1. 概述
为啥要用TLS?
Openldap默认使用简单验证,对slapd的所有访问都使用明文密码通过未加密通道进行。为了确保信息安全,需要对信息进行加密传输,SSL(Secure Sockets Layer)是一个可靠的解决方案。
它使用X.509证书,由可信任第三方(Certificate Authority(CA))进行数字签名的一个标准格式的数据。有效的数字签名意味着已签名的数据没有被篡改。如果签名的数据被更改,将不会通过验证。
SSL/TLS加密原理简介
SSL/TLS是基于PKI机制的加密方式,包括证书认证、密钥交换、非对称加密、对称加密。SSL/TLS采用CA作为服务端核客户端都信赖的具有权威性的组织,证书的颁发和认证都依赖于CA,并假定CA颁发的证书是可靠的、可信赖的,证书里面的内容是真实的、有效的,并可用于客户机和服务器进行安全的可靠的通信加密。
SSL/TLS证书用来认证服务器和客户机双方的身份,并用于密钥交换的非对称加密。密钥交换完毕之后,就可以用这个密钥做通信数据的对称加密了,具体的加密算法是由客户机和服务器相互协商得来的。服务器和客户机由于SSL/TLS库的不同以及用户的配置不同,双方支持的算法列表不完全相同,当双方做SSL/TLS握手的时候,就需要将自己支持的算法列表以及优先顺序告知对方,一旦对方按照优先顺序找到了第一个支持的算法,那么协商完成,否则双方协商失败,SSL/TLS连接断开。
2. 环境
ldap版本:openldap-2.4.44-13.el7.x86_64
系统版本:Centos7.4
服务器信息:
| hostname |
ip |
角色 |
| node105 |
192.168.1.105 |
ldap client+CA |
| node107 |
192.168.1.107 |
ldap server |
3. 步骤
以下命令均以root用户执行,却在https://www.cnblogs.com/swordfall/p/12119010.htmlOpenldap安装部署 的基础上。
3.1. 查看openldap版本
rpm -qa | grep openldap
3.2. 查看openldap server服务与SSL2/3、TLS等协议通信关系
扫描IP和端口
openssl s_client -ssl3 -connect 192.168.1.215:389
或
nmap --script ssl-enum-ciphers -p389 node214(推荐)
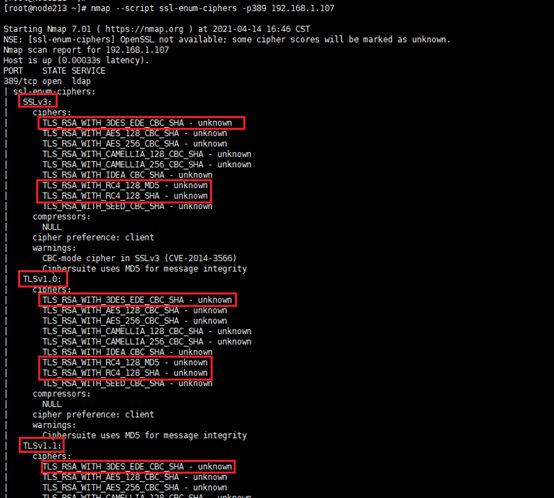
未切换TLS1.2协议之前,nmap扫描如下,包括SSLV3、TLS1、TLS1.1下的3DE、SSL RC4漏洞等:
3.3. CA服务器和openldap server配置私钥公钥
root用户登录192.168.1.105机器
3.3.1 CA服务器创建根密钥和CA签名证书公钥
- 创建根密钥CA.key(私钥)
openssl genrsa -out CA.key 2048
- 创建自签名根证书CA.pem,证书有效期为1024天(CA证书,即公钥)
openssl req -x509 -new -nodes -key CA.key -sha256 -days 1024 -out CA.pem
执行上面的命令会出现如下信息,需要填写并记住:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:GD
Locality Name (eg, city) [Default City]:SZ
Organization Name (eg, company) [Default Company Ltd]:Tech
Organizational Unit Name (eg, section) []:IT
Common Name (eg, your name or your server's hostname) []:test
Email Address []:[email protected]
红色字体则为填写的内容,需要记住!!!
3.3.2 LDAP Server 服务器创建私钥和证书公钥
root用户登录192.168.1.107 ldap server服务器
- LDAP服务器创建私钥ldap.key
openssl genrsa -out ldap.key 2048
- 创建证书签名请求
根据私钥ldap.key创建ldap.csr签名请求
openssl req -new -key ldap.key -out ldap.csr
执行上面的命令会出现如下信息,需要填写在CA服务器节点填写的红色字体:
You are about to be asked to enter information that will be incorporated
into your certificate request.
What you are about to enter is what is called a Distinguished Name or a DN.
There are quite a few fields but you can leave some blank
For some fields there will be a default value,
If you enter '.', the field will be left blank.
-----
Country Name (2 letter code) [XX]:CN
State or Province Name (full name) []:GD
Locality Name (eg, city) [Default City]:SZ
Organization Name (eg, company) [Default Company Ltd]:Tech
Organizational Unit Name (eg, section) []:IT
Common Name (eg, your name or your server's hostname) []:test1
Email Address []:[email protected]
Please enter the following 'extra' attributes
to be sent with your certificate request
A challenge password []:#输入密码test@123
An optional company name []:#不填写enter跳过
注意:
在OpenLDAP服务器向CA申请证书签署请求的时候,除了CommonName、Email Address以外,以上所有值必须和CA证书所填写的信息保持一致,否则无法得到验证。
3.3.3 CA服务器向openldap server签发证书
- 把openldap server的ldap.csr签名请求发送到CA服务器中
在openldap server服务器192.168.1.107使用root用户执行如下命令:
scp ldap.csr [email protected]:/root
- 使用自定义根和CA签署证书签名请求生成ldap.crt证书
在CA服务器192.168.1.105使用root用户执行如下命令,给openldap server的ldap.csr签名请求,生成ldap.crt证书,有效期1460天:
openssl x509 -req -in ldap.csr -CA CA.pem -CAkey CA.key -CAcreateserial -out ldap.crt -days 1460 -sha256
执行上述命令,会出现如下命令:
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Sep 18 08:22:46 2016 GMT
Not After : Sep 18 08:22:46 2017 GMT
Subject:
countryName = CN
stateOrProvinceName = GD
organizationName = Tech
organizationalUnitName = IT
commonName = redpeak1
emailAddress = [email protected]
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
39:FB:0E:BD:7D:03:7E:F3:9E:C3:BE:5B:4D:45:8B:63:B7:8B:7F:26
X509v3 Authority Key Identifier:
keyid:08:FF:94:52:EC:BD:97:12:5B:96:DD:1E:36:08:43:FF:AD:2F:7B:C8
Certificate is to be certified until Sep 18 08:22:46 2017 GMT (365 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
填写y,确认
3.3.4 openldap server下载签发证书并安装
- CA服务器完成openldap server的签发证书,并把该证书发送回给openldap server服务器,还需要把CA服务器的CA证书(公钥)一并发送给openldap server服务器
在CA服务器192.168.1.105使用root用户执行如下命令:
scp /root/ldap.crt CA.pem [email protected]:/root
- 在openldap server服务器192.168.1.107安装证书(包括签发证书和CA证书),并授予ldap用户权限
cp ldap.key ldap.crt CA.pem /etc/openldap/certs/
chown -R ldap:ldap /etc/openldap/certs
3.5. 配置LDAP Server开启TLS
在openldap server服务器192.168.1.107,使用root用户执行
- 编写ldif文件,导入证书
vim certs.ldif
certs.ldif配置内容为:
dn: cn=config
changetype: modify
replace: olcTLSCertificateFile
olcTLSCertificateFile: /etc/openldap/certs/ldap.crt
dn: cn=config
changetype: modify
replace: olcTLSCertificateKeyFile
olcTLSCertificateKeyFile: /etc/openldap/certs/ldap.key
dn: cn=config
changetype: modify
add: olcTLSCACertificateFile
olcTLSCACertificateFile: /etc/openldap/certs/CA.pem
- 执行命令导入配置到/etc/openldap/slapd.d/cn=config.ldif文件中
ldapmodify -Y EXTERNAL -H ldapi:/// -f certs.ldif
注意:
该命令大概率失败,报如下错误:
[root@node3 ~]# ldapmodify -Y EXTERNAL -H ldapi:/// -f certs.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
SASL SSF: 0
modifying entry "cn=config"
ldap_modify: Other (e.g., implementation specific) error (80)
如报上述红色字体错误,需要检查/etc/openldap/certs目录下的ldap.crt、ldap.key、CA.pem这三个文件的权限是否为644,可能还会继续出现该错误,如果出现,则忽略跳过,执行下面的
[root@node215 ranger-usersync]# ldapmodify -Y EXTERNAL -H ldapi:/// -f certs.ldif
SASL/EXTERNAL authentication started
SASL username: gidNumber=0+uidNumber=0,cn=peercred,cn=external,cn=auth
SASL SSF: 0
modifying entry "cn=config"
modifying entry "cn=config"
ldap_modify: Inappropriate matching (18)
additional info: modify/add: olcTLSCACertificateFile: no equality matching rule
如报上述红色字体,暂时不知原因,可以跳过进行第三步骤
- 直接编辑/etc/openldap/slapd.d/cn=config.ldif文件
注:一般情况下不直接修改
olcTLSCertificateFile: /etc/openldap/certs/ldap.crt
olcTLSCertificateKeyFile: /etc/openldap/certs/ldap.key
olcTLSCACertificateFile: /etc/openldap/certs/CA.pem
- 更改服务配置文件/etc/openldap/ldap.conf
vim /etc/openldap/ldap.conf
# 配置认证方式
TLS_REQCERT never
- 重启openldap server服务
systemctl start slapd
# 查看重启后的服务状态
systemctl status slapd
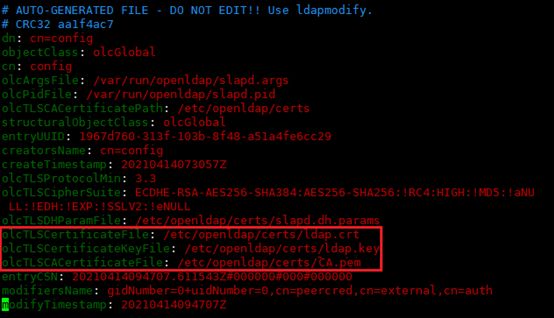
3.6. 配置LDAP Server的SSL/TLS的安全性
- 使用root执行如下命令:
vim tls1.2.ldif
配置内容如下:
dn: cn=config
changetype: modify
add: olcTLSProtocolMin
olcTLSProtocolMin: 3.3
dn: cn=config
changetype: modify
add: olcTLSCipherSuite
olcTLSCipherSuite: ECDHE-RSA-AES256-SHA384:AES256-SHA256:!RC4:HIGH:!MD5:!aNULL:!EDH:!EXP:!SSLV2:!eNULL
dn: cn=config
changetype: modify
add: olcTLSDHParamFile
olcTLSDHParamFile: /etc/openldap/certs/slapd.dh.params
注:
-
- olcTLSProtocolMin: 3.3 Support TLSv1.2 or better
- olcTLSCipherSuite: ECDHE-RSA-AES256-SHA384:AES256-SHA256:!RC4:HIGH:!MD5:!EDH:!EXP:!SSLV2:!eNULL Strongest available ciphers only
- 创建DH参数文件
openssl dhparam -out /etc/openldap/certs/slapd.dh.params.tmp 1024
mv /etc/openldap/certs/slapd.dh.params.tmp /etc/openldap/certs/slapd.dh.params
注:
-
- Use of stronger ciphers can be enabled by ensuring there is a Diffie-Helman parameter file available.This file should be renewed on a period (weekly) basis.
- 使用ldapmodify命令导入配置到/etc/openldap/slapd.d/cn=config.ldif文件中
ldapmodify -Y EXTERNAL -H ldapi:/// -f tls1.2.ldif
3.7. 使用TLS=required配置OpenLDAP
- 使用root用户执行如下命令
vim force-ssl.ldif
配置内容如下:
dn: olcDatabase={2}hdb,cn=config
changetype: modify
add: olcSecurity
olcSecurity: tls=1
- 执行命令导入配置到/etc/openldap/slapd.d/cn=config/ olcDatabase={2}hdb.ldif文件中
ldapmodify -v -Y EXTERNAL -H ldapi:/// -f force-ssl.ldif
3.8. 修改完上述配置重启openldap
systemctl restart slapd
systemctl status slapd
3.9. LDAP Client配置
登录各LDAP Client节点
- 使用nslcd
authconfig --enableldap --enableldapauth --enableldaptls --ldapserver=ldap://192.168.1.107 --ldapbasedn='dc=apache,dc=org' --enablemkhomedir --update
- 使用CA服务器证书
从CA服务器获取CA.pem证书
scp CA.pem [email protected]:/etc/openldap/cacerts/
- 配置使用证书与验证方式
vim /etc/openldap/ldap.conf
配置内容如下:
TLS_CACERTDIR /etc/openldap/cacerts
TLS_CACERT /etc/openldap/cacerts/CA.pem
TLS_REQCERT never
- 配置nslcd启用start_tls
vim /etc/nslcd.conf
nslcd.conf配置内容如下:
# StartTLS
ssl start_tls
tls_cacertdir /etc/openldap/cacerts
tls_cacertfile /etc/openldap/cacerts/CA.pem
tls_reqcert never
重启nslcd
systemctl restart nslcd
systemctl enable nslcd
- 指定LDAP检索顺序
vim /etc/nsswitch.conf
nsswitch.conf变更内容为:
passwd: files ldap
shadow: files ldap
group: files ldap
3.10. 测试TLS
- 命令1
ldapwhoami -v -x -Z
ldap_initialize( )
anonymous
Result: Success (0)
- 命令2
ldapsearch -x -Z -H ldap://192.168.1.107 -b 'ou=Group,dc=hadoop,dc=apache,dc=org'
会显示出数据
- 会报错,要求TLS验证
ldapsearch -H ldaps://192.168.1.107
ldapsearch -Z ldap:/192.168.1.107
- 登录测试
id username
su - username
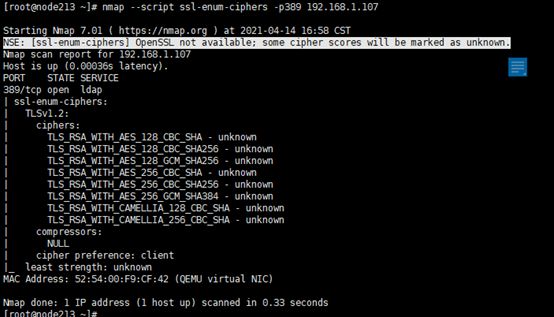
- nmap端口扫描
nmap --script ssl-enum-ciphers -p389 192.168.1.107
显示只有TLS1.2
需要先安装nmap,安装详情请看https://blog.csdn.net/u010142437/article/details/80097869
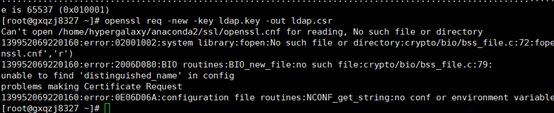
3.11. openldap问题
root用户执行如下命令:
openssl req -new -key ldap.key -out ldap.csr
报错openssl.cnf文件找不到,如下:
多添加-config /etc/pki/tls/openssl.cnf,如下:
openssl req -new -key ldap.key -out ldap.csr -config /etc/pki/tls/openssl.cnf
4. 参考资料
https://access.redhat.com/articles/1474813
https://blog.csdn.net/u011607971/article/details/86153804
https://blog.csdn.net/qq_41960479/article/details/103788338
https://blog.csdn.net/weixin_42167759/article/details/80509806
https://www.jb51.cc/bash/385993.html
https://www.cnblogs.com/zhaojiedi1992/p/zhaojiedi_linux_011_ca.html
https://www.linuxquestions.org/questions/linux-server-73/openldap-tls-config-edit-failing-4175563252/?__cf_chl_jschl_tk__=a966b6a18b283c6a1b6bb97890c1fa6f39e106b5-1618386492-0-AZP4RNO22O4Qyr8zFI9-wHCSbUiZZ6NSWgWcQvPb3idPmrGSAbopkXXax36D8CmNIw4_UoKc4ix_4BFDYnUcR45WL0_YElizylT40nV7J6d_AWN0NmzEY1b028mZ3M8hJs-3aqJb7eT_ketyZpO7XH60NnjB46u_XB7NiSIPiTzvbOOkcP-V6WlHS-qx18TbDGd-TvFAGezyND2FLAgVBp2H5xAjbgxS-Ch5PaaRsMHScmksffjxJSsUzZqErDHqYloz7NCBdumSRELIB3kdn3YNO6ipWr6XuOSDvYKrRYocbfDhicUVKxgLrXofspWFsf2-SoIes8WYtCAyb_IEoldKD5FS_BOWTQkC6x1upJ2FpzfZLU5npvaaPHGaUi53fwmDLSFnFAktDQTicuSMA4E1bKRpb0DdDX7yGyMYzJ1vuBpKW-MAP20ok2aaez90EA6F7uHayZHlh7WGGS_UKi0s_KacceGUhDFSw836wLgpFDp-SYESgo5ciqt32IXQcv1VW46YEkoks9snPkDYZz0
https://www.linuxquestions.org/questions/linux-server-73/openldap-disabling-ssl-ciphers-4175543664/?__cf_chl_jschl_tk__=66e9f5b4d27d28f60eefe3b3c9c7abe48cb8d1ad-1618300454-0-Ad0rP7tkI4iQOFE-Lh6coCIEmpZZLhKD0BfuLx2M5AtaHo-ZfoWcoJbzlIKjO8c0jJATn-XDeBNOfZIQOsWxIeVE8K_epka0Lem5K3L4zJBtEewdCDVSHVf6stakCgrqIEUJBLP0ujSF3BeT9HV6Ll6ZS4VGui9FN4TPi4i1a-9RKLAg8dMGT4RHSCdhsALHGgKX6bTGDZmo65cOqlZ-EnbwxwjU_zgmOZXylblcb696_dyDkAsQeOV55lrC4hwPIeEgXSAVmyeuqhBaXdMPdrzmrsXgDLf2TYwZ0EsHYaAMqe2GicFl_ov1btDUEJdMW4GRqFo2jtv3WKjdKfXc7bLDrLyZIH3hEfOYHRFjVBpLtdpJIc65FgNJBVZN9kwnwYE-CG2lDaNmkpzhr3jtZYKLvFXCbcWVtPC5-T1Eoj1AqiM_fl9KSlBNQcp5mcjPsHA_9EJLvcS21Jp2t6OOe89_ifpOJ1fvlPHqTvh0W392lKGuZXXIR7-JVHAXu48eL0Dq48YWC1edE3M1SQJAd5I