- [学习]M-QAM的数学原理与调制解调原理详解(仿真示例)
M-QAM的数学原理与调制解调原理详解QAM(正交幅度调制)作为现代数字通信的核心技术,其数学原理和实现方法值得深入探讨。本文将分为数学原理、调制解调原理和实现要点三个部分进行系统阐述。文章目录M-QAM的数学原理与调制解调原理详解一、数学原理二、调制原理三、解调原理四、实现要点五、16QAM的Python仿真实现5.1完整仿真代码5.2关键代码解析5.3仿真结果分析六、性能优化方向七、MATLA
- lesson1:Python入门知识
你的电影很有趣
python开发语言
目录文章目录前言一、python的语言特性1、语法简练2、解释型语言2.1解释型语言特点2.2编译型语言特点2.3执行效率比较3、标准库/第三方库4、支持面向对象二、windows常用命令三、程序的基本组成1、输入input2、运算3、输出print总结前言开始学习python的第一课一、python的语言特性1、语法简练变量不需要声明类型2、解释型语言2.1解释型语言特点需要解释器通过解释器逐行
- 学习笔记-JVM GC
绝不秃头的L君
学习笔记jvmjvm.gc
1.GC分类PartialGC并不会收集整个堆空间,仅仅包括新生代和老年代,不包含永久代(元空间)。YoungGC:只收集YoungGen的垃圾收集过程。OldGC:只收集OldGen的垃圾收集过程。(只有CMS的并发收集是这个模式)MixedGC:收集整个YoungGen以及部分OldGen的垃圾收集过程。(只有G1有这个模式)FullGC收集整个堆,包括YoungGen、OldGen以及Per
- spring bean生命周期 学习记录
不会吃萝卜的兔子
spring学习java
在SimpleAutowareConfig??中1,第三级缓存存放createBean的lambda表达式(BeanFactory采用函数式接口,使用时才会创建),当获取循环引用获取早期对象时(只实例化的bean),这个早期对象不知道有没有被AOP修饰,但AOP代理,要拿到完整的对象,才能正确代理,但是代理在beanAfterPostProcessor发生在popularBean属性填充之前。2,
- 从入门到精通:YashanDB数据库学习指南
数据库
在现代的数据库技术领域,性能瓶颈和数据一致性问题是开发人员和数据库管理员(DBA)面临的重要挑战。随着数据量的激增和对实时分析的需求上升,如何有效管理和利用数据库显得尤为重要。YashanDB作为一款新兴数据库,提供了一系列功能以应对这些挑战,适合希望深入理解数据库体系结构的开发者和DBA。本文旨在提供一份全面的YashanDB学习指南,内容涵盖系统架构、核心功能,并为实际应用提供具体建议,使读者
- 【学习笔记】jvm
liu1251303815
学习笔记jvm
1、jvm基础1.1什么是jvm?jvm是一种规范。jvm是一种什么样的规范?具体实现:hotspot2classFileFormat3:类加载-初始化3.1、loading加载class文件到内存中3.1.1引起类加载的情况new对象时调用静态属性,静态方法时。(访问staticfinal变量除外staticfinal修饰的是基本数据类型,或者字符串类型时,会替换为常量。比如有一个类A{stat
- JVM GC学习记录
不会吃萝卜的兔子
JVMGCjvm学习javaGC
垃圾标记算法:引用计数:解决不了垃圾对象循环引用问题。root扫描(可达性分析):从根对象(线程、main函数、静态变量、常量)扫描。三色标记:黑:其下所有子树,引用均被标记完成,是存活的最终状态。灰:其下所有子树,但引用的对象尚未完全检查,是存活的过渡状态。白:对象未被标记,默认初始状态,标记结束后仍为白色的对象将被回收。标记时会STW扫描根节点,然后标记线程与业务线程并行存在;会产生情况2,业
- 解密GPT工作原理:Transformer架构详解与自注意力机制剖析
AI智能应用
gpttransformer架构ai
解密GPT工作原理:Transformer架构详解与自注意力机制剖析关键词:GPT、Transformer、自注意力机制、神经网络、语言模型、深度学习、人工智能摘要:本文将深入浅出地解析GPT模型的核心架构——Transformer,重点剖析其革命性的自注意力机制。我们将从基本概念出发,通过生活化的比喻解释复杂的技术原理,并用Python代码示例展示实现细节,最后探讨这一技术的应用场景和未来发展方
- ChatGPT、DeepSeek等大语言模型技术教程
随着人工智能技术的快速发展,大语言模型如ChatGPT和DeepSeek在科研领域的应用正在为科研人员提供强大的支持。这些模型通过深度学习和大规模语料库训练,能够帮助科研人员高效地筛选文献、生成论文内容、进行数据分析和优化机器学习模型。ChatGPT和DeepSeek能够快速理解和生成复杂的语言,帮助研究人员在撰写论文时提高效率,不仅生成高质量的文章内容,还能优化论文结构和语言表达。在数据分析方面
- C++编程:打造角色扮演游戏
夏勇兴
本文还有配套的精品资源,点击获取简介:本项目“C++实现的角色扮演游戏”通过构建一个游戏示例,帮助学习者掌握C++编程,特别是C++17特性。项目涵盖了类、对象、继承、多态、模板、异常处理、文件操作、动态内存管理、STL、函数与运算符重载、构造和析构函数等关键概念。参与者将通过实际操作,加深对面向对象编程的理解,并为复杂项目开发打下基础。1.C++编程基础和C++17特性1.1C++编程的起源与优
- 提升学习能力(一)
如果决定要走又何必挽留
学习方法学习
前言:在学习一项技能在时候,通常会感到学了一遍,,没有任何的头绪,一直在通过做的时候通过来总结来去干,这样往往在学习的时候,不能事半功倍,在学习的时候也没有任何方法,毫无头绪,于是想写点关于提升学习能力的东西,刚才在前面的介绍说了,对于别人的教学没有任何头绪,下面的学习四步骤通过借鉴别人的学习经验,每个人的学习技巧,方法,都不一样,适合自己的才是做好的。一.学习方法1:兴趣法,有很多不感兴趣的东西
- Vue学习之路04----响应式基础
利刃之灵
#Vue基础vue.js前端
响应式基础ref()(基本类型的响应式数据)在组合式API中,推荐使用ref()函数来声明响应式状态,ref能定义基本类型的,也能定义对象类型的:import{ref}from'vue'letcount=ref(0)ref()接收参数,并将其包裹在一个带有.value属性的ref对象中返回,在模版中则不需要:{{count}}按钮1按钮2import{ref}from"vue";exportdef
- 强化学习【chapter0】-学习路线图
明朝百晓生
算法人工智能机器学习
前言:主要总结一下西湖大学赵老师的课程【强化学习的数学原理】课程:从零开始到透彻理解(完结)_哔哩哔哩_bilibili1️⃣基础阶段(Ch1-Ch7):掌握表格型算法,理解TD误差与贝尔曼方程2️⃣进阶阶段(Ch8-Ch9):动手实现DQN/策略梯度,熟悉PyTorch/TensorFlow3️⃣前沿阶段(Ch10:阅读论文(OpenAISpinningUp/RLlib文档)Chapter1:基
- GtkSharp跨平台WinForm实现
文章目录跨平台架构设计跨平台项目配置GtkSharp串口通讯实现跨平台部署配置Linux系统配置macOS系统配置相关学习资源GTK#跨平台开发跨平台.NET开发Linux开发环境macOS开发环境跨平台UI框架对比容器化部署开源项目参考性能优化与调试跨平台架构设计基于GTKSystem.Windows.Forms框架,我们可以实现真正的跨平台WinForm串口通讯应用:共享代码层macOS环境L
- docker容器学习基础篇
docker容器学习基础篇为什么要学docker在开发工作中,都是团队协作开发的,不同开发人员的代码运行环境,配置环境等等都不同,这回在整合过程中浪费太多时间,降低开发效率,而docker容器可以模拟配置环境等,解决了代码’'水土不服”的问题,对于要就业的小伙伴,docker是一项必须要掌握的技术。什么是dockerDocker是基于Go语言实现的云开源项目,Docker容器在任何操作系统上都是一
- 全面学习 OpenAI API:从 Python 教程到 API Key 使用详解,快速上手调用和部署
我的学校你进不来
学习python开发语言人工智能语言模型深度学习
说在前面我们正身处在人工智能迅猛发展的时代,OpenAIAPI无疑是其中的翘楚,它提供了强大的工具,让开发者能够创建智能应用程序。然而,对于许多刚接触这个领域的开发者来说,如何开始使用OpenAIAPI可能是一个不小的挑战。这篇文章旨在全面介绍如何从零开始学习和使用OpenAIAPI,从申请APIKey到在Python中调用和部署,助力你快速上手并实现在项目中的应用。在接下来的内容中,我们将详细阐
- .NET MAUI跨平台串口通讯方案
冰茶_
C#通讯编程#串口通讯.netIOTMAUI串口通讯
文章目录MAUI项目架构设计平台特定实现接口定义Windows平台实现Android平台实现MAUI主界面实现依赖注入配置相关学习资源.NETMAUI开发移动端开发平台特定实现依赖注入与架构移动应用发布跨平台开发最佳实践性能优化测试与调试开源项目参考MAUI项目架构设计MAUIApp共享业务逻辑串口服务接口Windows实现Android实现iOS实现macOS实现System.IO.PortsA
- 【机器学习】什么是逻辑回归?从入门到精通:掌握逻辑回归与二分类问题的解决之道
宸码
模式识别机器学习机器学习python逻辑回归分类人工智能算法
从入门到精通:掌握逻辑回归与二分类问题的解决之道引言1.1逻辑回归简介1.2逻辑回归的应用场景逻辑回归基本原理2.1逻辑回归概述逻辑回归的基本思想预测类别的概率2.2线性模型与Sigmoid函数线性模型Sigmoid函数Sigmoid函数的性质为什么选择Sigmoid函数2.3逻辑回归的输出:概率值分类决策代价函数与优化数学基础3.1逻辑回归的假设与目标假设目标3.2对数似然函数概率模型对数似然函
- 讯飞星火深度推理模型X1,为教育医疗带来革新
在科技飞速发展的今天,人工智能大模型已经成为推动各行业变革的重要力量。科大讯飞作为人工智能领域的佼佼者,其研发的星火深度推理模型X1,凭借独特的技术优势和强大的功能,为教育和医疗两大关乎国计民生的领域带来了前所未有的革新。技术原理与创新讯飞星火深度推理模型X1基于Transformer架构,并在此基础上进行了一系列创新。它通过大规模多阶段强化学习训练方法,在复杂推理、数学、代码、语言理解等场景全面
- Rust实现FasterR-CNN目标检测全流程
KENYCHEN奉孝
rustPolars
使用Rust和FasterR-CNN进行目标检测FasterR-CNN是目标检测领域广泛使用的深度学习模型。Rust生态中可以通过tch-rs(Torch绑定)调用预训练的PyTorch模型实现。以下为完整实现步骤:环境准备安装Rust和必要的依赖:cargoaddtchcargoaddanyhow#错误处理下载预训练的FasterR-CNN模型(需PyTorch格式.pt文件),或使用Torch
- Python爬虫实战:研究httplib2库相关技术
ylfhpy
爬虫项目实战python爬虫phphttplib2
1.引言1.1研究背景与意义随着互联网的快速发展,网络上的信息量呈爆炸式增长。如何从海量的网页中高效地获取有价值的数据,成为了当前信息技术领域的一个重要研究课题。网络爬虫作为一种自动获取互联网信息的程序,能够按照一定的规则,自动地抓取网页内容并提取和整理信息,为信息检索、数据分析、机器学习等领域提供了丰富的数据来源。在电子商务领域,爬虫可以用于价格监控、竞品分析和市场调研;在学术研究中,爬虫可以帮
- C语言结构体精讲:从定义到初始化的三种核心方式
资料合集下载链接:https://pan.quark.cn/s/472bbdfcd014在C语言编程中,我们经常需要将不同类型的数据组合成一个有机的整体来进行处理,比如记录一个学生的信息(姓名、学号、成绩)。这时,单独的int、char或float变量就显得力不从心了。为了解决这个问题,C语言提供了一种强大的数据类型——结构体(Struct)。本文将根据课堂学习的要点,带你深入理解结构体变量的三种
- Hamiltonian Transformer理论:融合哈密顿力学与Transformer架构的新范式
墨顿
transformer架构深度学习
HamiltonianTransformer理论是一种将经典哈密顿力学原理与现代Transformer架构相结合的新型神经网络范式。这一理论框架试图解决当前深度学习模型在效率、动态系统建模和长期依赖处理等方面的核心挑战。本文将系统梳理HamiltonianTransformer的理论基础、关键创新点、实现方法以及应用前景,并分析其相对于传统Transformer架构的优势与潜在限制。哈密顿力学与T
- 使用numpy或pytorch校验两个张量是否相等
文章目录1、numpy2、pytorch做算法过程中,如果涉及到模型落地,那必然会将原始的深度学习的框架训练好的模型转换成目标硬件模型的格式,如onnx,tensorrt,openvino,tflite;那么就有对比不同格式模型输出的一致性,从而判断模型转换是否成功。1、numpy用到的核心代码就一行,就是:importnumpyasnpnp.testing.assert_allclose(act
- 机器学习笔记:MATLAB实践
techDM
机器学习笔记matlabMatlab
在机器学习领域,MATLAB是一种功能强大且广泛使用的工具,它提供了许多内置函数和工具箱,方便开发者进行各种机器学习任务。本文将介绍一些常见的机器学习任务,并提供相应的MATLAB源代码示例。数据预处理在进行机器学习之前,通常需要对原始数据进行预处理。这包括数据清洗、特征选择、特征缩放和数据划分等步骤。%导入数据data=readmatrix('data.csv');%数据清洗cleaned_da
- vue3学习笔记
朝凡FR
其他学习笔记vue.js前端
目录vue3学习笔记数据绑定'v-bind'简写为':',语法v-bind:id='变量'v-on指令通过v-on:event="method"语法工作,简写语法:@event="method"v-model绑定到你在其上设置的数据属性,并使其与````保持同步v-model修饰符.trim,将删除输入之前或之后的空格;.lazy修饰符导致v-model使用change事件代替使用自定义事件将数据
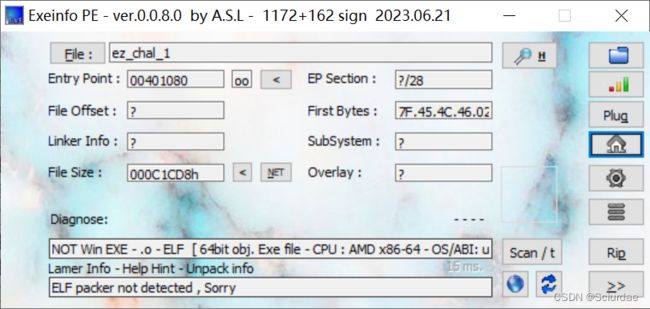
- 50.第二阶段x64游戏实战-代码实现特征码定位
计算机王
逆向学习x64游戏反游戏外挂c++汇编游戏攻防特征码搜索
免责声明:内容仅供学习参考,请合法利用知识,禁止进行违法犯罪活动!本次游戏没法给内容参考于:微尘网络安全上一个内容:49.第二阶段x64游戏实战-封包-代码实现自动登录现在找了很多基址了,但是游戏一更新,代码就会有变化,然后之前找的基址就没法用了,有得重新找,这是一个体力活,为了避免重新找就可以使用特征码进行定位,特征码定位也不是绝对的,可能需要多个版本才能让它不出错,如果特征代码进行了改动也还是
- 【深度学习pytorch-6】张量与numpy相互转换
超华东算法王
DL-pytorch深度学习pytorchnumpy
张量与Numpy数组之间的互相转换在深度学习中,张量(tensor)和Numpy数组(numpyarray)是两种常见的数据结构。张量通常用于深度学习框架(如PyTorch、TensorFlow等),而Numpy数组在科学计算中被广泛使用。为了便于数据处理和计算,常常需要在它们之间进行转换。下面介绍张量和Numpy数组之间的互相转换。1.PyTorch张量与Numpy数组的互相转换PyTorch提
- CppCon 2018 学习:From Metaprogramming Tricks to Elegance
#这段内容是VincentReverdy在CppCon2018演讲的一部分,核心主题是:这场演讲的核心问题是:如何在C++17中提高代码的通用性(Genericity),而不牺牲代码的可读性与简洁性?具体要解决的问题是:你希望写出既通用又可维护的模板代码。换句话说,你希望能像这样思考和写代码:如果满足某个条件,就执行这个函数:if(some_condition){do_this();}让编译器自动
- CppCon 2018 学习:A Semi Compile/Run-time Map with (Nearly) Zero Overhead Looup
虾球xz
CppCon学习开发语言c++
介绍一个C++和Java之间桥接(Bridge)系统的示例代码,它说明了如何在C++中调用Java类(如java.io.InputStream)的方法。下面是详细解读:一、内容来源说明《C++↔JavaBridge》目的:演示如何通过桥接层让C++直接调用Java方法(JNI背后封装)二、代码结构解读classInputStream//java.io.InputStream{public:inli
- Java常用排序算法/程序员必须掌握的8大排序算法
cugfy
java
分类:
1)插入排序(直接插入排序、希尔排序)
2)交换排序(冒泡排序、快速排序)
3)选择排序(直接选择排序、堆排序)
4)归并排序
5)分配排序(基数排序)
所需辅助空间最多:归并排序
所需辅助空间最少:堆排序
平均速度最快:快速排序
不稳定:快速排序,希尔排序,堆排序。
先来看看8种排序之间的关系:
1.直接插入排序
(1
- 【Spark102】Spark存储模块BlockManager剖析
bit1129
manager
Spark围绕着BlockManager构建了存储模块,包括RDD,Shuffle,Broadcast的存储都使用了BlockManager。而BlockManager在实现上是一个针对每个应用的Master/Executor结构,即Driver上BlockManager充当了Master角色,而各个Slave上(具体到应用范围,就是Executor)的BlockManager充当了Slave角色
- linux 查看端口被占用情况详解
daizj
linux端口占用netstatlsof
经常在启动一个程序会碰到端口被占用,这里讲一下怎么查看端口是否被占用,及哪个程序占用,怎么Kill掉已占用端口的程序
1、lsof -i:port
port为端口号
[root@slave /data/spark-1.4.0-bin-cdh4]# lsof -i:8080
COMMAND PID USER FD TY
- Hosts文件使用
周凡杨
hostslocahost
一切都要从localhost说起,经常在tomcat容器起动后,访问页面时输入http://localhost:8088/index.jsp,大家都知道localhost代表本机地址,如果本机IP是10.10.134.21,那就相当于http://10.10.134.21:8088/index.jsp,有时候也会看到http: 127.0.0.1:
- java excel工具
g21121
Java excel
直接上代码,一看就懂,利用的是jxl:
import java.io.File;
import java.io.IOException;
import jxl.Cell;
import jxl.Sheet;
import jxl.Workbook;
import jxl.read.biff.BiffException;
import jxl.write.Label;
import
- web报表工具finereport常用函数的用法总结(数组函数)
老A不折腾
finereportweb报表函数总结
ADD2ARRAY
ADDARRAY(array,insertArray, start):在数组第start个位置插入insertArray中的所有元素,再返回该数组。
示例:
ADDARRAY([3,4, 1, 5, 7], [23, 43, 22], 3)返回[3, 4, 23, 43, 22, 1, 5, 7].
ADDARRAY([3,4, 1, 5, 7], "测试&q
- 游戏服务器网络带宽负载计算
墙头上一根草
服务器
家庭所安装的4M,8M宽带。其中M是指,Mbits/S
其中要提前说明的是:
8bits = 1Byte
即8位等于1字节。我们硬盘大小50G。意思是50*1024M字节,约为 50000多字节。但是网宽是以“位”为单位的,所以,8Mbits就是1M字节。是容积体积的单位。
8Mbits/s后面的S是秒。8Mbits/s意思是 每秒8M位,即每秒1M字节。
我是在计算我们网络流量时想到的
- 我的spring学习笔记2-IoC(反向控制 依赖注入)
aijuans
Spring 3 系列
IoC(反向控制 依赖注入)这是Spring提出来了,这也是Spring一大特色。这里我不用多说,我们看Spring教程就可以了解。当然我们不用Spring也可以用IoC,下面我将介绍不用Spring的IoC。
IoC不是框架,她是java的技术,如今大多数轻量级的容器都会用到IoC技术。这里我就用一个例子来说明:
如:程序中有 Mysql.calss 、Oracle.class 、SqlSe
- 高性能mysql 之 选择存储引擎(一)
annan211
mysqlInnoDBMySQL引擎存储引擎
1 没有特殊情况,应尽可能使用InnoDB存储引擎。 原因:InnoDB 和 MYIsAM 是mysql 最常用、使用最普遍的存储引擎。其中InnoDB是最重要、最广泛的存储引擎。她 被设计用来处理大量的短期事务。短期事务大部分情况下是正常提交的,很少有回滚的情况。InnoDB的性能和自动崩溃 恢复特性使得她在非事务型存储的需求中也非常流行,除非有非常
- UDP网络编程
百合不是茶
UDP编程局域网组播
UDP是基于无连接的,不可靠的传输 与TCP/IP相反
UDP实现私聊,发送方式客户端,接受方式服务器
package netUDP_sc;
import java.net.DatagramPacket;
import java.net.DatagramSocket;
import java.net.Ine
- JQuery对象的val()方法执行结果分析
bijian1013
JavaScriptjsjquery
JavaScript中,如果id对应的标签不存在(同理JAVA中,如果对象不存在),则调用它的方法会报错或抛异常。在实际开发中,发现JQuery在id对应的标签不存在时,调其val()方法不会报错,结果是undefined。
- http请求测试实例(采用json-lib解析)
bijian1013
jsonhttp
由于fastjson只支持JDK1.5版本,因些对于JDK1.4的项目,可以采用json-lib来解析JSON数据。如下是http请求的另外一种写法,仅供参考。
package com;
import java.util.HashMap;
import java.util.Map;
import
- 【RPC框架Hessian四】Hessian与Spring集成
bit1129
hessian
在【RPC框架Hessian二】Hessian 对象序列化和反序列化一文中介绍了基于Hessian的RPC服务的实现步骤,在那里使用Hessian提供的API完成基于Hessian的RPC服务开发和客户端调用,本文使用Spring对Hessian的集成来实现Hessian的RPC调用。
定义模型、接口和服务器端代码
|---Model
&nb
- 【Mahout三】基于Mahout CBayes算法的20newsgroup流程分析
bit1129
Mahout
1.Mahout环境搭建
1.下载Mahout
http://mirror.bit.edu.cn/apache/mahout/0.10.0/mahout-distribution-0.10.0.tar.gz
2.解压Mahout
3. 配置环境变量
vim /etc/profile
export HADOOP_HOME=/home
- nginx负载tomcat遇非80时的转发问题
ronin47
nginx负载后端容器是tomcat(其它容器如WAS,JBOSS暂没发现这个问题)非80端口,遇到跳转异常问题。解决的思路是:$host:port
详细如下:
该问题是最先发现的,由于之前对nginx不是特别的熟悉所以该问题是个入门级别的:
? 1 2 3 4 5
- java-17-在一个字符串中找到第一个只出现一次的字符
bylijinnan
java
public class FirstShowOnlyOnceElement {
/**Q17.在一个字符串中找到第一个只出现一次的字符。如输入abaccdeff,则输出b
* 1.int[] count:count[i]表示i对应字符出现的次数
* 2.将26个英文字母映射:a-z <--> 0-25
* 3.假设全部字母都是小写
*/
pu
- mongoDB 复制集
开窍的石头
mongodb
mongo的复制集就像mysql的主从数据库,当你往其中的主复制集(primary)写数据的时候,副复制集(secondary)会自动同步主复制集(Primary)的数据,当主复制集挂掉以后其中的一个副复制集会自动成为主复制集。提供服务器的可用性。和防止当机问题
mo
- [宇宙与天文]宇宙时代的经济学
comsci
经济
宇宙尺度的交通工具一般都体型巨大,造价高昂。。。。。
在宇宙中进行航行,近程采用反作用力类型的发动机,需要消耗少量矿石燃料,中远程航行要采用量子或者聚变反应堆发动机,进行超空间跳跃,要消耗大量高纯度水晶体能源
以目前地球上国家的经济发展水平来讲,
- Git忽略文件
Cwind
git
有很多文件不必使用git管理。例如Eclipse或其他IDE生成的项目文件,编译生成的各种目标或临时文件等。使用git status时,会在Untracked files里面看到这些文件列表,在一次需要添加的文件比较多时(使用git add . / git add -u),会把这些所有的未跟踪文件添加进索引。
==== ==== ==== 一些牢骚
- MySQL连接数据库的必须配置
dashuaifu
mysql连接数据库配置
MySQL连接数据库的必须配置
1.driverClass:com.mysql.jdbc.Driver
2.jdbcUrl:jdbc:mysql://localhost:3306/dbname
3.user:username
4.password:password
其中1是驱动名;2是url,这里的‘dbna
- 一生要养成的60个习惯
dcj3sjt126com
习惯
一生要养成的60个习惯
第1篇 让你更受大家欢迎的习惯
1 守时,不准时赴约,让别人等,会失去很多机会。
如何做到:
①该起床时就起床,
②养成任何事情都提前15分钟的习惯。
③带本可以随时阅读的书,如果早了就拿出来读读。
④有条理,生活没条理最容易耽误时间。
⑤提前计划:将重要和不重要的事情岔开。
⑥今天就准备好明天要穿的衣服。
⑦按时睡觉,这会让按时起床更容易。
2 注重
- [介绍]Yii 是什么
dcj3sjt126com
PHPyii2
Yii 是一个高性能,基于组件的 PHP 框架,用于快速开发现代 Web 应用程序。名字 Yii (读作 易)在中文里有“极致简单与不断演变”两重含义,也可看作 Yes It Is! 的缩写。
Yii 最适合做什么?
Yii 是一个通用的 Web 编程框架,即可以用于开发各种用 PHP 构建的 Web 应用。因为基于组件的框架结构和设计精巧的缓存支持,它特别适合开发大型应
- Linux SSH常用总结
eksliang
linux sshSSHD
转载请出自出处:http://eksliang.iteye.com/blog/2186931 一、连接到远程主机
格式:
ssh name@remoteserver
例如:
ssh
[email protected]
二、连接到远程主机指定的端口
格式:
ssh name@remoteserver -p 22
例如:
ssh i
- 快速上传头像到服务端工具类FaceUtil
gundumw100
android
快速迭代用
import java.io.DataOutputStream;
import java.io.File;
import java.io.FileInputStream;
import java.io.FileNotFoundException;
import java.io.FileOutputStream;
import java.io.IOExceptio
- jQuery入门之怎么使用
ini
JavaScripthtmljqueryWebcss
jQuery的强大我何问起(个人主页:hovertree.com)就不用多说了,那么怎么使用jQuery呢?
首先,下载jquery。下载地址:http://hovertree.com/hvtart/bjae/b8627323101a4994.htm,一个是压缩版本,一个是未压缩版本,如果在开发测试阶段,可以使用未压缩版本,实际应用一般使用压缩版本(min)。然后就在页面上引用。
- 带filter的hbase查询优化
kane_xie
查询优化hbaseRandomRowFilter
问题描述
hbase scan数据缓慢,server端出现LeaseException。hbase写入缓慢。
问题原因
直接原因是: hbase client端每次和regionserver交互的时候,都会在服务器端生成一个Lease,Lease的有效期由参数hbase.regionserver.lease.period确定。如果hbase scan需
- java设计模式-单例模式
men4661273
java单例枚举反射IOC
单例模式1,饿汉模式
//饿汉式单例类.在类初始化时,已经自行实例化
public class Singleton1 {
//私有的默认构造函数
private Singleton1() {}
//已经自行实例化
private static final Singleton1 singl
- mongodb 查询某一天所有信息的3种方法,根据日期查询
qiaolevip
每天进步一点点学习永无止境mongodb纵观千象
// mongodb的查询真让人难以琢磨,就查询单天信息,都需要花费一番功夫才行。
// 第一种方式:
coll.aggregate([
{$project:{sendDate: {$substr: ['$sendTime', 0, 10]}, sendTime: 1, content:1}},
{$match:{sendDate: '2015-
- 二维数组转换成JSON
tangqi609567707
java二维数组json
原文出处:http://blog.csdn.net/springsen/article/details/7833596
public class Demo {
public static void main(String[] args) { String[][] blogL
- erlang supervisor
wudixiaotie
erlang
定义supervisor时,如果是监控celuesimple_one_for_one则删除children的时候就用supervisor:terminate_child (SupModuleName, ChildPid),如果shutdown策略选择的是brutal_kill,那么supervisor会调用exit(ChildPid, kill),这样的话如果Child的behavior是gen_