玩转华为ENSP模拟器系列 | 两个网关之间配置IPSec VdPdNd主备链路备份
素材来源:华为防火墙配置指南
一边学习一边整理试验笔记,并与大家分享,侵权即删,谢谢支持!
附上汇总贴:玩转华为ENSP模拟器系列 | 合集_COCOgsta的博客-CSDN博客_华为模拟器实验
目标
介绍IPSec主备链路备份的配置方法。
组网需求
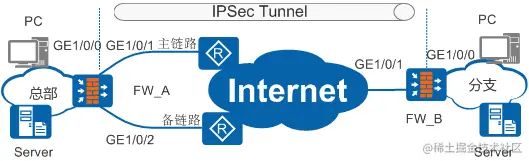
如图1所示,FW_A通过主备两条链路接入Internet,主备接口使用固定的公网IP地址;FW_B通过一条链路接入Internet,出接口同样使用固定的公网IP地址。
要求实现如下需求:
- FW_A和FW_B之间通过IPSec方式建立安全通信隧道,实现总部与分支之间的互访。
- FW_A上的主链路发生故障时,业务可以自动切换到备链路;主链路恢复时,业务会自动回切到主链路。
配置思路
在本例中,FW_A需要与FW_B建立两条隧道,而FW_B只有一个物理接口,所以需要在FW_B上配置两个Tunnel接口,来分别与FW_A的主备接口建立隧道。当FW_A发生主备链路切换时,FW_B也会切换Tunnel接口,双方重新进行IPSec隧道协商。
-
配置FW_A。
- 基本配置,包括配置接口IP地址,将接口加入相应的安全域。
- 配置路由。
- 配置两条FW_A到FW_B的路由,两条路由的优先级不同,实现路由备份。同时,为主路由绑定IP-Link,用于检测主路由上的链路状态。当主路由上的链路发生故障时,系统会自动切换到备用路由。
- 配置IPSec策略相关参数。
- 在接口上应用IPSec安全策略。
- FW_A的GE1/0/1、GE1/0/2分别为主接口和备接口。需要在主备接口上应用相同的IPSec安全策略,当主接口发生故障时,系统自动将IPSec隧道切换至备接口。
-
配置FW_B。
- 基本配置,包括配置接口IP地址,将接口加入相应的安全区域。
- 在FW_B上配置Tunnel1(主接口)和Tunnel2(备接口)两个Tunnel接口,分别与FW_A上的主备接口对应。当FW_A发生主备链路切换时,FW_B也会切换到对应的Tunnel接口。
- 配置路由。
- 在FW_B上将需要保护的数据流通过路由引流到Tunnel接口。因为FW_B上有两个Tunnel接口,所以需要配置两条到总部的路由,出接口为Tunnel1和Tunnel2,两条路由的优先级不同,实现路由备份。同时,为主路由绑定IP-Link,用于检测主路由上的链路状态。当主路由上的链路发生故障时,系统会自动切换到备用路由。
- 配置IPSec策略相关参数。
- FW_B需要与FW_A的主备接口建立IPSec隧道,所以需要创建两个IPSec策略。
- 在接口上应用IPSec策略。
- 在Tunnel1和Tunnel2上分别应用IPSec安全策略,当主接口发生故障时,系统自动将IPSec隧道切换至备接口。
操作步骤
-
配置FW_A(总部)。
-
基本配置。
- 配置接口IP地址。
-
system-view [sysname] sysname FW_A [FW_A] interface gigabitethernet 1 / 0 / 0 [FW_A-GigabitEthernet1/0/0] ip address 10.1.1.1 24 [FW_A-GigabitEthernet1/0/0] quit [FW_A] interface gigabitethernet 1 / 0 / 1 [FW_A-GigabitEthernet1/0/1] ip address 1.1.3.1 24 [FW_A-GigabitEthernet1/0/1] quit [FW_A] interface gigabitethernet 1 / 0 / 2 [FW_A-GigabitEthernet1/0/2] ip address 1.1.4.1 24 [FW_A-GigabitEthernet1/0/2] quit 复制代码 - 将接口加入相应安全区域。
-
[FW_A] firewall zone trust [FW_A-zone-trust] add interface gigabitethernet 1 / 0 / 0 [FW_A-zone-trust] quit [FW_A] firewall zone untrust [FW_A-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_A-zone-untrust] add interface gigabitethernet 1 / 0 / 2 [FW_A-zone-untrust] quit 复制代码
-
配置防火墙策略。
- 配置Trust域与Untrust域的转发策略,允许封装前和解封后的报文能通过FW_A。
-
[FW_A] security-policy [FW_A-policy-security] rule name 1 [FW_A-policy-security-rule-1] source-zone trust [FW_A-policy-security-rule-1] destination-zone untrust [FW_A-policy-security-rule-1] source-address 10.1.1.0 24 [FW_A-policy-security-rule-1] destination-address 10.2.1.0 24 [FW_A-policy-security-rule-1] action permit [FW_A-policy-security-rule-1] quit [FW_A-policy-security] rule name 2 [FW_A-policy-security-rule-2] source-zone untrust [FW_A-policy-security-rule-2] destination-zone trust [FW_A-policy-security-rule-2] source-address 10.2.1.0 24 [FW_A-policy-security-rule-2] destination-address 10.1.1.0 24 [FW_A-policy-security-rule-2] action permit [FW_A-policy-security-rule-2] quit 复制代码 - 配置Local域与Untrust域的本地策略,允许IKE协商报文能正常通过FW_A。
-
[FW_A-policy-security] rule name 3 [FW_A-policy-security-rule-3] source-zone local [FW_A-policy-security-rule-3] destination-zone untrust [FW_A-policy-security-rule-3] source-address 1.1.0.0 16 [FW_A-policy-security-rule-3] destination-address 2.2.2.0 24 [FW_A-policy-security-rule-3] action permit [FW_A-policy-security-rule-3] quit [FW_A-policy-security] rule name 4 [FW_A-policy-security-rule-4] source-zone untrust [FW_A-policy-security-rule-4] destination-zone local [FW_A-policy-security-rule-4] source-address 2.2.2.0 24 [FW_A-policy-security-rule-4] destination-address 1.1.0.0 16 [FW_A-policy-security-rule-4] action permit [FW_A-policy-security-rule-4] quit [FW_A-policy-security] quit 复制代码
-
配置IP-Link,用于检测FW_A到FW_B的主链路是否正常。
-
[FW_A] ip-link check enable [FW_A] ip-link name n1 [FW_A-iplink-n1] destination 2.2.2.2 interface gigabitethernet 1 / 0 / 1 next-hop 1.1.3.2 [FW_A-iplink-n1] quit 复制代码 -
配置到分支的路由。 配置两条到分支的路由,主路由的优先级为10,绑定IP-Link功能;备用路由的优先级为20。当设备检测到主链路故障时,将自动启用备用路由。
-
[FW_A] ip route- static 10.2.1.0 24 1.1.3.2 preference 10 track ip-link n1 [FW_A] ip route- static 10.2.1.0 24 1.1.4.2 preference 20 [FW_A] ip route- static 0.0.0.0 0.0.0.0 1.1.3.2 preference 10 track ip-link n1 [FW_A] ip route- static 0.0.0.0 0.0.0.0 1.1.4.2 preference 20 复制代码 -
配置访问控制列表,定义需要保护的数据流。
-
[FW_A] acl 3000 [FW_A-acl-adv-3000] rule 5 permit ip source 10.1.1.0 0.0.0.255 destination 10.2.1.0 0.0.0.255 [FW_A-acl-adv-3000] quit [FW_A] acl 3001 [FW_A-acl-adv-3001] rule 5 permit ip source 10.1.1.0 0.0.0.255 destination 10.2.1.0 0.0.0.255 [FW_A-acl-adv-3001] quit 复制代码 -
配置名称为tran1的IPSec安全提议。
-
[FW_A] ipsec proposal tran1 [FW_A-ipsec-proposal-tran1] encapsulation-mode tunnel [FW_A-ipsec-proposal-tran1] transform esp [FW_A-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_A-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_A-ipsec-proposal-tran1] quit 复制代码 -
配置序号为10的IKE安全提议。
-
[FW_A] ike proposal 10 [FW_A-ike-proposal-10] authentication-method pre-share [FW_A-ike-proposal-10] prf hmac-sha2- 256 [FW_A-ike-proposal-10] encryption-algorithm aes- 256 [FW_A-ike-proposal-10] dh group2 [FW_A-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_A-ike-proposal-10] quit 复制代码 -
配置IKE Peer。
-
[FW_A] ike peer b [FW_A-ike-peer-b] ike-proposal 10 [FW_A-ike-peer-b] pre-shared-key Test ! 1234 [FW_A-ike-peer-b] remote-address 2.2.2.2 [FW_A-ike-peer-b] quit 复制代码 -
配置IPSec安全策略。
-
[FW_A] ipsec policy map1 10 isakmp [FW_A-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_A-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_A-ipsec-policy-isakmp-map1-10] ike-peer b [FW_A-ipsec-policy-isakmp-map1-10] quit [FW_A] ipsec policy map2 10 isakmp [FW_A-ipsec-policy-isakmp-map2-10] security acl 3001 [FW_A-ipsec-policy-isakmp-map2-10] proposal tran1 [FW_A-ipsec-policy-isakmp-map2-10] ike-peer b [FW_A-ipsec-policy-isakmp-map2-10] quit 复制代码 -
在出接口上应用安全策略组。
-
[FW_A] interface gigabitethernet 1 / 0 / 1 [FW_A-GigabitEthernet1/0/1] ipsec policy map1 [FW_A-GigabitEthernet1/0/1] quit [FW_A] interface gigabitethernet 1 / 0 / 2 [FW_A-GigabitEthernet1/0/2] ipsec policy map2 [FW_A-GigabitEthernet1/0/2] quit 复制代码
-
-
配置FW_B(分支)。
-
基础配置。
- 配置接口IP地址。
-
system-view [sysname] sysname FW_B [FW_B] interface gigabitethernet 1 / 0 / 0 [FW_B-GigabitEthernet1/0/0] ip address 10.2.1.1 24 [FW_B-GigabitEthernet1/0/0] quit [FW_B] interface gigabitethernet 1 / 0 / 1 [FW_B-GigabitEthernet1/0/1] ip address 2.2.2.2 24 [FW_B-GigabitEthernet1/0/1] quit [FW_B] interface tunnel 1 [FW_B-Tunnel1] ip address unnumbered interface gigabitethernet 1 / 0 / 1 [FW_B-Tunnel1] tunnel-protocol ipsec [FW_B-Tunnel1] quit [FW_B] interface tunnel 2 [FW_B-Tunnel2] ip address unnumbered interface gigabitethernet 1 / 0 / 1 [FW_B-Tunnel2] tunnel-protocol ipsec [FW_B-Tunnel2] quit 复制代码 - 将接口加入相应安全区域。
-
[FW_B] firewall zone trust [FW_B-zone-trust] add interface gigabitethernet 1 / 0 / 0 [FW_B-zone-trust] quit [FW_B] firewall zone untrust [FW_B-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_B-zone-untrust] add interface Tunnel 1 [FW_B-zone-untrust] add interface Tunnel 2 [FW_B-zone-untrust] quit 复制代码
-
配置防火墙策略。
- 配置Trust域与Untrust域的转发策略,允许封装前和解封后的报文能通过FW_B。
-
[FW_B] security-policy [FW_B-policy-security] rule name 1 [FW_B-policy-security-rule-1] source-zone trust [FW_B-policy-security-rule-1] destination-zone untrust [FW_B-policy-security-rule-1] source-address 10.2.1.0 24 [FW_B-policy-security-rule-1] destination-address 10.1.1.0 24 [FW_B-policy-security-rule-1] action permit [FW_B-policy-security-rule-1] quit [FW_B-policy-security] rule name 2 [FW_B-policy-security-rule-2] source-zone untrust [FW_B-policy-security-rule-2] destination-zone trust [FW_B-policy-security-rule-2] source-address 10.1.1.0 24 [FW_B-policy-security-rule-2] destination-address 10.2.1.0 24 [FW_B-policy-security-rule-2] action permit [FW_B-policy-security-rule-2] quit 复制代码 - 配置Local域与Untrust域的本地策略,允许IKE协商报文能正常通过FW_B。
-
[FW_B-policy-security] rule name 3 [FW_B-policy-security-rule-3] source-zone local [FW_B-policy-security-rule-3] destination-zone untrust [FW_B-policy-security-rule-3] source-address 2.2.2.0 24 [FW_B-policy-security-rule-3] destination-address 1.1.0.0 16 [FW_B-policy-security-rule-3] action permit [FW_B-policy-security-rule-3] quit [FW_B-policy-security] rule name 4 [FW_B-policy-security-rule-4] source-zone untrust [FW_B-policy-security-rule-4] destination-zone local [FW_B-policy-security-rule-4] source-address 1.1.0.0 16 [FW_B-policy-security-rule-4] destination-address 2.2.2.0 24 [FW_B-policy-security-rule-4] action permit [FW_B-policy-security-rule-4] quit [FW_B-policy-security] quit 复制代码
-
配置IP-Link,用于检测FW_B到FW_A的链路是否正常。
-
[FW_B] ip-link check enable [FW_B] ip-link name n1 [FW_B-iplink-n1] destination 1.1.3.1 interface gigabitethernet 1 / 0 / 1 next-hop 2.2.2.1 [FW_B-iplink-n1] quit 复制代码 -
配置到Tunnel接口的路由。分支访问总部的数据流被首先引流到Tunnel接口。
-
[FW_B] ip route- static 10.1.1.0 255.255.255.0 Tunnel 1 preference 10 track ip-link n1 [FW_B] ip route- static 10.1.1.0 255.255.255.0 Tunnel 2 preference 20 复制代码 -
配置到总部的路由,假设到总部的下一跳是2.2.2.1。
-
[FW_B] ip route- static 0.0.0.0 0.0.0.0 2.2.2.1 复制代码 -
配置访问控制列表,定义需要保护的数据流。
-
[FW_B] acl 3000 [FW_B-acl-adv-3000] rule 5 permit ip source 10.2.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255 [FW_B-acl-adv-3000] quit [FW_B] acl 3001 [FW_B-acl-adv-3001] rule 5 permit ip source 10.2.1.0 0.0.0.255 destination 10.1.1.0 0.0.0.255 [FW_B-acl-adv-3001] quit 复制代码 -
配置名称为tran1的IPSec安全提议。
-
[FW_B] ipsec proposal tran1 [FW_B-ipsec-proposal-tran1] encapsulation-mode tunnel [FW_B-ipsec-proposal-tran1] transform esp [FW_B-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_B-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_B-ipsec-proposal-tran1] quit 复制代码 -
配置序号为10的IKE安全提议。
-
[FW_B] ike proposal 10 [FW_B-ike-proposal-10] authentication-method pre-share [FW_B-ike-proposal-10] prf hmac-sha2- 256 [FW_B-ike-proposal-10] encryption-algorithm aes- 256 [FW_B-ike-proposal-10] dh group2 [FW_B-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_B-ike-proposal-10] quit 复制代码 -
配置IKE Peer。 需要在FW_B上配置两个对等体。当FW_A主备切换时,FW_B将切换对等体与FW_A进行协商。
-
[FW_B] ike peer a1 [FW_B-ike-peer-a1] ike-proposal 10 [FW_B-ike-peer-a1] remote-address 1.1.3.1 [FW_B-ike-peer-a1] pre-shared-key Test ! 1234 [FW_B-ike-peer-a1] quit [FW_B] ike peer a2 [FW_B-ike-peer-a2] ike-proposal 10 [FW_B-ike-peer-a2] remote-address 1.1.4.1 [FW_B-ike-peer-a2] pre-shared-key Test ! 1234 [FW_B-ike-peer-a2] quit 复制代码 -
配置IPSec安全策略组map1和map2。
-
[FW_B] ipsec policy map1 10 isakmp [FW_B-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_B-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map1-10] ike-peer a1 [FW_B-ipsec-policy-isakmp-map1-10] quit [FW_B] ipsec policy map2 10 isakmp [FW_B-ipsec-policy-isakmp-map2-10] security acl 3001 [FW_B-ipsec-policy-isakmp-map2-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map2-10] ike-peer a2 [FW_B-ipsec-policy-isakmp-map2-10] quit 复制代码 -
在接口Tunnel1和Tunnel2上分别应用安全策略组map1和map2。
-
[FW_B] interface tunnel 1 [FW_B-Tunnel1] ipsec policy map1 [FW_B-Tunnel1] quit [FW_B] interface tunnel 2 [FW_B-Tunnel2] ipsec policy map2 [FW_B-Tunnel2] quit 复制代码
-
结果验证
- 配置完成后,在总部的PC1上执行ping命令,看能否ping通分支下的PC2。如果配置正确,则PC1和PC2可以相互ping通。
- 分别在FW_A、FW_B上执行display ike sa命令会显示IKE安全联盟的建立情况。以FW_A为例,出现以下显示说明IKE安全联盟建立成功。
display ike sa
Ike sa information :
-----------------------------------------------------------------------------
Conn-ID Peer VPN Flag(s) Phase
-----------------------------------------------------------------------------
40002 2.2.2.2 RD|ST|A v2:2
40001 2.2.2.2 RD|ST|A v2:1
Number of SA entries : 2
Number of SA entries of all cpu : 2
Flag Description:
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT
HRT--HEARTBEAT LKG--LAST KNOWN GOOD SEQ NO. BCK--BACKED UP
M--ACTIVE S--STANDBY A--ALONE NEG--NEGOTIATING
复制代码 - 分别在FW_A、FW_B上执行display ipsec sa命令会显示IPSec安全联盟的建立情况。以FW_A为例,出现以下显示说明IPSec安全联盟建立成功。
display ipsec sa
===============================
Interface: GigabitEthernet1/0/1
===============================
-----------------------------
IPSec policy name: "map1"
Sequence number : 10
Acl group : 3000
Acl rule : 5
Mode : ISAKMP
-----------------------------
Connection ID : 40002
Encapsulation mode: Tunnel
Tunnel local : 1.1.3.1
Tunnel remote : 2.2.2.2
Flow source : 10.1.1.0/255.255.255.0 0/0
Flow destination : 10.2.1.0/255.255.255.0 0/0
[Outbound ESP SAs]
SPI: 120037772 (0x727a18c)
Proposal: ESP-ENCRYPT-AES-256 SHA2-256-128
SA remaining key duration (bytes/sec): 1887436464/3549
Max sent sequence-number: 5
UDP encapsulation used for NAT traversal: N
SA decrypted packets (number/kilobytes): 4/0
[Inbound ESP SAs]
SPI: 38742361 (0x24f2959)
Proposal: ESP-ENCRYPT-AES-256 SHA2-256-128
SA remaining key duration (bytes/sec): 1887436464/3549
Max received sequence-number: 4
UDP encapsulation used for NAT traversal: N
SA decrypted packets (number/kilobytes): 4/0
Anti-replay : Enable
Anti-replay window size: 1024
复制代码 - 执行命令display ipsec statistics可以查看被加密的数据包的变化,即它们之间的数据传输将被加密。以FW_A为例。
display ipsec statistics
IPSec statistics information:
the security packet statistics:
input/output security packets: 4/4
input/output security bytes: 400 / 400
input/output dropped security packets: 0/0
the encrypt packet statistics:
send chip: 4, recv chip: 4, send err: 0
local cpu: 4, other cpu: 0, recv other cpu: 0
intact packet: 4, first slice: 0, after slice: 0
the decrypt packet statistics:
send chip: 4, recv chip: 4, send err: 0
local cpu: 4, other cpu: 0, recv other cpu: 0
reass first slice: 0, after slice: 0
dropped security packet detail:
can not find SA: 0, wrong SA: 0
authentication: 0, replay: 0
front recheck: 0, after recheck: 0
change cpu enc: 0, dec change cpu: 0
fib search: 0, output l3: 0
flow err: 0, slice err: 0, byte limit: 0
negotiate about packet statistics:
IKE fwd packet ok: 23300, err: 0
IKE ctrl packet inbound ok: 22100, outbound ok: 1105
SoftExpr: 0, HardExpr: 0, DPDOper: 0
trigger ok: 0, switch sa: 2, sync sa: 0
recv IKE nat keepalive: 0, IKE input: 0
复制代码 -
断开FW_A的GE1/0/1接口,查看是否完成链路切换。通过以下操作来判断:
- 执行display ike sa、display ipsec sa命令,查看到新的安全联盟已经存在。
- 总部和分支之间依然能够成功发送和接收报文。且执行display ipsec statistics命令,能看到报文数量在增长。