。
sync
可以在 UI 上点击 SYNC 按钮,或者通过 argocd CLI 来触发同步操作。
➜ (MoeLove) argocd app sync argo-cd-demo
TIMESTAMP GROUP KIND NAMESPACE NAME STATUS HEALTH HOOK MESSAGE
2021-10-30T10:35:33+00:00 Service kustomize argo-cd-demo OutOfSync Missing
2021-10-30T10:35:33+00:00 apps Deployment kustomize argo-cd-demo OutOfSync Missing
2021-10-30T10:35:35+00:00 Service kustomize argo-cd-demo Synced Healthy
2021-10-30T10:35:35+00:00 Service kustomize argo-cd-demo Synced Healthy service/argo-cd-demo created
2021-10-30T10:35:35+00:00 apps Deployment kustomize argo-cd-demo OutOfSync Missing deployment.apps/argo-cd-demo created
2021-10-30T10:35:35+00:00 apps Deployment kustomize argo-cd-demo Synced Progressing deployment.apps/argo-cd-demo created
Name: argo-cd-demo
Project: default
Server: https://kubernetes.default.svc
Namespace: kustomize
URL: https://localhost:8080/applications/argo-cd-demo
Repo: https://github.com/tao12345666333/argo-cd-demo.git
Target: kustomize
Path: ./kustomization
SyncWindow: Sync Allowed
Sync Policy:
Sync Status: Synced to kustomize (e8a2d77)
Health Status: Progressing
Operation: Sync
Sync Revision: e8a2d77cf0e5405ba9e5dc70d3bf44da91b3ce00
Phase: Succeeded
Start: 2021-10-30 10:35:33 +0000 UTC
Finished: 2021-10-30 10:35:35 +0000 UTC
Duration: 2s
Message: successfully synced (all tasks run)
GROUP KIND NAMESPACE NAME STATUS HEALTH HOOK MESSAGE
Service kustomize argo-cd-demo Synced Healthy service/argo-cd-demo created
apps Deployment kustomize argo-cd-demo Synced Progressing deployment.apps/argo-cd-demo created 同步成功后,在 UI 上也能看到当前应用和同步的状态。
 img
img
点击查看详情,可以看到应用部署的拓扑结构:
 img
img
验证效果
CI
接下来在 kustomize 分支,进行一些代码上的修改,并提交到 GitHub 上。此时会触发项目中基于 GitHub Action 的 CI,我们来看看其具体的配置:
deploy:
name: Deploy
runs-on: ubuntu-latest
continue-on-error: true
needs: build
steps:
- name: Check out code
uses: actions/checkout@v2
- name: Setup Kustomize
uses: imranismail/setup-kustomize@v1
with:
kustomize-version: "4.3.0"
- name: Update Kubernetes resources
env:
DOCKER_USERNAME: ${{ secrets.DOCKER_USERNAME }}
run: |-
cd manifests
kustomize edit set image ghcr.io/${{ github.repository }}/argo-cd-demo:${{ github.sha }}
cat kustomization.yaml
kustomize build ./ > ../kustomization/manifests.yaml
cat ../kustomization/manifests.yaml
- uses: EndBug/add-and-commit@v7
with:
default_author: github_actions
branch: kustomize可以看到这里其实利用了 kustomize 这个工具,将最新的镜像写入到了部署应用所用的 manifest.yaml 文件中了,然后利用 EndBug/add-and-commit@v7 这个 action 将最新的 manifest.yaml 文件再提交回 GitHub 中。
查看状态
此时当 Sync 再次触发后,我们也就可以看到最新的部署拓扑了。
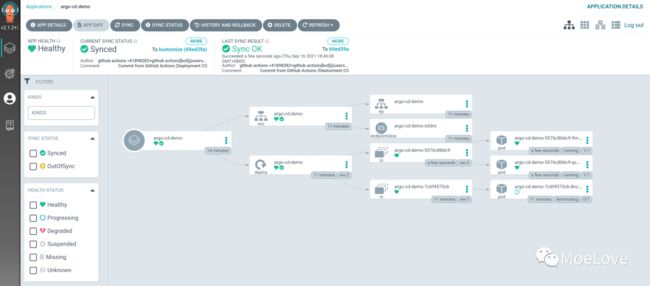 img
img
总结
以上就是关于使用 Argo CD 实现 GitOps 的实践内容了。感兴趣的小伙伴可以直接在 GitHub 上找到此项目的完整示例:https://github.com/tao12345666333/argo-cd-demo
欢迎订阅我的文章公众号【MoeLove】
